#FactCheck -Old Image from Iraq Falsely Linked to Alleged Attack on Iran’s Water Treatment Plant
Executive Summary:
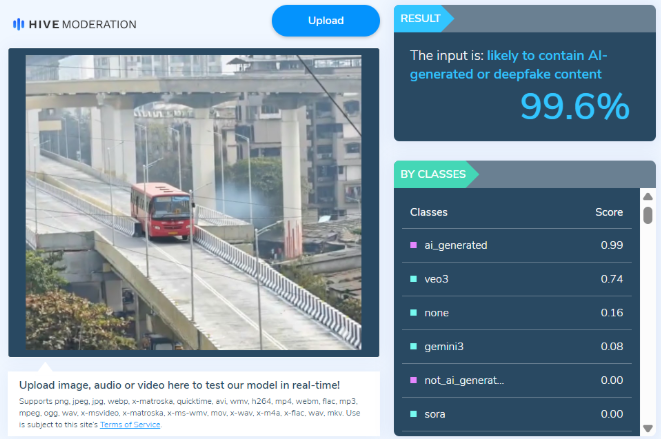
Amid the ongoing tensions and conflict involving the United States, Israel, and Iran, an image of a heavily damaged industrial facility is circulating widely on social media. Several users are sharing the picture claiming that it shows an Iranian water treatment or desalination plant destroyed in a US–Israel attack. Some media reports have also used the same image while reporting on the alleged attack on a freshwater desalination plant in Iran.
However, a research by the CyberPeace found that the claim is misleading. The viral image is not from Iran. It actually shows the aftermath of a drone attack on a warehouse belonging to a US company in Basra, Iraq.
Claim
X user “Shashank Shekhar Jha” shared the image on March 8, 2026, claiming that a freshwater desalination plant in Qeshm, Iran, had been destroyed.
Fact check
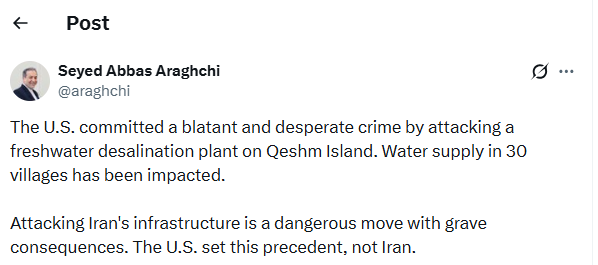
To verify the claim, we conducted a reverse image search using Google Lens. During the search, we found a report published on March 7, 2026, on the website of Asian News International (ANI). The report stated that Iran’s Foreign Minister Seyed Abbas Araghchi condemned a US attack on a freshwater desalination plant on Qeshm Island, calling it a “blatant and desperate crime.”
The report used the same viral image; however, the caption clearly mentioned that it was a representational image credited to Reuters.
https://www.aninews.in/news/world/middle-east/blatant-and-desperate-crime-irans-fm-condemns-us-attack-on-qeshms-freshwater-desalination-plant-warns-of-grave-consequences20260307212645/

To further confirm the claim, we checked the official X account of Seyed Abbas Araghchi. In a post on March 7, he condemned the alleged attack on the desalination plant in Qeshm and stated that the strike had disrupted water supply to around 30 villages. However, the post did not include any image of the incident.
Conclusion
The viral image being shared as evidence of a US–Israel attack on Iran’s water treatment plant is misleading. The photo actually shows the aftermath of a drone strike on a warehouse belonging to a US company in Basra, Iraq, and has been wrongly linked to the situation in Iran.