#FactCheck-Deepfake Video Falsely Shows DRDO Chief Claiming ‘Agni-6 Was Washed with Cow Urine’
Executive Summary
A video of Dr. Samir V. Kamat, Chairman of the Defence Research and Development Organisation (DRDO), is going viral on social media. In the clip, he appears to claim that Prime Minister Narendra Modi instructed scientists to wash the Agni-6 missile with cow urine, and later use a mixture of cow dung and urine to prevent rusting. Research by CyberPeace Research Wing found that the video is a deepfake, created by manipulating original footage using AI tools. It was also shared by an account previously known for posting anti-India misinformation and is reportedly banned in India.
Claim
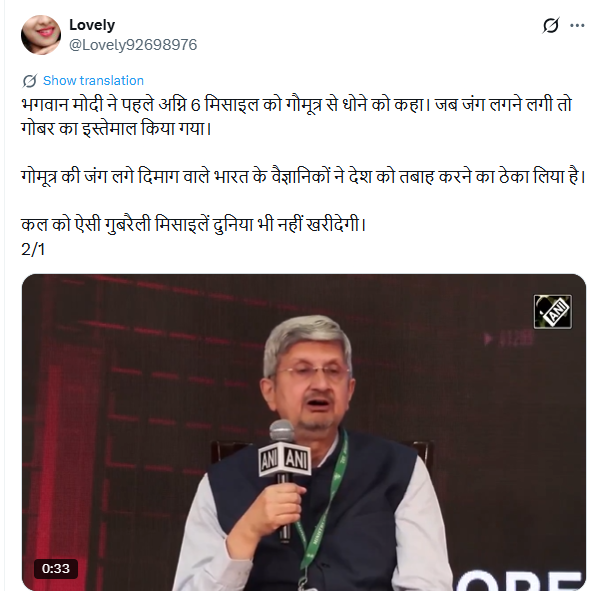
An X user named “Lovely” shared the video on May 1, 2026, alleging that Indian scientists were using cow urine and dung in missile development under government direction. The post used derogatory language and criticized India’s scientific community.
Fact Check
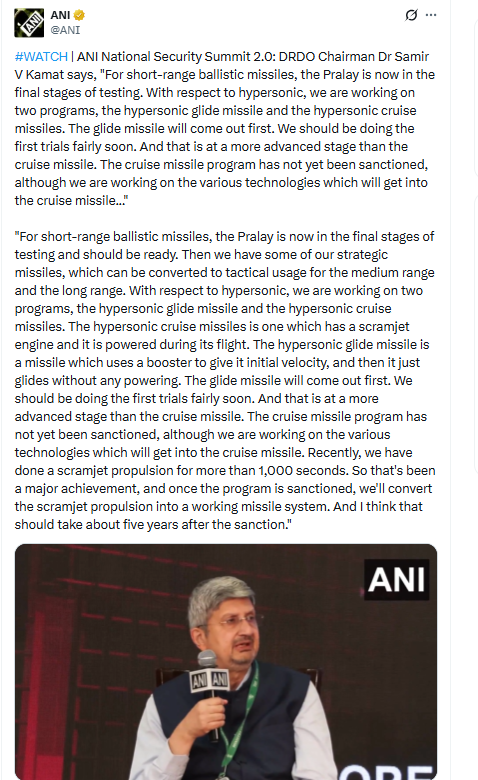
To verify the claim, we searched relevant keywords on Google but found no credible media reports supporting such statements by the DRDO chief. We then extracted keyframes from the viral clip and conducted a reverse image search using Google Lens. This led us to the original video posted by ANI on April 30, 2026. The footage is from the National Security Summit 2.0, where Dr. Kamat spoke about India’s missile development programs.
In the authentic video, Dr. Kamat discusses short-range ballistic missiles like ‘Pralay’, and advancements in hypersonic glide and cruise missile technologies, including scramjet propulsion. There is no mention of cow urine, cow dung, or any such practices.
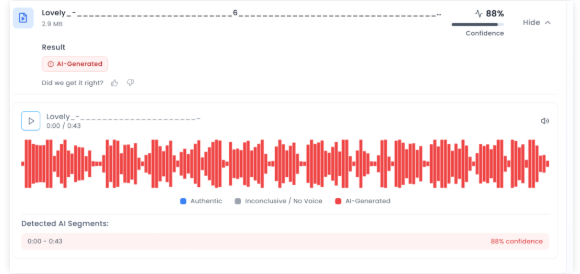
Further analysis using AI detection tool Aurigin indicated an 88% probability that the viral video was AI-generated or manipulated.
Conclusion
Our research confirms that the viral video is fake and AI-manipulated. Dr. Samir V. Kamat never made any statement about washing missiles with cow urine. The clip is a deepfake created to spread misinformation and mislead viewers.
Related Blogs

Executive Summary
Amid rising tensions involving Iran, Israel and the United States following reports in early April 2026 that Iran had shot down an American fighter aircraft, a picture is going viral on social media claiming to show Iranian soldiers standing beside the wreckage of a destroyed helicopter while holding the Iranian flag. Research by CyberPeace Research Wing found that the viral claim is false. The image has been created using artificial intelligence and does not depict any real incident. The picture was generated using Google AI tools and is being misleadingly circulated online with different claims.
Claim
A Facebook page named “official salman 09” shared the image on May 1, 2026, along with a lengthy caption describing the scene as a symbol of Iran’s battlefield success. The post portrayed the image as evidence of a helicopter being brought down during ongoing tensions in the Middle East and suggested that the photo reflected strength, morale and victory in war.
- https://www.facebook.com/permalink.phpstory_fbid=pfbid02TAac6JwZha2UU4T8QiCGq4ENmsnNSwvigaz3vKxr9UWLbhghNsnMMpZdQ3dUuQ1rl&id=100092392280139
- https://archive.ph/

Fact Check
To verify the authenticity of the image, we first conducted a reverse image search using Google Lens. The image did not appear in any credible news reports or authentic media coverage. Instead, it was found circulating mainly on social media platforms, raising suspicion about its authenticity. We then analyzed the image using Google’s SynthID detector. The analysis confirmed the presence of a SynthID watermark with a “very high confidence” score, indicating that the image had been generated using Google AI tools. SynthID is Google’s watermarking technology used to identify AI-generated content created through its models.

Further verification using another AI-detection platform, Hive Moderation, also indicated a high probability that the image had been generated using AI. The tool identified Gemini as the likely source and assessed the image as overwhelmingly AI-generated.

Conclusion
Our research confirms that the viral image is AI-generated and unrelated to any real-world event. The picture showing soldiers holding the Iranian flag near helicopter wreckage was created using Google AI tools and is being falsely shared on social media to spread misleading claims.

Introduction
The ramifications of cybercrime can be far-reaching. Depending on the size of the attack, even entire countries can be affected if their critical infrastructure is connected to the internet. The vast majority of security breaches start within the perimeter and most internet attacks are socially engineered. Unwittingly trusting any email or web request from an unknown sender creates a potential danger for those organisations that depend on the Internet for their business functions. In this ever-evolving digital downtown yet another group has emerged from its darkest corners of targeting the UK’s very bastion of British and global heritage; a treasure trove of around 14 million volumes, ancient manuscripts, in the precious British Library. A group self-identified as Rhysida. Their bold maneuver, executed with the stealth of seasoned cyber brigands, has cast a shadow as long and dark as those found in the Gothic novels that rest on the library's shelves. The late October cyber-attack has thrust the British Library into an unnerving state of chaos, a situation more commonly aligned with works of dystopian fiction than the everyday reality of a revered institution.
The Modus Operandi
The gang uses all-new Rhysida ransomware to jeopardize Virtual Private Networks, which is typically used by library staff to gain access to their employee’s systems remotely. The Ransomware presents itself as a regular decoy file in a familiar fashion as regular phishing attacks in an email, tricking its victim and downloading itself into the host system. Once the malware enters the system it stays dormant and lurks around the system for a period of time. The new malware has significantly reduced the dwell time from 4 days to less than 24 hours which enables it to evade periodic system checks to avoid detection.
Implications of Cyber Attack
Implications of the cyber-attack have been sobering and multifaceted. The library's systems, which serve as the lifeline for countless scholars, students, and the reading public, were left in disarray, unsettlingly reminiscent of a grand mansion invaded by incorporeal thieves. The violation has reverberated through the digital corridors of this once-impenetrable fortress, and the virtual aftershocks are ongoing. Patrons, who traverse a diverse spectrum of society, but share a common reverence for knowledge, received unsettling news: the possibility that their private data has been compromised—a sanctity breached, revealing yet again how even the most hallowed of spaces are not impervious to modern threats.
It is with no small sense of irony that we consider the nature of the stolen goods—names, email addresses, and the like. It is not the physical tomes of inestimable value that have been ransacked, but rather the digital footprints of those who sought the wisdom within the library's walls. This virtual Pandora's Box, now unleashed onto the dark web, has been tagged with a monetary value. Rhysida has set the ominous asking price of a staggering $740,000 worth of cryptocurrency for the compromised data, flaunting their theft with a hubris that chills the spine.
Yet, in this convoluted narrative unfolds a subplot that offers some measure of consolation. Payment information purports the library has not been included in this digital heist, offering a glint of reassurance amidst the prevailing uncertainty. This digital storm has had seismic repercussions: the library's website and interconnected systems have been besieged and access to the vast resources significantly hampered. The distressing notice of a 'major technology outage' transformed the digital facade from a portal for endless learning to a bulletin of sorrow, projecting the sombre message across virtual space.
The Impact
The impact of this violation will resonate far beyond the mere disruption of services; it signals the dawn of an era where venerable institutions of culture and learning must navigate the depths of cybersecurity. As the library grapples with the breach, a new front has opened in the age-old battle for the preservation of knowledge. The continuity of such an institution in a digitised world will be tested, and the outcome will define the future of digital heritage management. As the institution rallies, led by Roly Keating, its Chief Executive, one observes not a defeatist retreat, but a stoic, strategic regrouping. Gratitude is extended to patrons and partners whose patience has become as vital a resource as the knowledge the library preserves. The reassurances given, while acknowledging the laborious task ahead, signal not just an intention to repair but to fortify, to adapt, to evolve amidst adversity.
This wretched turn of events serves as a portentous reminder that threats to our most sacred spaces have transformed. The digital revolution has indeed democratised knowledge but has also exposed it to neoteric threats. The British Library, a repository of the past, must now confront a distinctly modern adversary. It requires us to posit whether our contemporary guardians of history are equipped to combat those who wield malicious code as their weapons of choice.
Best Practices for Cyber Resilience
It is crucial to keep abreast with recent developments in cyberspace and emerging trends. Libraries in the digital age must ensure the protection of their patron’s data by applying comprehensive security protocols to safeguard the integrity, availability and confidentiality of sensitive information of their patrons. A few measures that can be applied by libraries include.
- Secured Wi-Fi networks: Libraries offering public Wi-Fi facilities must secure them with strong encryption protocols such as WPA 3. Libraries should establish separate networks for internal operations allowing separation of staff and public networks to protect sensitive information.
- Staff Training Programs: To avoid human error it is imperative that comprehensive training programs are conducted on a regular basis to generate greater awareness of cyber threats among staff and educate them about best practices of cyber hygiene and data security.
- Data Backups and Recovery Protocols: Patrons' sensitive data should be updated and backed up regularly. Proper verification of the user’s data integrity is crucial and should be stored securely in a dedicated repository to ensure full recovery of the user’s data in the event of a breach.
- Strong Authentication: Strong authentication to enhance library defenses is crucial to combat cyber threats. Staff and Patrons should be educated on strong password usage and the implementation of Multi-Factor Authentication to add an extra layer of security.
Conclusion
Finally, whatever the future holds, what remains unassailable is the cultural edifice that is the British Library. Its trials and tribulations, like those of the volumes it safeguards, become a part of a larger narrative of endurance and defiance. In the canon of history—filled with conflicts and resolutions—the library, like the lighter anecdotes and tragic tales it harbours, will decidedly hold its place. And perhaps, with some assurance, we might glean from the sentiment voiced by Milton—an assurance that the path from turmoil to enlightenment, though fraught with strenuous challenges, is paved with lessons learned and resilience rediscovered. Cyberspace is constantly evolving hence it is in our best interest to keep abreast of all developments in this digital sphere. Maximum threats can be avoided if we are vigilant.
References:

Introduction
The Pahalgam terror attack, which took place on April 22, 2025, was a tragic incident that shook the nation. The National Investigation Agency (NIA) formally took over the Pahalgam terrorist attack case on Sunday, April 27, 2025. Following India's strikes on Pakistan, tensions between the two countries have heightened, leading to concerns about potential escalation, including the risk of cyber attacks and the spread of misinformation that could further complicate the situation. It is crucial for corporations, critical sectors, and all netizens in India to stay proactive and vigilant against cyber attacks, while also being cautious of the risks of misinformation. This includes protecting themselves from being affected and avoiding the inadvertent or deliberate spread of false information.
Be Careful with the Information You Consume and Share
It is crucial to note that the Press Information Bureau (PIB) has alerted citizens to stay cautious of fake narratives being circulated by Pakistani handles. Through an official fact check, PIB debunked several misleading claims aimed at undermining India’s internal stability and security forces. Citizens are urged to verify any suspicious content via PIB Fact Check before sharing it further. As social media becomes a hub for viral content, netizens must be cautious about the information they consume and share. Misleading information, old videos, false claims, and misinformation flood the platform, making it essential to be mindful of the content you consume and share, as spreading unverified content can have severe consequences.
CyberPeace Recommends Following Crucial Cyber Safety Tips to Stay Vigilant Against Potential Digital Threats:
- Do not open/download any video file you receive in social media groups or from unknown sources.
- As per several media reports, a video file named "Dance of the Hilary" is being circulated, which may be intended for a cyber attack on India. Please refrain from clicking, downloading, or sharing any such file. Additionally, there are reports of suspicious files circulating on WhatsApp, including tasksche.exe, OperationSindoor.ppt, and OperationSindhu.pptx. Do not download or open any of these files, as they may pose a serious cyber threat.
- To receive accurate alerts, you can enable government notifications on your iPhone. Go to Settings > Notifications and scroll down to Government Alerts. Make sure all the toggles under Government Alerts are turned on. This will allow you to receive timely information and important alerts from government agencies, and your device will display critical notifications to keep you informed and safe.
- Turn off automatic media download in WhatsApp to reduce the risk of downloading potentially harmful files.
- To protect your privacy, disable location services on apps like WhatsApp, Instagram, Snapchat, and X unless absolutely necessary.
- Refrain from sharing sensitive information like government data, confidential details, or personal records on unsecured devices or networks.
- To avoid misinformation and manipulation during conflict, verifying and cross-checking the news before sharing it with anyone is crucial. Stay updated with official news updates, and be cautious while sharing information.
Conclusion
In times of heightened tensions, all of us need to stay vigilant, protect our digital spaces, and verify the information we encounter. Together, we can safeguard ourselves from cyber threats and misinformation, ensuring the safety, stability, and digital security of our nation. As proud citizens, let us unite to protect both our physical and digital well-being.
References
- https://www.thehindu.com/news/national/pakistan-has-unleashed-propaganda-machine-in-response-to-successful-operation-sindoor-ib-ministry/article69549084.ece
- https://sambadenglish.com/national-international-news/india/centre-asks-people-to-stay-alert-against-misinformation-in-social-media-9048169
- https://www.youtube.com/watch?v=gLHo_Vd1_H0&t=19s


