#FactCheck: Old Ukraine Blast Video Falsely Shared as Iran Strike on Israeli Nuclear Site
Executive Summary
A video showing a massive fire and explosion is going viral on social media. The clip shows a large plume of smoke followed by a sudden blast. It is being shared with the claim that it depicts Iran attacking a nuclear reactor in Israel amid the ongoing Iran-Israel conflict. However, research by CyberPeace found that the claim is misleading. The viral video is actually from 2017 and shows a massive explosion at an ammunition depot in Ukraine.
Claim:
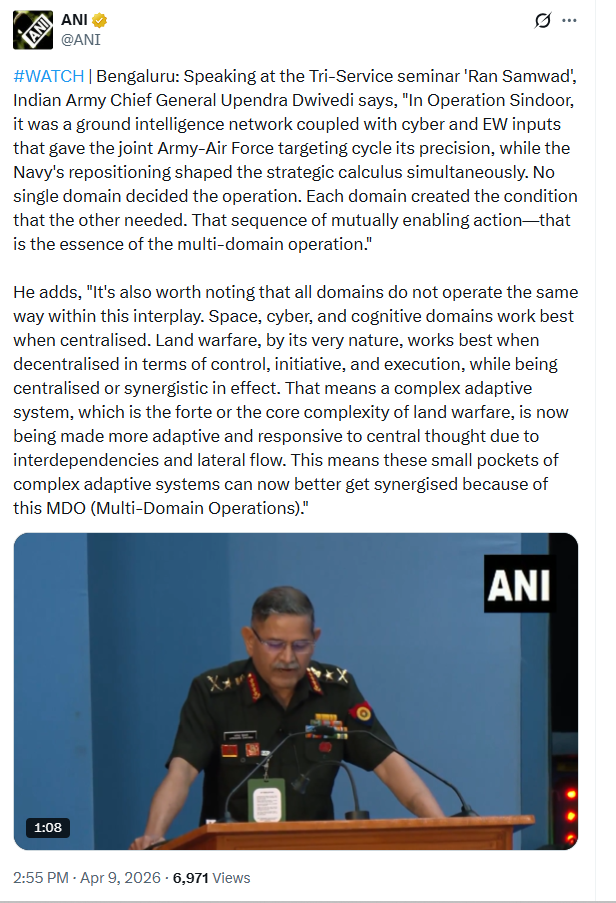
On social media platform X (formerly Twitter), a user shared the video on March 21, 2026, with the caption:“Israel’s nuclear reactor was targeted with Fateh and Khyber missiles. Well done Iran! The whole world is with you.”

Fact Check:
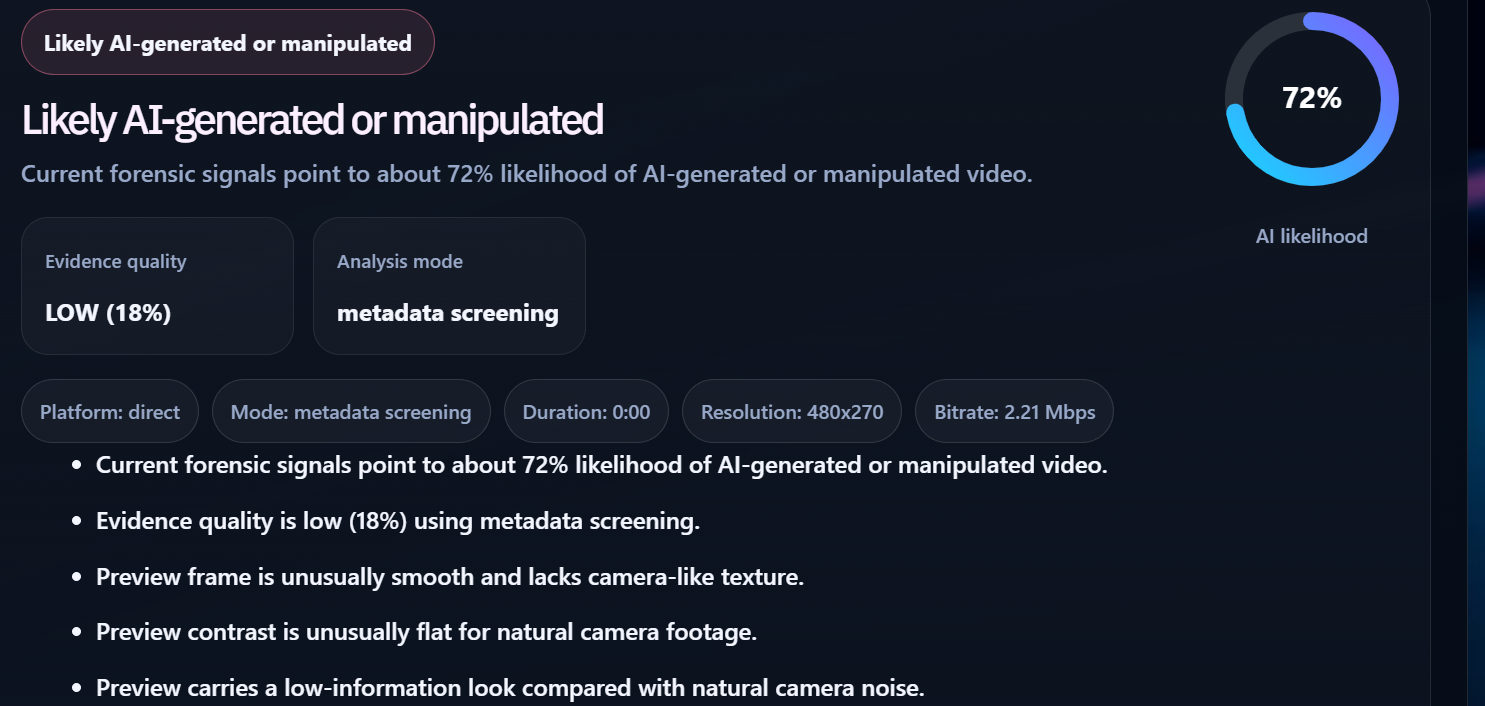
To verify the viral claim, we extracted keyframes from the video and conducted a reverse image search. During this process, we found the same video uploaded on March 23, 2017, on a YouTube channel named “null.” According to the upload, the video shows a massive explosion at an ammunition depot in Balakliya, Ukraine. Using these clues, we performed a keyword search and found a report published on March 24, 2017, by Global News.

According to the report, a major fire and explosion broke out at a large military ammunition depot in Balakliya, located in Ukraine’s Kharkiv region. The incident resulted in one death, while nearly 20,000 people from surrounding areas were evacuated to safer locations.
Conclusion:
The claim that the video shows Iran attacking a nuclear reactor in Israel is misleading. The viral footage is actually from 2017 and depicts an explosion at an ammunition depot in Ukraine.