#FactCheck:AI-Created Video Falsely Shows Car Catching Fire During Celebration
Executive Summary:
A video showing a car catching fire is rapidly going viral on social media. In the clip, a family can be seen bursting firecrackers in front of a newly purchased car. Moments later, the vehicle also appears to catch fire. The video is being shared with the claim that the family was celebrating the purchase of a new car with fireworks, which accidentally led to the vehicle going up in flames. Many users are circulating the clip as footage of a real incident. However, an research by the CyberPeace found that the video is not from a real-life event but has been created using Artificial Intelligence (AI).
Claim
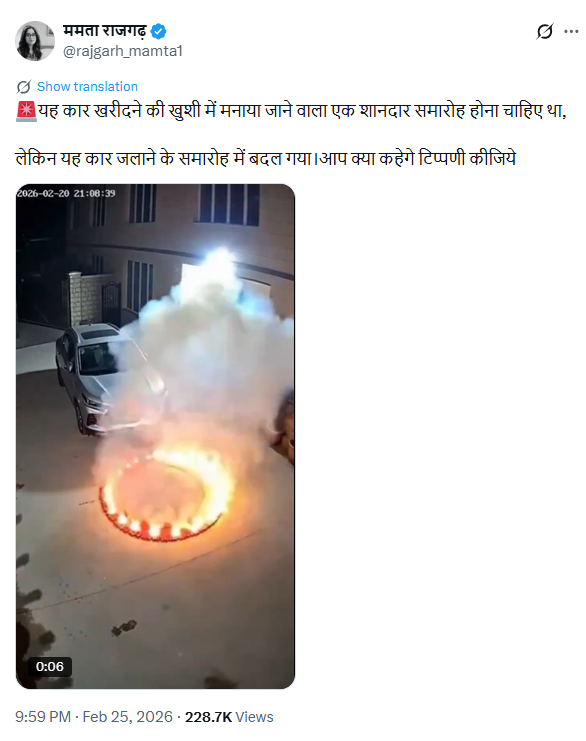
On February 25, 2026, an X user named “Mamta Rajgarh” shared the viral video with the caption:“This was supposed to be a grand celebration for buying a new car, but it turned into a ceremony of burning the car. What do you say? Comment below.”
- Post link: https://x.com/rajgarh_mamta1/status/2026696175311786408?s=20
- Archived link: https://perma.cc/22AA-KBS4
Fact Check:
To verify the claim, we conducted a keyword search on Google but found no credible news reports supporting the alleged incident. Upon closely examining the video, we noticed several technical inconsistencies. The car’s number plate is unclear, a common flaw often seen in AI-generated content. Additionally, the sequence of events appears unnatural — the firecrackers seem to extinguish first, and only after a delay does the car suddenly catch fire. These irregularities raised suspicion that the video may have been artificially generated. To further verify, we analyzed the clip using AI detection tools. Hive Moderation indicated a 98.7 percent likelihood that the video was generated using Artificial Intelligence.
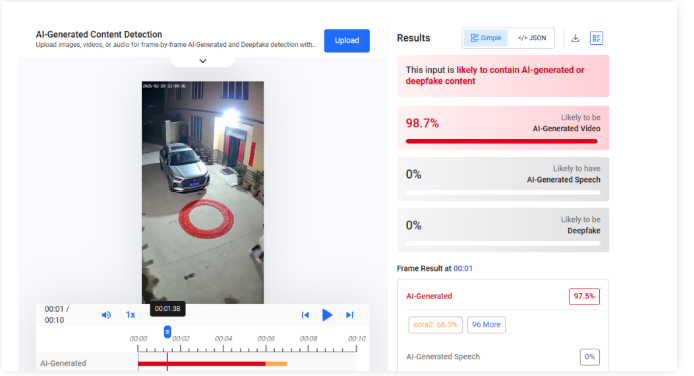
Another AI detection tool, Undetectable.ai, suggested a 77 percent probability that the video was AI-generated.
Conclusion
Our research confirms that the viral video does not depict a real incident. It has been created using Artificial Intelligence and is being misleadingly shared as genuine footage.
Related Blogs
.webp)
Introduction
YouTube is testing a new feature called ‘Notes,’ which allows users to add community-sourced context to videos. The feature allows users to clarify if a video is a parody or if it is misrepresenting information. The feature builds on existing features to provide helpful content alongside videos. Currently under testing, the feature will be available to a limited number of eligible contributors who will be invited to write notes on videos. These notes will appear publicly under a video if they are found to be broadly helpful. Viewers will be able to rate notes into three categories: ‘Helpful,’ ‘Somewhat helpful,’ or ‘Unhelpful’. Based on the ratings, YouTube will determine which notes are published. The feature will first be rolled out on mobile devices in the U.S. in English. The Google-owned platform will look at ways to improve the feature over time, including whether it makes sense to expand it to other markets.
YouTube To Roll Out The New ‘Notes’ Feature
YouTube is testing an experimental feature that allows users to add notes to provide relevant, timely, and easy-to-understand context for videos. This initiative builds on previous products that display helpful information alongside videos, such as information panels and disclosure requirements when content is altered or synthetic. YouTube in its blog clarified that the pilot will be available on mobiles in the U.S. and in the English language, to start with. During this test phase, viewers, participants, and creators are invited to give feedback on the quality of the notes.
YouTube further stated in its blog that a limited number of eligible contributors will be invited via email or Creator Studio notifications to write notes so that they can test the feature and add value to the system before the organisation decides on next steps and whether or not to expand the feature. Eligibility criteria include having an active YouTube channel in good standing with Yotube’s Community Guidelines.
Viewers in the U.S. will start seeing notes on videos in the coming weeks and months. In this initial pilot, third-party evaluators will rate the helpfulness of notes, which will help train the platform’s systems. As the pilot moves forward, contributors themselves will rate notes as well.
Notes will appear publicly under a video if they are found to be broadly helpful. People will be asked whether they think a note is helpful, somewhat helpful, or unhelpful and the reasons for the same. For example, if a note is marked as ‘Helpful,’ the evaluator will have the opportunity to specify if it is so because it cites high-quality sources or is written clearly and neutrally. A bridging-based algorithm will be used to consider these ratings and determine what notes are published. YouTube is excited to explore new ways to make context-setting even more relevant, dynamic, and unique to the videos we are watching, at scale, across the huge variety of content on YouTube.
CyberPeace Analysis: How Can Notes Help Counter Misinformation
The potential effectiveness of countering misinformation on YouTube using the proposed ‘Notes’ feature is significant. Enabling contributors to include notes on videos can offer relevant and accurate context to clarify any misleading or false information in the video. These notes can aid in enhancing viewers' comprehension of the content and detecting misinformation. The participation from users to rate the added notes as helpful, somewhat helpful, and unhelpful adds a heightened layer of transparency and public participation in identifying the accuracy of the content.
As YouTube intends to gather feedback from its various stakeholders to improve the feature over time, one can look forward to improved policy and practical over time: the feedback mechanism will allow for continuous refinement of the feature, ensuring it effectively addresses misinformation. The platform employs algorithms to identify helpful notes that cater to a broad audience across different perspectives. This helps showcase accurate information and combat misinformation.
Furthermore, along with the Notes feature, YouTube should explore and implement prebunking and debunking strategies on the platform by promoting educational content and empowering users to discern between fact and any misleading information.
Conclusion
The new feature, currently in the testing phase, aims to counter misinformation by providing context, enabling user feedback, leveraging algorithms, promoting transparency, and continuously improving information quality. Considering the diverse audience on the platform and high volumes of daily content consumption, it is important for both the platform operators and users to engage with factual, verifiable information. The fallout of misinformation on such a popular platform can be immense, and so, any mechanism or feature that can help counter the same must be developed to its full potential. Apart from this new Notes feature, YouTube has also implemented certain measures in the past to counter misinformation, such as providing authenticated sources to counter any election misinformation during the recent 2024 elections in India. These efforts are a welcome contribution to our shared responsibility as netizens to create a trustworthy, factual and truly-informational digital ecosystem.
References:
- https://blog.youtube/news-and-events/new-ways-to-offer-viewers-more-context/
- https://www.thehindu.com/sci-tech/technology/internet/youtube-tests-feature-that-will-let-users-add-context-to-videos/article68302933.ece
Executive Summary
A postcard featuring BJP leader Manoj Tiwari is being widely shared on social media with a purported statement attributed to him. The viral postcard claims that Tiwari suggested that if people stopped using the ₹1 coin and treated ₹2 as ₹1, the value of the dollar would automatically come down to ₹45. Users are sharing the post claiming that the BJP leader made the bizarre suggestion to strengthen the Indian rupee against the US dollar.
However, research by the CyberPeace Research Wing found the claim to be false. Manoj Tiwari never made any such statement regarding the rupee and the dollar. The BJP MP himself has dismissed the viral claim as fake.
Claim
TMC leader Kirti Azad shared the viral postcard on X and wrote, “As received on X, forwarded as it is. India is truly blessed with such brilliant minds.”
https://x.com/KirtiAzaad/status/2055905987115233473?s=20

Fact Check
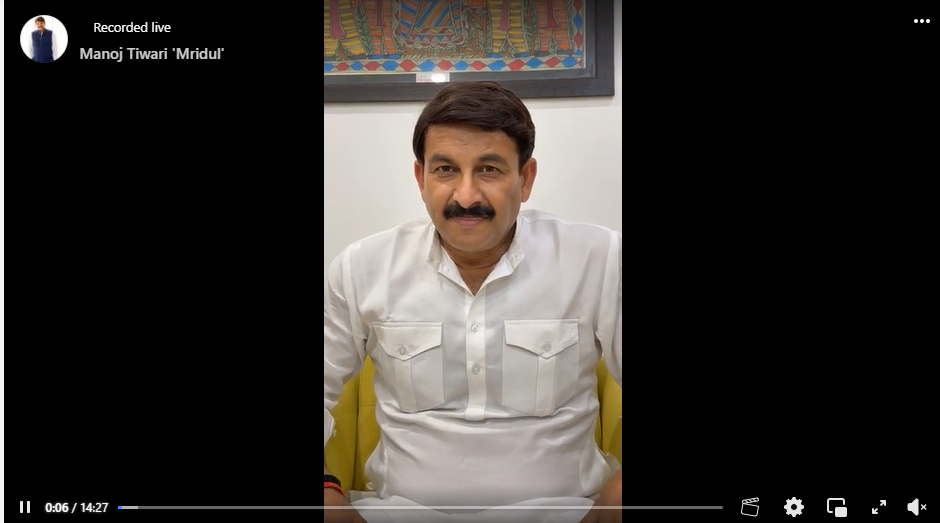
A keyword search on Google did not yield any credible media reports suggesting that Manoj Tiwari had made such a statement. No reliable source was found to support the viral claim. Further research led to a clarification posted on Manoj Tiwari’s official Facebook page. In the video statement, Tiwari categorically denied making any such remark about the rupee and the dollar. He stated that the viral claim being circulated in his name was completely fake.
Manoj Tiwari’s clarification video on Facebook
Conclusion
The viral claim is false. Manoj Tiwari never made any statement suggesting that stopping the use of ₹1 and treating ₹2 as ₹1 would strengthen the rupee against the dollar. He has himself denied the claim and called it fake.

Introduction
The Telecom Regulatory Authority of India (TRAI) issued a consultation paper titled “Encouraging Innovative Technologies, Services, Use Cases, and Business Models through Regulatory Sandbox in Digital Communication Sector. The paper presents a draft sandbox structure for live testing of new digital communication products or services in a regulated environment. TRAI seeks comments from stakeholders on several parts of the framework.
What is digital communication?
Digital communication is the use of internet tools such as email, social media messaging, and texting to communicate with other people or a specific audience. Even something as easy as viewing the content on this webpage qualifies as digital communication.
Aim of Paper
- Frameworks are intended to support regulators’ desire for innovation while also ensuring economic resilience and consumer protection. Considering this, the Department of Telecom (DoT) asked TRAI to offer recommendations on a regulatory sandbox framework. TRAI approaches the issue with the goal of encouraging creativity and hastening the adoption of cutting-edge digital communications technologies.
- Artificial intelligence, the Internet of Things, edge computing, and other emerging technologies are revolutionizing how we connect, communicate, and access information, driving the digital communication sector to rapidly expand. To keep up with this dynamic environment, an enabling environment for the development and deployment of novel technologies, services, use cases, and business models is required.
- The regulatory sandbox concept is becoming increasingly popular around the world as a means of encouraging innovation in a range of industries. A regulatory sandbox is a regulated environment in which businesses and innovators can test their concepts, commodities, and services while operating under changing restrictions.
- Regulatory Sandbox will benefit the telecom startup ecosystem by providing access to a real-time network environment and other data, allowing them to evaluate the reliability of new applications before releasing them to the market. Regulatory Sandbox also attempts to stimulate cross-sectoral collaboration for carrying out such testing by engaging the assistance of other ministries and departments in order to give the starting company with a single window for acquiring all clearances.
What is regulatory sandbox?
- A regulatory sandbox is a controlled regulatory environment in which new products or services are tested in real-time.
- It serves as a “safe space” for businesses because authorities may or may not allow certain relaxations for the sole purpose of testing.
- The sandbox enables the regulator, innovators, financial service providers, and clients to perform field testing in order to gather evidence on the benefits and hazards of new financial innovations, while closely monitoring and mitigating their risks.
What are the advantages of having a regulatory sandbox?
- Firstly, regulators obtain first-hand empirical evidence on the benefits and risks of emerging technologies and their implications, allowing them to form an informed opinion on the regulatory changes or new regulations that may be required to support useful innovation while mitigating the associated risks.
- Second, sandbox customers can evaluate the viability of a product without the need for a wider and more expensive roll-out. If the product appears to have a high chance of success, it may be authorized and delivered to a wider market more quickly.
Digital communication sector and Regulatory Sandbox
- Many countries’ regulatory organizations have built sandbox settings for telecom tech innovation.
- These frameworks are intended to encourage regulators’ desire for innovation while also promoting economic resilience and consumer protection.
- In this context, the Department of Telecom (DoT) had asked TRAI to give recommendations on a regulatory sandbox framework.
- Written comments on the drafting framework will be received until July 17, 2023, and counter-comments will be taken until August 1, 2023. The Authority’s goal in the digital communication industry is to foster creativity and expedite the use of emerging technologies such as artificial intelligence (AI), the Internet of Things (IoT), and edge computing. These technologies are changing the way individuals connect, engage, and access information, causing rapid changes in the industry.
Conclusion
According to TRAI, these technologies are changing how individuals connect, engage, and obtain information, resulting in significant changes in the sector.
The regulatory sandbox also wants to stimulate cross-sectoral collaboration for carrying out such testing by engaging the assistance of other ministries and departments in order to give the starting company with a single window for acquiring all clearances. The consultation paper covers some of the worldwide regulatory sandbox frameworks in use in the digital communication industry, as well as some of the frameworks in use inside the country in other sectors.


