#FactCheck: Viral image shows the Maldives mocking India with a "SURRENDER" sign on photo of Prime Minister Narendra Modi
Executive Summary:
A manipulated viral photo of a Maldivian building with an alleged oversized portrait of Indian Prime Minister Narendra Modi and the words "SURRENDER" went viral on social media. People responded with fear, indignation, and anxiety. Our research, however, showed that the image was manipulated and not authentic.

Claim:
A viral image claims that the Maldives displayed a huge portrait of PM Narendra Modi on a building front, along with the phrase “SURRENDER,” implying an act of national humiliation or submission.

Fact Check:
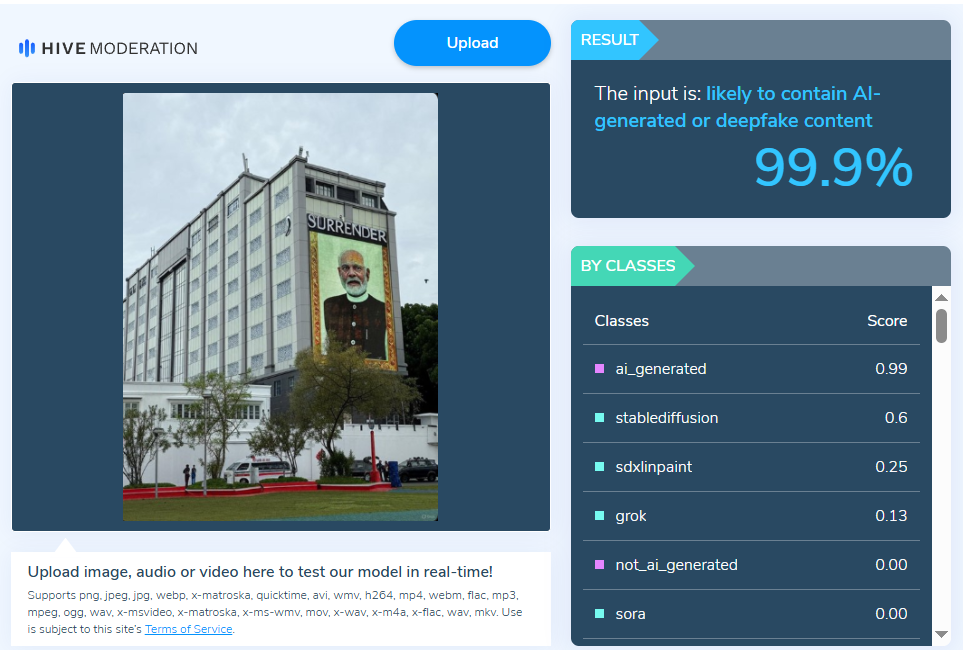
After a thorough examination of the viral post, we got to know that it had been altered. While the image displayed the same building, it was wrong to say it included Prime Minister Modi’s portrait along with the word “SURRENDER” shown in the viral version. We also checked the image with the Hive AI Detector, which marked it as 99.9% fake. This further confirmed that the viral image had been digitally altered.
During our research, we also found several images from Prime Minister Modi’s visit, including one of the same building displaying his portrait, shared by the official X handle of the Maldives National Defence Force (MNDF). The post mentioned “His Excellency Prime Minister Shri @narendramodi was warmly welcomed by His Excellency President Dr.@MMuizzu at Republic Square, where he was honored with a Guard of Honor by #MNDF on his state visit to Maldives.” This image, captured from a different angle, also does not feature the word “surrender.


Conclusion:
The claim that the Maldives showed a picture of PM Modi with a surrender message is incorrect and misleading. The image is altered and is being spread to mislead people and stir up controversy. Users should check the authenticity of photos before sharing.
- Claim: Viral image shows the Maldives mocking India with a surrender sign
- Claimed On: Social Media
- Fact Check: False and Misleading
Related Blogs

Introduction
US President Biden takes a step by signing a key executive order to manage the risks posed by AI. The new presidential order on Artificial intelligence (AI) sets rules on the rapidly growing technology that has big potential but also covers risks. The presidential order was signed on 30th October 2023. It is a strong action that the US president has taken on AI safety and security. This order will require the developers to work on the most powerful AI model to share their safety test results with the government before releasing their product to the public. It also includes developing standards for ethically using AI and for detecting AI-generated content and labelling it as such. Tackling the many dangers of AI as it rapidly advances, the technology poses certain risks by replacing human workers, spreading misinformation and stealing people's data. The white house is also making clear that this is not just America’s problem and that the US needs to work with the world to set standards here and to ensure the responsible use of AI. The white house is also urging Congress to do more and pass comprehensive privacy legislation. The order includes new safety guidelines for AI developers, standards to disclose AI-generated content and requirements for federal agencies that are utilising AI. The white house says that it is the strongest action that any government has taken on AI safety and security. In the most recent events, India has reported the biggest ever data breach, where data of 815 million Indians has been leaked. ICMR is the Indian Council of Medical Research and is the imperial medical research institution of India.
Key highlights of the presidential order
The presidential order requires developers to share safety test results. It focuses on developing standards, tools & tests to ensure safe AI. It will ensure protection from AI-enabled frauds and protect Americans' privacy, advance equity and civil rights, stand up for consumers and workers, promote innovation and competition, protect against risks of using AI to engineer dangerous material and provide guidelines for detecting AI -AI-generated content and establishing overall standards for AI safety and security.
Online content authentication and labelling
Biden administration has asked the Department of Commerce to set guidelines to help authenticate content coming from the government, meaning the American people should be able to trust official documents coming from the government. So, focusing on content authentication, they have also talked about labelling AI-generated content, making the differentiation between a real authentic piece of content and something that has been manipulated or generated using AI.
ICMR Breach
On 31/10/2023, an American intelligence and cybersecurity agency flagged the biggest-ever data breach, putting the data of 81.5 crore Indians at stake and at at potential risk of making its way to the dark market. The cyber agency has informed that a ‘threat actor’, also known as ‘pwn001’ shared a thread on Breach Forums, which is essentially claimed as the ‘premier Databreach discussion and leaks forum’. The forum confirms a breach of 81.5 crore Indians. As of today,, ICRM has not issued any official statement, but it has informed the government that the prestigious Central Bureau of Investigation (CBI) will be taking on the investigation and apprehending the cybercriminals behind the cyber attack. The bad actor’s alias, 'pwn001,' made a post on X (formerly Twitter); the post informed that Aadhaar and passport information, along with personal data such as names, phone numbers, and addresses. It is claimed that the data was extracted from the COVID-19 test details of citizens registered with ICMR. This poses a serious threat to the Indian Netizen from any form of cybercrime from anywhere in the world.
Conclusion:
The US presidential order on AI is a move towards making Artificial intelligence safe and secure. This is a major step by the Biden administration, which is going to protect both Americans and the world from the considerable dangers of AI. The presidential order requires developing standards, tools, and tests to ensure AI safety. The US administration will work with allies and global partners, including India, to develop a strong international framework to govern the development and use of AI. It will ensure the responsible use of AI. With the passing of legislation such as the Digital Personal Data Protection Act, 2023, it is pertinent that the Indian government works towards creating precautionary and preventive measures to protect Indian data. As the evolution of cyber laws is coming along, we need to keep an eye on emerging technologies and update/amend our digital routines and hygienes to stay safe and secure.
References:
- https://m.dailyhunt.in/news/india/english/lokmattimes+english-epaper-lokmaten/biden+signs+landmark+executive+order+to+manage+ai+risks-newsid-n551950866?sm=Y
- https://www.hindustantimes.com/technology/in-indias-biggest-data-breach-personal-information-of-81-5-crore-people-leaked-101698719306335-amp.html?utm_campaign=fullarticle&utm_medium=referral&utm_source=inshorts

Cyber attacks in India besides becoming common are also getting deadlier. Each strike has taken proportions to drive home the fact that no one is safe.
Hacker ‘John Wick’, hasn’t spared India’s PM or Paytm. Cyber intelligence firm Cyble which dredges the Dark Web has red-flagged hacking episodes at Truecaller, Dunzo, Unacademy, Naukri.com, Bharat Earth Movers Limited (BEML), LimeRoad and IndiaBulls.Picture this, Mumbai-based cybersecurity firm Sequretek, says in Covid-hit 2020, India has seen a 4000% spike in phishing emails and a 400% uptake in the number of policy violations that have grown over 400% as per the latest statistics.Besides the threat to crucial data, the cost suffered by companies is phenomenal. According to a report by IBM’s ‘Cost of a Data Breach Report 2020’ report, Indian companies witnessed an average $2 Mn total cost of data breach in 2020, this is an increase of 9.4% from 2019.
Another survey by Barracuda Networks revealed that 66% of Indian organisations have had at least one data breach or cybersecurity incident since shifting to a remote working model during the pandemic.
Indian Startups At Mercy Of Cyber Attacks
More recently personal data of 2.8 Lakh WhiteHat Jr students and teachers were exposed, where crucial details of minors have been made available on the dark web. Another major breach that took place this week and exclusively reported by Inc42 was when data of 1.4 Mn job seekers was leaked when jobs portal IIMjobs was hacked.
Vineet Kumar, the founder of Cyber Peace Foundation (CPF), a think tank of cybersecurity and policy experts, said that with the increased digitisation of companies and their processes, data has become the new oil.
“You get good money when you sell users data on the dark web. Hackers discovering vulnerabilities and using SQL injections to pull entire databases remains a common practice for hacking,” Kumar told Inc42.
The CyberPeace Foundation says from mid-April to the end of June it noticed 8,98,7841 attacks, July and August saw 64,52,898 attacks. Whereas September and October saw 1,37,37,516 attacks and 18,149,233 attacks respectively.
Speaking to Inc42, Pankit Desai, cofounder and CEO, Sequretek says, “Originally only a limited set of systems were being exposed, now with WFH all systems have to be exposed to the internet as all your processes are enabled remotely. WFH also creates an additional challenge where ‘personal assets are being used for professional purposes’ and ‘professional assets are being used for personal purposes.”
Malwares like SpyMax, Blackwater are being used as a combination of phishing mails and poorly secured home computers to harvest credentials. These credentials are then used for carrying out attacks. The number of attacks with harvested credentials is already up 30%, the company revealed.
Government data shows that in 2019 alone, India witnessed 3.94 lakh instances of cybersecurity breaches. In terms of hacking of state and central government websites, Indian Computer Emergency Response Team (CERT-In) data shows that a total of 336 websites belonging to central ministries, departments, and state governments were hacked between 2017 and 2019.
According to Nasscom’s Data Security Council of India (DSCI) report 2019, India witnessed the second-highest number of cyber attacks in the world between 2016 and 2018. This comes at a time when digitisation of the Indian economy is predicted to result in a $435 Bn opportunity by 2025.On September 22, the Ministry of Electronics and Information Technology (MeITY) told the Parliament that Indian citizens, commercial and legal entities faced almost 7 lakh cyberattacks till August this year.
The Indian Computer Emergency Response Team (CERT-In) has “reported 49,455, 50,362, 53,117, 208,456, 394,499 and 696,938 cybersecurity incidents during the year 2015, 2016, 2017, 2018, 2019 and 2020 (till August) respectively,” the MeITY said while responding to an unstarred question in the Lok Sabha regarding cyberattacks on Indian citizens and India-based commercial and legal entities.“
India also lacks a cohesive nation-wide cyber-strategy, policies, and procedures. Regulations around data privacy, protection, and penalty should be enacted and enforced as these measures will help businesses evaluate their cybersecurity posture and seek ways to improve. Currently, incident reporting is not mandatory. By making it compulsory, there will be a body of research data that can provide insights on threats to India and inform the government on strategies it can undertake to strengthen the nation’s cyber posture,” said Kumar Ritesh, founder and CEO, Cyfirma.The Internet Crime Report for 2019, released by the USA’s Internet Crime Complaint Centre of the Federal Bureau of Investigation (FBI), has revealed that India stands third in the world among top 20 countries that are victims of internet crimes.
Kumar attributes these numbers to Indian’s lack of basic cyber awareness. However, a poignant point is also the lack of a robust cybersecurity policy in India. Though the issue was touched upon by Prime Minister Narendra Modi during his Independence Day speech on Aug 15, 2020, not much movement has happened on that front.
“Cybersecurity is a very important aspect, which cannot be ignored. The government is alert on this and is working on a new, robust policy,” Modi said.The PM’s announcement was made in the backdrop of the government’s initiative to connect 1.5 lakh gram panchayats through an optical fiber network, thereby increasing the country’s internet connectivity.
With India pipped to take on the world with its IT prowess and increased digital integration the need for a robust policy is now more than ever.
Source: https://inc42.com/buzz/3-94-lakhs-and-counting-how-cyberattacks-are-a-worry-for-digital-india/
Executive Summary:
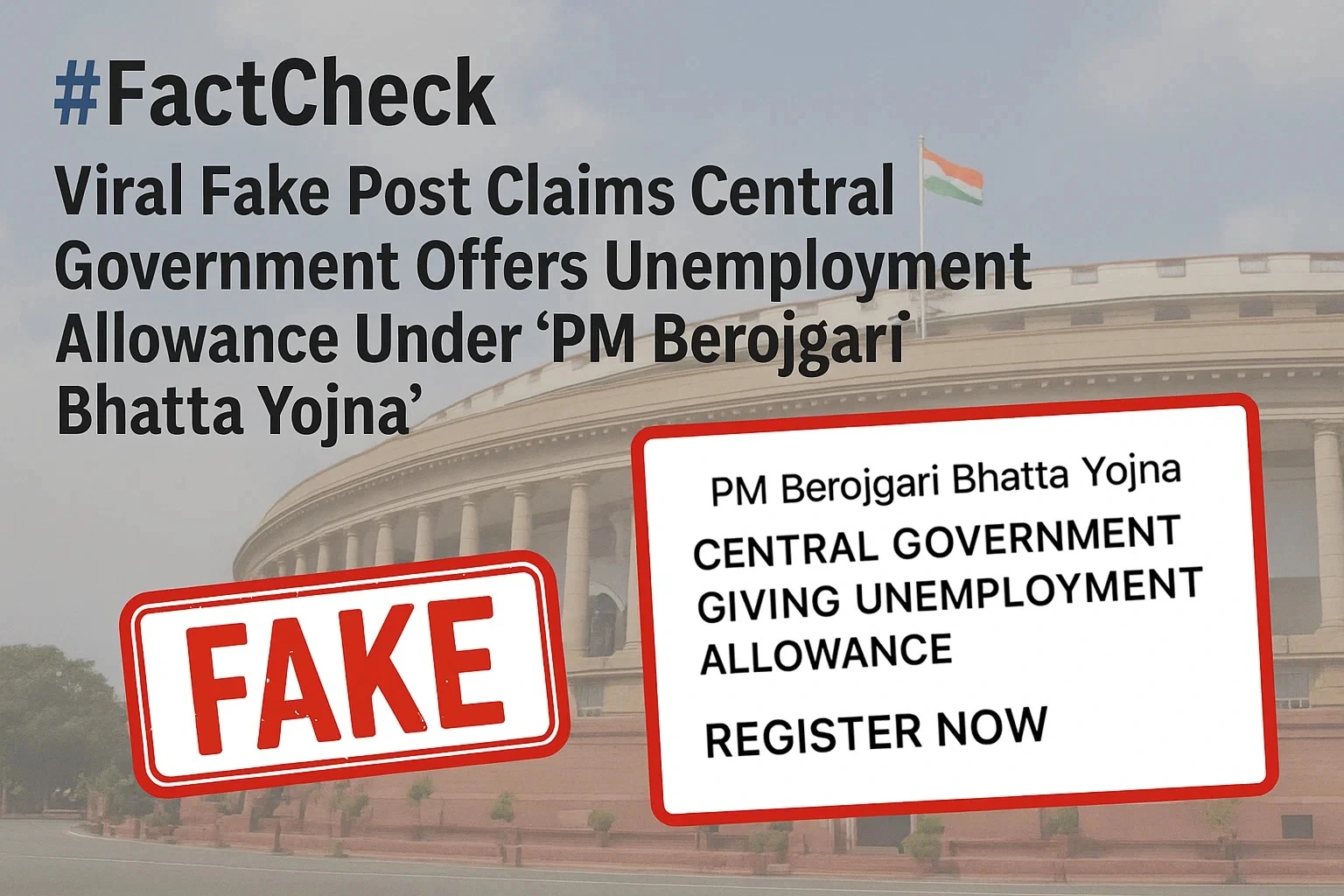
A viral thumbnail and numerous social posts state that the government of India is giving unemployed youth ₹4,500 a month under a program labeled "PM Berojgari Bhatta Yojana." This claim has been shared on multiple online platforms.. It has given many job-seeking individuals hope, however, when we independently researched the claim, there was no verified source of the scheme or government notification.

Claim:
The viral post states: "The Central Government is conducting a scheme called PM Berojgari Bhatta Yojana in which any unemployed youth would be given ₹ 4,500 each month. Eligible candidates can apply online and get benefits." Several videos and posts show suspicious and unverified website links for registration, trying to get the general public to share their personal information.
Fact check:
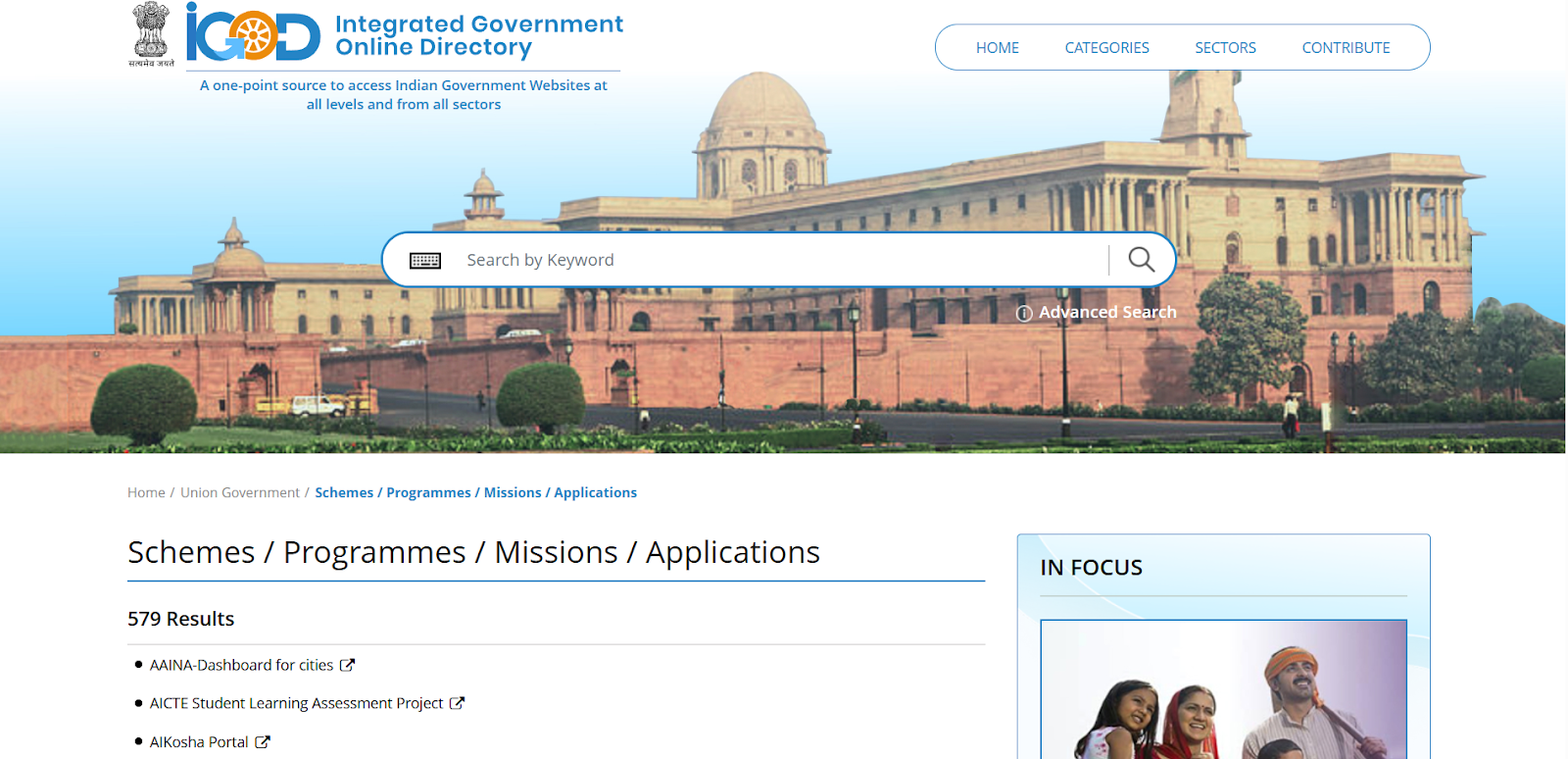
In the course of our verification, we conducted a research of all government portals that are official, in this case, the Ministry of Labour and Employment, PMO India, MyScheme, MyGov, and Integrated Government Online Directory, which lists all legitimate Schemes, Programmes, Missions, and Applications run by the Government of India does not posted any scheme related to the PM Berojgari Bhatta Yojana.
Numerous YouTube channels seem to be monetizing false narratives at the expense of sentiment, leading users to misleading websites. The purpose of these scams is typically to either harvest data or market pay-per-click ads that suspend disbelief in outrageous claims.
Our research findings were backed up later by the PIB Fact Check which shared a clarification on social media. stated that: “No such scheme called ‘PM Berojgari Bhatta Yojana’ is in existence. The claim that has gone viral is fake”.
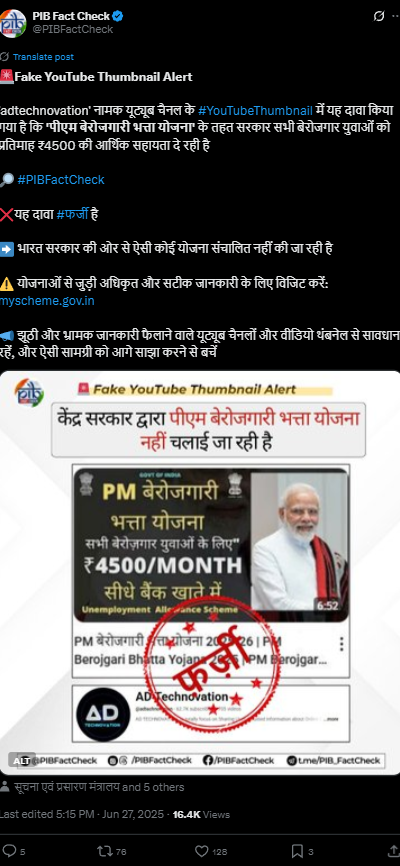
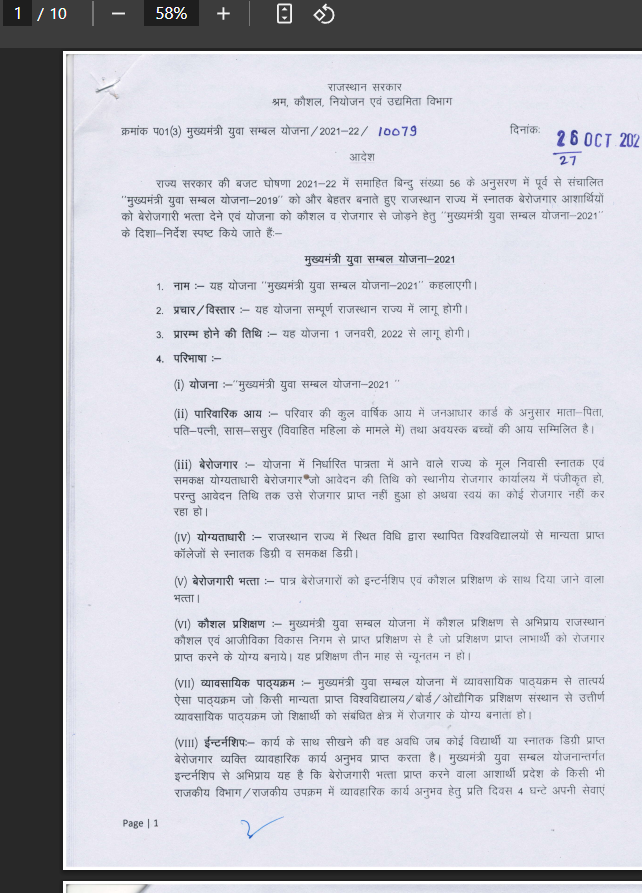
To provide some perspective, in 2021-22, the Rajasthan government launched a state-level program under the Mukhyamantri Udyog Sambal Yojana (MUSY) that provided ₹4,500/month to unemployed women and transgender persons, and ₹4000/month to unemployed males. This was not a Central Government program, and the current viral claim falsely contextualizes past, local initiatives as nationwide policy.
Conclusion:
The claim of a ₹4,500 monthly unemployment benefit under the PM Berojgari Bhatta Yojana is incorrect. The Central Government or any government department has not launched such a scheme. Our claim aligns with PIB Fact Check, which classifies this as a case of misinformation. We encourage everyone to be vigilant and avoid reacting to viral fake news. Verify claims through official sources before sharing or taking action. Let's work together to curb misinformation and protect citizens from false hopes and data fraud.
- Claim: A central policy offers jobless individuals ₹4,500 monthly financial relief
- Claimed On: Social Media
- Fact Check: False and Misleading


