#FactCheck - Debunking Manipulated Photos of Smiling Secret Service Agents During Trump Assassination Attempt
Executive Summary:
Viral pictures featuring US Secret Service agents smiling while protecting former President Donald Trump during a planned attempt to kill him in Pittsburgh have been clarified as photoshopped pictures. The pictures making the rounds on social media were produced by AI-manipulated tools. The original image shows no smiling agents found on several websites. The event happened with Thomas Mathew Crooks firing bullets at Trump at an event in Butler, PA on July 13, 2024. During the incident one was deceased and two were critically injured. The Secret Service stopped the shooter, and circulating photos in which smiles were faked have stirred up suspicion. The verification of the face-manipulated image was debunked by the CyberPeace Research Team.

Claims:
Viral photos allegedly show United States Secret Service agents smiling while rushing to protect former President Donald Trump during an attempted assassination in Pittsburgh, Pennsylvania.



Fact Check:
Upon receiving the posts, we searched for any credible source that supports the claim made, we found several articles and images of the incident but in those the images were different.

This image was published by CNN news media, in this image we can see the US Secret Service protecting Donald Trump but not smiling. We then checked for AI Manipulation in the image using the AI Image Detection tool, True Media.


We then checked with another AI Image detection tool named, contentatscale AI image detection, which also found it to be AI Manipulated.

Comparison of both photos:

Hence, upon lack of credible sources and detection of AI Manipulation concluded that the image is fake and misleading.
Conclusion:
The viral photos claiming to show Secret Service agents smiling when protecting former President Donald Trump during an assassination attempt have been proven to be digitally manipulated. The original image found on CNN Media shows no agents smiling. The spread of these altered photos resulted in misinformation. The CyberPeace Research Team's investigation and comparison of the original and manipulated images confirm that the viral claims are false.
- Claim: Viral photos allegedly show United States Secret Service agents smiling while rushing to protect former President Donald Trump during an attempted assassination in Pittsburgh, Pennsylvania.
- Claimed on: X, Thread
- Fact Check: Fake & Misleading
Related Blogs

Introduction
In the evolving landscape of cybercrime, attackers are not only becoming more sophisticated in their approach but also more adept in their infrastructure. The Indian Cybercrime Coordination Centre (I4C) has issued a warning about the use of ‘disposable domains’ by cybercriminals. These are short-lived websites designed tomimic legitimate platforms, deceive users, and then disappear quickly to avoid detection and legal repercussions.
Although they may appear harmless at first glance, disposable domains form the backbone of countless online scams, phishing campaigns, malware distributionschemes, and disinformation networks. Cybercriminals use them to host fake websites, distribute malicious files, send deceptive emails, and mislead unsuspecting users, all while evading detection and takedown efforts.
As India’s digital economy grows and more citizens, businesses, and public services move online, it is crucial to understand this hidden layer of cybercrime infrastructure.Greater awareness among individuals, enterprises, and policymakers is essential to strengthen defences against fraud, protect users from harm, and build trust in thedigital ecosystem
What Are Disposable Domains?
A disposable domain is a website domain that is registered to be used temporarily, usually for hours or days, typically to evade detection or accountability.
These domains are inexpensive, easy to obtain, and can be set up with minimal information. They are often bought in bulk through domain registrars that do not strictly verify ownership information, sometimes using stolen credit cards or cryptocurrencies to remain anonymous. They differ from legitimate temporary domains used for testing or development in one significant aspect, which is ‘purpose’. Cybercriminals use disposable domains to carry out malicious activities such as phishing, sextortion, malware distribution, fake e-commerce sites, spam email campaigns, and disinformation operations.
How Cybercriminals Utilise Disposable Domains
1. Phishing & Credential Stealing: Attackers tend to register lookalike domains that are similar to legitimate websites (e.g., go0gle-login[.]com or sbi-verification[.]online) and trick victims into entering their login credentials. These domains will be active only long enough to deceive, and then they will disappear.
2. Malware Distribution: Disposable domains are widely used for ransomware and spyware operations for hosting malicious files. Because the domains are temporary, threat intelligence systems tend to notice them too late.
3. Fake E-Commerce & Investment Scams: Cyber crooks clone legitimate e-commerce or investment sites, place ad campaigns, and trick victims into "purchasing" goods or investing in scams. The domain vanishes when the scam runs out.
4. Spam and Botnets: Disposable domains assist in botnet command-and-control activities. They make it more difficult for defenders to block static IPs or trace the attacker's infrastructure.
5. Disinformation and Influence Campaigns: State-sponsored actors and coordinated troll networks use disposable domains to host fabricated news articles, fake government documents, and manipulated videos. When these sites are detected and taken down, they are quickly replaced with new domains, allowing the disinformation cycle to continue uninterrupted.
Why Are They Hard to Stop?
Registering a domain is inexpensive and quick, often requiring no more than an email address and payment. The difficulty is the easy domain registrations and the absence of worldwide enforcement. Domain registrars differ in enforcing Know-Your-Customer (KYC) standards stringently. ICANN (Internet Corporation for Assigned Names and Numbers) has certain regulations in place but enforcement is inconsistent. ICANN does require registrars to maintain accurate Who is information (the “Registrant Data Accuracy Policy”) and to act on abuse complaints. However, ICANN is not an enforcement agency. It oversees contracts with registrars but cannot directly police every registration. Cybercriminals exploit services such as:
- Privacy protection shields that conceal actual WHOIS information.
- Bulletproof hosting that evades takedown notices.
- Fast-flux DNS methods to rapidly alter IP addresses
Additionally, utilisation of IDNs ( Internationalised Domain Names) and homoglyph attacks enables the attackers to register visually similar domains to legitimate ones (e.g., using Cyrillic characters to represent Latin ones).
Real-World Example: India and the Rise of Fake Investment Sites
India has witnessed a wave of monetary scams that are connected with disposable domains. Over hundreds of false websites impersonating government loan schemes, banks or investment websites, and crypto-exchanges were found on disposable domains such as gov-loans-apply[.]xyz, indiabonds-secure[.]top, or rbi-invest[.]store. Most of them placed paid advertisements on sites such as Facebook or Google and harvested user information and payments, only to vanish in 48–72 hours. Victims had no avenue of proper recourse, and the authorities were left with a digital ghost trail.
How Disposable Domains Undermine Cybersecurity
- Bypass Blacklists: Dynamic domains constantly shifting evade static blacklists.
- Delay Attribution: Time is wasted pursuing non-existent owners or takedowns.
- Mass Targeting: One actor can register thousands of domains and attack at scale.
- Undermine Trust: Frequent users become targets when genuine sites are duplicated and it looks realistic.
Recommendations Addressing Legal and Policy Gaps in India
1. There is a need to establish a formal coordination mechanism between domain registrars and national CERTs such as CERT-In to enable effective communication and timely response to domain-based threats.
2. There is a need to strengthen the investigative and enforcement capabilities of law enforcement agencies through dedicated resources, training, and technical support to effectively tackle domain-based scams.
3. There is a need to leverage the provisions of the Digital Personal Data Protection Act, 2023 to take action against phishing websites and malicious domains that collect personal data without consent.
4. There is a need to draft and implement specific regulations or guidelines to address the misuse of digital infrastructure, particularly disposable and fraudulent domains, and close existing regulatory gaps.
What Can Be Done: CyberPeace View
1. Stronger KYC for Domain Registrations: Registrars selling domains to Indian users or based in India should conduct verified KYC processes, with legal repercussions for carelessness.
2. Real-Time Domain Blacklists: CERT-In, along with ISPs and hosting companies, should operate and enforce a real-time blacklist of scam domains known.
3. Public Reporting Tools: Observers or victims should be capable of reporting suspicious domains through an easy interface (tied to cybercrime.gov.in).
4. Collaboration with Tech Platforms: Social media services and online ad platforms should filter out ads associated with disposable or spurious domains and report abuse data to CERT-In.
5. User Awareness: Netizens should be educated to check URLs thoroughly, not click on unsolicited links and they must verify the authenticity of websites.
Conclusion
Disposable domains have silently become the foundation of contemporary cybercrime. They are inexpensive, highly anonymous, and short-lived, which makes them a darling weapon for cybercriminals ranging from solo spammers to nation-state operators. In an increasingly connected Indian society where the penetration rate of internet users is high, this poses an expanding threat to economic security, public confidence, and national resilience. Combating this problem will need a combination of technical defences, policy changes, public-private alliances, and end-user sensitisation. As India develops a Cyber Secure Bharat, monitoring and addressing disposable domain abuse must be the utmost concern.
References
- https://www.bitcot.com/disposable-domains
- https://atdata.com/blog/evolution-of-email-fraud-rise-of-hyper-disposable-domains/
- https://www.cyfirma.com/research/scamonomics-the-dark-side-of-stock-crypto-investments-in-india/
- https://knowledgebase.constantcontact.com/lead-gen-crm/articles/KnowledgeBase/50330-Understanding-Blocked-Forbidden-and-Disposable-Domains?lang=en_US
- https://www.meity.gov.in/
- https://intel471.com/blog/bulletproof-hosting-fast-flux-dns-double-flux-vps

Introduction
Ransomware is one of the serious cyber threats as it causes consequences such as financial losses, data loss, and reputation damage. Recently in 2023, a new ransomware called Akira ransomware emerged or surfaced. It has targeted and affected various enterprises or industries, such as BSFI, Construction, Education, Healthcare, Manufacturing, real estate and consulting, primarily based in the United States. Akira ransomware has targeted industries by exploiting the double-extortion technique by exfiltrating and encrypting sensitive data and imposing the threat on victims to leak or sell the data on the dark web if the ransom is not paid. The Akira ransomware gang has extorted a ransom ranging from $200,000 to millions of dollars.
Uncovering the Akira Ransomware operations and their targets
Akira ransomware gang has gained unauthorised access to computer systems by using sophisticated encryption algorithms to encrypt the Data. When such an encryption process is completed, the affected device or network will not be able to access its files or use its data.
The affected files by Akira ransomware showed the extension named “.akira”, and the file’s icon shows blank white pages. The Akira ransomware has developed a data leak site so as to extort victims. And it has also used the ransom note named “akira_readme.txt”.
Akira ransomware steeled the corporate data of various organisations, which the Akira ransomware gang used as leverage while threatening the affected organisation with high ransom demands. Akira Ransomware gang threaten the victims to leak their sensitive data or corporate data in the public domain if the demanded ransom amount is not paid. Akira ransomware gang has leaked the data of four organisations and the size ranges from 5.9GB to 259 GB of data leakage.
Akira Ransomware gang communicating with Victims
The Akira ransomware has provided a unique negotiation password to each victim to initiate communication. Where the ransomware gang deployed a chat system for the purpose of negotiation and demanding ransom from the affected organisations. They have deployed a ransom note as akira_readme.txt so as to provide information as to how they have affected the victim’s files or data along with links to the Akira data leak site and negotiation site.
How Akira Ransomware is different from Pegasus Spyware
Pegasus, developed in the year 2011, belongs to one of the most powerful family of spyware. Once it has infected, it can spear your phone and your text messages or emails. It has the ability to turn your phone into a surveillance device, from copying your messages to harvesting your photos and recording calls. In fact, it has the ability to record you through your phone camera or record your conversation by using your microphone, it also has the ability to track your pinpoint location. In contrast, newly Akira ransomware affects encrypting your files and preventing access to your Data and then asking for ransom n the pretext of leaking your data or for decryption.
How to recover from malware attacks
If affected by such type of malware attack, you can use anti-malware tools such as SpyHunter 5 or Malwarebytes to scan your system. These are the security software which can scan your system and remove suspicious malware files and entries. If you are unable to perform the scan or antivirus in normal mode due to malware in your system, you can use it in Safe Mode. And try to find a relevant decryptor which can help you to recover your files. Do not fall into a ransomware gang’s trap because there is no guarantee that they will help you to recover or will not leak your data after paying the ransom amount.
Best practices to be safe from such ransomware attacks
Conclusion
The Akira ransomware operation poses serious threats to various organisations worldwide. There is a high need to employ robust cybersecurity measures to safeguard networks and sensitive data. Organisations must ensure to keep their software system updated and backed up to a secure network on a regular basis. Paying the ransom is illegal mean instead you should report the incident to law enforcement agencies and can consult with cybersecurity professionals for the recovery method.

Executive Summary
Amid the ongoing tensions in West Asia between the United States–Israel alliance and Iran since February 28, 2026, a video is rapidly going viral on social media. The clip shows buildings engulfed in flames and thick plumes of smoke following an attack. Several users are sharing it with the claim that it depicts Iran’s recent strike on Tel Aviv, Israel. However, an research by the CyberPeace found the claim to be misleading. The viral video is actually from August 2025, when Israel carried out airstrikes in Sanaa, the capital of Yemen. It has no connection to the current conflict.
Claim:
An Instagram user ‘iran_.news24’ posted the video on March 27, 2026, with the caption: “Iran has turned Israel’s largest city Tel Aviv into hell—fears that 200,000 people have died in the war so far.”
Fact Check
To verify the viral claim, keyframes of the video were extracted and searched using Google Lens. The same video was found posted on August 24, 2025, by a Facebook user ‘Mhmdmhywbalshrby5’. The accompanying text, when translated, stated that it showed Israeli bombardment of Sanaa, Yemen.
Similarly, another Instagram user ‘ae5ce’ had also shared the same video on August 24, 2025, identifying it as footage from Sanaa.
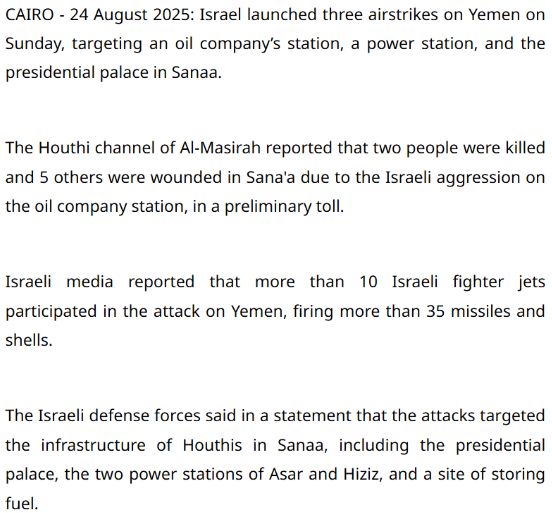
Media reports further support this finding. According to a report published by Egypt Today on August 24, 2025, Israel carried out multiple airstrikes in Sanaa targeting key locations, including an oil station, a power facility, and the presidential palace. Casualties were also reported. The strikes were said to be in response to attacks by Houthi forces.
Additionally, the New York Post shared another video of the same incident from a different angle on its X (formerly Twitter) handle on August 25, 2025.
Conclusion
The video being circulated with the claim of Iran attacking Tel Aviv is actually old footage from Israeli airstrikes in Yemen in August 2025. It is unrelated to the ongoing conflict.


