#FactCheck -Viral Humanoid Robot Video Actually Filmed at the Museum of the Future
Executive Summary
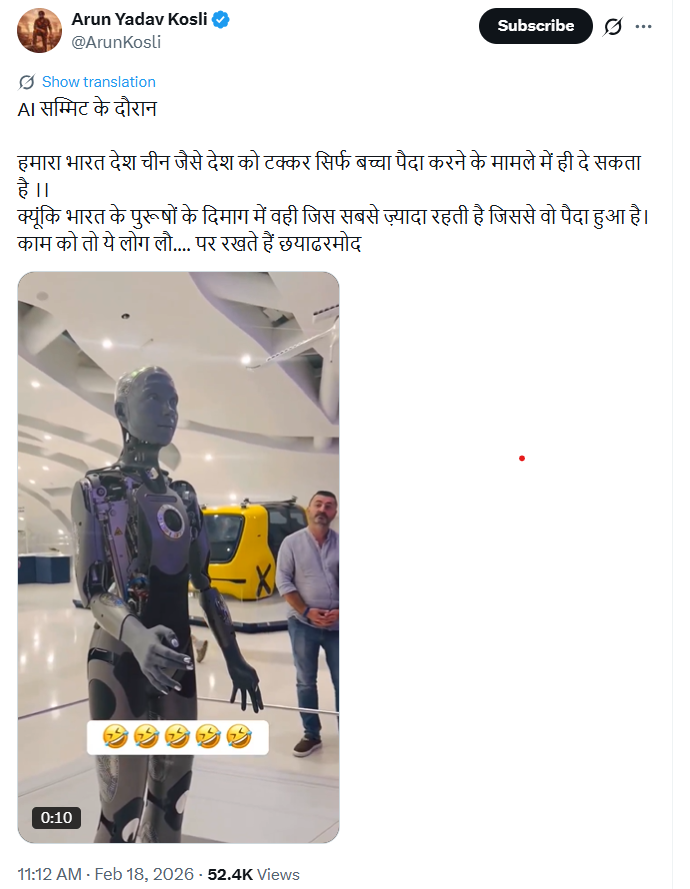
A video circulating widely on social media shows a man interacting with a humanoid robot and using abusive language, after which the robot asks him to maintain politeness. Several users shared the clip claiming that the incident took place during a recent AI summit in New Delhi. The video triggered strong reactions online, with some users demanding legal action against the individual. However, research by CyberPeace found the claim to be misleading.
Claim
Social media users claimed that the viral video showing a man abusing a robot was recorded during an AI summit in New Delhi, India.
Fact Check
To verify the claim, we conducted a reverse image search of the individual seen in the video. The search led us to an Instagram post uploaded by a Pakistani account identifying the individual as Kashif Zameer.

Further keyword searches helped us locate his Instagram profile, where the same video had been uploaded on February 17, 2026. The post included hashtags such as “Dubai,” indicating the actual location of the incident. The profile also lists Lahore, Pakistan, as the user’s location and describes him as a businessman and social media personality.

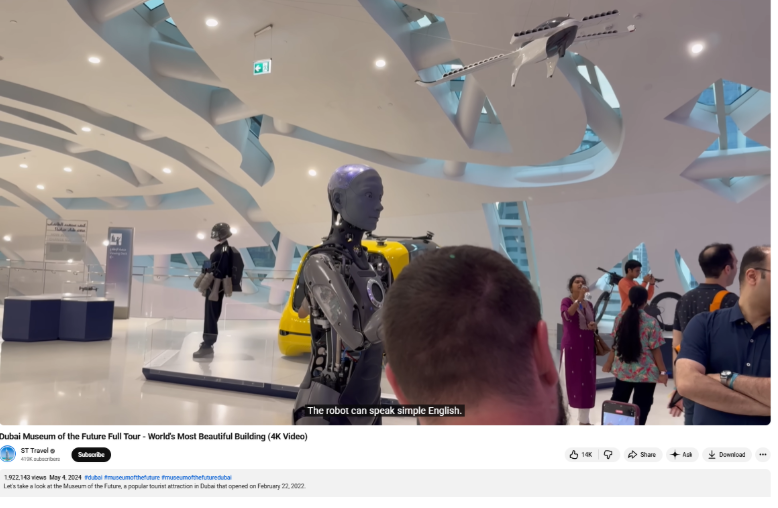
To confirm the location shown in the video, we conducted additional searches using keywords such as “Dubai” and “humanoid robot.” The research revealed that the robot featured in the clip is “Ameca,” located at the Museum of the Future in Dubai.
Conclusion
The viral claim is false. The video is not related to any AI summit held in New Delhi. The incident occurred in Dubai, and the person seen in the video is not an Indian citizen.
Related Blogs

Executive Summary:
A viral video depicting a powerful tsunami wave destroying coastal infrastructure is being falsely associated with the recent tsunami warning in Japan following an earthquake in Russia. Fact-checking through reverse image search reveals that the footage is from a 2017 tsunami in Greenland, triggered by a massive landslide in the Karrat Fjord.

Claim:
A viral video circulating on social media shows a massive tsunami wave crashing into the coastline, destroying boats and surrounding infrastructure. The footage is being falsely linked to the recent tsunami warning issued in Japan following an earthquake in Russia. However, initial verification suggests that the video is unrelated to the current event and may be from a previous incident.

Fact Check:
The video, which shows water forcefully inundating a coastal area, is neither recent nor related to the current tsunami event in Japan. A reverse image search conducted using keyframes extracted from the viral footage confirms that it is being misrepresented. The video actually originates from a tsunami that struck Greenland in 2017. The original footage is available on YouTube and has no connection to the recent earthquake-induced tsunami warning in Japan
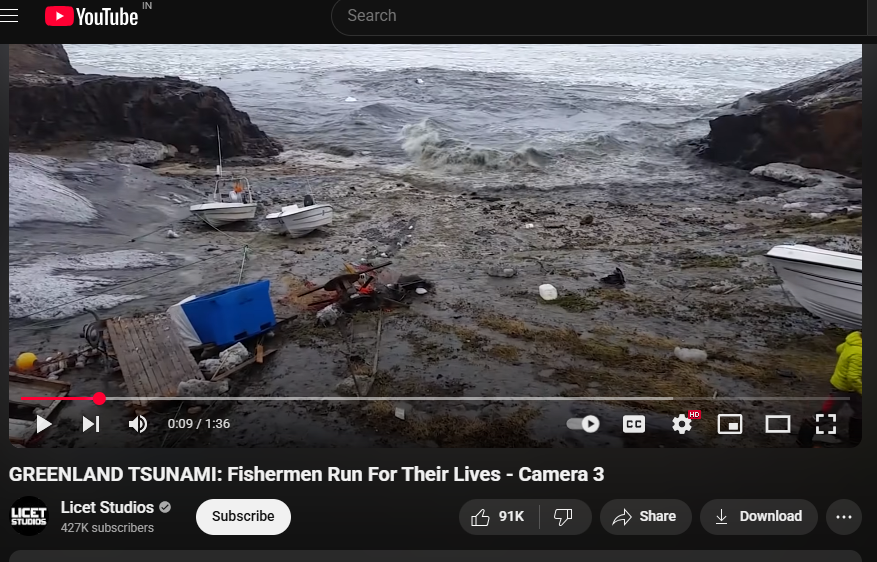
The American Geophysical Union (AGU) confirmed in a blog post on June 19, 2017, that the deadly Greenland tsunami on June 17, 2017, was caused by a massive landslide. Millions of cubic meters of rock were dumped into the Karrat Fjord by the landslide, creating a wave that was more than 90 meters high and destroying the village of Nuugaatsiaq. A similar news article from The Guardian can be found.

Conclusion:
Videos purporting to depict the effects of a recent tsunami in Japan are deceptive and repurposed from unrelated incidents. Users of social media are urged to confirm the legitimacy of such content before sharing it, particularly during natural disasters when false information can exacerbate public anxiety and confusion.
- Claim: Recent natural disasters in Russia are being censored
- Claimed On: Social Media
- Fact Check: False and Misleading

Introduction
As the world is being "Digitally Interlaced", cyber security has become a continuous wrangle. The “Gambling industry” is considered an incredibly lucrative mark for cybercriminals, principally due to the enormous quantities of cash on hand and the sensitive details it processes day to day. Cybercriminals may use susceptibilities in gambling scaffolds to achieve financial scams or launder unlawful funds. An analysis by Security Scorecard discovered that the online gambling industry was ranked third in the possibility of encountering a cyber attack, following the energy and financial services sectors. Similarly, Online gambling is a bending matter that demands meticulous contemplation by policymakers and nationals. The incredible rise of online gambling has led to a terse acclivity in unlawful activities such as online scams, fraud, etc. Also, online sports gambling has become a thriving endeavour in contemporary years as millions of people are putting stakes and gambles on their electronic devices.
The Challenges
Online gambling has thus become a widespread frolicking for numerous youngsters, with the industry tossed to be worth billions of dollars in the forthcoming decades. The prominent cyber security challenges in the gambling industry are money laundering, financial laundering, ransomware, personal information theft, data breaches, distributed Denial of Service (DDoS), system disruptions and Insider perils and employee malfeasance. Challenges of online gambling also include being properly not regulated and a lack of social interaction with near and dear ones. The spread of Internet gambling has presented many problems affecting consumer behaviour online, motivations to gamble, problem gambling, security of websites, and the righteousness and virtue of the games. The rise of online gambling among young people due to the lack of clear regulations has likewise produced an abundant backdrop for financial ruination.
Web games and betting are among the fastest-evolving areas of the Internet. Over the past several years, there has been an international flare-up in online gambling, permitting customers to play from the convenience of home, work, and public locations. Numerous offshore betting websites and apps usually permit parties to win in the start with sound returns, whereas after the user gets addicted and invests considerable sums, they either keep failing or have the website refuse to cash out the winnings. Also, the information demonstrates that online games have been employed to commit wrongdoings (Child sexual exploitive material, religious conversion, cyberbullying, fraud, betting in virtual online casinos, etc.)
India's laws and regulations surrounding online gambling are complex and constantly evolving. While the legal framework is not entirely clear, a few state in India have their own set of rules.
Recently In April 2023, the Union Ministry of Electronics and Information Technology (“MeitY”), by virtue of the rule-making powers available to the central government under the Information Technology Act, 2000 (“IT Act 2000”), implemented a new central legal framework for online gaming through amendments to the Information Technology (Intermediary Guidelines and Digital Media Ethics Code) Rules, 2021 (“IT Rules 2021”). These amendments (“Online Gaming Rules”) propose a light-touch, co-regulatory regime whereby MeitY-recognised, independent self-regulatory bodies (“SRB”) will verify whether an “online real-money game” is to be made available to the general public or not – in accordance with the baseline criteria prescribed by the Online Gaming Rules.
The Online Gaming Rules attempt to regulate online gaming platforms by treating them as an “online gaming intermediary” (“OGI”) and prescribing intermediary due diligence obligations for them under the IT Rules 2021. An OGI has been defined in the Online Gaming Rules as “any intermediary that enables the users of its computer resource to access one or more online games”. Under the Online Gaming Rules, an online game can be a “permissible online game” if (i) it is not an online real-money game, or (ii) it is an online real-money game but is “verified” by an SRB in accordance with the baseline criteria prescribed by the Online Gaming Rules and any additional criteria prescribed by the SRB itself.
Global Perspective
The global gaming industry worth over US$227 billion in 2022 is further projected to grow to US$312 billion by 2027. Several countries have set regulatory frameworks about online gaming, though these are skewed, concentrating mainly on gambling and circumventing numerous of the more typical cyber threats. The US spends about $60 billion annually on online gambling and sports betting. In Europe, gambling is an even larger moneymaker. Also, numerous countries in Europe, like the UK, have legalised gambling. Nevertheless, it is prohibited for a US based company to operate an online gambling site. Yet, sports betting online is permitted in some states.
Today, though the gaming market has been overpowered by China and the US, future growth in the sector is anticipated to come from emerging economies like India with increasing populations. The permitted status of online gambling in India is nonetheless imprecise, vamoosing space for exploitation by cyber criminals and disarray for players involved. One of the climactic points that ought to be addressed is the sudden upsurge of online games, which increases gambling. Skill-based games such as poker, rummy etc., have additionally been developed to circumvent the legal definition of gambling in India. The recent instances of the online gaming industry not being properly regulated have also come to light in India. For instance, the Enforcement Directorate (ED) is still investigating the vast Mahadev Online Betting scandal, exposing an unknown money laundering method using Unified Payment Interface (UPI) IDs. Also, the Cyber Cell in Agra has taken proactive action against copyright violations, illegal online gambling and betting activities, shutting down 27 Illegal cricket betting sites in major operations, safeguarding several lakhs of Indians with thousands of crores from being transferred to overseas shores principally China.
Consequently, though India has announced new regulations on online gaming, its contemporary policy framework cannot contend with the problems endangering this sector. The Public Gambling Act of 1867 makes it unlawful to use a public gambling house or to be seen in one. Nevertheless, the act does not explicitly cite online gambling, leading to further interpretation. The Ministry of Home Affairs (MHA) has released a further awareness campaign for offshore illegal gambling apps, notifying users to be mindful of foreign apps as they may be fraudulent and might induce monetary damage to the user. Also, state laws control gambling in India with each state having its own directive on the subject. Yet, the Supreme Court of India has maintained that skilled games are not gambling and are thus legal. Furthermore, the Information Technology (IT) Act, of 2000 does not precisely handle online gambling or games that enable gambling.
Today, developers have strived for new ways to monetise the growing popularity of online gaming, which oversaw the creation of in-game currencies that can be bought using actual money, usually through credit cards. Several nations have prohibited the usage of in-game currency and loot boxes, considering them a kind of online gambling. The in-game currency has thus caused much disagreement about becoming a state of hunting monetisation by developers, especially targeting minor or newbie players. The gambling industry, therefore, faces unique cybersecurity challenges that require a comprehensive and proactive approach to cybersecurity.
Conclusion
Presently, there are approximately 3.09 billion active video game players worldwide, and the number is expected to reach 3.32 billion by 2024 as of 2023. In the contemporary digital era, information is priceless, and encryption acts as a necessary means to safeguard it. Thus, Regulators are working to maintain the swiftness of shift in the industry, as the dearth of transparency in the law has made it challenging to implement regulations. There is also less awareness about cyber security in India due to the following grounds such as the lack of ethical hackers in the country, companies in India lacking focus on cyber security and hiring a team of ethical hackers and cyber security experts. Furthermore, there has been a lack of knowledge among the citizens as well.
It is essential to realise the conceivable social and economic consequences and take measures to handle the online gambling industry. The industry has thus been undersized in the mode of research following online crime and Internet gambling, even though it is an acute emphasis. There is also a pressing necessity to rebuild these regulations to tackle the more unbridled cyber security hazards swarming the gaming industry. Similarly, there is an urgent need for governments and policymakers around the world to start paying more attention to the gaming industry as cyber security threats continue to rise. There should be a further need to strengthen the regulatory framework, establish Self Regulatory Organizations (SROs), create ethical gaming designs and increase awareness among gamers. The Government of India should consider devising its own rating system to rate games so that players under 18 cannot access them.
Eventually, cyber security is a shared commitment, and everyone in the online gambling ecosystem must function jointly to provide a secure and safe setting for all.
References:
- https://truefort.com/gambling-industry-cybersecurity/
- https://www.orfonline.org/research/cybersecurity-threats-in-online-gaming-learnings-for-india
- https://www.hackread.com/chinese-scammers-cloned-websites-gambling-network/
- https://www.civilsdaily.com/news/cybersecurity-threats-from-online-gaming/
- https://www.linkedin.com/pulse/legal-considerations-online-gambling-india-sudden-increase-mathur/
- https://www.jsheld.com/insights/articles/the-importance-of-cybersecurity-in-the-online-sports-betting-industry
- https://www.the420.in/agra-cyber-cell-takes-down-27-illegal-betting-sites/
- https://g2g.news/gaming/ministry-of-home-affairs-releases-new-awareness-campaign-for-online-gaming-in-india/
- https://smestreet.in/technology/kaspersky-warns-of-increased-phishing-scams-and-data-breaches-in-apac-for-2024-2381601
- https://economictimes.indiatimes.com/tech/newsletters/morning-dispatch/govt-bans-mahadev-other-illegal-betting-apps-cyber-attacks-against-india-spike/articleshow/104996017.cms?from=mdr
- https://cipher.com/cybersecurity-for-gambling/
- https://www.mangalorean.com/tightening-the-reins-indian-government-blocks-over-550-illegal-betting-and-gambling-apps/
- https://cybersecurityasean.com/news-press-releases/kaspersky-predicts-rise-cyber-threats-across-apac-2024
- https://www.cnbctv18.com/technology/mahadev-betting-app-scam-ed-money-laundering-upi-celebrities-under-scanner-17815661.htm
- https://iclg.com/practice-areas/gambling-laws-and-regulations/india

Introduction
In April 2026, a class action suit in a federal court in California rejuvenated one of the most basic assertions in digital communication: that private messages are private. The suit claims that Meta Platforms, its subsidiary WhatsApp, and third-party contractors such as Accenture could have accessed user messages even though it had long promised end-to-end encryption.
This case is not merely about a single company or a single platform. It poses more profound questions regarding the definition, communication and regulation of privacy in an age when digital infrastructure is becoming more and more incomprehensible or unprovable to regular users.
What the Lawsuit Actually Says
The suit was filed by plaintiffs Brian Y. Shirazi and Nida Samson, who alleged that WhatsApp, Meta and contractors had intercepted and shared private messages with third parties without their consent. The complaint states that the federal investigators were notified by the whistleblowers that employees of Meta and external contractors had access to the content of WhatsApp messages that were expected to be encrypted and inaccessible.
This directly puts into question the main privacy promise of WhatsApp. The platform has been promoting itself as an end-to-end encrypted service in which not even WhatsApp can read your messages. The case asserts that this assertion was deceptive in its application and that no one ever gave any consent prior to their messages being intercepted, stored, or read.
The plaintiffs are proposing to represent a nationwide class of users of WhatsApp who sent or received messages between April 5, 2016, and the current time and subclasses in California and Pennsylvania. The claims involve breach of contract, California laws on privacy and data violations, false advertising and the Pennsylvania Wiretapping and Electronic Surveillance Act.
It should be mentioned that they are allegations. Similar assertions have been refuted by Metacomet in the past, with the company asserting that its encryption frameworks ensure that the company cannot access the messages. The case is in progress, and no facts have been found.
The Grey Area No One Talks About
In order to see the significance of this lawsuit outside the court, it is useful to consider the way modern messaging platforms actually work. In principle, end-to-end encryption means that only the sender and receiver can decipher a message. Even the service provider should not be able to access the content.
However, there is a grey space that is seldom publicly discussed: content moderation. User reports, metadata analysis or restricted message review processes are common methods used by platforms to identify harmful content, like fraud, child exploitation, or spam. The complaint indicates that such moderation procedures might have opened avenues to the content of messages to human reviewers or automated systems more than users were made to think.
This is not the first time that privacy and safety are at odds. Many jurisdictions have also advocated access to encrypted communications through legal means in the name of national security or criminal investigations. What this suit does is put that tension into even more stark relief by asking whether platforms are really open with users about these trade-offs.
The Consent Problem
The emphasis on consent is one of the most significant implications of this case. The plaintiffs claim that the users were never warned that their messages would be accessed by the employees or third parties and were never provided with any meaningful option on the same.
This is where the case turns into a data governance issue, rather than a legal one. Most data protection models consider the legality of data processing to be based on whether the users know how their data is being processed or not. When the accusations are found to be true, then the matter is not technical. It would be a contractual and ethical failure, a disjuncture between what platforms promise and what they do.
The implications are huge to the billions of users who use WhatsApp to communicate, both personally and professionally, and even politically.
What This Means Going Forward
An effective attack on the encryption assertions of WhatsApp might have actual implications for the rest of the digital ecosystem. Users might start doubting that any platform can be really considered to guarantee privacy. The regulators can advocate more stringent disclosure policies and compulsory independent audits of encryption systems. Social networks might have to re-architect their moderation frameworks to make sure that safety features do not silently compromise privacy guarantees that they claim.
Meanwhile, there is a real policy dilemma in this case that cannot be disregarded. Complete privacy may preclude the capacity to identify abuse or hateful material. The manner in which that balance is achieved and, more to the point, the manner in which it is made transparent to users is an issue that has yet to be addressed by policymakers, civil society and the tech industry.
Other technical experts have also questioned the plausibility of the claims in the lawsuit at scale, noting that it would be an extraordinary undertaking to systematically bypass end-to-end encryption. This further supports the argument of independent verification mechanisms. The problem is that users should not be forced to decide what they should believe in more: corporate guarantees or legal charges. There must be rules that can be enforced which are above the two.
Conclusion: Beyond One Lawsuit
The WhatsApp class action is eventually concerning a structural issue within the digital economy. Users are expected to have faith in systems that they cannot observe, on the assertions that they cannot test themselves.
This case is a warning, regardless of whether the allegations are proved or not. Privacy cannot be based on marketing language. It needs legally binding norms, actual transparency in the treatment of data, and external control that will provide users with something more to hang on than a tagline.
References
- https://www.bitdefender.com/en-us/blog/hotforsecurity/lawsuit-claims-meta-can-access-whatsapp-messages-despite-end-to-end-encryption-2
- https://blog.cryptographyengineering.com/2026/02/02/whatsapp-encryption-a-lawsuit-and-a-lot-of-noise/
- https://www.bloomberg.com/news/articles/2026-01-25/lawsuit-claims-meta-can-see-whatsapp-chats-in-breach-of-privacy
- https://www.classaction.org/blog/despite-privacy-promises-meta-third-parties-read-and-store-whatsapp-messages-class-action-lawsuit-alleges


