#FactCheck - Video Showing Sadhus in Ice Is Artificially Generated
Executive Summary
A video showing a group of Hindu ascetics (sadhus) allegedly performing intense penance while their bodies appear to be covered in ice is being widely shared on social media. Users are circulating the video as real and claiming that it represents an ancient tradition of Sanatan Dharma. CyberPeace research found the viral claim to be false.The research revealed that the video circulating on social media is not real but has been generated using artificial intelligence (AI).
Claim
On social media platform Facebook, a user shared the viral video on January 16, 2026. The video shows several ascetics engaged in penance, with their bodies seemingly covered in ice. Users shared the video while claiming that it depicts an authentic spiritual practice rooted in Sanatan Dharma.
Links to the post, archive link, and screenshots can be seen below.

Fact Check:
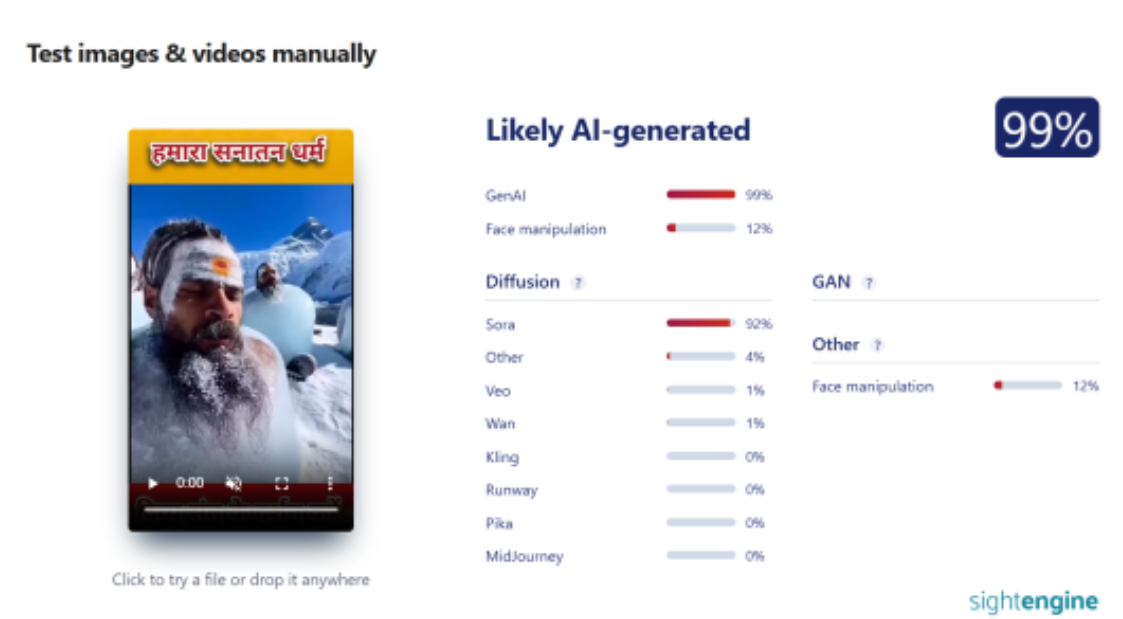
To verify the authenticity of the viral claim, CyberPeace searched relevant keywords on Google. However, no credible or reliable media reports supporting the claim were found. A close examination of the viral video raised suspicion that it may have been AI-generated. To verify this, the video was analysed using the AI detection tool Hive Moderation. According to the results, the video was found to be 99 percent AI-generated.
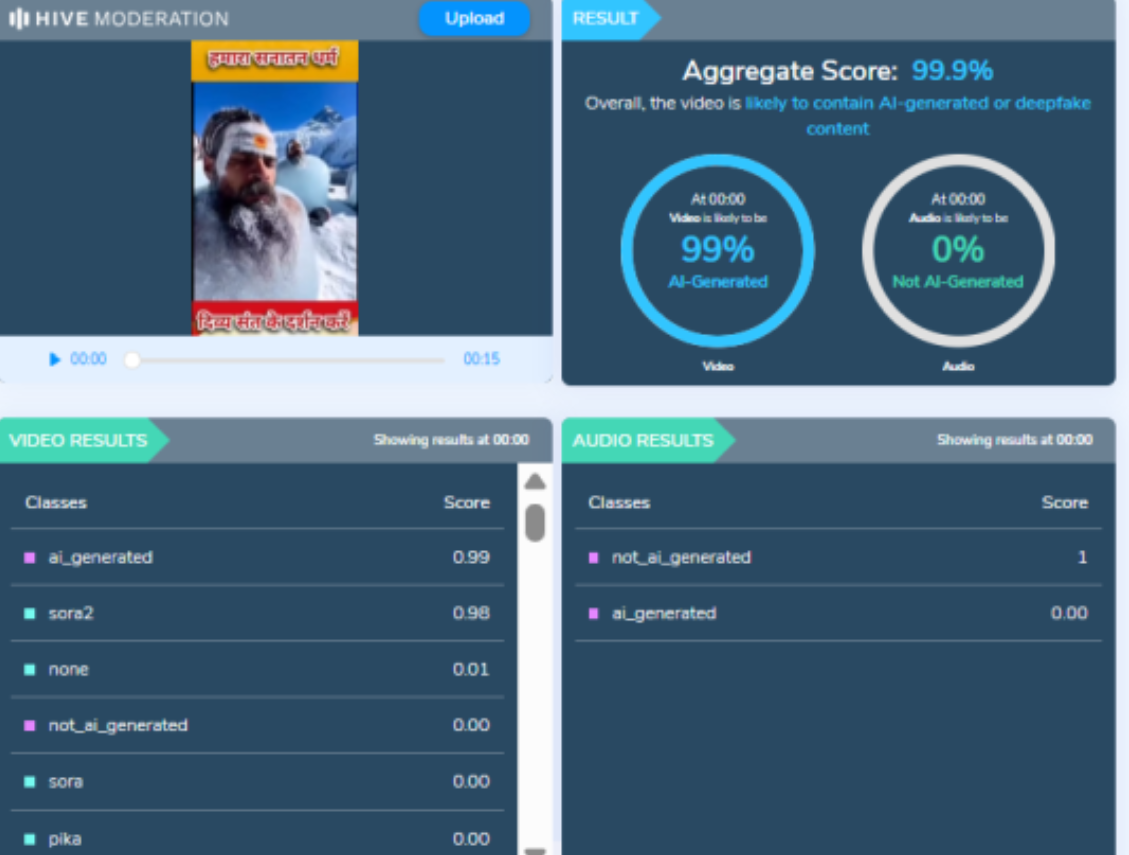
In the next step of the research, the same video was analysed using another AI detection tool, Sightengine. The results again indicated that the video was 99 percent AI-generated.
Conclusion
CyberPeace concludes that the video circulating on social media is not real. The viral video showing ascetics covered in ice was generated using artificial intelligence and does not depict an actual religious or spiritual practice.
Related Blogs

Introduction
Devices and interconnectivity are the pipelines which drive the data into cyberspace, and in turn, the users consume this data to perform different tasks in the digital age. The security of devices and networks is essential as they are the first defenders of cyberspace. Bad actors often target systems and networks with malware and ransomware, these attacks are differently motivated, but all wreak havoc upon the system and can impact individuals and organisations alike. Mobile users worldwide prefer iOS or Android, but both operating systems are vulnerable to cyberattacks these days. Some of these attacks go undetected for a long time.
Op Triangulation
As reported by Kaspersky, While monitoring the network traffic of their own corporate Wi-Fi network dedicated to mobile devices using the Kaspersky Unified Monitoring and Analysis Platform (KUMA), Kaspersky noticed suspicious activity that originated from several iOS-based phones. Since it is impossible to inspect modern iOS devices from the inside, they created offline backups of the devices in question, inspected them using the Mobile Verification Toolkit’s mvt-ios and discovered traces of compromise. This is known as Operation Triangulation and has been in action since 2019 and got detected in 2023.
The Malware
A portion of the filesystem, including some of the user data and service databases, is included in mobile device backups. The files, directories, and database entries’ timestamps make it possible to reconstruct the events that happened to the device roughly. The “timeline.csv” file created by the mvt-ios software contains a sorted timeline of events that is comparable to the super-timeline utilised by traditional digital forensic tools. Pinpointing particular artefacts that show the compromise using this timeframe. This made it possible to advance the research and reassemble the broad infection sequence:
Through the iMessage service, a message with an attachment containing an exploit is delivered to the target iOS device.
The message initiates a vulnerability that results in code execution without any user input.
The exploit’s code downloads multiple additional stages, including additional exploits for privilege escalation, from the C&C server.
After successful exploitation, a fully functional APT platform is downloaded as the final payload from the C&C server.
The first message and the attachment’s exploit are removed

The lack of persistence support in the harmful toolset is most likely a result of OS restrictions. Multiple devices’ timeframes suggest that after rebooting, they might get infected again. The earliest signs of infection that we found date to 2019. The most recent version of the devices that have been successfully attacked as of the time of writing in June 2023 is iOS 15.7.
The final payload analysis is still ongoing. The programme executes with root rights, implements a set of commands for gathering user and system data, and can run any code downloaded as plugin modules from the C&C server.
Malicious Domains
Using the forensic artefacts, it was possible to identify the domain name set used by the exploits and further malicious stages. They can be used to check the DNS logs for historical information and to identify the devices currently running the malware:
addatamarket[.]net
backuprabbit[.]com
businessvideonews[.]com
cloudsponcer[.]com
datamarketplace[.]net
mobilegamerstats[.]com
snoweeanalytics[.]com
tagclick-cdn[.]com
topographyupdates[.]com
unlimitedteacup[.]com
virtuallaughing[.]com
web-trackers[.]com
growthtransport[.]com
anstv[.]netAns7tv[.]net
Safeguards for iOS users
Despite its world-class safety and privacy architecture, iOS is vulnerable to a few attacks; the following steps can be undertaken to safeguard iOS users –
Keeping Device updated
Security patches
Disabling iMessage would prevent Zero clicks exploits or the Triangulation attacks
Paying zero attention to unwanted, unsolicited messages
The user should make sure that any application they are downloading or installing; it should be from a trusted source ( This Zero click attack does not occur by any other means, It exploits / it targets software vulnerabilities in operating systems networks and applications)
Being cautious with the messaging app and emails
Implement device restrictions (management features like parental control and restrictions over using necessary applications)

Conclusion
Operation Triangulation is one of the recent operations combating cyber attacks, but such operations are launched nearly daily. This is also due to a rapid rise in internet and technology penetration across the world. Cyberattacks have taken a new face as they have evolved with the new and emerging technology. The influence of the Darknet has allowed many hackers to remain on the black hat side due to easy accessibility to illegal tools and material over the dark net, which facilitates such crimes.
.webp)
Introduction
Personalised advertisements deploy a mechanism that derives from the collection of the user’s data. Although it allows for a more tailored user experience, one cannot ignore the method through which this is achieved. Recently, as per a report by the Indian Express on 13th November 2024, Meta has come up with a less personalised ad option on Facebook and Instagram for its users in the European Union (EU). This was done due to the incompatibility of their previous ad offer with the EU’s Digital Markets Act (DMA).
Relevant Legislation
In October 2023, Meta came up with a “Pay or Consent” option for their users in the EU. It gave the users two options: either to pay a monthly subscription fee to avail of the ad-free usage variant of Facebook and Instagram, or to give consent to see personalised ads based on the user’s data. This consent model was introduced in their attempts to comply with the EU’s DMA. However, this was found to be incompatible with the said mandate, according to the EU regulators, as they believed that the users should not only have the option to consent to ads but also have access to less personalised but equivalent alternatives. It is this decision that pushed Meta to come up with less personalised ad options for users in the EU. The less-personalised ad option claims to rely on limited data and show ads that are only based on the context of what is being viewed i.e. during a Facebook or Instagram session requiring a minimum set of data points such as location, age, gender, and the user’s engagement with the ads. However, choosing this option also allows for such ads to be less skippable.
The EU’s Digital Markets Act came into force on November 1, 2022. The purpose was to make the digital marketing sector fairer and in doing so, identify what they consider to be “Gatekeepers” (core platform services such as messenger services, search engines, and app stores) and a list of do’s and don’ts for them. One of them, applicable to the case mentioned above, is the effective consent required by the user in case the gatekeeper decides to target advertisements enabled by tracking the users' activity outside the gatekeeper's core platform services.
The Indian Context
Although no such issues have been raised in India yet, it is imperative to know that in the Indian context, the DPDP (Digital Personal Data Protection) Act 2023 governs personal data regulation. This includes rules for Data Fiduciaries (those who, alone or in partnership with others, determine the means and purpose of processing personal data), the Data Principal (those who give data), Consent Managers, and even rules regarding processing data of children.
CyberPeace Recommendations:
At the level of the user, one can take steps to ensure limited collection of personal data by following the mentioned steps:
- Review Privacy Settings- Reviewing Privacy settings for one’s online accounts and devices is a healthy practice to avoid giving unnecessary information to third-party applications.
- Private Browsing- Browsing through private mode or incognito is encouraged, as it prevents websites from tracking your activity and personal data.
- Using Ad-blockers- Certain websites have a user option to block ads when the user first visits their page. Availing of this prevents spam advertisements from the respective websites.
- Using VPN- Using Virtual Private Networks enables users to hide their IP address and their data to be encrypted, preventing third-party actors from tracking the users' online activities
- Other steps include clearing cookies and cache data and using the location-sharing feature with care.
Conclusion
Meta’s compliance with the EU’s DMA signals that social media platforms cannot circumnavigate their way around rules. Balancing the services provided while respecting user privacy is of the utmost importance. The EU has set precedence for a system that respects this and can be used as an example to help set guidelines for how other countries can continue to deal with similar issues and set standards accordingly.
References
- https://indianexpress.com/article/technology/tech-news-technology/meta-less-personalised-ads-eu-regulatory-demands-9667266/
- https://rainmaker.co.in/blog/view/the-price-of-personalization-how-targeted-advertising-breaches-data-privacy-and-challenges-the-gdprs-shield
- https://www.infosecurity-magazine.com/magazine-features/fines-data-protection-violations/
- https://www.forbes.com/councils/forbestechcouncil/2023/09/01/the-landscape-of-personalized-advertising-efficiency-versus-privacy/
- https://iapp.org/news/a/pay-or-consent-personalized-ads-the-rules-and-whats-next
- https://economictimes.indiatimes.com/news/how-to/how-to-safeguard-privacy-in-the-era-of-personalised-ads/articleshow/102748711.cms?from=mdr
- https://www.business-standard.com/technology/tech-news/facebook-instagram-users-in-europe-can-opt-for-less-personalised-ads-124111201558_1.html
- https://digital-markets-act.ec.europa.eu/about-dma_en

Executive Summary:
The picture of a boy making sand art of Indian Cricketer Virat Kohli spreading in social media, claims to be false. The picture which was portrayed, revealed not to be a real sand art. The analyses using AI technology like 'Hive' and ‘Content at scale AI detection’ confirms that the images are entirely generated by artificial intelligence. The netizens are sharing these pictures in social media without knowing that it is computer generated by deep fake techniques.

Claims:
The collage of beautiful pictures displays a young boy creating sand art of Indian Cricketer Virat Kohli.




Fact Check:
When we checked on the posts, we found some anomalies in each photo. Those anomalies are common in AI-generated images.

The anomalies such as the abnormal shape of the child’s feet, blended logo with sand color in the second image, and the wrong spelling ‘spoot’ instead of ‘sport’n were seen in the picture. The cricket bat is straight which in the case of sand made portrait it’s odd. In the left hand of the child, there’s a tattoo imprinted while in other photos the child's left hand has no tattoo. Additionally, the face of the boy in the second image does not match the face in other images. These made us more suspicious of the images being a synthetic media.
We then checked on an AI-generated image detection tool named, ‘Hive’. Hive was found to be 99.99% AI-generated. We then checked from another detection tool named, “Content at scale”


Hence, we conclude that the viral collage of images is AI-generated but not sand art of any child. The Claim made is false and misleading.
Conclusion:
In conclusion, the claim that the pictures showing a sand art image of Indian cricket star Virat Kohli made by a child is false. Using an AI technology detection tool and analyzing the photos, it appears that they were probably created by an AI image-generated tool rather than by a real sand artist. Therefore, the images do not accurately represent the alleged claim and creator.
Claim: A young boy has created sand art of Indian Cricketer Virat Kohli
Claimed on: X, Facebook, Instagram
Fact Check: Fake & Misleading


