Introduction
The Ministry of Electronics and Information Technology (MEITy) released the Draft Information Technology (Intermediary Guidelines and Digital Media Ethics Code) Second Amendment Rules, 2026 on March 30, 2026, inviting public comments with a response window closing on April 14. This is a limited 15-day period for public input on proposed rules that will have major constitutional impacts. The brevity and timing of this opportunity demonstrate debatable commitment to stakeholder engagement and meaningful consultation by the drafting agency.
While MEITY describes the proposed amendments as "clarificatory and procedural nature," an analysis shows they will have substantive effects. Collectively, the amended language changes significantly how online speech will be regulated in India by providing the executive with more concentrated regulatory authority, limiting the required transparency of content enforcement, mandating greater retention of data without proportionality-based safeguards, and placing excessive compliance burden on intermediaries. Each of these changes has consequences beyond just changes in process and together, these changes collectively raise substantial concerns regarding compliance with Articles 14, 19, and 21 of the Constitution of India.
The Constitutional Baseline: Shreya Singhal and the Limits of Intermediary Liability
India’s Supreme Court decision in Shreya Singhal v Union of India (2015) 5 SCC 1 provides the foundation for intermediary liability, wherein the Court read down Section 79(3)(b) of the IT Act, 2000, holding that intermediaries are required to act upon receiving actual knowledge only through a court order or a valid notification by the appropriate government authority. The Supreme Court’s decision intended to provide a constitutional protection to intermediaries from being subjected to informal, unverified executive pressure to take down content by requiring that any such order be subject to some level of legal objective credibility or threshold.
Rule 3(4) of the proposed amendments places that balance under significant strain. By requiring intermediaries to comply with advisories, directions, standard operating procedures, codes of practice, and guidelines issued by the Ministry — and tying non-compliance to the loss of safe harbour — the draft effectively lowers the constitutional threshold that Shreya Singhal was designed to maintain. Compliance obligations now potentially arise from instruments that carry no judicial sanction and no mandatory public disclosure.
Rule 3(4): Delegated Legislation or Executive Overreach
The rule-making power conferred on the Central Government under Section 87 of the IT Act is limited to carrying out the provisions of the Act. It does not authorise the creation of new substantive obligations. This principle has been consistently affirmed in Indian Express Newspapers v. Union of India (1985) 1 SCC 641 and Confederation of Ex-Servicemen Associations v. Union of India (2006) 8 SCC 399, where the Court held that delegated legislation must remain within the four corners of the parent statute.
Rule 3(4) tests those limits. It converts executive advisories into binding compliance instruments without a clear statutory foundation in either Section 79 or Section 87. Although the proposed rule requires that such instruments specify their legal basis, there is no requirement that they be published or made publicly accessible. This creates a framework in which legality risks becoming circular — instruments claimed to be lawful solely by reference to a provision that does not clearly authorise them, shielded from scrutiny by their own opacity. Justice Chandurkar’s judgment in Kunal Kamra v. Union of India identified precisely this defect in the Fact Check Unit amendment. Rule 3(4) replicates the structural problem in a broader form.
Compliance Pressure and the Logic of Over-Censorship
The practical consequence of Rule 3(4) lies not only in its legality but in how it reshapes incentive structures for platforms. An intermediary facing the permanent threat of safe harbour loss will not wait to assess the legal merit of each advisory. The rational calculation is to comply early, broadly, and without friction. Lawful content — particularly satire, political commentary, and journalism — becomes vulnerable not because it is unlawful, but because it presents regulatory risk.
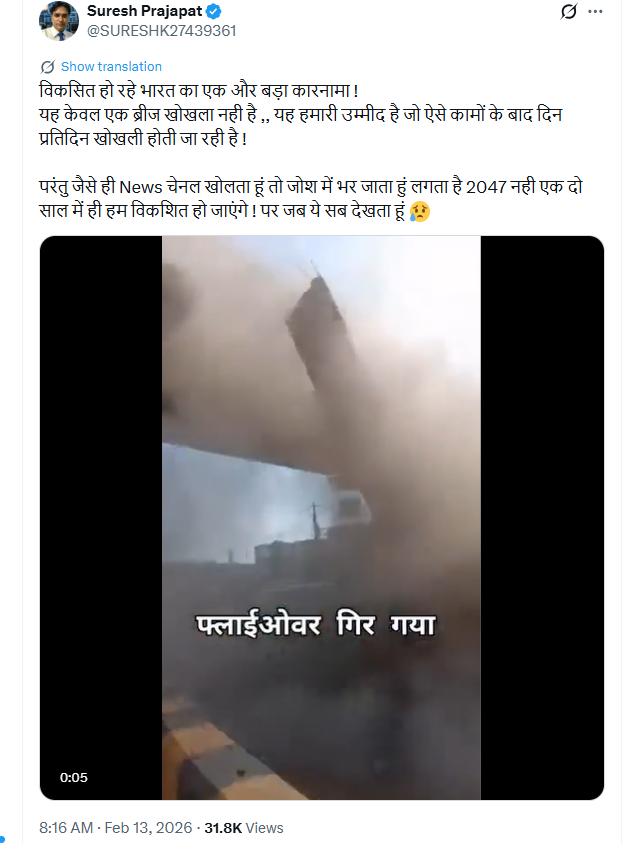
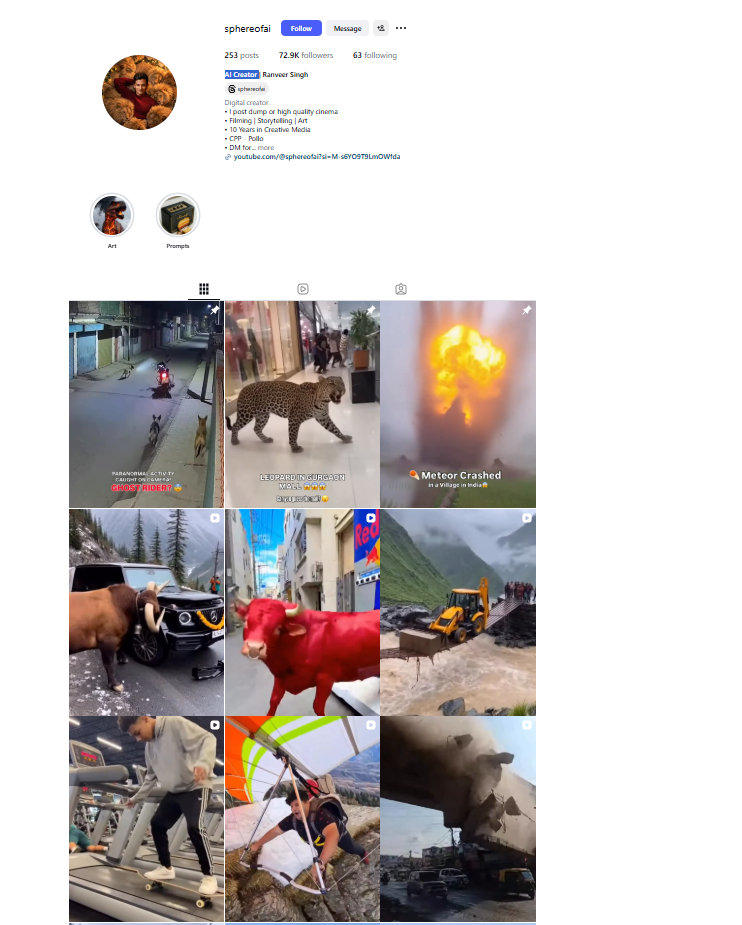
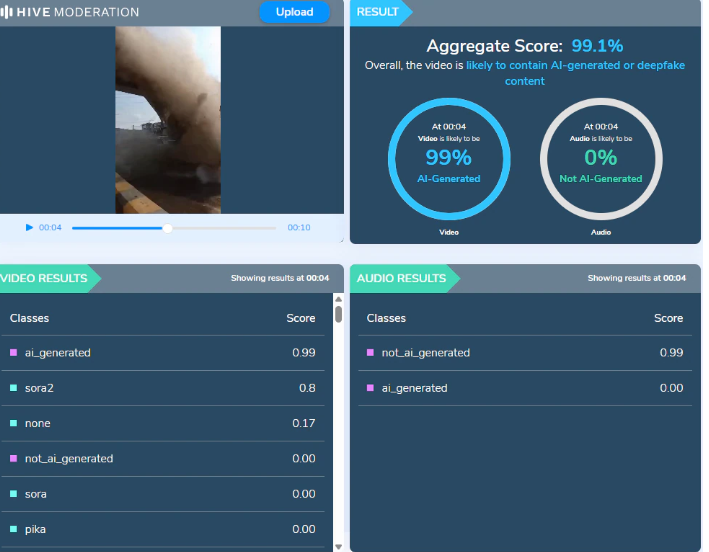
This dynamic was visible on 18 March 2026, when stand-up comedian Pulkit Mani (@hunnywhoisfunny) found his satirical Instagram reel being restricted across India. The video had accumulated over 16.5 million views. Users encountered a notice citing Section 79(3)(b) of the IT Act. No reasons were publicly provided. No prior hearing was offered. The same night, several political parody and satire accounts were withheld on X.
Data Retention, Privacy, and the Proportionality Test
The amendments to Rules 3(1)(g) and 3(1)(h) extend data retention obligations by making them additional to requirements under any other law. The existing 180-day floor for retained user data — covering removed content, registration information, and associated records — becomes a minimum rather than a ceiling. No maximum is specified, and no proportionality requirement accompanies the extension.
This raises direct concerns under Article 21 as interpreted in Justice K.S. Puttaswamy v. Union of India (2017) 10 SCC 1, which held that any state intrusion into privacy must satisfy the triple test of legality, necessity, and proportionality. Undefined retention periods, with no statutory ceiling and no requirement of purpose limitation, risk failing all three. The longer user data is held, including metadata, device information, and records of removed content, the greater the exposure to surveillance, unauthorised access, and use beyond the original justification.
Circumventing Judicial Scrutiny Through Procedural Redesign
The Bombay High Court, in its August 2021 order, stayed provisions of the IT Rules’ oversight mechanism as prima facie violative of Article 19(1)(a). The Madras High Court in T.M. Krishna v. Union of India affirmed that stay, cautioning that government-controlled media oversight risked undermining press independence. Both matters remain pending before the Delhi High Court.
The amendments to Rules 8(1) and 14 restructure the same oversight machinery through a modified procedural design. By extending the Inter-Departmental Committee’s jurisdiction to cover “matters” referred by the Ministry with no requirement of a complainant, no defined subject matter, and no guaranteed prior hearing, the proposed rules effectively reconstitute what courts found constitutionally suspect. Individual users posting news and current affairs content are now brought within reach of blocking mechanisms originally designed for institutional publishers.
Conclusion
As seen above, the Draft IT Rules 2026 are unable to meet the constitutional and judicial requirements to regulate free speech. What the proposed amendments construct is a durable system in which platforms self-censor under liability pressure, data is retained without proportionate justification, and content oversight expands through procedural adjustment rather than parliamentary legislation. Regulation of the digital public sphere is both legitimate and necessary. But it must be anchored in law, not in the quiet authority of executive advisories. The law must ultimately remain anchored in constitutional values, guided by the enduring principles of justice, equity, and good conscience.
The comment period closes on 14 April 2026.
Submissions may be sent to itrules.consultation@meity.gov.in.
References
- https://www.meity.gov.in/static/uploads/2026/03/30591fc6e322dcbcc9dae84a0f02e9e7.pdf
- https://www.meity.gov.in/static/uploads/2026/03/a71a21d35c107f2e528363d3eb17646a.pdf
- https://www.meity.gov.in/static/uploads/2026/02/550681ab908f8afb135b0ad42816a1c9.pdf
- https://neopolitico.com/india/government-blocks-viral-satirical-reel-impersonating-pm-modi-raising-fresh-questions-on-free-speech-and-digital-regulation/
- https://internetfreedom.in/sound-the-alarm-iffs-first-read-on-meitys-draft-it-rules-second-amendment-2026/