#FactCheck- Viral Video Misleadingly Linked to Alleged Israeli Strike on Iran
Executive Summary:
A video is rapidly circulating on social media following claims that Iran’s national security chief Ali Larijani was killed in an Israeli airstrike. The viral clip is being shared with the assertion that it shows the moment Israel launched a powerful attack on Iran to eliminate Larijani, allegedly shaking the ground due to the intensity of the strike However, research by CyberPeace has found the claim to be misleading. The viral video is AI-generated and has no connection to real-world events.
Claim:
Social media users have shared the video with alarming captions. One such post by Deepak Sharma reads:
“WAR UPDATE… Iran is in its final phase… Israel is striking selectively… This attack will leave you shocked… Iran’s national security chief Ali Larijani has been killed in this attack… The intensity of the strike shook the Iranian الأرض.
Post links:

Similar videos were also shared by other users:
- urabh_raj3026/status/2038834832869032026
- https://x.com/ibmindia20/status/2038938020154597447
- https://x.com/Saurabh_raj3026/status/2038834832869032026
Fact Check
To verify the claim, we extracted keyframes from the viral video and conducted a reverse image search. During this process, we found the same video on Instagram, uploaded on March 9, 2026, by the account “_iranwar_2026” without any descriptive caption.

According to a BBC report, Ali Larijani died on March 17 in an Israeli strike. This establishes that the viral video predates the reported incident, making the claim factually inconsistent. Further examination of the Instagram account revealed that it frequently shares pro-Iran content, including gaming visuals and AI-generated clips, raising doubts about the authenticity of the video.

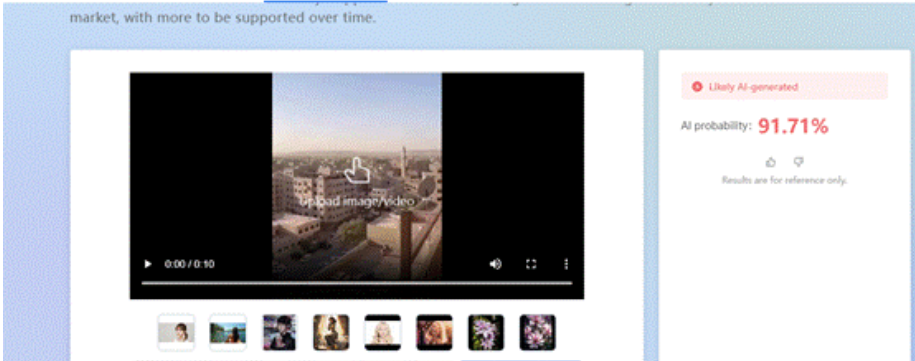
To strengthen the verification, we analyzed the viral clip using the AI detection tool “Zhuque AI Detection Assistant.” The results indicated a 91.71% probability that the video is AI-generated, confirming that it is not real footage.
Conclusion
The viral claim linking the video to an Israeli airstrike that allegedly killed Ali Larijani is misleading and factually incorrect. Multiple layers of verification show that the video existed online before the reported incident, ruling out any direct connection. Additionally, AI detection analysis strongly suggests that the video is artificially generated. The source account’s pattern of sharing AI and gaming-related content further weakens the credibility of the claim. There is no verified evidence to support that the viral clip depicts a real attack or any event related to Larijani’s death. Instead, the video appears to be a digitally created visual circulated without context to amplify misinformation.
Related Blogs

Introduction
In September 2025, social media feeds were flooded with strikingly vintage saree-type portraits. These images were not taken by professional photographers, but AI-generated images. More than a million people turned to the "Nano Banana" AI tool of Google Gemini, uploading their ordinary selfies and watching them transform into Bollywood-style, cinematic, 1990s posters. The popularity of this trend is evident, as are the concerns of law enforcement agencies and cybersecurity experts regarding risks of infringement of privacy, unauthorised data sharing, and threats related to deepfake misuse.
What is the Trend?
This trend in AI sarees is created using Google Geminis' Nano Banana image-editing tool, editing and morphing uploaded selfies into glitzy vintage portraits in traditional Indian attire. A user would upload a clear photograph of a solo subject and enter prompts to generate images of cinematic backgrounds, flowing chiffon sarees, golden-hour ambience, and grainy film texture, reminiscent of classic Bollywood imagery. Since its launch, the tool has processed over 500 million images, with the saree trend marking one of its most popular uses. Photographs are uploaded to an AI system, which uses machine learning to alter the pictures according to the description specified. The transformed AI portraits are then shared by users on their Instagram, WhatsApp, and other social media platforms, thereby contributing to the viral nature of the trend.
Law Enforcement Agency Warnings
- A few Indian police agencies have issued strong advisories against participation in such trends. IPS Officer VC Sajjanar warned the public: "The uploading of just one personal photograph can make greedy operators go from clicking their fingers to joining hands with criminals and emptying one's bank account." His advisory had further warned that sharing personal information through trending apps can lead to many scams and fraud.
- Jalandhar Rural Police issued a comprehensive warning stating that such applications put the user at risk of identity theft and online fraud when personal pictures are uploaded. A senior police officer stated: "Once sensitive facial data is uploaded, it can be stored, analysed, and even potentially misused to open the way for cyber fraud, impersonation, and digital identity crimes.
The Cyber Crime Police also put out warnings on social media platforms regarding how photo applications appear entertaining but can pose serious risks to user privacy. They specifically warned that selfies uploaded can lead to data misuse, deepfake creation, and the generation of fake profiles, which are punishable under Sections 66C and 66D of the IT Act 2000.
Consequences of Such Trends
The massification of AI photo trends has several severe effects on private users and society as a whole. Identity fraud and theft are the main issues, as uploaded biometric information can be used by hackers to generate imitated identities, evading security measures or committing financial fraud. The facial recognition information shared by means of these trends remains a digital asset that could be abused years after the trend has passed. ‘Deepfake’ production is another tremendous threat because personal images shared on AI platforms can be utilised to create non-consensual artificial media. Studies have found that more than 95,000 deepfake videos circulated online in 2023 alone, a 550% increase from 2019. The images uploaded can be leveraged to produce embarrassing or harmful content that can cause damage to personal reputation, relationships, and career prospects.
Financial exploitation is also when fake applications in the guise of genuine AI tools strip users of their personal data and financial details. Such malicious platforms tend to look like well-known services so as to trick users into divulging sensitive information. Long-term privacy infringement also comes about due to the permanent retention and possible commercial exploitation of personal biometric information by AI firms, even when users close down their accounts.
Privacy Risks
A few months ago, the Ghibli trend went viral, and now this new trend has taken over. Such trends may subject users to several layers of privacy threats that go far beyond the instant gratification of taking pleasing images. Harvesting of biometric data is the most critical issue since facial recognition information posted on these sites becomes inextricably linked with user identities. Under Google's privacy policy for Gemini tools, uploaded images might be stored temporarily for processing and may be kept for longer periods if used for feedback purposes or feature development.
Illegal data sharing happens when AI platforms provide user-uploaded content to third parties without user consent. A Mozilla Foundation study in 2023 discovered that 80% of popular AI apps had either non-transparent data policies or obscured the ability of users to opt out of data gathering. This opens up opportunities for personal photographs to be shared with anonymous entities for commercial use. Exploitation of training data includes the use of personal photos uploaded to enhance AI models without notifying or compensating users. Although Google provides users with options to turn off data sharing within privacy settings, most users are ignorant of these capabilities. Integration of cross-platform data increases privacy threats when AI applications use data from interlinked social media profiles, providing detailed user profiles that can be taken advantage of for purposeful manipulation or fraud. Inadequacy of informed consent continues to be a major problem, with users engaging in trends unaware of the entire context of sharing information. Studies show that 68% of individuals show concern regarding the misuse of AI app data, but 42% use these apps without going through the terms and conditions.
CyberPeace Expert Recommendations
While the Google Gemini image trend feature operates under its own terms and conditions, it is important to remember that many other tools and applications allow users to generate similar content. Not every platform can be trusted without scrutiny, so users who engage in such trends should do so only on trustworthy platforms and make reliable, informed choices. Above all, following cybersecurity best practices and digital security principles remains essential.
Here are some best practices:-
1.Immediate Protection Measures for User
In a nutshell, protection of personal information may begin by not uploading high-resolution personal photos into AI-based applications, especially those trained for facial recognition. Instead, a person can play with stock images or non-identifiable pictures to the degree that it satisfies the program's creative features without compromising biometric security. Strong privacy settings should exist on every social media platform and AI app by which a person can either limit access to their data, content, or anything else.
2.Organisational Safeguards
AI governance frameworks within organisations should enumerate policies regarding the usage of AI tools by employees, particularly those concerning the upload of personal data. Companies should appropriately carry out due diligence before the adoption of an AI product made commercially available for their own use in order to ensure that such a product has its privacy and security levels as suitable as intended by the company. Training should instruct employees regarding deepfake technology.
3.Technical Protection Strategies
Deepfake detection software should be used. These tools, which include Microsoft Video Authenticator, Intel FakeCatcher, and Sensity AI, allow real-time detection with an accuracy higher than 95%. Use blockchain-based concepts to verify content to create tamper-proof records of original digital assets so that the method of proposing deepfake content as original remains very difficult.
4.Policy and Awareness Initiatives
For high-risk transactions, especially in banks and identity verification systems, authentication should include voice and face liveness checks to ensure the person is real and not using fake or manipulated media. Implement digital literacy programs to empower users with knowledge about AI threats, deepfake detection techniques, and safe digital practices. Companies should also liaise with law enforcement, reporting purported AI crimes, thus offering assistance in combating malicious applications of synthetic media technology.
5.Addressing Data Transparency and Cross-Border AI Security
Regulatory systems need to be called for requiring the transparency of data policies in AI applications, along with providing the rights and choices to users regarding either Biometric data or any other data. Promotion must be given to the indigenous development of AI pertaining to India-centric privacy concerns, assuring the creation of AI models in a secure, transparent, and accountable manner. In respect of cross-border AI security concerns, there must be international cooperation for setting common standards of ethical design, production, and use of AI. With the virus-like contagiousness of AI phenomena such as saree editing trends, they portray the potential and hazards of the present-day generation of artificial intelligence. While such tools offer newer opportunities, they also pose grave privacy and security concerns, which should have been considered quite some time ago by users, organisations, and policy-makers. Through the setting up of all-around protection mechanisms and keeping an active eye on digital privacy, both individuals and institutions will reap the benefits of this AI innovation, and they shall not fall on the darker side of malicious exploitation.
References
- https://www.hindustantimes.com/trending/amid-google-gemini-nano-banana-ai-trend-ips-officer-warns-people-about-online-scams-101757980904282.html%202
- https://www.moneycontrol.com/news/india/viral-banana-ai-saree-selfies-may-risk-fraud-warn-jalandhar-rural-police-13549443.html
- https://www.parliament.nsw.gov.au/researchpapers/Documents/Sexually%20explicit%20deepfakes.pdf
- https://www.mckinsey.com/capabilities/quantumblack/our-insights/the-state-of-ai-in-2023-generative-ais-breakout-year
- https://www.mckinsey.com/capabilities/quantumblack/our-insights/the-state-of-ai-in-2023-generative-ais-breakout-year
- https://socradar.io/top-10-ai-deepfake-detection-tools-2025/

Introduction
Since the inception of the Internet and social media platforms like Facebook, X (Twitter), Instagram, etc., the government and various other stakeholders in both foreign jurisdictions and India have looked towards the intermediaries to assume responsibility for the content floated on these platforms, and various legal provisions showcase that responsibility. For the first time in many years, these intermediaries come together to moderate the content by setting a standard for the creators and propagators of this content. The influencer marketing industry in India is at a crucial juncture, with its market value projected to exceed Rs. 3,375 crore by 2026. But every industry is coupled with its complications; like in this scenario, there is a section of content creators who fail to maintain the standard of integrity and propagate content that raises concerns of authenticity and transparency, often violating intellectual property rights (IPR) and privacy.
As influencer marketing continues to shape digital consumption, the need for ethical and transparent content grows stronger. To address this, the India Influencer Governing Council (IIGC) has released its Code of Standards, aiming to bring accountability and structure to the fast-evolving online space.
Bringing Accountability to the Digital Fame Game
The India Influencer Governing Council (IIGC), established on 15th February, 2025, is founded with the objective to empower creators, advocate for fair policies, and promote responsible content creation. The IIGC releases the Code of Standard, not a moment too soon; it arrives just in time, a necessary safeguard before social media devolves into a chaotic marketplace where anything and everything is up for grabs. Without effective regulation, digital platforms become the marketplace for misinformation and exploitation.
The IIGC leads the movement with clarity, stating that the Code is a significant piece that spans across 20 crucial sections governing key areas such as paid partnership disclosures, AI-generated personas, content safety, and financial compliance.
Highlights from the Code of Standard
- The Code exhibits a technical understanding of the industry of content creation and influencer marketing. The preliminary sections advocate for accuracy, transparency, and maintaining credibility with the audience that engages with the content. Secondly, the most fundamental development is with regard to the “Paid Partnership Disclosure” included in Section 2 of the Code that mandates disclosure of any material connection, such as financial agreements or collaboration with the brand.
- Another development, which potently comes at a befitting hour, is the disclosure of “AI Influencers”, which establishes that the nature of the influencer has to be disclosed, and such influencers, whether fully virtual or partially AI-enhanced, must maintain the same standards as any human influencer.
- The code ranges across various other aspects of influencer marketing, such as expressing unpaid “Admiration” for the brand and public criticism of the brand, being free from personal bias, honouring financial agreements, non-discrimination, and various other standards that set the stage for a safe and fair digital sphere.
- The Code also necessitates that the platform users and the influencers handle sexual and sensitive content with sincere deliberation, and usage of such content shall be for educational and health-related contexts and must not be used against community standards. The Code includes various other standards that work towards making digital platforms safer for younger generations and impressionable minds.
A Code Without Claws? Challenges in Enforcement
The biggest obstacle to the effective implementation of the code is distinguishing between an honest promotion and a paid brand collaboration without any explicit mention of such an agreement. This makes influencer marketing susceptible to manipulation, and the manipulation cannot be tackled with a straitjacket formula, as it might be found in the form of exaggerated claims or omission of critical information.
Another hurdle is the voluntary compliance of the influencers with the advertising standards. Influencer marketing is an exercise in a borderless digital cyberspace, where the influencers often disregard the dignified standards to maximise their earnings and commercial motives.
The debate between self-regulation and government oversight is constantly churning, where experience tells us that overreliance on self-regulation has proven to be inadequate, and succinct regulatory oversight is imperative in light of social media platforms operating as a transnational commercial marketplace.
CyberPeace Recommendations
- Introduction of a licensing framework for influencers that fall into the “highly followed” category with high engagement, who are more likely to shape the audience’s views.
- Usage of technology to align ethical standards with influencer marketing practices, ensuring that misleading advertisements do not find a platform to deceive innocent individuals.
- Educating the audience or consumers on the internet about the ramifications of negligence and their rights in the digital marketplace. Ensuring a well-established grievance redressal mechanism via digital regulatory bodies.
- Continuous and consistent collaboration and cooperation between influencers, brands, regulators, and consumers to establish an understanding and foster transparency and a unified objective to curb deceptive advertising practices.
References
- https://iigc.org/code-of-standards/influencers/code-of-standards-v1-april.pdf
- https://legalonus.com/the-impact-of-influencer-marketing-on-consumer-rights-and-false-advertising/
- https://exhibit.social/news/india-influencer-governing-council-iigc-launched-to-shape-the-future-of-influencer-marketing/

Introduction
Have you ever wondered how the internet works? Yes, there are screens and wires, but what’s going on beneath the surface? Every time you open a website, send an email, chat on messaging apps, or stream movies, you’re relying on something you probably don’t think about: the TCP/IP protocol suite. Without it, the internet as we know it wouldn’t exist. Let’s take a look at why this unassuming set of rules allows us to connect to anyone anywhere in the world.
The Problem: Networks That Couldn't Talk to Each Other
The internet is widely called a network of networks. A network is a group of devices that are connected and can share data with each other.
Researchers and governments began building early computer networks in the 1960s and 70s. But as the Cold War intensified, the U.S. military felt the need to establish a robust data-sharing infrastructure through interconnected networks that could withstand attacks. At the time, each network had different standards and protocols, which meant getting networks to communicate wasn’t easy or efficient. One network would have to be subsumed into another. This would lead to major problems in the reliability of data relay, flexibility of including more nodes, scalability of the interconnected network, and innovation.
The Breakthrough: Open Architecture Networking
This changed in the 1970s, when Bob Kahn proposed the concept of open architecture networking. It was a simple but revolutionary idea. He envisioned a system where all networks could talk to each other as equals. In this conceptualisation, all networks, even though unique in design and interface, could connect as peers to facilitate end-to-end communication. End-to-end communication helps deliver data between the source and destination without relying on intermediate nodes to control or modify it. This helps to make data relay more reliable and less prone to errors.
Along with Vint Cerf, he developed a network protocol, the TCP/IP suite, that would go on to enable different networks across satellite, wired, and non-wired domains to communicate with one another.
What Is TCP/IP?
TCP/IP stands for Transmission Control Protocol / Internet Protocol. It’s a set of communication rules that allow computers and devices to exchange information across different networks.
It’s powerful because:
- Layered and open architecture: Each function (like data delivery or routing) is handled by a specific layer. This modular design makes it easy to build new technologies like the World Wide Web or streaming services on top of it.
- Decentralisation: There's no single point of control. Any device can connect to another across the internet, making it scalable and resilient.
- Standardisation: TCP/IP works across all kinds of hardware and operating systems, making it truly universal.
The Core Components
- TCP (Transmission Control Protocol): Ensures that data is delivered accurately and in order. If any piece is lost or duplicated, TCP handles it.
- IP (Internet Protocol): Handles addressing and routing. It decides where each packet of data should go and how it gets there.
- UDP (User Datagram Protocol): A lightweight version of TCP, used when speed is more important than accuracy, such as for video calls or online gaming.
Why It Matters
The TCP/IP protocol suite introduced a set of standardised guidelines that enable networks to communicate, thereby laying the foundation of the Internet. It has made the Internet global, open, reliable, interoperable, scalable, and resilient, — features because of which the Internet has come to become the backbone of modern communication systems. So the next time you open a browser or send a message, remember: it’s TCP/IP quietly making it all possible.
References
- https://www.techtarget.com/searchnetworking/definition/ARPANET
- https://www.internetsociety.org/internet/history-internet/brief-history-internet/
- https://www.geeksforgeeks.org/tcp-ip-model/
- https://www.oreilly.com/library/view/tcpip-network-administration/0596002971/ch01.html


