#FactCheck: AI-Generated Photo Shared to Claim Boycott of Hindu Sammelan
Executive Summary:
A photo circulating on social media shows a stage with the words “Hindu Sammelan” (Hindu Conference) written in large letters. In front of the stage, rows of chairs appear largely empty, with only a few people seated while most seats remain vacant.
Users sharing the image claim that the event, held under the banner of a “Hindu Sammelan,” was in fact a “Brahmin Sammelan,” and that indigenous communities chose to stay away, resulting in poor attendance.
It is noteworthy that, on the occasion of the centenary year of the Rashtriya Swayamsevak Sangh (RSS), various “Hindu Sammelan” events are being organized across the country. The viral image is being linked to this broader context.
However, research conducted by the CyberPeace found the viral claim to be false. Our research revealed that the image being shared on social media is not authentic but AI-generated and is being circulated with a misleading narrative.
Claim
On February 21, 2026, a Facebook user shared the viral image. The original and archived links are provided below
- https://www.facebook.com/photo?fbid=935049042540479&set=gm.2425972001215469&idorvanity=465387370607285
- https://ghostarchive.org/archive/sxC6d

Fact Check:
A keyword search on Google confirmed that several “Hindu Sammelan” events have indeed been organized across the country as part of the RSS centenary year. For instance, media reports have covered such events in different cities, including Nagpur.
However, upon closely examining the viral image, we observed certain visual inconsistencies and unnatural elements that raised suspicion of AI generation. We first analyzed the image using the AI detection tool Hive Moderation, which indicated a 79.3 percent probability that the image was AI-generated.
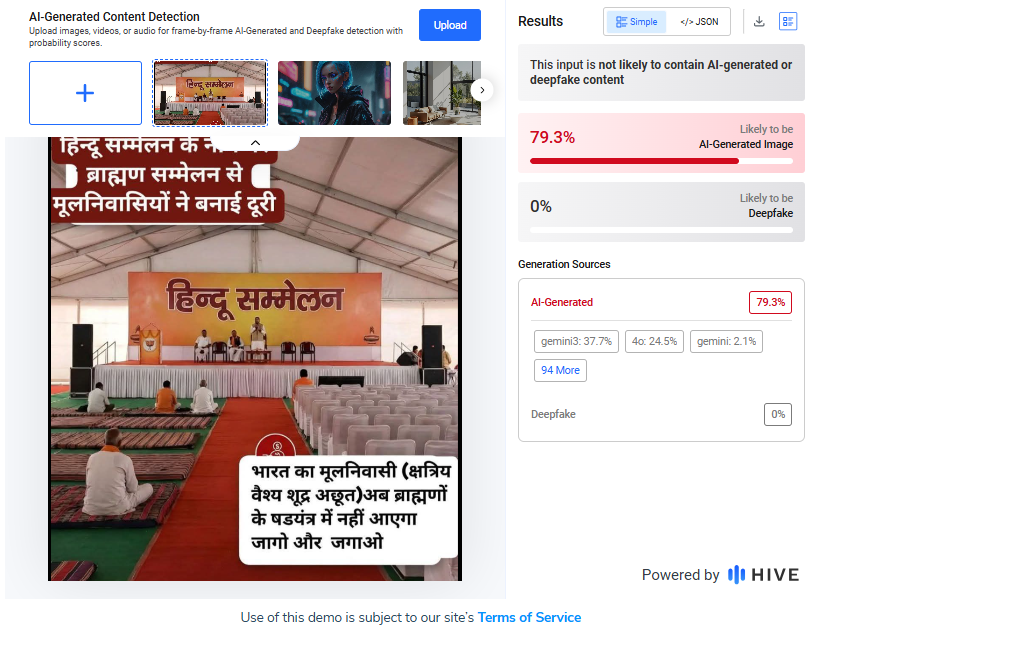
To further verify, we scanned the image using another AI detection platform, Sightengine. The results showed a 97 percent likelihood that the image was AI-generated.

Conclusion
Our research confirms that the image circulating on social media is not genuine. It has been artificially created using AI technology and is being shared with a misleading claim.





.webp)





