#FactCheck -AI-Generated Video Falsely Shows Car Stuck on Delhi–Jaipur Highway Signboard
Executive Summary
A shocking video showing a car hanging from a highway signboard is going viral on social media. The clip allegedly shows a black Mahindra Thar stuck on an overhead direction signboard on the Delhi–Jaipur Highway (NH-48). Social media users are widely sharing the video, claiming it shows a real road accident. However, a research by CyberPeace found the viral claim to be false. Our findings reveal that the circulating video is not real but AI-generated.
Claim
Social media users are sharing the clip as footage of an actual road accident. A viral post on X (formerly Twitter) claims that the incident took place on the Delhi–Jaipur Highway, showing a black Mahindra & Mahindra Thar lodged in a highway signboard.
- https://x.com/SenBaijnath/status/2024098520006029504
- https://archive.ph/cmr5e

Fact Check
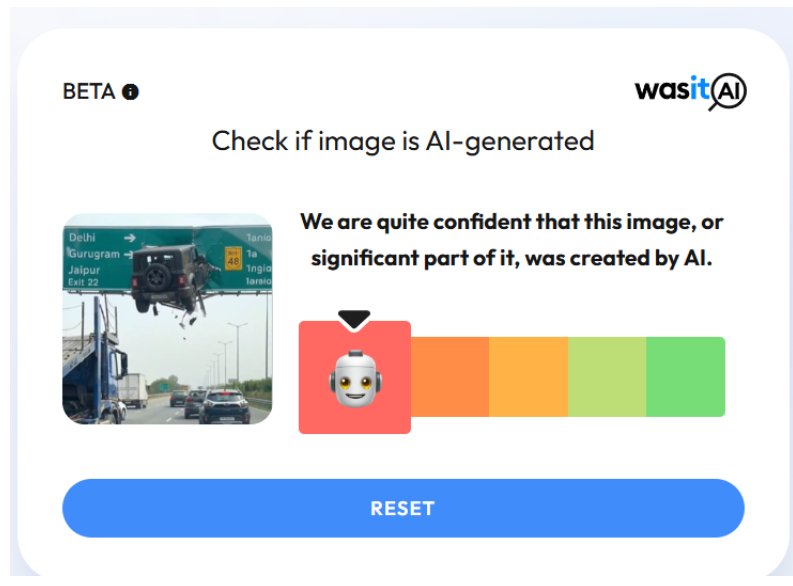
On closely examining the viral video, several inconsistencies were observed that are commonly associated with AI-generated content. For instance, it appears highly improbable for a heavy vehicle to get stuck precisely at the center of a signboard at such a height. Despite the scale of the alleged incident, traffic on the highway below continues moving normally without any disruption. Additionally, the text visible on the right side of the signboard appears distorted and unusually written. To further verify the authenticity of the video, we analysed it using the AI detection tool Hive Moderation, which indicated a 99.9% probability that the video was AI-generated.
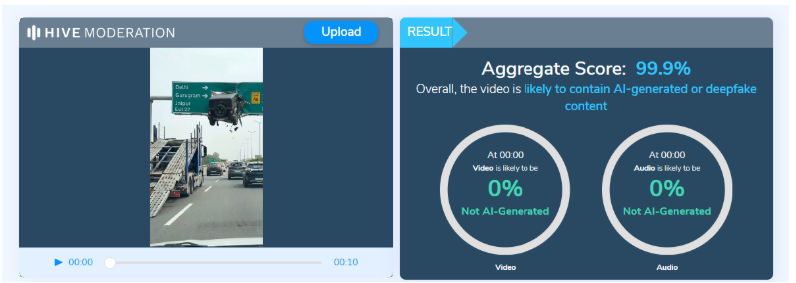
Another AI image detection tool, WasitAI, also found that the visuals in the viral clip were largely AI-generated.
Conclusion
Based on our research and available evidence, it is clear that the viral video showing a Mahindra Thar hanging from a highway signboard is not real but AI-generated.
Related Blogs

Introduction
The Indian healthcare sector has been transforming remarkably. This is mainly due to the development of emerging technologies such as AI and IoT. The rapid adoption of technology in healthcare delivery such as AI and IoT integration along with telemedicine, digital health solutions, and Electronic Medical Records (EMR) have enhanced the efficacy of hospitals, driving growth. The integration of AI and IoT devices in healthcare can improve patient care, health record management, and telemedicine and reshape the medical landscape as we know it. However, their implementation must be safe, with robust security and ethical safeguards in place.
The Transformative Power of AI and IoT in Revolutionising Healthcare
IoT devices for healthcare such as smartwatches, wearable patches, and ingestive sensors are equipped with sensors. These devices take physiological parameters in real-time, including heart rate, blood pressure, glucose level, etc. This can be forwarded automatically from these wearables to healthcare providers and EHR systems. Real-time patient health data enable doctors to monitor progress and intervene when needed.
The sheer volume of data generated by IoT healthcare devices opens avenues for applying AI. AI and ML algorithms can analyse patient data for patterns that further provide diagnostic clues and predict adverse events before they occur. A combination of AI and IoT opens avenues for proactive and personalised medicine tailored to specific patient profiles. This amalgamation can be a bridge between healthcare accessibility and quality. And, especially in rural and underserved areas, it can help receive timely and effective medical consultations, significantly improving healthcare outcomes. Moreover, the integration of AI-powered chatbots and virtual health assistants is enhancing patient engagement by providing instant medical advice and appointment scheduling.
CyberPeace Takeaway, the Challenges and the Way Forward
Some of the main challenges associated with integrating AI and IoT in healthcare include cybersecurity due to data privacy concerns, lack of interoperability, and skill gaps in implementation. Addressing these requires enhanced measures or specific policies, such as:
- Promoting collaborations among governments, regulators, industry, and academia to foster a healthcare innovation ecosystem such as public-private partnerships and funding opportunities to drive collaborative advancements in the sector. Additionally, engaging in capacity-building programs to upskill professionals.
- Infrastructural development, including startup support for scalable AI and IoT solutions. Engaging in creating healthcare-specific cybersecurity enhancements to protect sensitive data. According to a 2024 report by Check Point Software Technologies, the Indian healthcare sector has experienced an average of 6,935 cyberattacks per week, compared to 1,821 attacks per organisation globally in 2024.
Conclusion
The Deloitte survey highlights that on average hospitals spend 8–10% of their IT budget on cybersecurity techniques, such as hiring professionals and acquiring tools to minimise cyber-attacks to the maximum extent. Additionally, this spending is likely to increase to 12-15 % in the next two years moving towards proactive measures for cybersecurity.
The policy frameworks and initiatives are also carried out by the government. One of the Indian government's ways of driving innovation in AI and IoT in healthcare is through initiatives under the National Digital Health Mission (NDHM), the National Health Policy and the Digital India Initiative.
Though the challenges presented by data privacy and cyber security persist, the strong policies, public-private collaborations, capacity-building initiatives and the evolving startup ecosystem carry AI and IoT’s potential forward from the thoughtful merging of innovative health technologies, delivery models, and analytics. If the integration complexities are creatively tackled, these could profoundly improve patient outcomes while bending the healthcare cost curve.
References
- https://www.ndtv.com/business-news/indian-healthcare-sector-faced-6-935-cyberattacks-per-week-in-last-6-months-report-5989240
- https://www.businesstoday.in/technology/news/story/meity-nasscom-coe-collaborates-with-start-ups-to-enhance-healthcare-with-ai-iot-458739-2024-12-27
- https://www2.deloitte.com/content/dam/Deloitte/in/Documents/risk/in-ra-deloitte-dsci-hospital-report-noexp.pdf
- https://medium.com/@shibilahammad/the-transformative-potential-of-iot-and-ai-in-healthcare-78a8c7b4eca1
Transforming Misguided Knowledge into Social Strength
यत्र योगेश्वरः कृष्णो यत्र पार्थो धनुर्धरः । तत्र श्रीर्विजयो भूतिर्ध्रुवा नीतिर्मतिर्मम ॥ (Bhagavad Gita) translates as “Where there is divine guidance and righteous effort, there will always be prosperity, victory, and morality.” In the context of the idea of rehabilitation, this verse teaches us that if offenders receive proper guidance, their skills can be redirected. Instead of causing harm, the same abilities can be transformed into tools for protection and social good. Cyber offenders who misuse their skills can, through structured guidance, be redirected toward constructive purposes like cyber defence, digital literacy, and security innovation. This interpretation emphasises not discarding the “spoiled” but reforming and reintegrating them into society.
Introduction
Words and places are often associated with positive and negative aspects based on their history, stories, and the activities that might happen in that certain place. For example, the word “hacker” has a negative connotation, as does the place “Jamtara”, which is identified with its shady history as a cybercrime hotspot, but often people forget that there are lots of individuals who use their hacking skills to serve and protect their nation, also known as “white hat hackers”, a.k.a. ethical hackers, and places like Jamtara have a substantial number of talented individuals who have lost their way and are often victims of their circumstances. This presents the authorities with a fundamental issue of destigmatising cybercriminals and the need to act on their rehabilitation. The idea is to shift from punitive responses to rehabilitative and preventive approaches, especially in regions like Jamtara.
The Deeper Problem: Systemic Gaps and Social Context
Jamtara is not an isolated or a single case; there are many regions like Mewat, Bharatpur, Deoghar, Mathura, etc., that are facing a crisis, and various lives are uprooted because youth are entrapped in cybercrime rings, often to escape unemployment, poverty, and simply in the hope of a better life. In one such heart-wrenching story, a 24-year-old Shakil, belonging to Nuh, Haryana, was arrested for committing various cybercrimes, including sextortion and financial scams, and while his culpability is not in question here, his background reflects a deeper issue. He committed these crimes to pay for his diabetic father’s mounting bills and to see his sister, Shabana, married. This is the story of almost every other individual in the rural areas who is forced into committing these crimes, if not by a person, but by their circumstances. In a news report covered in 2024, an intervention was launched by various Meo leaders and social organisations in the Mewat region aimed at weaning the youth away from cybercrimes.
Not only poverty, but lack of education, social awareness, and digital literacy have acted as active agents for pushing the youth of India away from mainstream growth and towards the dark trenches of the cybercrime world. The local authorities have made active efforts to solve this problem; for instance, to dispel Jamtara’s unfavourable reputation for cybercrime and set the city firmly on the path to change, community libraries have been established in all 118 panchayats spread across six blocks of the district by IAS officer and DM Faiz Aq Ahmed Mumtaz.
The menace of cybercrimes is not limited to rural areas, as various reports surfaced during and post-COVID, where young children from urban areas became victims of various cybercrimes such as cyberbullying and stalking, and often perpetrators were someone from the same age group, adding to the dilemma. The issue has been noticed by various agencies, and the a need to deal with both victims and the accused in a sensitised manner. Recently, ex-CJI DY Chandrachud called for international collaboration to combat juvenile cybercrimes, as there are many who are ensnared and coerced into these criminal gangs, and swift resolution is the key to ensuring justice and rehabilitation.
CyberPeace Policy Outlook
Cybercrime is often a product of skill without purpose. The youth who are often pushed into these crimes either have an incomplete idea of the veracity of their actions or have no other resort. The legal system and the agencies will have to look beyond the nature of the crimes and adopt and undertake a reformative approach so that these people can make their way into society and harness their skills ethically. A good alternative would be to organise Cyber Bootcamps for Reform, i.e., structured training with placement support, and explain to them how ethical hacking and cybersecurity careers can be attractive alternatives. One way to make the process effective is to share real-world stories of reformed hackers. There are many who belong to small villages and districts who have written success stories on reform after participating in digital training programmes. The crime they commit doesn’t have to be the last thing they are able to do in life; it doesn’t have to be the ending. The digital programmes should be organised in a way and in a vernacular that the youth are well-versed in, so there are no language barriers. The programme may give training for coding, cyber hygiene, legal literacy, ethical hacking, psychological counselling, and financial literacy workshops.
It has become a matter of reclaiming the misdirected talent, as rehabilitation is not just humane; it is strategic in the fight against cybercrime. On 1st April 2025, IIT Madras Pravartak Technologies Foundation finished training its first batch of law enforcement officers in cybersecurity techniques. The initiative is commendable, and a similar initiative may prove effective for the youth accused of cybercrimes, and preferably, they can be involved in similar rehabilitation and empowerment programmes during the early stages of criminal proceedings. This will help prevent recidivism and convert digital deviance into digital responsibility. In order to successfully incorporate this into law enforcement, the police can effectively use it to identify first-time, non-habitual offenders involved in low-impact cybercrimes. Also, courts can exercise the authority to require participation in an approved cyber-reform programme as a condition of bail in addition to bail hearings.
Along with this, under the Juvenile Justice (Care and Protection of Children) Act, 2015, children in conflict with the law can be sent to observation homes where modules for digital literacy and skill development can be implemented. Other methods that may prove effective may include Restorative Justice Programmes, Court-monitored rehabilitation, etc.
Conlusion
A rehabilitative approach does not simply punish offenders, it transforms their knowledge into a force for good, ensuring that cybercrime is not just curtailed but converted into cyber defence and progress.
References
- Ismat Ara, How an impoverished district in Haryana became a breeding ground for cybercriminals, FRONTLINE (Jul 27, 2023, 11:00 IST), https://frontline.thehindu.com/the-nation/spotlight-how-nuh-district-in-haryana-became-a-breeding-ground-for-cybercriminals/article67098193.ece )
- Mohammed Iqbal, Counselling, skilling aim to wean Mewat youth away from cybercrimes, THE HINDU (Jul. 28, 2024, 01:39 AM), https://www.thehindu.com/news/cities/Delhi/counselling-skilling-aim-to-wean-mewat-youth-away-from-cybercrimes/article68454985.ece
- Prawin Kumar Tiwary,Jamtara’s journey from cybercrime to community libraries, 101 REPORTERS (Feb. 16, 2022), https://101reporters.com/article/development/Jamtaras_journey_from_cybercrime_to_community_libraries .
- IIT Madras Pravartak completes Training First Batch of Cyber Commandos, PRESS INFORMATION BUREAU (Apr. 1, 2025, 03:36 PM), https://www.pib.gov.in/PressReleasePage.aspx?PRID=2117256

Executive Summary:
A video has gone viral that claims to show Hon'ble Minister of Home Affairs, Shri Amit Shah stating that the BJP-Led Central Government intends to end quotas for scheduled castes (SCs), scheduled tribes (STs), and other backward classes (OBCs). On further investigation, it turns out this claim is false as we found the original clip from an official source, while he delivered the speech at Telangana, Shah talked about falsehoods about religion-based reservations, with specific reference to Muslim reservations. It is a digitally altered video and thus the claim is false.

Claims:
The video which allegedly claims that the Hon'ble Minister of Home Affairs, Shri Amit Shah will be terminating the reservation quota systems of scheduled castes (SCs), scheduled tribes (STs) and other backward classes (OBCs) if BJP government was formed again has been viral on social media platforms.

English Translation: If the BJP government is formed again we will cancel ST, SC reservations: Hon'ble Minister of Home Affairs, Shri Amit Shah


Fact Check:
When the video was received we closely observed the name of the news media channel, and it was V6 News. We divided the video into keyframes and reverse searched the images. For one of the keyframes of the video, we found a similar video with the caption “Union Minister Amit Shah Comments Muslim Reservations | V6 Weekend Teenmaar” uploaded by the V6 News Telugu’s verified Youtube channel on April 23, 2023. Taking a cue from this, we also did some keyword searches to find any relevant sources. In the video at the timestamp of 2:38, Hon'ble Minister of Home Affairs, Shri Amit Shah talks about religion-based reservations calling ‘unconstitutional Muslim Reservation’ and that the Government will remove it.

Further, he talks about the SC, ST, and OBC reservations having full rights for quota but not the Muslim reservation.
While doing the reverse image, we found many other videos uploaded by other media outlets like ANI, Hindustan Times, The Economic Times, etc about ending Muslim reservations from Telangana state, but we found no such evidence that supports the viral claim of removing SC, ST, OBC quota system. After further analysis for any sign of alteration, we found that the viral video was edited while the original information is different. Hence, it’s misleading and false.
Conclusion:
The video featuring the Hon'ble Minister of Home Affairs, Shri Amit Shah announcing that they will remove the reservation quota system of SC, ST and OBC if the new BJP government is formed again in the ongoing Lok sabha election, is debunked. After careful analysis, it was found that the video was fake and was created to misrepresent the actual statement of Hon'ble Minister of Home Affairs, Shri Amit Shah. The original footage surfaced on the V6 News Telugu YouTube channel, in which Hon'ble Minister of Home Affairs, Shri Amit Shah was explaining about religion-based reservations, particularly Muslim reservations in Telangana. Unfortunately, the fake video was false and Hon'ble Minister of Home Affairs, Shri Amit Shah did not mention the end of SC, ST, and OBC reservations.
- Claim: The viral video covers the assertion of Hon'ble Minister of Home Affairs, Shri Amit Shah that the BJP government will soon remove reservation quotas for scheduled castes (SCs), scheduled tribes (STs), and other backward classes (OBCs).
- Claimed on: X (formerly known as Twitter)
- Fact Check: Fake & Misleading


