#FactCheck : AI Video Falsely Shows Iran Destroying Israeli Military Base
Executive Summary
Amid the ongoing conflict involving the US-Israel and Iran in West Asia, a video showing destroyed aircraft at an airport is going viral on social media. The clip is being shared with the claim that it shows an Israeli military base destroyed in an Iranian attack. However, an research by the CyberPeacen found that the viral video is not real but AI-generated.
Claim:
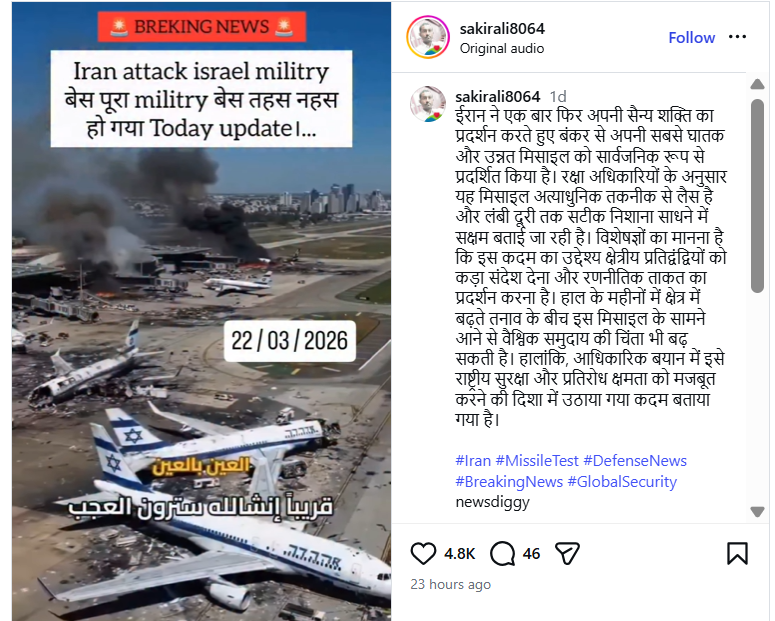
An Instagram user “sakirali8064” shared the video on March 22, 2026, claiming that Iran had demonstrated its military strength by deploying advanced missiles capable of long-range precision strikes.The video also carries a “Breaking News” overlay stating:“Iran attack Israel military base… the entire base destroyed.
Post link and archive link:
Fact Check:
To verify the claim, we extracted keyframes from the viral clip and conducted a reverse image search using Google Lens. We found a longer version of the same video posted on March 5, 2026, by a Facebook user named “With INC,” where it was also falsely linked to an Iranian attack on Israel’s Ben Gurion Airport.

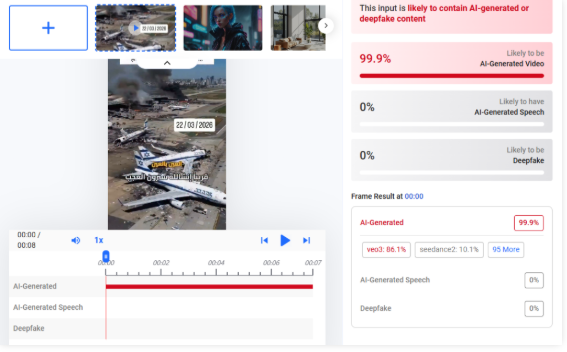
Upon closely examining the video, we observed inconsistencies such as fire changing positions unnaturally, which raised suspicion of AI manipulation. We then analyzed the video using Hive Moderation, which indicated a probability of over 99% that the content is AI-generated.
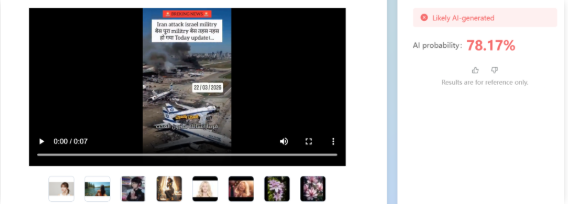
Additionally, analysis using Tencent’s “Zhuque AI” detection tool suggested more than 78% likelihood of the video being AI-generated.
Conclusion:
The viral video claiming that an Iranian attack destroyed an Israeli military base is AI-generated and misleading. While Iran has claimed to have targeted Israel’s Ben Gurion International Airport using drones, the viral footage does not depict a real event.
Related Blogs

Introduction
According to a new McAfee survey, 88% of American customers believe that cybercriminals will utilize artificial intelligence to "create compelling online scams" over the festive period. In the meanwhile, 31% believe it will be more difficult to determine whether messages from merchants or delivery services are genuine, while 57% believe phishing emails and texts will be more credible. The study, which was conducted in September 2023 in the United States, Australia, India, the United Kingdom, France, Germany, and Japan, yielded 7,100 responses. Some people may decide to cut back on their online shopping as a result of their worries about AI; among those surveyed, 19% stated they would do so this year.
In 2024, McAfee predicts a rise in AI-driven scams on social media, with cybercriminals using advanced tools to create convincing fake content, exploiting celebrity and influencer identities. Deepfake technology may worsen cyberbullying, enabling the creation of realistic fake content. Charity fraud is expected to rise, leveraging AI to set up fake charity sites. AI's use by cybercriminals will accelerate the development of advanced malware, phishing, and voice/visual cloning scams targeting mobile devices. The 2024 Olympic Games are seen as a breeding ground for scams, with cybercriminals targeting fans for tickets, travel, and exclusive content.
AI Scams' Increase on Social Media
Cybercriminals plan to use strong artificial intelligence capabilities to control social media by 2024. These applications become networking goldmines because they make it possible to create realistic images, videos, and audio. Anticipate the exploitation of influencers and popular identities by cybercriminals.
AI-powered Deepfakes and the Rise in Cyberbullying
The negative turn that cyberbullying might take in 2024 with the use of counterfeit technology is one trend to be concerned about. This cutting-edge technique is freely accessible to youngsters, who can use it to produce eerily convincing synthetic content that compromises victims' privacy, identities, and wellness.
In addition to sharing false information, cyberbullies have the ability to alter public photographs and re-share edited, detailed versions, which exacerbates the suffering done to children and their families. The study issues a warning, stating that deepfake technology would probably cause online harassment to take a negative turn. With this sophisticated tool, young adults may now generate frighteningly accurate synthetic content in addition to using it for fun. The increasing severity of these deceptive pictures and phrases can cause serious, long-lasting harm to children and their families, impairing their identity, privacy, and overall happiness.
Evolvement of GenAI Fraud in 2023
We simply cannot get enough of these persistent frauds and fake emails. People in general are now rather adept at [recognizing] those that are used extensively. But if they become more precise, such as by utilizing AI-generated audio to seem like a loved one's distress call or information that is highly personal to the person, users should be much more cautious about them. The rise in popularity of generative AIs brings with it a new wrinkle, as hackers can utilize these systems to refine their attacks:
- Writing communications more skillfully in order to deceive consumers into sending sensitive information, clicking on a link, or uploading a file.
- Recreate emails and business websites as realistically as possible to prevent arousing concern in the minds of the perpetrators.
- People's faces and voices can be cloned, and deepfakes of sounds or images can be created that are undetectable to the target audience. a problem that has the potential to greatly influence schemes like CEO fraud.
- Because generative AIs can now hold conversations, and respond to victims efficiently.
- Conduct psychological manipulation initiatives more quickly, with less money spent, and with greater complexity and difficulty in detecting them. AI generative already in use in the market can write texts, clone voices, or generate images and program websites.
AI Hastens the Development of Malware and Scams
Even while artificial intelligence (AI) has many uses, cybercriminals are becoming more and more dangerous with it. Artificial intelligence facilitates the rapid creation of sophisticated malware, illicit web pages, and plausible phishing and smishing emails. As these risks become more accessible, mobile devices will be attacked more frequently, with a particular emphasis on audio and visual impersonation schemes.
Olympic Games: A Haven for Scammers
The 2024 Olympic Games are seen as a breeding ground for scams, with cybercriminals targeting fans for tickets, travel, and exclusive content. Cybercriminals are skilled at profiting from big occasions, and the buzz that will surround the 2024 Olympic Games around the world will make it an ideal time for scams. Con artists will take advantage of customers' excitement by focusing on followers who are ready to purchase tickets, arrange travel, obtain special content, and take part in giveaways. During this prominent event, vigilance is essential to avoid an invasion of one's personal records and financial data.
Development of McAfee’s own bot to assist users in screening potential scammers and authenticators for messages they receive
Precisely such kind of technology is under the process of development by McAfee. It's critical to emphasize that solving the issue is a continuous process. AI is being manipulated by bad actors and thus, one of the tricksters can pull off is to exploit the fact that consumers fall for various ruses as parameters to train advanced algorithms. Thus, the con artists may make use of the gadgets, test them on big user bases, and improve with time.
Conclusion
According to the McAfee report, 88% of American customers are consistently concerned about AI-driven internet frauds that target them around the holidays. Social networking poses a growing threat to users' privacy. By 2024, hackers hope to take advantage of AI skills and use deepfake technology to exacerbate harassment. By mimicking voices and faces for intricate schemes, generative AI advances complex fraud. The surge in charitable fraud affects both social and financial aspects, and the 2024 Olympic Games could serve as a haven for scammers. The creation of McAfee's screening bot highlights the ongoing struggle against developing AI threats and highlights the need for continuous modification and increased user comprehension in order to combat increasingly complex cyber deception.
References
- https://www.fonearena.com/blog/412579/deepfake-surge-ai-scams-2024.html
- https://cxotoday.com/press-release/mcafee-reveals-2024-cybersecurity-predictions-advancement-of-ai-shapes-the-future-of-online-scams/#:~:text=McAfee%20Corp.%2C%20a%20global%20leader,and%20increasingly%20sophisticated%20cyber%20scams.
- https://timesofindia.indiatimes.com/gadgets-news/deep-fakes-ai-scams-and-other-tools-cybercriminals-could-use-to-steal-your-money-and-personal-details-in-2024/articleshow/106126288.cms
- https://digiday.com/media-buying/mcafees-cto-on-ai-and-the-cat-and-mouse-game-with-holiday-scams/

Introduction
Criminal justice in India is majorly governed by three laws which are – Indian Penal Code, Criminal Procedure Code and Indian Evidence Act. The centre, on 11th August 2023’ Friday, proposes a new bill in parliament Friday, which is replacing the country’s major criminal laws, i.e. Indian Penal Code, Criminal Procedure Code and Indian Evidence Act.
The following three bills are being proposed to replace major criminal laws in the country:
- The Bharatiya Nyaya Sanhita Bill, 2023 to replace Indian Penal Code 1860.
- The Bharatiya Nagrik Suraksha Sanhita Bill, 2023, to replace The Code Of Criminal Procedure, 1973.
- The Bharatiya Sakshya Bill, 2023, to replace The Indian Evidence Act 1872.
Cyber law-oriented view of the new shift in criminal lawNotable changes:Bharatiya Nyaya Sanhita Bill, 2023 Indian Penal Code 1860.
Way ahead for digitalisation
The new laws aim to enhance the utilisation of digital services in court systems, it facilitates online registration of FIR, Online filing of the charge sheet, serving summons in electronic mode, trial and proceedings in electronic mode etc. The new bills also allow the virtual appearance of witnesses, accused, experts, and victims in some instances. This shift will lead to the adoption of technology in courts and all courts to be computerised in the upcoming time.
Enhanced recognition of electronic records
With the change in lifestyle in terms of the digital sphere, significance is given to recognising electronic records as equal to paper records.
Conclusion
The criminal laws of the country play a significant role in establishing law & order and providing justice. The criminal laws of India were the old laws existing under British rule. There have been several amendments to criminal laws to deal with the growing crimes and new aspects. However, there was a need for well-established criminal laws which are in accordance with the present era. The step of the legislature by centralising all criminal laws in their new form and introducing three bills is a good approach which will ultimately strengthen the criminal justice system in India, and it will also facilitate the use of technology in the court system.

Introduction
The nation got its first consolidated data protection regulation in the form of the Digital Personal Data Protection Act, 2023, in the month of August, and the Indian netizens got their independence in terms of data protection and privacy. The act lays heavy penalties for non-compliance with the provisions, and the same is under the jurisdiction of a Data Protection Board set up by the Central Government, which enjoys powers equivalent to a civil court. The act upholds the right to data privacy as the fundamental right under Article 19 (1)(A) and 21 of the Constitution of India. The same has been judicially supported in the form of the landmark judgement, Jus. K.S Puttawamy vs. Union of India of 2018. Let us take a look at the impact the act will make on the Indian netizens.
What is Personal Data?
Personal Data refers to any form of digitised data which can be directly replicated by any person. This includes email IDs, mobile numbers, health data, banking data, photos, etc. A person to whom the personal data belongs is called the Data Principle. A Data principle is anyone who is above the age of 18 years and consents to the data of children/minors. In the case of children/minors, it is mandatory for the parents or guardians to provide their express consent for the processing of personal data for all or any purposes. Any individual who is processing personal data is known as the Data Fiduciry, and individuals registered under the act may act as consent managers to make the consent transparent. When it comes to the rights of the netizens, it is seen that the act is created with an aspect of “Safety by Design” to secure the rights and responsibilities of the netizens.
Rights secured under the DPDP Act 2023
- Right to Grievance Redressal: The Data fiduciary and the consent manager are required to respond to the grievances of the Data Principal within a time period, which is soon to be prescribed, thus creating a blanket of responsibility for the data fiduciary and consent manager.
- Right to Nominate: Data Principals have the right to nominate any other individual who shall, in the event of death or incapacity of the data principal, exercise his/her rights.
- Right to access to information: The Data principal has the right to seek confirmation from Data fiduciaries regarding the processing of their personal data and the summary of the processed data as well.
- Right to Erasure and Correction: Data principals can reach out to the data fiduciaries in order to exercise their right to correct, complete, update and erasure of their personal data.
- Territorial Rights: The data is to be processed within India, and processing outside India should be in regard to the services provided in India.
- Material Rights: The rights are applicable to any personal data collected in digitised form and also for the data collected in a non-digital form but subsequently digitised.
Obligations for Data Fiduciaries
The data fiduciaries are mandated to oblige with the following provisions in order to maintain compliance with the laws of the land and by securing the Digital rights of the netizens.
These are the obligations of the data fiduciaries:
- Implement technical and organisational measures to safeguard Personal Data.
- Determine the legal grounds for processing and obtaining consent from Data principals where required.
- Provide a privacy notice while obtaining consent from Data principals.
- Implement a mechanism for data principals to exercise their rights.
- Implement a grievance redressal mechanism for handling the queries from Data principals.
- Irrecoverably delete personal data after the purpose for which it was collected has expired or when the consent has been withdrawn.
- Have a breach management policy to notify the data protection board and the data principals in accordance with prescribed timelines.
- Sign a valid contract with Data processors to ensure key obligations are abided by them, including timely deletion of data.
Conclusion
As the world steps into the digital age, it is pertinent for the governments of the world to come up with efficient and effective legislation to protect cyber rights and responsibilities, but as cyberspace has no boundaries, nations need to work in synergy to protect their cyber interests and netizens. This can only begin once all nations have indigenous Cyber laws and rights to protect netizens, and the same has been addressed by the Indian Government in the form of the Digital Perosnl Data Protection Act, 2023. The future is full of emerging technologies and the evolution of cyber laws; hence, consolidating a basic legal structure now is of utmost importance and the same is expected to be strengthened in India by the soon-to-be-released Draft Digital India Bill.


