#FactCheck - AI-Generated Video Falsely Claims Salman Khan Is Joining AIMIM
A video of Bollywood actor Salman Khan is being widely circulated on social media, in which he can allegedly be heard saying that he will soon join Asaduddin Owaisi’s party, the All India Majlis-e-Ittehadul Muslimeen (AIMIM). Along with the video, a purported image of Salman Khan with Asaduddin Owaisi is also being shared. Social media users are claiming that Salman Khan is set to join the AIMIM party.
CyberPeace research found the viral claim to be false. Our research revealed that Salman Khan has not made any such statement, and that both the viral video and the accompanying image are AI-generated.
Claim
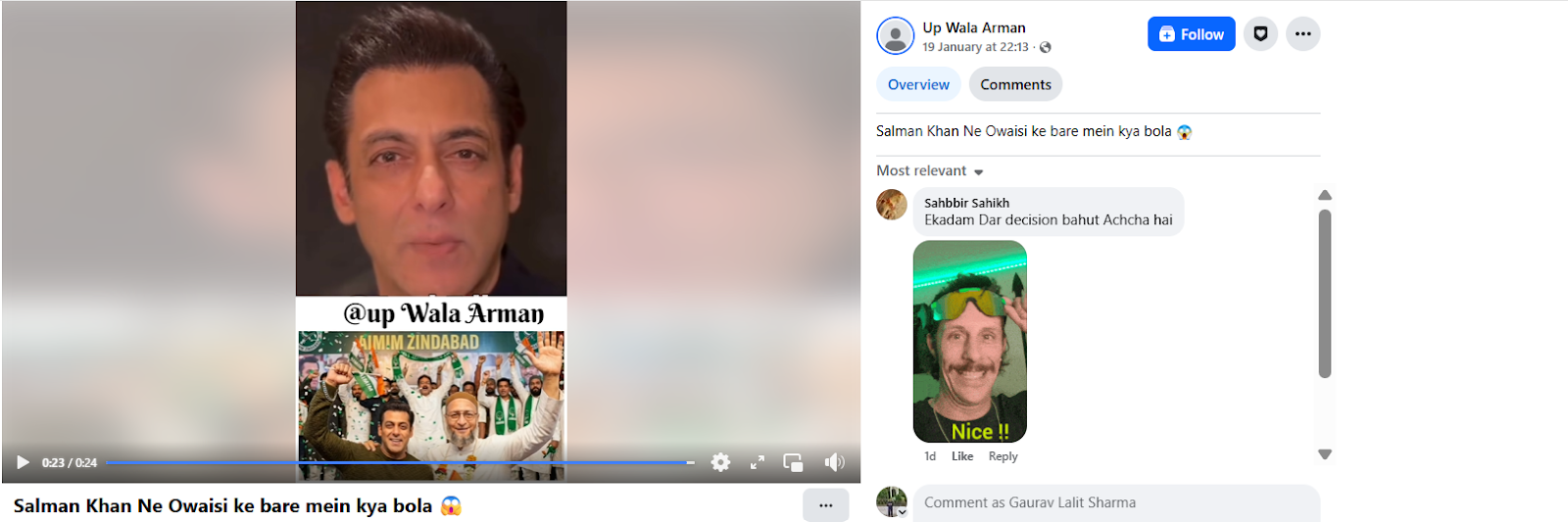
Social media users claim that Salman Khan has announced his decision to join AIMIM.On 19 January 2026, a Facebook user shared the viral video with the caption, “What did Salman say about Owaisi?” In the video, Salman Khan can allegedly be heard saying that he is going to join Owaisi’s party. (The link to the post, its archived version, and screenshots are available.)
Fact Check:
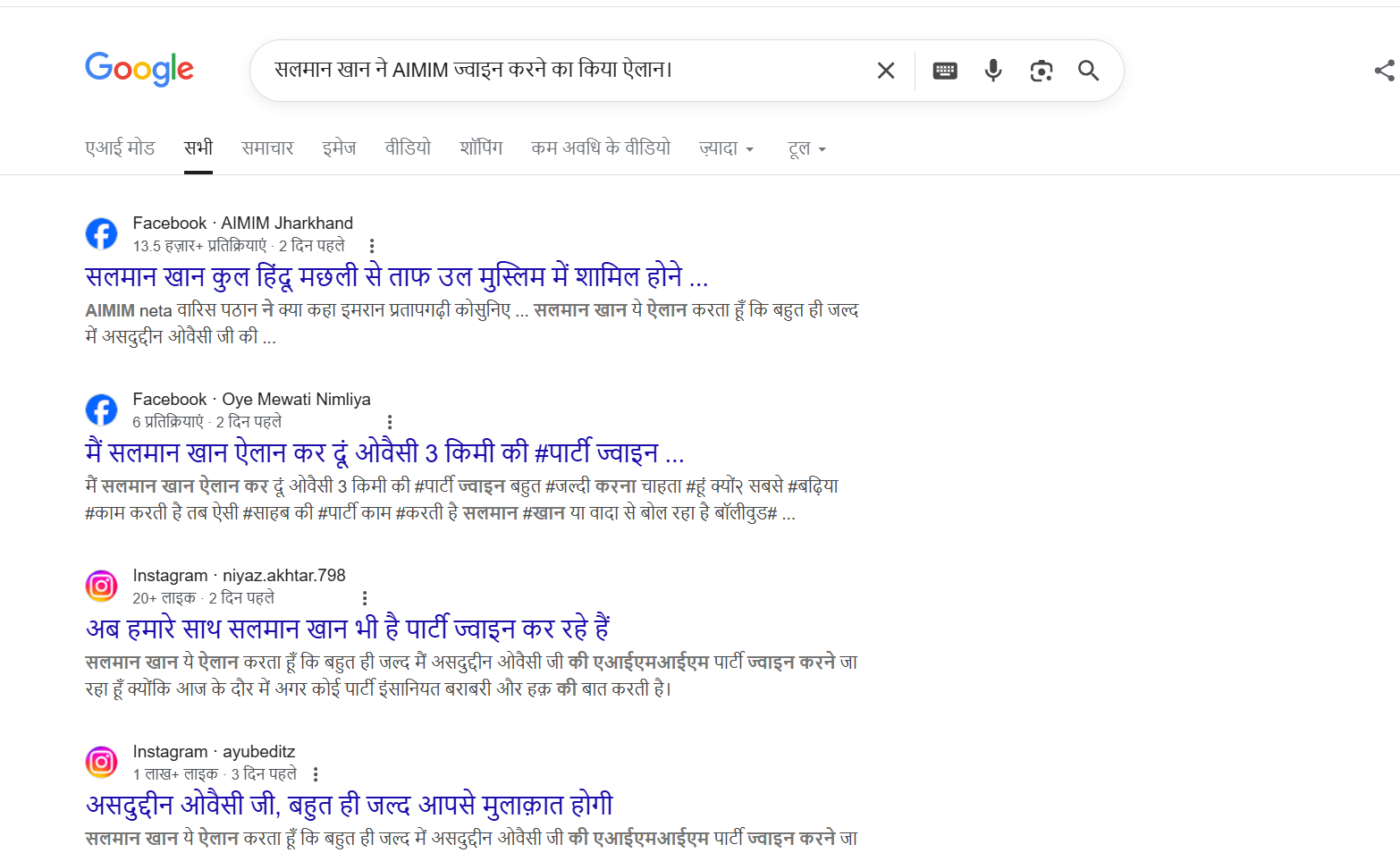
To verify the claim, we first searched Google using relevant keywords. However, no credible or reliable media reports were found supporting the claim that Salman Khan is joining AIMIM.
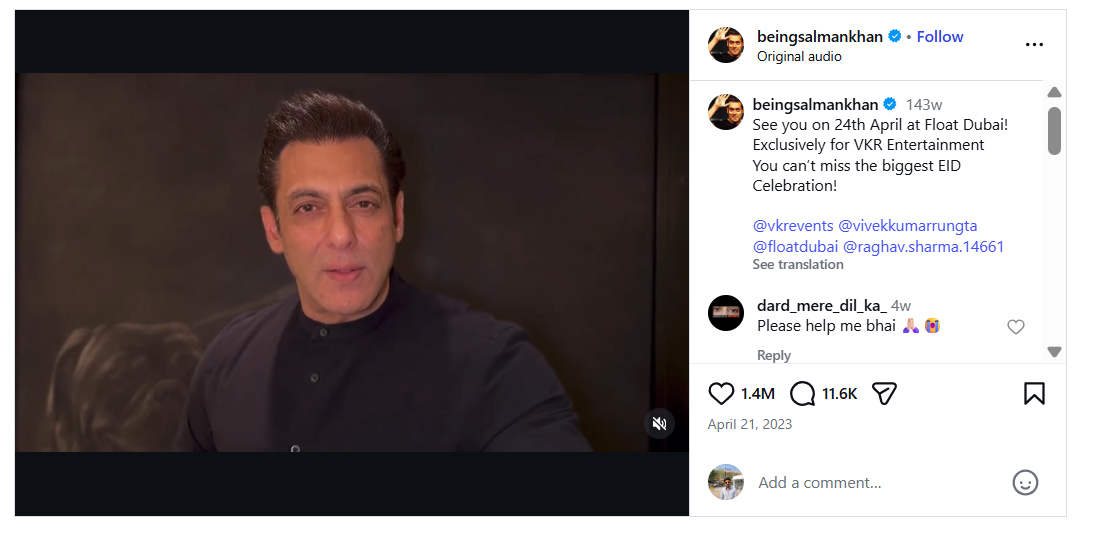
In the next step of verification, we extracted key frames from the viral video and conducted a reverse image search using Google Lens. This led us to a video posted on Salman Khan’s official Instagram account on 21 April 2023. In the original video, Salman Khan is seen talking about an event scheduled to take place in Dubai. A careful review of the full video confirmed that no statement related to AIMIM or Asaduddin Owaisi is made.
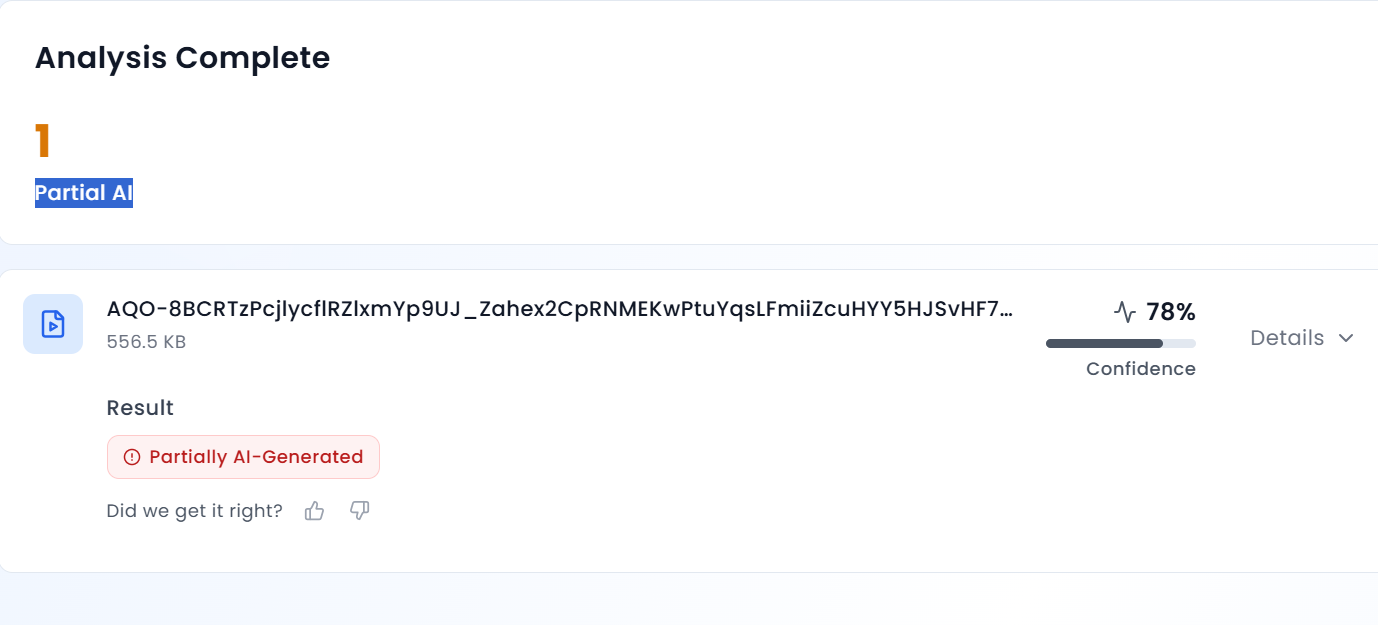
Further analysis of the viral clip revealed that Salman Khan’s voice sounds unnatural and robotic. To verify this, we scanned the video using AURGIN AI, an AI-generated content detection tool. According to the tool’s analysis, the viral video was generated using artificial intelligence.
Conclusion
Salman Khan has not announced that he is joining the AIMIM party. The viral video and the image circulating on social media are AI-generated and manipulated.
Related Blogs

Introduction
A zero-click cyber attack solely relies on software and hardware flaws, bypassing any human factor to infect a device and take control over its data. It is almost impossible to discover the attack and know that the device is hacked unless someone on your side is closely monitoring your network traffic data.
At Kaspersky, security analysts used their SIEM solution KUMA to monitor their corporate WiFi network traffic and discovered this mysterious attack. They took necessary actions to investigate it and even went a step further to dive right into the action and uncover the entire attack chain.
A few months ago, Kaspersky shared their findings about this attack on iOS devices. They shared how these zero-click vulnerabilities were being exploited by the attackers and called this attack ‘Operation Triangulation’.
A zero-click exploit in the network
Kaspersky detected a zero-click attack on the iPhones of their colleagues while monitoring their corporate WiFi network traffic. They managed to get detailed information on all the stages of the attack by simply identifying a pattern in the domain names flowing through their network. Although the attackers were quite experienced, their mistakes helped Kaspersky detect critical vulnerabilities in all iOS devices.
The name-pattern
These previously unsuspected domains had a similar name-style which consisted of two names and ended with ‘.com’, such as ‘backuprabbit.com’ and ‘cloudsponcer.com’. They were used in pairs, one for an exportation process and the other served as a command and control server. These domains showed high outbound traffic, they were registered with NameCheap and protected with Cloudflare.
The network pattern
Each time a connection to these suspicious domains was made, it was preceded by an iMessage connection which indicated these domains are being accessed by iOS devices. It was observed that the devices connected to these domains, downloaded attachments, performed a few requests to a first level domain which was an exploitation framework server, then made regular connections with the second level domain which was a command and control server controlled by the attackers.
Getting more information
To get more information about the attack all the infected devices were collected and backed up after carefully informing the device owners. Although the attackers had managed to clean their artefacts, the backed up data was used to perform digital forensic procedures and find traces of the attacks. This helped Kaspersky to figure out how the infection might be taking place.
The attacker’s mistakes
The attackers deleted all the attachment files and exploits but did not delete the modified SMS attachment folder. That folder had no files left inside it. The attackers removed evidence from other databases as well, like the ‘SMS.db’ database, however another database called ‘datausage.sqlite’ was not sanitised.
The ‘datausage.sqlite’ database is the most important database when it comes to iOS forensics as its contents can be used to track applications and network usage. Upon examination of this database, a process logged as ‘BackupAgent’ was found to be making network connections at the same time the device was making connections to the suspicious domains.
The indicator of compromise
‘BackupAgent’ stood out in this scenario because although it is a legitimate binary, it has been deprecated since iOS4 and it should not have been making any network connections. This identified the ‘BackupAgent’ process as the first solid indicator of compromise in Operation Triangulation. The indicator is termed as- ‘Data usage by process BackupAgent’, and was used to determine if any specific device was infected.
Taking it a step ahead
The team at Kaspersky successfully identified the indicator of compromise and determined which devices were infected, but as the attackers were experienced enough to delete their payloads, they decided to set a trap and perform a man-in-the-middle attack. When they did, the attackers were unable to detect it.
The man-in the-middle attack
Kaspersky prepared a server with ‘WireGuard’ and ‘mitmproxy’. They installed root certificates on devices that could be used as targets for the attackers and routed all the network traffic to that server. They also developed a ‘Telegram’ bot to notify them about new infections as they decrypted the network traffic.
Setting up a bot proved to be an effective way of real time monitoring while modifying all the network packets on-the-fly with ‘mitmproxy’, this gave them unlimited power! Their trap was successful in capturing a payload sent by the attackers and it was analysed in detail.
The name was in the payload
The payload was an HTML page with obfuscator javascript which performed various code checks and canvas footprinting. It rendered a yellow triangle and calculated its hash value. This is why the operation was named Operation Triangulation.
The team at Kaspersky started cracking various layers of asymmetric cryptography with regular expressions. They patched the stages one-by-one on the fly to move the logic from each stage to ‘mitmproxy’ and finally implemented a 400 line ‘mitmproxy’ add-on. This add-on decrypted all the validators, exploits, spyware and additional modules.
The mystery
It is remarkable how Kaspersky detected the attack and identified multiple vulnerabilities, set up a trap to capture a payload and decrypted it completely. They shared all their findings with the device manufacturer and Apple responded by sending out a security patch update addressing four zero-day vulnerabilities.
A zero-click vulnerability
Traditionally any spyware relies on the user to to click on a compromised link or file to initiate the infection. However a zero-click vulnerability is a specific flaw in the device software or hardware that the attacker can use to infect the device without the need for a click or tap from the user.
The vulnerabilities identified
- Tricky Font Flaw (CVE-2023-41990): A clandestine method involving the manipulation of font rendering on iPhones, akin to a secret code deciphered by the attackers.Apple swiftly addressed this vulnerability in versions iOS 15.7.8 and iOS 16.3.
- Kernel Trick (CVE-2023-32434): Exploiting a hidden language understood only by the iPhone's core, the attackers successfully compromised the kernel's integrity.Apple responded with fixes implemented in iOS 15.7.7, iOS 15.8, and iOS 16.5.1.
- Web Sneakiness (CVE-2023-32435): Leveraging a clever ploy in the interpretation of web content by iPhones, the attackers manipulated the device's behaviour.Apple addressed this vulnerability in iOS 15.7.7 and iOS 16.5.1.
- Kernel Key (CVE-2023-38606): The pinnacle of the operation, the attackers discovered a covert method to tamper with the iPhone's core, the kernel.Apple responded with a fix introduced in iOS 16.6, thwarting the intrusion into the most secure facets of the iPhone
Still, how these attackers were able to find this critical vulnerability in a device which stands out for it’s security features is still unknown.
CyberPeace Advisory
Zero-click attacks are a real threat, but you can defend yourself. Being aware of the risks and taking proactive steps can significantly reduce vulnerability. Regularly installing the latest updates for your operating system, apps, and firmware helps patch vulnerabilities before attackers can exploit them.
- Keep your software updated as they contain crucial security patches that plug vulnerabilities before attackers can exploit them.
- Use security software to actively scan for suspicious activity and malicious code, acting as a first line of defence against zero-click intrusions.
- Be cautious with unsolicited messages if the offer seems too good to be true or the link appears suspicious as it can contain malware that can infect your device.
- Disable automatic previews as it can potentially trigger malicious code hidden within the content.
- Be mindful of what you install and avoid unverified apps and pirated software, as they can be Trojan horses laden with malware.
- Stay informed about the latest threats and updates by following reliable news sources and security blogs to stay ahead of the curve, recognize potential zero-click scams and adjust your behaviour accordingly.
Check out our (advisory report)[add report link] to get in depth information.
Conclusion
Operation Triangulation stands as a testament to the continuous cat-and-mouse game between cybercriminals and tech giants. While the covert spy mission showcased the vulnerabilities present in earlier iPhone versions, Apple's prompt response underscores the commitment to user security. As the digital landscape evolves, vigilance, timely updates, and collaborative efforts remain essential in safeguarding against unforeseen cyber threats.
References:
- Operation Triangulation: iOS devices targeted with previously unknown malware | Securelist, 1 June, 2023
- Operation Triangulation: The last (hardware) mystery | Securelist, 27 December, 2023.
- 37C3 - Operation Triangulation: What You Get When Attack iPhones of Researchers (youtube.com), 29 December,2023

Executive Summary:
Recently, we came upon some AI-generated deep fake videos that have gone viral on social media, purporting to show Indian political figures Prime Minister Narendra Modi, Home Minister Amit Shah, and External Affairs Minister Dr. S. Jaishankar apologizing in public for initiating "Operation Sindoor." The videos are fake and use artificial intelligence tools to mimic the leaders' voices and appearances, as concluded by our research. The purpose of this report is to provide a clear understanding of the facts and to reveal the truth behind these viral videos.
Claim:
Multiple videos circulating on social media claim to show Prime Minister Narendra Modi, Central Home Minister Amit Shah, and External Affairs Minister Dr. S. Jaishankar publicly apologised for launching "Operation Sindoor." The videos, which are being circulated to suggest a political and diplomatic failure, feature the leaders speaking passionately and expressing regret over the operation.



Fact Check:
Our research revealed that the widely shared videos were deepfakes made with artificial intelligence tools. Following the 22 April 2025 Pahalgam terror attack, after “Operation Sindoor”, which was held by the Indian Armed Forces, this video emerged, intending to spread false propaganda and misinformation.
Finding important frames and visual clues from the videos that seemed suspicious, such as strange lip movements, misaligned audio, and facial distortions, was the first step in the fact-checking process. By putting audio samples and video frames in Hive AI Content Moderation, a program for detecting AI-generated content. After examining audio, facial, and visual cues, Hive's deepfake detection system verified that all three of the videos were artificial intelligence (AI) produced.
Below are three Hive Moderator result screenshots that clearly flag the videos as synthetic content, confirming that none of them are authentic or released by any official government source.



Conclusion:
The artificial intelligence-generated videos that claim Prime Minister Narendra Modi, Home Minister Amit Shah, and External Affairs Minister Dr. S. Jaishankar apologized for the start of "Operation Sindoor" are completely untrue. A purposeful disinformation campaign to mislead the public and incite political unrest includes these deepfake videos. No such apology has been made by the Indian government, and the operation in question does not exist in any official or verified capacity. The public must exercise caution, avoid disseminating videos that have not been verified, and rely on reliable fact-checking websites. Such disinformation can seriously affect national discourse and security in addition to eroding public trust.
- Claim: India's top executives apologize publicly for Operation Sindoor blunder.
- Claimed On: Social Media
- Fact Check: AI Misleads

Executive Summary:
An alleged video is making the rounds on the internet featuring Ranveer Singh criticizing the Prime Minister Narendra Modi and his Government. But after examining the video closely it revealed that it has been tampered with to change the audio. In fact, the original videos posted by different media outlets actually show Ranveer Singh praising Varanasi, professing his love for Lord Shiva, and acknowledging Modiji’s role in enhancing the cultural charms and infrastructural development of the city. Differences in lip synchronization and the fact that the original video has no sign of criticizing PM Modi show that the video has been potentially manipulated in order to spread misinformation.

Claims:
The Viral Video of Bollywood actor Ranveer Singh criticizing Prime Minister Narendra Modi.

Fact Check:
Upon receiving the Video we divided the video into keyframes and reverse-searched one of the images, we landed on another video of Ranveer Singh with lookalike appearance, posted by an Instagram account named, “The Indian Opinion News''. In the video Ranveer Singh talks about his experience of visiting Kashi Vishwanath Temple with Bollywood actress Kriti Sanon. When we watched the Full video we found no indication of criticizing PM Modi.

Taking a cue from this we did some keyword search to find the full video of the interview. We found many videos uploaded by media outlets but none of the videos indicates criticizing PM Modi as claimed in the viral video.

Ranveer Singh shared his thoughts about how he feels about Lord Shiva, his opinions on the city and the efforts undertaken by the Prime Minister Modi to keep history and heritage of Varanasi alive as well as the city's ongoing development projects. The discrepancy in the viral video clip is clearly seen when we look at it closely. The lips are not in synchronization with the words which we can hear. It is clearly seen in the original video that the lips are in perfect synchronization with the words of audio. Upon lack of evidence to the claim made and discrepancies in the video prove that the video was edited to misrepresent the original interview of Bollywood Actor Ranveer Singh. Hence, the claim made is misleading and false.
Conclusion:
The video that claims Ranveer Singh criticizing PM Narendra Modi is not genuine. Further investigation shows that it has been edited by changing the audio. The original footage actually shows Singh speaking positively about Varanasi and Modi's work. Differences in lip-syncing and upon lack of evidence highlight the danger of misinformation created by simple editing. Ultimately, the claim made is false and misleading.
- Claim: A viral featuring Ranveer Singh criticizing the Prime Minister Narendra Modi and his Government.
- Claimed on: X (formerly known as Twitter)
- Fact Check: Fake & Misleading


