#FactCheck - Viral Graphic Falsely Attributes Statement on UGC to CM Yogi Adityanath
Executive Summary
A news graphic is being shared on social media claiming that Uttar Pradesh Chief Minister Yogi Adityanath said,“Those who practice casteism and discrimination are the ones opposing UGC. If you do not indulge in caste-based discrimination, what is there to fear?” The CyberPeace’s research found the viral claim circulating on social media to be false. Our research revealed that Chief Minister Yogi Adityanath never made such a statement. It was also established that the viral news graphic has been digitally edited.
Claim
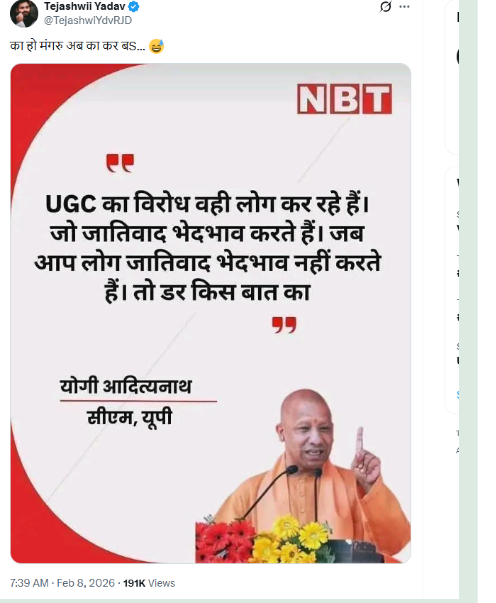
On February 8, a user on social media platform X (formerly Twitter) shared a news graphic bearing the logo of Navbharat Times, attributing the above statement to CM Yogi Adityanath. The post and its archived version can be seen below, along with screenshots. (Links and screenshots provided)
Fact Check:
To verify the authenticity of the claim, we conducted a keyword-based search on Google. However, we did not find any credible or reliable media report supporting the viral statement. We further examined the official social media accounts of Chief Minister Yogi Adityanath, including his Facebook and Instagram handles. Our review found no post, speech, or statement resembling the claim made in the viral graphic.
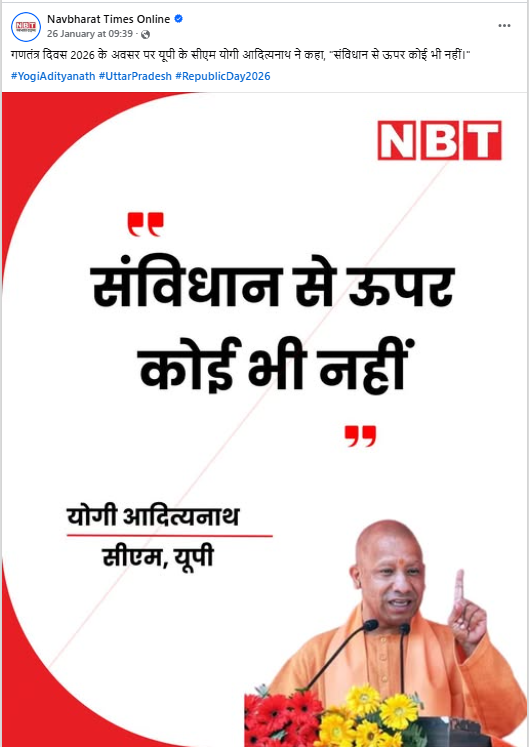
Continuing the research , we examined the official social media accounts of Navbharat Times. During this process, we found the original graphic published on the Navbharat Times Facebook page on January 26, 2026. The caption of the original graphic read: “On the occasion of Republic Day 2026, Uttar Pradesh Chief Minister Yogi Adityanath said, ‘No one is above the Constitution.’”
This clearly differs from the claim made in the viral graphic, indicating that the latter was altered.
Conclusion
Our research confirms that Uttar Pradesh Chief Minister Yogi Adityanath did not make the statement being attributed to him on social media. The viral news graphic is digitally edited and misleading. The claim, therefore, is false.
Related Blogs

Executive Summary:
The claim of a video of US President Joe Biden dozing off during a television interview is digitally manipulated . The original video is from a 2011 incident involving actor and singer Harry Belafonte. He seems to fall asleep during a live satellite interview with KBAK – KBFX - Eyewitness News. Upon thorough analysis of keyframes from the viral video, it reveals that US President Joe Biden’s image was altered in Harry Belafonte's video. This confirms that the viral video is manipulated and does not show an actual event involving President Biden.

Claims:
A video shows US President Joe Biden dozing off during a television interview while the anchor tries to wake him up.


Fact Check:
Upon receiving the posts, we watched the video then divided the video into keyframes using the inVid tool, and reverse-searched one of the frames from the video.
We found another video uploaded on Oct 18, 2011 by the official channel of KBAK - KBFX - Eye Witness News. The title of the video reads, “Official Station Video: Is Harry Belafonte asleep during live TV interview?”

The video looks similar to the recent viral one, the TV anchor could be heard saying the same thing as in the viral video. Taking a cue from this we also did some keyword searches to find any credible sources. We found a news article posted by Yahoo Entertainment of the same video uploaded by KBAK - KBFX - Eyewitness News.

Upon thorough investigation from reverse image search and keyword search reveals that the recent viral video of US President Joe Biden dozing off during a TV interview is digitally altered to misrepresent the context. The original video dated back to 2011, where American Singer and actor Harry Belafonte was the actual person in the TV interview but not US President Joe Biden.
Hence, the claim made in the viral video is false and misleading.
Conclusion:
In conclusion, the viral video claiming to show US President Joe Biden dozing off during a television interview is digitally manipulated and inauthentic. The video is originally from a 2011 incident involving American singer and actor Harry Belafonte. It has been altered to falsely show US President Joe Biden. It is a reminder to verify the authenticity of online content before accepting or sharing it as truth.
- Claim: A viral video shows in a television interview US President Joe Biden dozing off while the anchor tries to wake him up.
- Claimed on: X (Formerly known as Twitter)
- Fact Check: Fake & Misleading

About Global Commission on Internet Governance
The Global Commission on Internet Governance was established in January 2014 with the goal of formulating and advancing a strategic vision for Internet governance going forward. Independent research on Internet-related issues of international public policy is carried out and supported over the two-year initiative. An official commission report with particular policy recommendations for the future of Internet governance will be made available as a result of this initiative.
There are two goals for the Global Commission on Internet Governance. First, it will encourage a broad and inclusive public discussion on how Internet governance will develop globally. Second, through its comprehensive policy-oriented report and the subsequent marketing of this final report, the Global Commission on Internet Governance will present its findings to key stakeholders at major Internet governance events.
The Internet: exploring the world wide web and the deep web
The Internet can be thought of as a vast networking infrastructure, or network of networks. By linking millions of computers worldwide, it creates a network that allows any two computers, provided they are both online, to speak with one another.
The Hypertext Transfer Protocol is the only language spoken over the Internet and is used by the Web to transfer data. Email, which depends on File Transfer Protocol, Usenet newsgroups, Simple Mail Transfer Protocol, and instant messaging, is also used on the Internet—not the Web. Thus, even though it's a sizable chunk, the Web is only a part of the Internet [1]. In summary, the deep Web is the portion of the Internet that is not visible to the naked eye. It is stuff from the World Wide Web that isn't available on the main Web. Standard search engines cannot reach it. More than 500 times larger than the visible Web is this enormous subset of the Internet [1-2].
The Global Commission on Internet Governance will concentrate on four principal themes:
• Improving the legitimacy of government, including standards and methods for regulation;
• Promoting economic innovation and expansion, including the development of infrastructure, competition laws, and vital Internet resources;
• Safeguarding online human rights, including establishing the idea of technological neutrality for rights to privacy, human rights, and freedom of expression;
• Preventing systemic risk includes setting standards for state behaviour, cooperating with law enforcement to combat cybercrime, preventing its spread, fostering confidence, and addressing disarmament-related issues.
Dark Web
The part of the deep Web that has been purposefully concealed and is unreachable using conventional Web browsers is known as the "dark Web." Dark Web sites are a platform for Internet users who value their anonymity since they shield users from prying eyes and typically utilize encryption to thwart monitoring. The Tor network is a well-known source for content that may be discovered on the dark web. Only a unique Web browser known as the Tor browser is required to access the anonymous Tor network (Tor 2014). It was a technique for anonymous online communication that the US Naval Research Laboratory first introduced as The Onion Routing (Tor) project in 2002. Many of the functionality offered by Tor are also available on I2P, another network. On the other hand, I2P was intended to function as a network inside the Internet, with traffic contained within its boundaries. Better anonymous access to the open Internet is offered by Tor, while a more dependable and stable "network within the network" is provided by I2P [3].
Cybersecurity in the dark web
Cyber crime is not any different than crime in the real world — it is just executed in a new medium: “Virtual criminality’ is basically the same as the terrestrial crime with which we are familiar. To be sure, some of the manifestations are new. But a great deal of crime committed with or against computers differs only in terms of the medium. While the technology of implementation, and particularly its efficiency, may be without precedent, the crime is fundamentally familiar. It is less a question of something completely different than a recognizable crime committed in a completely different way [4].”
Dark web monitoring
The dark Web, in general, and the Tor network, in particular, offer a secure platform for cybercriminals to support a vast amount of illegal activities — from anonymous marketplaces to secure means of communication, to an untraceable and difficult to shut down infrastructure for deploying malware and botnets.
As such, it has become increasingly important for security agencies to track and monitor the activities in the dark Web, focusing today on Tor networks, but possibly extending to other technologies in the near future. Due to its intricate webbing and design, monitoring the dark Web will continue to pose significant challenges. Efforts to address it should be focused on the areas discussed below [5].
Hidden service directory of dark web
A domain database used by both Tor and I2P is based on a distributed system called a "distributed hash table," or DHT. In order for a DHT to function, its nodes must cooperate to store and manage a portion of the database, which takes the shape of a key-value store. Owing to the distributed character of the domain resolution process for hidden services, nodes inside the DHT can be positioned to track requests originating from a certain domain [6].
Conclusion
The deep Web, and especially dark Web networks like Tor (2004), offer bad actors a practical means of transacting in products anonymously and lawfully.
The absence of discernible activity in non-traditional dark web networks is not evidence of their nonexistence. As per the guiding philosophy of the dark web, the actions are actually harder to identify and monitor. Critical mass is one of the market's driving forces. It seems unlikely that operators on the black Web will require a great degree of stealth until the repercussions are severe enough, should they be caught. It is possible that certain websites might go down, have a short trading window, and then reappear, which would make it harder to look into them.
References
- Ciancaglini, Vincenzo, Marco Balduzzi, Max Goncharov and Robert McArdle. 2013. “Deepweb and Cybercrime: It’s Not All About TOR.” Trend Micro Research Paper. October.
- Coughlin, Con. 2014. “How Social Media Is Helping Islamic State to Spread Its Poison.” The Telegraph, November 5.
- Dahl, Julia. 2014. “Identity Theft Ensnares Millions while the Law Plays Catch Up.” CBS News, July 14.
- Dean, Matt. 2014. “Digital Currencies Fueling Crime on the Dark Side of the Internet.” Fox Business, December 18.
- Falconer, Joel. 2012. “A Journey into the Dark Corners of the Deep Web.” The Next Web, October 8.
- Gehl, Robert W. 2014. “Power/Freedom on the Dark Web: A Digital Ethnography of the Dark Web Social Network.” New Media & Society, October 15. http://nms.sagepub.com/content/early/2014/ 10/16/1461444814554900.full#ref-38.

Introduction
Netflix is no stranger to its subscribers being targeted by SMS and email-led phishing campaigns. But the most recent campaign has been deployed at a global scale, affecting paid users in as many as 23 countries according to cybersecurity firm Bitdefender. In this particular campaign, attackers are using the carrot-and-stick tactic of either creating a false sense of urgency or promising rewards to steal financial information and Netflix credentials. For example, users may be contacted via SMS and told that their account is being suspended due to payment failures. A fake website may be shared through a link, encouraging the individual to share sensitive information to restore their account. Once this information has been input, it is now accessible to the attackers. This can create significant stress and even financial loss for its users. Thus, they are encouraged to develop the necessary skills to recognize and respond to these threats effectively.
How The Netflix Scam Works
Users are typically contacted through SMS. Bitdefender reports that these messages may look something like this:
"NETFLIX: There was an issue processing your payment. To keep your services active, please sign in and confirm your details at: https://account-details[.]com"
On clicking the link, the victim is directed to a website designed to mimic an authentic user experience interface, containing Netflix’s logo, color scheme, and grammatically-correct text. The website uses this interface to encourage the victim to divulge sensitive personal information, such as account credentials and payment details. Since this is a phishing website, the user’s personal information becomes accessible to the attacker as soon as it is entered. This information is then sold individually or in bundles on the dark web.
Practical Steps to Stay Safe
- Know Netflix’s Customer Interface: According to Netflix, it will never ask users to share personal information including credit or debit card numbers, bank account details, and Netflix passwords. It will also never ask for payment through a third-party vendor or website.
- Verify Authenticity: Do not open links from unknown sources sent by email or sms. If unsure, access Netflix directly by typing the URL into the browser instead of clicking on links in emails or texts. If the link has been opened, do not enter any information.
- Use Netflix’s Official Support Channels: Confirm any suspicious communication through Netflix’s verified help page or app. Write to phishing@netflix.com with any complaints about such an issue.
- Contact Your Financial Institution: If you have entered your personal information into a phishing website, you should immediately reach out to your bank to block your card and change your Netflix password. Contact the authorities via www.cybercrime.gov.in or by calling the helpline at 1930 in case of loss of funds.
- Use Strong Passwords and Enable MFA/2FA: Users are advised to use a unique, strong password with multiple characters. Enable Multi-Factor Authentication or Two Factor Authentication to your accounts, if available, to add an extra level of security.
Conclusion
Phishing campaigns which are designed to gather customer data through fraudulent means often involve sending links to as many users as possible, with the aim of monetizing stolen information. Attackers exploit user trust in online platforms to steal sensitive personal information, making such campaigns more sophisticated as highlighted above. This underscores the need for users of online platforms to practice good cyber hygiene by verifying information, learning to detect suspicious information and ignoring it, and staying aware of the types of online fraud they may be exposed to.
Sources
- https://www.bitdefender.com/en-gb/blog/hotforsecurity/netflix-scam-stay-safe
- https://help.netflix.com/en/node/65674
- https://timesofindia.indiatimes.com/technology/tech-news/netflix-users-beware-this-netflix-subscription-scam-is-active-in-23-countries-how-to-spot-one-and-stay-safe/articleshow/115820070.cms


