#FactCheck: Viral video blast of fuel tank in UAE Al Hariyah Port portray as Russia-Ukraine Conflict
Executive Summary:
A viral video showing flames and thick smoke from large fuel tanks has been shared widely on social media. Many claimed it showed a recent Russian missile attack on a fuel depot in Ukraine. However, our research found that the video is not related to the Russia-Ukraine conflict. It actually shows a fire that happened at Al Hamriyah Port in Sharjah, United Arab Emirates, on May 31, 2025. The confusion was likely caused by a lack of context and misleading captions.

Claim:
The circulating claim suggests that Russia deliberately bombed Ukraine's fuel reserves and the viral video shows evidence of the bombing. The posts claim the fuel depot was destroyed purposefully during military operations, implying an increase in violence. This narrative is intended to generate feelings and reinforce fears related to war.

Fact Check:
After doing a reverse image search of the key frames of the viral video, we found that the video is actually from Al Hamriyah Port, UAE, not from the Russia-Ukraine conflict. During further research we found the same visuals were also published by regional news outlets in the UAE, including Gulf News and Khaleej Times, which reported on a massive fire at Al Hamriyah Port on 31 May 2025.
As per the news report, a fire broke out at a fuel storage facility in Al Hamriyah Port, UAE. Fortunately, no casualties were reported. Fire Management Services responded promptly and successfully brought the situation under control.


Conclusion:
The belief that the viral video is evidence of a Russian strike in Ukraine is misleading and incorrect. The video is actually of a fire at a commercial port in the UAE. When you share misleading footage like that, you distort reality and incite fear based on lies. It is simply a reminder that not all viral media is what it appears to be, and every viewer should take the time to check and verify the content source and context before accepting or reposting. In this instance, the original claim is untrue and misleading.
- Claim: Fresh attack in Ukraine! Russian military strikes again!
- Claimed On: Social Media
- Fact Check: False and Misleading
Related Blogs

Executive Summary
A deepfake video is being widely circulated on social media with a false claim that External Affairs Minister S. Jaishankar admitted in a podcast interview that India was surprised by Pakistan’s counter-response during “Operation Sindoor” and suffered some losses. However, a fact-check by CyberPeace Research Wing has found the claim to be fake. The research shows that AI-generated audio has been used to misrepresent the External Affairs Minister’s remarks.
Claim
A Facebook user shared the viral video claiming that in a recent podcast with journalist Smita Prakash, Jaishankar admitted that Pakistan’s aggressive response during Operation Sindoor had caught India off guard.
Fact Check
A review of the original interview on ANI’s YouTube channel shows that the conversation between Smita Prakash and S. Jaishankar was uploaded on May 24, 2024—well before Operation Sindoor.
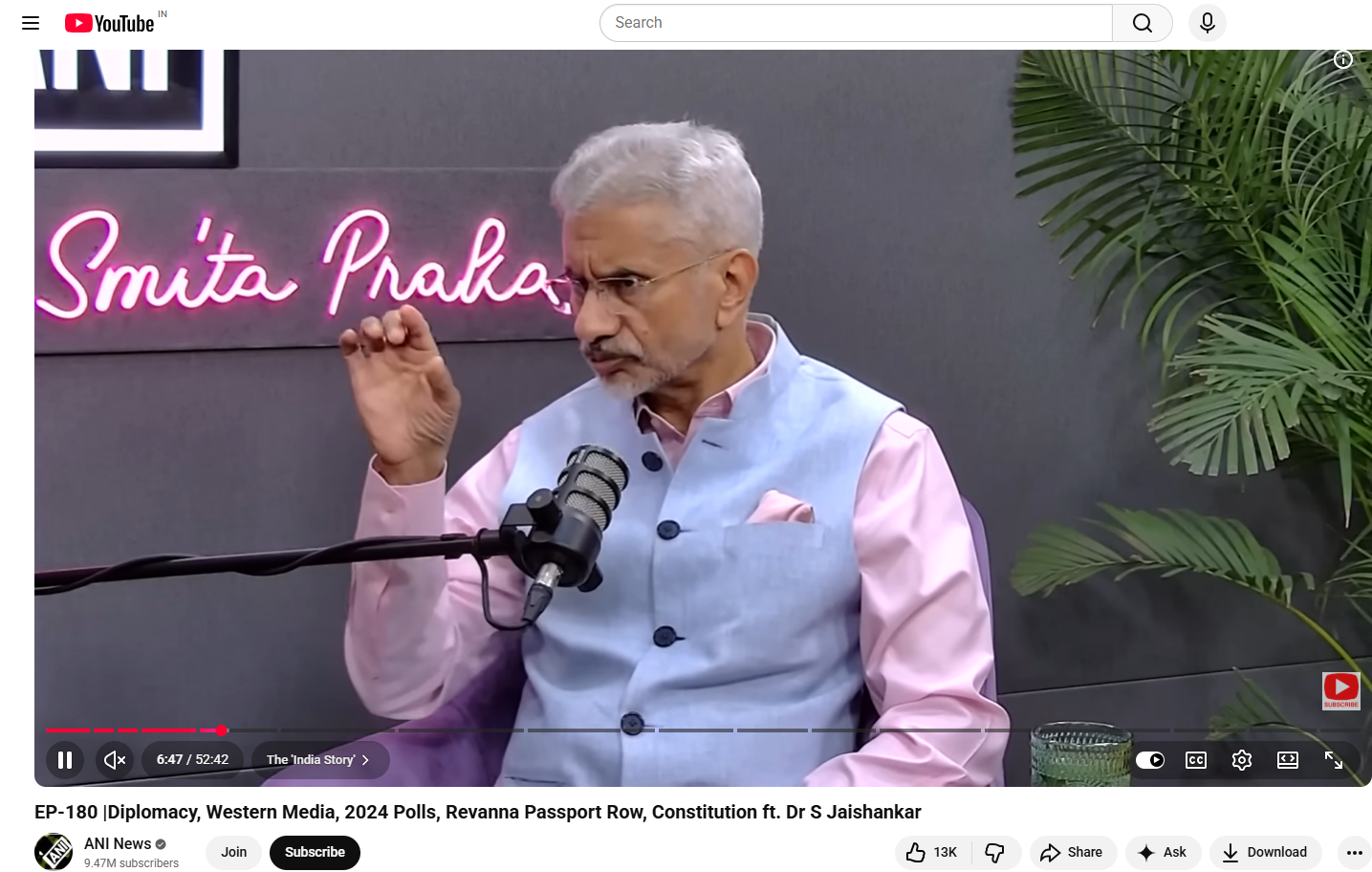
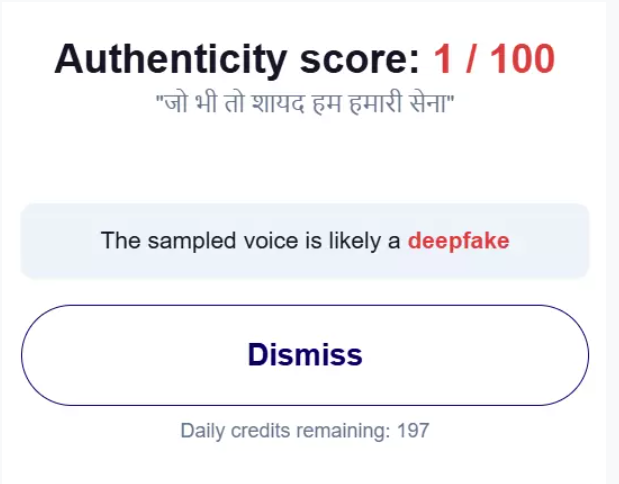
Operation Sindoor reportedly began on May 7, 2025. In the original video, there is no mention of Operation Sindoor or any Pakistani counter-response, making the viral claim baseless. Further analysis using AI detection tools such as Hive Moderation and Hiya indicated that the audio in the viral clip is likely AI-generated, suggesting manipulation of the original content.
Conclusion
The viral video is fake. AI-generated audio has been used to alter an old interview and falsely attribute statements to External Affairs Minister S. Jaishankar.
Introduction
India is seeing a major change due to the introduction of Artificial Intelligence (AI) across all sectors of government, business, and the digital economy with regard to areas such as governance, healthcare, finance, and the infrastructure. The large scale and rapid pace of AI implementation are expected to lead to efficiency gains, innovations in products and services, and to drive economic growth; however, the growth of AI also creates many serious concerns regarding ethics, legality, and societal ramifications. Issues such as algorithmic bias in the use of algorithms by AI, a lack of transparency in decision-making algorithms, data protection risks resulting from AI employments, and unclear frameworks for determining accountability for AI-related action; bring issues of how we will govern AI in a responsible manner to the forefront of public policy discourse.
India wants to become an AI superpower and leader in technology on the world stage. As such, India has a dual responsibility to fuel innovation without discounting democratic ideals, human rights, and public trust. UNESCO's AI Readiness Assessment Methodology (RAM) is a global tool for AI governance, created to provide concrete policy guidance on how to make ethical AI a reality. The India AI RAM Report is set to be formally released by UNESCO during the India AI Impact Summit 2026, taking place in New Delhi, as a major milestone in India's developing AI governance journey.
What is UNESCO’s AI Readiness Assessment Methodology (RAM)?
UNESCO has created a simple yet effective tool, called the AI Readiness Assessment Methodology (RAM), that can assist governments in determining how well they are prepared to develop, deploy and manage Artificial Intelligence ethically, responsibly and trustworthily. RAM provides a framework for diagnosing and self-assessing the state of a country’s ability to govern AI on the basis of evidence-based decision making rather than serving as a regulatory framework or ranking system.
The most important goal of RAM is to assess a country’s overall state of readiness to govern AI based on four dimensions: institutionally, legally, socially and technologically. In doing so, RAM examines how institutions function, their maturity level and the extent to which various policies align with one another; thereby giving governments an overview of strengths, weaknesses and priorities for reform.
Unlike other frameworks, RAM does not prescribe any one-size-fits-all solutions; instead, it uses a context sensitive approach when implementing the concepts of AI governance due to differing national realities, developmental priorities and social/economic conditions. Using the ethical principles established by UNESCO, RAM converts these principles into practical actions that can guide countries in their transition from abstract commitments to concrete strategies for governing AI.
Key Dimensions Assessed Under RAM
UNESCO's AI Readiness Assessment Methodology (RAM) is a tool used to assess a country's readiness to implement ethical Artificial Intelligence through five interconnected dimensions. These include: the legal and regulatory dimension (which looks at the laws, rules, and safeguards that are currently in place related to AI), the social and cultural dimension (which looks at whether the public is aware of AI, whether it trusts AI, whether AI is an inclusive experience for all people who use AI and whether AI has affected society in various ways), and the economic dimension (which looks at innovation, participation from industry, and readiness of the market for AI).
Also included in the framework/functionality of the RAM are: scientific and educational dimension (which examines a country’s capacity to conduct serious scientific research, including research activities that prepare persons to be employable in AI jobs); and technological and infrastructure dimension (which examines the availability of data, digital infrastructure, and computing capabilities for AI projects in a country).
All five of these dimensions consider the entirety of the scope of an AI readiness evaluation to ensure that AI Governance is more than just a technical issue; rather, it is a condition of a country’s capacity to generate laws, create policy and maintain social equality in relation to all forms of Artificial Intelligence.
Methodology and Nationwide Consultative Process
RAM takes both qualitative and quantitative characteristics together to create an overall understanding of how ready any nation is for AI capabilities. It is designed with flexibility so nations can define their assessments with respect to their own institutional capabilities and development agenda.
Normally, RAM is implemented by an independent expert who is assisted by a national team consisting of various stakeholders. With respect to the RAM process used in India, it was conducted as a national consultation where representatives from across all sectors of society (government, private sector, academia, civil society, and young people) participated in the assessment's creation. This consultation process made sure there were many different viewpoints present, which increased the legitimacy of the assessment results and how relevant they are in each country. The consultation process also yields policy recommendations based on real life governing situations or challenges that are specific to different sectors.
Institutional Partnerships Behind India’s RAM
The India RAM Initiative was developed by the UNESCO South Asia Regional Office (as a partner of IndiaAI Mission and the Indian Ministry of Electronics and Information Technology) and implemented by Ikigai Law with the help of The Patrick J. McGovern Foundation. This demonstrated the need for and importance of partnership in developing governance frameworks for Artificial Intelligence (AI). The result of the RAM process is a collaborative effort that includes evidence-based international norm-setting capabilities from around the world; government policies under the guidance of national political leadership; independent legal-technical implementation; input from civil society; all with the goal of empowering (increasing) India's ability to establish and implement both a consistent (i.e., coherent) and comprehensive (i.e., inclusive) AI Governance Framework.
Significance of the India AI RAM Report and Its Launch
The India AI RAM Report provides a complete initial assessment of India’s AI ecosystem and includes key insights into AI readiness, governance strengths/weaknesses, and potential opportunities across multiple sectors. It identifies priority areas to promote a responsible and trustworthy AI ecosystem in India.
The report will be officially released during the India AI Impact Summit (February 16, 2026 at Bharat Mandapam, New Delhi) where Mr. Abhishek Venkateswaran (National Project Officer-Social and Human Sciences at UNESCO South Asia) offered additional insight into the consultative process and the overall importance of this launch on India's future AI policy path.
Policy Relevance and the Road Ahead
The RAM Framework gives the government a structure and roadmap for developing and implementing AI Governance. In doing this, RAM reinforces the alignment of IndiaAI Mission, which includes safety and trust in AI as one of the pillars. However, the results from this Assessment will not automatically translate to reforming institutions, issuing guidelines specific to sectors, or developing a mechanism for continued evaluation. Implementation will require strong and sustained commitment from political leaders, as well as the commitment of institutions involved in the reforms made possible by RAM's implementation.
Conclusion
UNESCO has developed an AI Readiness Assessment Methodology (AI-RAM) that can greatly advance the way India approaches governance with respect to artificial intelligence (AI). By focusing on "readiness" (doing what needs to be done), "responsibility" (being or having good moral principles) and "inclusivity" (including everyone), the AI-RAM will enable India to become an active participant in discussions around ethical use of AI at a global level. India is now positioned to take on a leadership role in the world by adopting this methodology, which provides a platform for establishing global standards for AI development. The real benefit of the AI-RAM will come from policy measures that will ensure future AI development in India is 'human-centered', 'trustworthy' and 'aligns with democratic values'.
References
- https://icaire.org/files/UNESCORam-en.pdf
- https://www.pib.gov.in/PressReleasePage.aspx?PRID=2134492®=3&lang=2
- https://www.facebook.com/unesconewdelhi/videos/unesco-is-set-to-launch-the-india-ai-readiness-assessment-methodology-ram-report/25955631820699516/
- https://www.unesco.org/ethics-ai/en/ram
- https://www.hindustantimes.com/india-news/unesco-meity-launch-exercise-to-assess-india-s-ai-readiness-101749188341803.html#
- https://www.manoramayearbook.in/current-affairs/india/2025/06/09/unesco-ai-readiness-assessment-methodology-ram.html

Introduction
The Telecom Regulatory Authority of India (TRAI) has directed all telcos to set up detection systems based on Artificial Intelligence and Machine Learning (AI/ML) technologies in order to identify and control spam calls and text messages from unregistered telemarketers (UTMs).
The TRAI Directed telcos
The telecom regulator, TRAI, has directed all Access Providers to detect Unsolicited commercial communication (UCC)by systems, which is based on Artificial Intelligence and Machine Learning to detect, identify, and act against senders of Commercial Communication who are not registered in accordance with the provisions of the Telecom Commercial Communication Customer Preference Regulations, 2018 (TCCCPR-2018). Unregistered Telemarketers (UTMs) are entities that do not register with Access Providers and use 10-digit mobile numbers to send commercial communications via SMS or calls.
TRAI steps to curb Unsolicited commercial communication
TRAI has taken several initiatives to reduce Unsolicited Commercial Communication (UCC), which is a major source of annoyance for the public. It has resulted in fewer complaints filed against Registered Telemarketers (RTMs). Despite the TSPs’ efforts, UCC from Unregistered Telemarketers (UTMs) continues. Sometimes, these UTMs use messages with bogus URLs and phone numbers to trick clients into revealing crucial information, leading to financial loss.
To detect, identify, and prosecute all Unregistered Telemarketers (UTMs), the TRAI has mandated that Access Service Providers implement the UCC.
Detect the System with the necessary functionalities within the TRAI’s Telecom Commercial Communication Customer Preference Regulations, 2018 framework.
Access service providers have implemented such detection systems based on their applicability and practicality. However, because UTMs are constantly creating new strategies for sending unwanted communications, the present UCC detection systems provided by Access Service providers cannot detect such UCC.
TRAI also Directs Telecom Providers to Set Up Digital Platform for Customer Consent to Curb Promotional Calls and Messages.
Unregistered Telemarketers (UTMs) sometimes use messages with fake URLs and phone numbers to trick customers into revealing essential information, resulting in financial loss.

TRAI has urged businesses like banks, insurance companies, financial institutions, and others to re-verify their SMS content templates with telcos within two weeks. It also directed telecom companies to stop misusing commercial messaging templates within the next 45 days.
The telecom regulator has also instructed operators to limit the number of variables in a content template to three. However, if any business intends to utilise more than three variables in a content template for communicating with their users, this should be permitted only after examining the example message, as well as adequate justifications and justification.
In order to ensure consistency in UCC Detect System implementations, TRAI has directed all Access Providers to deploy UCC and detect systems based on artificial intelligence and Machine Learning that are capable of constantly evolving to deal with new signatures, patterns, and techniques used by UTMs.
Access Providers have also been directed to use the DLT platform to share intelligence with others. Access Providers have also been asked to ensure that such UCC Detect System detects senders that send unsolicited commercial communications in bulk and do not comply with the requirements. All Access Providers are directed to follow the instructions and provide an update on actions done within thirty days.
The move by TRAI is to curb the menacing calls as due to this, the number of scam cases is increasing, and now a new trend of scams started as recently, a Twitter user reported receiving an automated call from +91 96681 9555 with the message “This call is from Delhi Police.” It then asked her to stay in the queue since some of her documents needed to be picked up. Then he said he works as a sub-inspector at the Kirti Nagar police station in New Delhi. He then inquired whether she had recently misplaced her Aadhaar card, PAN card, or ATM card, to which she replied ‘no’. The scammer then poses as a cop and requests that she authenticate the last four digits of her card because they have found a card with her name on it. And a lot of other people tweeted about it.

Conclusion
TRAI directed the telcos to check the calls and messages from Unregistered numbers. This step of TRAI will curb the pesky calls and messages and catch the Frauds who are not registered with the regulation. Sometimes the unregistered sender sends fraudulent links, and through these fraudulent calls and messages, the sender tries to take the personal information of the customers, which results in financial losses.


