#FactCheck- AI-Generated Image of Narendra Modi Goes Viral Ahead of Kerala Elections
Executive Summary
As Kerala gears up for its upcoming Assembly elections, political activity has intensified across the state. Amid this charged atmosphere, a purported image of Narendra Modi has gone viral on social media. The image shows the Prime Minister holding coconuts, with several photographers around him. It is being claimed that the photo was taken during his recent visit for the 2026 Kerala Assembly election campaign.
However, an research by the CyberPeace has debunked the claim, confirming that the image is fake and generated using artificial intelligence.
Claim
A Facebook user named “Javed Ahmad” shared the viral image on April 6, 2026, with a sarcastic caption suggesting that the Prime Minister was posing for reels during his Kerala visit.
- https://www.facebook.com/Ahmadspeaks4u/posts/pfbid0aRnhwXBjnfSXF9S48vaH1gTQrGQmxnRmhpJCRxMWazqLJhYs6zxM9rot51qtBgRLl
- https://perma.cc/N3AM-Q2YC

Fact Check
To verify the claim, we conducted keyword searches on Google but found no credible news reports supporting it. A reverse image search also did not yield any reliable sources. Additionally, a thorough review of the Prime Minister’s official social media accounts showed no trace of such an image or event. Given these inconsistencies, suspicion arose about the image’s authenticity.
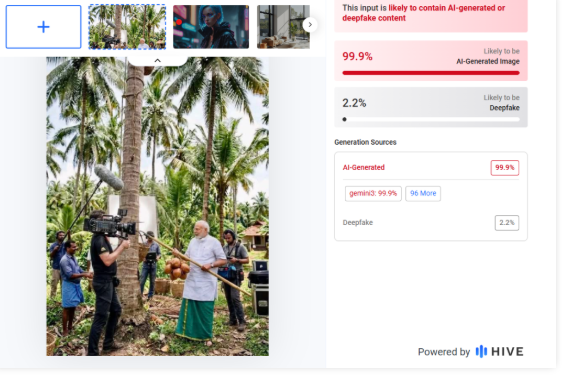
The viral image was then analyzed using AI detection tools. Results from HIVE Moderation indicated a 99% probability that the image is AI-generated.
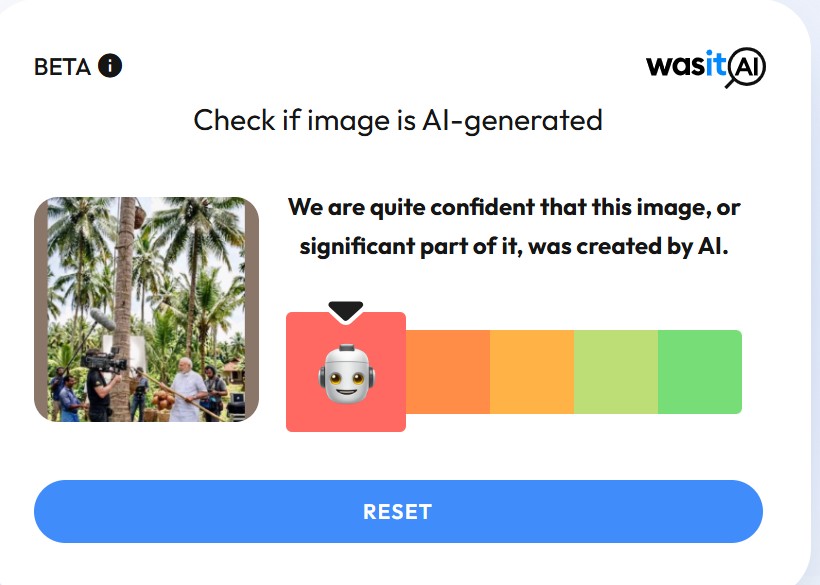
Another tool, Wasit AI, also confirmed that the image is artificially created.
Conclusion
The claim is false. The viral image of Prime Minister Narendra Modi is not real and has been generated using AI tools, likely similar to Google AI.
Related Blogs

Introduction
In an era expounded by rapid communications and live coverage of global affairs, users often encounter misinformation continuously, and it has emerged as a huge challenge. Misinformation is false or inaccurate information, believed to be true, and shared without any intention to deceive. On the other hand, disinformation refers to false information that is intended to mislead, especially with set propaganda. It steadily affects all aspects of life and can even lead to a profound impact on geopolitics, international relations, wars, etc. When modern media announces “breaking news,” it captures attention and keeps viewers engaged. In the rush for television rating points, information may be circulated without proper fact-checking. This urgency can result in the spread of unverified claims and the elevation of irrelevant details, while truly important issues are overlooked. Such practices can distort public understanding and impact strategic political decisions.
Misinformation and Fake News in Recent History
The phenomenon of misinformation is not limited to isolated incidents but has become a recurring feature of political events around the globe. This business has increasingly become visible in recent political history, where it has not only sensationalised the general public but also affected international relations and democratic outcomes. For example, during Slovakia’s elections in 2023, the country experienced a major surge of online misinformation. Over 365,000 misleading posts were posted on social media platforms, majorly influencing public opinion and leading to challenges for voters. A lot of this content was amplified by political leaders. The media's rush to deliver content sometimes makes it easier for false narratives to dominate the public sphere, shaping voter opinions and undermining informed political discourse.
Current Geopolitical Interference by Misinformation
In the recent Hamas-Israel conflict, manipulated images and unverified reports complicated diplomacy. Such campaigns distort facts, complicate humanitarian responses, and escalate conflicts. This growing trend shows how misinformation now acts as a weapon of war, exploiting media urgency and undermining international stability.
Indo–Pak Conflict Exaggeration
The India-Pakistan conflict is a long-dragged and complex issue in South Asia. It has been continuously dragged from traditional to contemporary media. But in recent tensions and war situations media raised serious concerns about misinformation. Live media coverage can sometimes mislead the public with speculative information. The live coverage continuously addressed it as breaking news and escalated excitement and fear, distorting the reality on the ground. Moreover, the real-time reporting of sensitive military activities like mock drills, blackouts, troop movements, air strikes, etc., interfered with strategic operations. Such reporting may lead to obstructing decision-making processes and placing operational missions at risk. Later Defence Ministry called it out in one of their X posts. Such media-driven exaggeration causes mass hysteria, and eventually, emotional and patriotic sentiments are evoked.
Legal and Political Recommendations
The intersection of media urgency and national security may have serious geopolitical repercussions if not managed with legal and ethical restrictions. International Frameworks like UNESCO‘s Guidelines for regulating Digital Platforms, 2023, and the Digital Services Act, 2022, regulate and govern digital platforms.
Despite the existence of international and national guidelines, there remains an urgent need to strengthen cyber laws by imposing strict penalties and compensation mechanisms for the dissemination of unverified information. Media outlets must also refrain from indiscriminately labelling every report as “breaking news.” Since the modern media deals in digital data, the protection of strategic state movements should be regulated with checks and balances.
Ethical considerations should be maintained during the publication or streaming of any information. Media should have self-regulations to fact-check and publish only authorised and double-verified information.
Given the borderless nature of the internet and the rapid, global spread of misinformation, international cooperation is imperative. Addressing the challenges posed by cross-border mis/disinformation requires a shared understanding and coordinated response among states at the global level.
References
- https://pam.int/wp-content/uploads/2024/10/EN-Background-paper-on-disinformation-and-fake-news-Jan-2024.pdf
- https://papers.ssrn.com/sol3/papers.cfm?abstract_id=3172349
- https://www.unesco.org/sites/default/files/medias/fichiers/2023/04/draft2_guidelines_for_regulating_digital_platforms_en.pdf
- https://commission.europa.eu/strategy-and-policy/priorities-2019-2024/europe-fit-digital-age/digital-services-act_en

Introduction
The Supreme Court of India recently ruled that telecom companies cannot be debarred from reissuing the deactivated numbers to a new subscriber. Notably, such reallocation of deactivated numbers is allowed only after the expiration of the period of 90 days. The Apex Court of India also mentioned that it is the responsibility of the user to delete their associated data with their number or any WhatsApp account data to ensure privacy. The Centre has recently also blocked 22 apps which were part of unlawful operations including betting and money laundering. Meanwhile, in the digital landscape, the Intervention of legislature and judiciary is playing a key role in framing policies or coming up with guidelines advocating for a true cyber-safe India. The government initiatives are encouraging the responsible use of technologies and Internet-availed services.
Supreme Court stated that telecom companies cannot be barred from reissuing deactivated numbers
Taking note of a petition before the Supreme Court of India, seeking direction from the Telecom Regulatory Authority of India (TRAI) to instruct mobile service providers to stop issuing deactivated mobile numbers, the Apex Court dismissed it by stating that mobile service providers in India are allowed to allocate the deactivated numbers to new users or subscribers but only after 90 days from the deactivation of the number.
A concern of Breach of Confidential Data
The Court further stated, “It is for the earlier subscriber to take adequate steps to ensure that privacy is maintained.” stating that it is the responsibility of the user to delete their WhatsApp account attached to the previous phone number and erase their data. The Court further added that users need to be aware of the Supreme Court ruling that once the number is deactivated for non-use and disconnection, it can not be reallocated before the expiry of the 90-day period of such deactivation. However, after the allotted time passes, such reallocation of numbers to a new user is allowed.
MEITY issued blocking orders against 22 illegal betting apps & websites
The government of India has been very critical in safeguarding Indian cyberspace by banning and blocking various websites and apps that have been operating illegally by scamming/dupping people of huge sums of money and also committing cyber crimes like data breaches. In recent developments, the Ministry of Electronic and Information Technology (Meity), on November 5, 2023, banned 22 apps including Mahadev Book and Reddyannaprestopro. The Centre has taken this decision on recommendations from the Enforcement Directorate (ED). ED raids on the Mahadev book app in Chattisgarh also revealed unlawful operations. This investigation has been underway for the past few months by the ED.
Applicable laws to prevent money laundering and the power of government to block such websites and apps
On the other hand, the Prevention of Money Laundering Act (PMLA) 2002 is a legislation already in place which aims to prevent and prosecute cases of money laundering. The government also has the power to block or recommend shutting down websites and apps under section 69A of the Information and Technology Act, 2000, under some specific condition as enumerated in the same.
Conclusion
In the evolving digital landscape, cyberspace covers several aspects while certain regulations or guidelines are required for smooth and secure functioning. We sometimes change our phone numbers or deactivate them, hence, it is significantly important to delete the data associated with the phone number or any such social media account data attached to it. Hence, such a number is eligible for reallocation to a new or early subscriber after the expiration of a period of 90 days from such deactivation. On the other hand, the centre has also blocked the websites or apps that were found to be part of illegal operations including betting and money laundering. Users have also been advised not to misuse the Internet-availed services. Hence, trying to create a lawful and safe Internet environment for all.
References:
- https://timesofindia.indiatimes.com/india/cant-bar-telecom-companies-from-reissuing-deactivated-numbers-says-supreme-court/articleshow/104993401.cms
- https://pib.gov.in/PressReleseDetailm.aspx?PRID=1974901#:~:text=Ministry%20of%20Electronics%20and%20Information,including%20Mahadev%20Book%20and%20Reddyannaprestopro

Executive Summary:
The rise in cybercrime targeting vulnerable individuals, particularly students and their families, has reached alarming levels. Impersonation scams, where fraudsters pose as Law Enforcement Officers, have become increasingly sophisticated, exploiting fear, urgency, and social stigma. This report delves into recent incidents of ransom scams involving fake CBI officers, highlighting the execution methods, psychological impact on victims, and preventive measures. The goal is to raise public awareness and equip individuals with the knowledge needed to protect themselves from such fraudulent activities.
Introduction:
Cybercriminals are evolving their tactics, with impersonation and social engineering at the forefront. Scams involving fake law enforcement officers have become rampant, preying on the fear of legal repercussions and the desire to protect loved ones. This report examines incidents where scammers impersonated CBI officers to extort money from families of students, emphasizing the urgent need for awareness, verification, and preventive measures.
Case Study:
This case study explains how the scammers impersonate themselves for the money targeting students' families.
Targets receive calls from scammers posing as CBI officers. Mostly the families of students are targeted by the fraudsters using sophisticated impersonation and emotional manipulation tactics. In our case study, the targets received calls from unknown international numbers, falsely claiming that the students, along with their friends, were involved in a fabricated rape case. The parents get calls during school or college hours, a time when it is particularly difficult and chaotic for parents to reach their children, adding to the panic and sense of urgency. The scammers manipulate the parents by stating that, due to the students' clean records, they are not officially arrested but would face severe legal consequences unless a sum of money is paid immediately.
Although in these specific cases, the parents did not pay the money, many parents in our country fall victim to such scams, paying large sums out of fear and desperation to protect their children’s futures. The fear of legal repercussions, social stigma, and the potential damage to the students' reputations, the scammers used high-pressure tactics to force compliance.
These incidents may result in significant financial losses, emotional trauma, and a profound loss of trust in communication channels and authorities. This underscores the urgent need for awareness, verification of authority, and prompt reporting of such scams to prevent further victimisation
Modus Operandi:
- Caller ID Spoofing: The scammer used a unknown number and spoofing techniques to mimic a legitimate law enforcement authority.
- Fear Induction: The fraudster played on the family's fear of social stigma, manipulating them into compliance through emotional blackmail.
Analysis:
Our research found that the unknown international numbers used in these scams are not real but are puppet numbers often used for prank calls and fraudulent activities. This incident also raises concerns about data breaches, as the scammers accurately recited students' details, including names and their parents' information, adding a layer of credibility and increasing the pressure on the victims. These incidents result in significant financial losses, emotional trauma, and a profound loss of trust in communication channels and authorities.
Impact on Victims:
- Financial and Psychological Losses: The family may face substantial financial losses, coupled with emotional and psychological distress.
- Loss of Trust in Authorities: Such scams undermine trust in official communication and law enforcement channels.
- Exploitation of Fear and Urgency: Scammers prey on emotions such as fear, urgency, and social stigma to manipulate victims.
- Sophisticated Impersonation Techniques: Using caller ID spoofing, Virtual/Temporary numbers and impersonation of Law Enforcement Officers adds credibility to the scam.
- Lack of Verification: Victims often do not verify the caller's identity, leading to successful scams.
- Significant Psychological Impact: Beyond financial losses, these scams cause lasting emotional trauma and distrust in institutions.
Recommendations:
- Cross-Verification: Always cross-verify with official sources before acting on such claims. Always contact official numbers listed on trusted Government websites to verify any claims made by callers posing as law enforcement.
- Promote Awareness: Educational institutions should conduct regular awareness programs to help students and families recognize and respond to scams.
- Encourage Prompt Reporting: Reporting such incidents to authorities can help track scammers and prevent future cases. Encourage victims to report incidents promptly to local authorities and cybercrime units.
- Enhance Public Awareness: Continuous public awareness campaigns are essential to educate people about the risks and signs of impersonation scams.
- Educational Outreach: Schools and colleges should include Cybersecurity awareness as part of their curriculum, focusing on identifying and responding to scams.
- Parental Guidance and Support: Parents should be encouraged to discuss online safety and scam tactics with their children regularly, fostering a vigilant mindset.
Conclusion:
The rise of impersonation scams targeting students and their families is a growing concern that demands immediate attention. By raising awareness, encouraging verification of claims, and promoting proactive reporting, we can protect vulnerable individuals from falling victim to these manipulative and harmful tactics. It is high time for the authorities, educational institutions, and the public to collaborate in combating these scams and safeguarding our communities. Strengthening data protection measures and enhancing public education on the importance of verifying claims can significantly reduce the impact of these fraudulent schemes and prevent further victimisation.


