#FactCheck: Old clip of Greenland tsunami depicts as tsunami in Japan
Executive Summary:
A viral video depicting a powerful tsunami wave destroying coastal infrastructure is being falsely associated with the recent tsunami warning in Japan following an earthquake in Russia. Fact-checking through reverse image search reveals that the footage is from a 2017 tsunami in Greenland, triggered by a massive landslide in the Karrat Fjord.

Claim:
A viral video circulating on social media shows a massive tsunami wave crashing into the coastline, destroying boats and surrounding infrastructure. The footage is being falsely linked to the recent tsunami warning issued in Japan following an earthquake in Russia. However, initial verification suggests that the video is unrelated to the current event and may be from a previous incident.

Fact Check:
The video, which shows water forcefully inundating a coastal area, is neither recent nor related to the current tsunami event in Japan. A reverse image search conducted using keyframes extracted from the viral footage confirms that it is being misrepresented. The video actually originates from a tsunami that struck Greenland in 2017. The original footage is available on YouTube and has no connection to the recent earthquake-induced tsunami warning in Japan
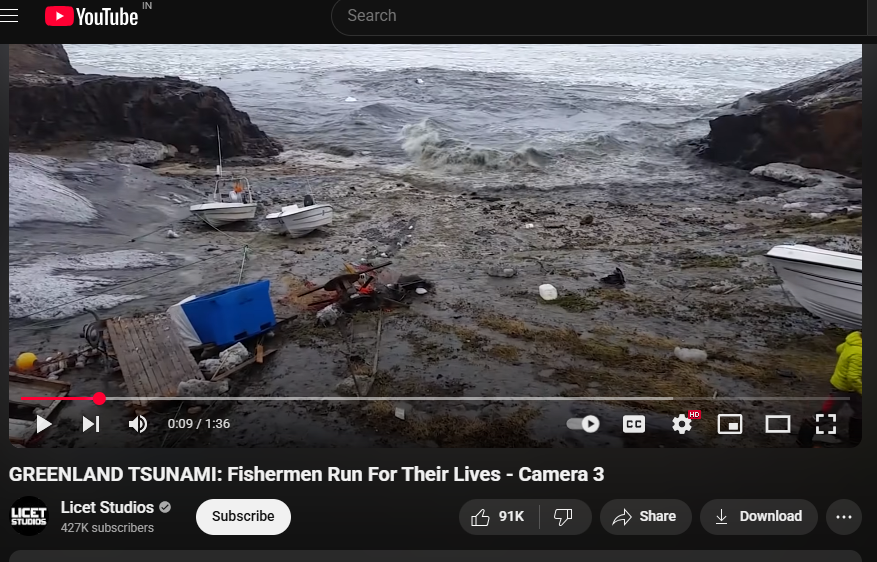
The American Geophysical Union (AGU) confirmed in a blog post on June 19, 2017, that the deadly Greenland tsunami on June 17, 2017, was caused by a massive landslide. Millions of cubic meters of rock were dumped into the Karrat Fjord by the landslide, creating a wave that was more than 90 meters high and destroying the village of Nuugaatsiaq. A similar news article from The Guardian can be found.

Conclusion:
Videos purporting to depict the effects of a recent tsunami in Japan are deceptive and repurposed from unrelated incidents. Users of social media are urged to confirm the legitimacy of such content before sharing it, particularly during natural disasters when false information can exacerbate public anxiety and confusion.
- Claim: Recent natural disasters in Russia are being censored
- Claimed On: Social Media
- Fact Check: False and Misleading
Related Blogs
.webp)
Introduction
In an era where organisations are increasingly interdependent through global supply chains, outsourcing and digital ecosystems, third-party risk has become one of the most vital aspects of enterprise risk management. The SolarWinds hack, the MOVEit vulnerabilities and recent software vendor attacks all serve as a reminder of the necessity to enhance Third-Party Risk Management (TPRM). As cyber risks evolve and become more sophisticated and as regulatory oversight sharpens globally, 2025 is a transformative year for the development of TPRM practices. This blog explores the top trends redefining TPRM in 2025, encompassing real-time risk scoring, AI-driven due diligence, harmonisation of regulations, integration of ESG, and a shift towards continuous monitoring. All of these trends signal a larger movement towards resilience, openness and anticipatory defence in an increasingly dependent world.
Real-Time and Continuous Monitoring becomes the Norm
The old TPRM methods entailed point-in-time testing, which typically was an annual or onboarding process. By 2025, organisations are shifting towards continuous, real-time monitoring of their third-party ecosystems. Now, authentic advanced tools are making it possible for companies to take a real-time pulse of the security of their vendors by monitoring threat indicators, patching practices and digital footprint variations. This change has been further spurred by the growth in cyber supply chain attacks, where the attackers target vendors to gain access to bigger organisations. Real-time monitoring software enables the timely detection of malicious activity, equipping organisations with a faster defence response. It also guarantees dynamic risk rating instead of relying on outdated questionnaire-based scoring.
AI and Automation in Risk Assessment and Due Diligence
Manual TPRM processes aren't sustainable anymore. In 2025, AI and machine learning are reshaping the TPRM lifecycle from onboarding and risk classification to contract review and incident handling. AI technology can now analyse massive amounts of vendor documentation and automatically raise red flags on potential issues. Natural language processing (NLP) is becoming more common for automated contract intelligence, which assists in the detection of risky clauses or liability gaps or data protection obligations. In addition, automation is increasing scalability for large organisations that have hundreds or thousands of third-party relationships, eliminating human errors and compliance fatigue. However, all of this must be implemented with a strong focus on security, transparency, and ethical AI use to ensure that sensitive vendor and organisational data remains protected throughout the process.
Risk Quantification and Business Impact Mapping
Risk scoring in isolation is no longer adequate. One of the major trends for 2025 is the merging of third-party risk with business impact analysis (BIA). Organisations are using tools that associate vendors to particular business processes and assets, allowing better knowledge of how a compromise of a vendor would impact operations, customer information or financial position. This movement has resulted in increased use of risk quantification models, such as FAIR (Factor Analysis of Information Risk), which puts dollar values on risks associated with vendors. By using the language of business value, CISOs and risk officers are more effective at prioritising risks and making resource allocations.
Environmental, Social, and Governance (ESG) enters into TPRM
As ESG keeps growing on the corporate agenda, organisations are taking TPRM one step further than cybersecurity and legal risks and expanding it to incorporate ESG-related factors. In 2025, organisations evaluate if their suppliers have ethical labour practices, sustainable supply chains, DEI (Diversity, Equity, Inclusion) metrics and climate impact disclosures. This growth is not only a reputational concern, but also a third-party non-compliance with ESG can now invoke regulatory or shareholder action. ESG risk scoring software and vendor ESG audits are becoming components of onboarding and performance evaluations.
Shared Assessments and Third-Party Exchanges
With the duplication of effort by having multiple vendors respond to the same security questionnaires, the trend is moving toward shared assessments. Systems such as the SIG Questionnaire (Standardised Information Gathering) and the Global Vendor Exchange allow vendors to upload once and share with many clients. This change not only simplifies the due diligence process but also enhances data accuracy, standardisation and vendor experience. In 2025, organisations are relying more and more on industry-wide vendor assurance platforms to minimise duplication, decrease costs and maximise trust.
Incident Response and Resilience Partnerships
Another trend on the rise is bringing vendors into incident response planning. In 2025, proactive organisations address major vendors as more than suppliers but as resilience partners. This encompasses shared tabletop exercises, communication procedures and breach notification SLAs. With the increasing ransomware attacks and cloud reliance, organisations are now calling for vendor-side recovery plans, RTO and RPO metrics. TPRM is transforming into a comprehensive resilience management function where readiness and not mere compliance takes centre stage.
Conclusion
Third-Party Risk Management in 2025 is no longer about checklists and compliance audits; it's a dynamic, intelligence-driven and continuous process. With regulatory alignment, AI automation, real-time monitoring, ESG integration and resilience partnerships leading the way, organisations are transforming their TPRM programs to address contemporary threat landscapes. As digital ecosystems grow increasingly complex and interdependent, managing third-party risk is now essential. Early adopters who invest in tools, talent and governance will be more likely to create secure and resilient businesses for the AI era.
References
- https://finance.ec.europa.eu/publications/digital-operational-resilience-act-dora_en
- https://digital-strategy.ec.europa.eu/en/policies/nis2-directive
- https://www.meity.gov.in/data-protection-framework
- https://securityscorecard.com
- https://sharedassessments.org/sig/
- https://www.fairinstitute.org/fair-model

Executive Summary:
A viral online video claims Canadian Prime Minister Justin Trudeau promotes an investment project. However, the CyberPeace Research Team has confirmed that the video is a deepfake, created using AI technology to manipulate Trudeau's facial expressions and voice. The original footage has no connection to any investment project. The claim that Justin Trudeau endorses this project is false and misleading.

Claims:
A viral video falsely claims that Canadian Prime Minister Justin Trudeau is endorsing an investment project.

Fact Check:
Upon receiving the viral posts, we conducted a Google Lens search on the keyframes of the video. The search led us to various legitimate sources featuring Prime Minister Justin Trudeau, none of which included promotion of any investment projects. The viral video exhibited signs of digital manipulation, prompting a deeper investigation.

We used AI detection tools, such as TrueMedia, to analyze the video. The analysis confirmed with 99.8% confidence that the video was a deepfake. The tools identified "substantial evidence of manipulation," particularly in the facial movements and voice, which were found to be artificially generated.



Additionally, an extensive review of official statements and interviews with Prime Minister Trudeau revealed no mention of any such investment project. No credible reports were found linking Trudeau to this promotion, further confirming the video’s inauthenticity.
Conclusion:
The viral video claiming that Justin Trudeau promotes an investment project is a deepfake. The research using various tools such as Google Lens, AI detection tool confirms that the video is manipulated using AI technology. Additionally, there is no information in any official sources. Thus, the CyberPeace Research Team confirms that the video was manipulated using AI technology, making the claim false and misleading.
- Claim: Justin Trudeau promotes an investment project viral on social media.
- Claimed on: Facebook
- Fact Check: False & Misleading

Introduction
The two-day Apple’s Worldwide Developer Conference (WWDC) 2023, which was held on the 6th & 7th of June, has become an essential and highly anticipated part of our calendar as frequently as the trend. This year’s keynote announcements will include all of the usual enhancements for iOS, iPadOS, watchOS, macOS, and more. However, this year is also unique due to the unveiling of the Vision Pro headset, a brand-new Apple product.
In this blog, we will examine the exciting announcements made at Apple WWDC 2023, which was a ground-breaking event.
macOS Sonoma
macOS Sonoma, the new presentation of macOS disclosed at the WWDC full of exciting features. It comes with stunning video screensavers that show stunning scenes from all over the world. Gadgets can now be added genuinely to the work area and adjusted totally based on the client’s action. Also, it changes variety and blurring out of the spotlight while utilising applications. In addition, Death Stranding: Directors Cut for Mac announced that the Game Mode is added to make Macs more suitable for gaming. A presenter overlay enhances video presentations, and viewers can respond to them with interactive responses. Updated Safari is also included in the WebApp feature that turns frequently used websites into dedicated windows, a new Profile system for separating browsing history, and secure password sharing. Currently, the developer beta is available and the public beta will be available in July, and the final release is anticipated for the fall.
ios 16
Apple WWDC 2023 shows the following iOS, and iOS 16 replication, offering plenty of energising highlights for iPhone and iPad clients. Apple maintains its commitment to privacy with iOS 16, which introduces enhanced privacy settings that give users even more control over their data and online privacy. Users can also personalise their devices according to their preferences thanks to the new operating system’s refinement and customisable user interface.Improved multitasking capabilities like redesigned Files app and advanced note-taking features are just a few of the productivity enhancements included in the iOS 16. With iOS 16, Apple also improves its AR capabilities, allowing developers to develop even more immersive and interactive AR experiences.

WatchOS 9
Apple WWDC 2023 carried energising updates to the Apple Watch with the presentation of watchOS 9. The Apple Watch is an essential companion for sustaining a healthy lifestyle because the most recent version of the operating system includes cutting-edge health and fitness features. WatchOS 9 gives users unprecedented control over their health, offering personalised fitness recommendations and advanced sleep tracking.
Additionally, new watch faces were added, enhancing communication capabilities and improving app performance in watchOS 9, making the Apple Watch even easier to use daily.
ios 17
Rather than focusing on major features, Apple focused on quality-of-life enhancements when it announced iOS 17 at WWDC 2023. Live Voicemail with real-time transcripts of voicemails, personalised personal contact “posters,” and video voicemails for FaceTime are all part of the update. Search filters, a catch-up arrow, live location sharing, and a safety feature called Check-In are all available in Messages. AirDrop now supports NameDrop for transferring contact information; stickers have been expanded. The autocorrect and recording features on the keyboard have been improved for accuracy. Standby in the lock screen is an intelligent home display that shows the weather, upcoming appointments, and notifications. Siri works on Standby and adjusts itself for the night. The developer beta is currently available now, and a public beta will take place next month before the full release is in the fall.
Vision Pro VR Headset
Apple unveiled the Vision Pro AR headset, their first foray into virtual reality (VR), during the WWDC keynote. The Vision Pro is a virtual reality headset that competes with PlayStation VR2 and Meta Quest 3. This is in contrast to the long-awaited Apple smart glasses. Apple put a lot of effort into making a thin and light headset by using premium materials when needed. Voice, hand, and eye commands are all used to operate the Digital Crown-equipped device. The showcases offer extraordinary clarity, which is fueled by Apple’s M2 processor with a committed R1 chip. The Vision Pro combines virtual reality (VR) and augmented reality (AR), enabling users to interact with Apple apps and gain access to the company’s existing ecosystem. The expanded reality space created by the headset’s sensors and cameras allows users to place apps in real-world environments and adjust their level of concentration. Optic ID is a security and unlocking eye-tracking technology that is incorporated into the Vision Pro. It allows for a more immersive screen experience because it is compatible with Apple accessories like Magic Keyboard and Mac. At launch, the Vision Pro supports over a hundred Apple game galleries. Disney gave a hint that Apple and Disney might work together in the future by announcing support for the Vision Pro and making the Disney Plus app available immediately. The show highlighted the headset’s lightweight plan and recommended Apple clients wear it for extended periods. However, widespread adoption may be difficult due to the high price of $3,499 (₹289,093.01 approx). Apple is expected to release the Vision Pro for public use in 2024.

15-inch MacBook Air
At the WWDC event, Apple revealed a new MacBook Air with a larger 15-inch model instead of the standard 13-inch model. The 15-inch MacBook Air features a powerful Apple M2 processor, a thin, light, and long-lasting design, and a stunning 15.3-inch Retina display. It comes in four colours and has a headphone jack, two USB-C ports, and MagSafe charging. The display has six spatial speakers, a 1080p webcam, and 500 nits of brightness. Apple claims a battery life of up to 18 hours.
Conclusion
At Apple’s 2023 WWDC, the company demonstrated its commitment to developing technology that is user-friendly and accessible to all. Apple’s commitment to improving the user experience across all of its products is demonstrated in the updates to operating systems, improvements of Siri, breakthroughs in augmented reality, and enhancements to health and fitness.By making complex innovations more like-minded and easy to understand, Apple is enabling people to use the maximum capacity of their gadgets. Apple’s innovations at WWDC 2023 are expected to shape the future of technology, simplifying everyday tasks and revolutionising how we interact with the digital world.As we push ahead, it is exciting to guess what these advancements will proceed to develop and decidedly mean for our lives. The future holds even more incredible possibilities for all of us because of Apple’s focus on privacy, user-centric design, and pushing the boundaries of innovation. Thus, prepare to embrace a future where innovation flawlessly incorporates into our lives because of the endeavours displayed at Apple WWDC 2023.


