#FactCheck -AI-Generated Video Falsely Shows PM Modi Praising Christianity
Executive Summary:
A video of Prime Minister Narendra Modi is going viral across multiple social media platforms. In the clip, PM Modi is purportedly heard praising Christianity and stating that only Jesus Christ can lead people to heaven.Several users are sharing and commenting on the video, believing it to be genuine. The CyberPeace researched the viral claim and found it to be false. The circulating video has been created using artificial intelligence (AI).
Claim:
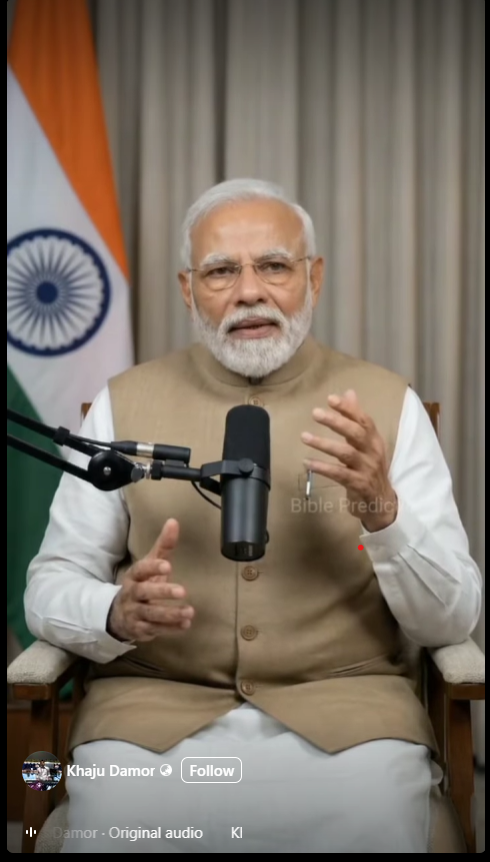
On January 29, 2026, a Facebook user named ‘Khaju Damor’ posted the viral video of PM Modi. The post gained traction, with many users sharing and commenting on it as if it were authentic. (Links and archived versions provided)
Fact Check:
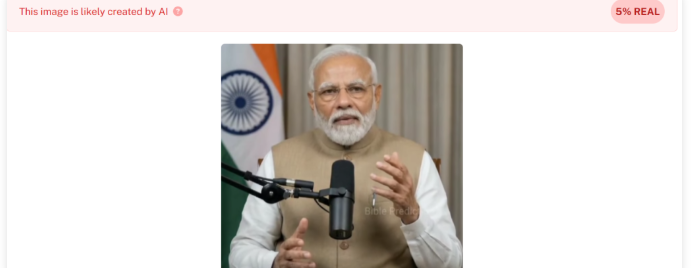
As part of our research , we first closely examined the viral video. Upon careful observation, several inconsistencies were noticed. The Prime Minister’s facial expressions and hand movements appeared unnatural. The lip-sync and overall visual presentation also raised suspicions about the clip being digitally manipulated. To verify this further, we analyzed the video using the AI detection tool Hive Moderation. The tool’s analysis indicated a 99% probability that the video was AI-generated.
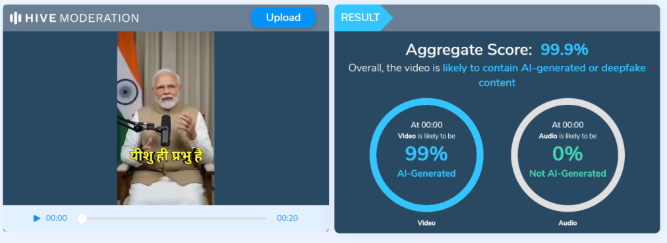
To independently confirm the findings, we also ran the clip through another detection platform, Undetectable.ai. Its analysis likewise indicated a very high likelihood that the video was created using artificial intelligence.
Conclusion:
Our research confirms that the viral video of Prime Minister Narendra Modi praising Christianity and making the alleged statement about heaven is fake. The clip has been generated using AI tools and does not depict a real statement made by the Prime Minister.
Related Blogs

Executive Summary
A photograph showing Union Education Minister Dharmendra Pradhan standing with a woman is being widely circulated on social media. Users are falsely claiming that the woman in the image is Manisha Mandhare, a teacher allegedly arrested in the NEET-UG paper leak case. CyberPeace Research Wing research confirms that the woman in the viral photograph is Dr. Nivedita Ekbote and not Manisha Mandhare. Social media users are falsely misidentifying her and linking her to the NEET paper leak case without evidence.
Claim
Several social media users, including Facebook and Instagram pages, have shared the image claiming that the woman seen with the Union Minister is Manisha Mandhare, who was arrested in connection with the NEET paper leak case.
- https://www.facebook.com/Sri.Media.Kannada/posts/pfbid0pCuJrhcz3mcf8MzYci4oWXaTKvaJYNjCtGo34Z6R9ztshWqs3QUupyHNu2K4Rodpl?rdid=WtnRhDM22ftHT9oe
- https://archive.is/uwmsj

Fact Check
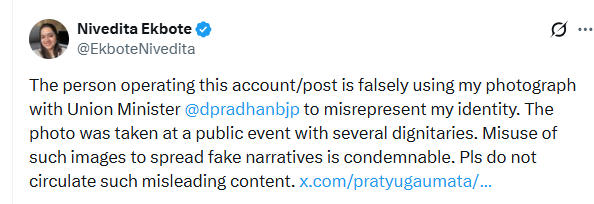
A reverse image search of the viral photograph reveals that the woman is actually Dr. Nivedita Ekbote, Principal of Modern College and Vice President of the Bharatiya Janata Yuva Morcha in Maharashtra. Nivedita Ekbote originally shared this photograph on December 18, 2024, across her official social media accounts on X (formerly Twitter), Facebook, and Instagram. According to the caption, the image was taken during the Pune Book Festival, where she met the Union Education Minister along with her parents.

In a public clarification, she stated that her photograph was being misused online. She added that the image was taken at a public event with several dignitaries and strongly condemned the circulation of false and misleading claims using it.
- https://x.com/EkboteNivedita/status/2056265520765399049?s=20
Further verification from credible news reports confirms that Manisha Mandhare, who is linked to the NEET paper leak case, is a senior botany teacher from Pune. She was reportedly appointed as a subject expert by the National Testing Agency (NTA) for NEET-related processes. Her identity is completely different from the woman seen in the viral image.

Conclusion
The viral claim is completely false and misleading. The woman seen with Union Education Minister Dharmendra Pradhan is Dr. Nivedita Ekbote, and she has no connection to the NEET-UG paper leak case.

Introduction
According to a new McAfee survey, 88% of American customers believe that cybercriminals will utilize artificial intelligence to "create compelling online scams" over the festive period. In the meanwhile, 31% believe it will be more difficult to determine whether messages from merchants or delivery services are genuine, while 57% believe phishing emails and texts will be more credible. The study, which was conducted in September 2023 in the United States, Australia, India, the United Kingdom, France, Germany, and Japan, yielded 7,100 responses. Some people may decide to cut back on their online shopping as a result of their worries about AI; among those surveyed, 19% stated they would do so this year.
In 2024, McAfee predicts a rise in AI-driven scams on social media, with cybercriminals using advanced tools to create convincing fake content, exploiting celebrity and influencer identities. Deepfake technology may worsen cyberbullying, enabling the creation of realistic fake content. Charity fraud is expected to rise, leveraging AI to set up fake charity sites. AI's use by cybercriminals will accelerate the development of advanced malware, phishing, and voice/visual cloning scams targeting mobile devices. The 2024 Olympic Games are seen as a breeding ground for scams, with cybercriminals targeting fans for tickets, travel, and exclusive content.
AI Scams' Increase on Social Media
Cybercriminals plan to use strong artificial intelligence capabilities to control social media by 2024. These applications become networking goldmines because they make it possible to create realistic images, videos, and audio. Anticipate the exploitation of influencers and popular identities by cybercriminals.
AI-powered Deepfakes and the Rise in Cyberbullying
The negative turn that cyberbullying might take in 2024 with the use of counterfeit technology is one trend to be concerned about. This cutting-edge technique is freely accessible to youngsters, who can use it to produce eerily convincing synthetic content that compromises victims' privacy, identities, and wellness.
In addition to sharing false information, cyberbullies have the ability to alter public photographs and re-share edited, detailed versions, which exacerbates the suffering done to children and their families. The study issues a warning, stating that deepfake technology would probably cause online harassment to take a negative turn. With this sophisticated tool, young adults may now generate frighteningly accurate synthetic content in addition to using it for fun. The increasing severity of these deceptive pictures and phrases can cause serious, long-lasting harm to children and their families, impairing their identity, privacy, and overall happiness.
Evolvement of GenAI Fraud in 2023
We simply cannot get enough of these persistent frauds and fake emails. People in general are now rather adept at [recognizing] those that are used extensively. But if they become more precise, such as by utilizing AI-generated audio to seem like a loved one's distress call or information that is highly personal to the person, users should be much more cautious about them. The rise in popularity of generative AIs brings with it a new wrinkle, as hackers can utilize these systems to refine their attacks:
- Writing communications more skillfully in order to deceive consumers into sending sensitive information, clicking on a link, or uploading a file.
- Recreate emails and business websites as realistically as possible to prevent arousing concern in the minds of the perpetrators.
- People's faces and voices can be cloned, and deepfakes of sounds or images can be created that are undetectable to the target audience. a problem that has the potential to greatly influence schemes like CEO fraud.
- Because generative AIs can now hold conversations, and respond to victims efficiently.
- Conduct psychological manipulation initiatives more quickly, with less money spent, and with greater complexity and difficulty in detecting them. AI generative already in use in the market can write texts, clone voices, or generate images and program websites.
AI Hastens the Development of Malware and Scams
Even while artificial intelligence (AI) has many uses, cybercriminals are becoming more and more dangerous with it. Artificial intelligence facilitates the rapid creation of sophisticated malware, illicit web pages, and plausible phishing and smishing emails. As these risks become more accessible, mobile devices will be attacked more frequently, with a particular emphasis on audio and visual impersonation schemes.
Olympic Games: A Haven for Scammers
The 2024 Olympic Games are seen as a breeding ground for scams, with cybercriminals targeting fans for tickets, travel, and exclusive content. Cybercriminals are skilled at profiting from big occasions, and the buzz that will surround the 2024 Olympic Games around the world will make it an ideal time for scams. Con artists will take advantage of customers' excitement by focusing on followers who are ready to purchase tickets, arrange travel, obtain special content, and take part in giveaways. During this prominent event, vigilance is essential to avoid an invasion of one's personal records and financial data.
Development of McAfee’s own bot to assist users in screening potential scammers and authenticators for messages they receive
Precisely such kind of technology is under the process of development by McAfee. It's critical to emphasize that solving the issue is a continuous process. AI is being manipulated by bad actors and thus, one of the tricksters can pull off is to exploit the fact that consumers fall for various ruses as parameters to train advanced algorithms. Thus, the con artists may make use of the gadgets, test them on big user bases, and improve with time.
Conclusion
According to the McAfee report, 88% of American customers are consistently concerned about AI-driven internet frauds that target them around the holidays. Social networking poses a growing threat to users' privacy. By 2024, hackers hope to take advantage of AI skills and use deepfake technology to exacerbate harassment. By mimicking voices and faces for intricate schemes, generative AI advances complex fraud. The surge in charitable fraud affects both social and financial aspects, and the 2024 Olympic Games could serve as a haven for scammers. The creation of McAfee's screening bot highlights the ongoing struggle against developing AI threats and highlights the need for continuous modification and increased user comprehension in order to combat increasingly complex cyber deception.
References
- https://www.fonearena.com/blog/412579/deepfake-surge-ai-scams-2024.html
- https://cxotoday.com/press-release/mcafee-reveals-2024-cybersecurity-predictions-advancement-of-ai-shapes-the-future-of-online-scams/#:~:text=McAfee%20Corp.%2C%20a%20global%20leader,and%20increasingly%20sophisticated%20cyber%20scams.
- https://timesofindia.indiatimes.com/gadgets-news/deep-fakes-ai-scams-and-other-tools-cybercriminals-could-use-to-steal-your-money-and-personal-details-in-2024/articleshow/106126288.cms
- https://digiday.com/media-buying/mcafees-cto-on-ai-and-the-cat-and-mouse-game-with-holiday-scams/

Introduction
In the digital entertainment world, OTT platforms have become highly popular and have attracted larger audiences. They offer a wide variety of entertaining content. However, there are certain concerns about depicting illicit or objectionable content on such platforms. The Indian Ministry of Information and Broadcasting (I&B) has been working on tackling issues like the availability of obscene content on online streaming platforms and other platforms. I&B Ministry has taken important steps to prevent the spread of such illicit or objectionable content.
The I&B Ministry has taken action against obscene and vulgar content on OTT platforms. A total 18 OTT platforms and several associated websites, apps, and social media handles have been blocked nationwide. The government has been in consistent talks with these platforms and issued several advisories, but they have not been adhered to. The decision was made after consultation with other ministries, domain experts, and industry bodies. The content allegedly obscene was found to depict nudity, sexual intercourse, and inappropriate sexual acts within societal contexts. The government states that it is the responsibility of platforms to ensure that content is not present in a vulgar fashion. Creativities do not necessarily mean promoting or propagating vulgar and sexual content.
Key Highlights of I&B Ministry Action against Obscene Content
On 14th March 2024, The Indian Ministry of Information and Broadcasting (I&B) announced the blocking of 18 OTT platforms, 19 Websites, 10 apps, and 57 social media handles for displaying obscene and vulgar content. Union Minister for Information & Broadcasting Shri Anurag Singh Thakur has announced the removal of 18 OTT platforms that published obscene and vulgar content, underscoring the responsibility of platforms to prevent the spread of such content. The decision was made under the Information Technology Act 2000 and in consultation with other Indian ministries and domain experts in media, entertainment, women's rights, and child rights.
List of Blocked OTT Platforms
OTT platforms that have been blocked are Dreams Films, Voovi, Yessma, Uncut Adda, Tri Flicks, X Prime, Neon X VIP, Besharams, Hunters, Rabbit, Xtramood, Nuefliks, MoodX, Mojflix, Hot Shots VIP, Fugi, Chikooflix, Prime Play.
It was highlighted that these OTT platforms, despite not being widely popular, have a significant viewership. One app has over 1 crore downloads, while two others have more than 50 lakh downloads on Google Play Store. These platforms also market their content through social media, with a combined followership of over 32 lakh.
Nature of content
The ministry reported that a significant portion of the content on social media platforms was obscene, vulgar, and demeaning, depicting nudity and sexual acts in inappropriate contexts like teacher-student relationships and incestuous family relationships. The content included sexual innuendos and prolonged pornographic scenes without any thematic or societal relevance. It was further stated that the content was found to be prima facie in violation of Section 67 and 67A of the Information & Technology Act, 2000, Section 292 of the Indian Penal Code and Section 4 of the Indecent Representation of Women (Prohibition) Act, 1986.
Way Forward
The press release by the ministry stated that “The Government of India remains committed to fostering the growth and development of the OTT industry. Several measures have been undertaken in this regard, including the introduction of the Inaugural OTT Award for Web Series at the 54th International Film Festival of India, collaboration with OTT platforms in the media and entertainment sector, and the establishment of a light touch regulatory framework with an emphasis on self-regulation under the IT Rules, 2021.”
This shows that the Indian government is dedicated to promoting the growth of the OTT industry but within certain checks or oversight mechanisms to prevent illicit or objectionable content on such platforms.
OTT Content and Regulatory Checks
Online content streaming on OTT platforms lacks regulatory checks, unlike films, which are reviewed and certified by a government-appointed board. The government has instructed streaming services to independently review content for obscenity and violence before it is made available online. There have been repeated instances where criticism has been raised about the illicit or violative depicted content in some OTT shows. This highlights the issue of checks and balances. The government has urged self-regulation on platforms, but the repeated instances of illicit content raise societal concerns. The Ministry of I&B is keen towards promoting ethical & moral standards of content that is being hosted on online OTT platforms.
Conclusion
The Ministry of I&B has taken a step and announced the shutdown of 18 OTT platforms that were engaged in depicting illicit content. This shows that the I&B Ministry is committed to promoting ethical online content. While legislative measures are required to prevent the spread of such illicit or violative content, joint efforts by the government, industry players, and civil society are critical to ensuring a secure and responsible digital environment for all users.
References
- https://pib.gov.in/PressReleaseIframePage.aspx?PRID=2014477
- https://www.thehindu.com/news/national/centre-bans-ott-platforms-websites-and-apps-over-obscene-and-vulgar-content/article67949819.ece
- https://economictimes.indiatimes.com/news/india/ib-ministry-blocks-18-ott-platforms-for-vulgar-content/articleshow/108485880.cms?from=mdr
- https://indianexpress.com/article/entertainment/information-and-broadcasting-ministry-blocks-18-ott-platforms-for-obscene-and-vulgar-content-9213749/
- https://www.storyboard18.com/ott-news/mib-blocks-18-ott-platforms-for-showing-obscene-and-vulgar-content-26400.htm


