#FactCheck -Old Karnataka Video Falsely Linked to Holi Celebrations on Eid in Delhi
Executive Summary
A video is being shared on social media showing a group of people dancing on a road while carrying saffron flags. A mosque can also be seen nearby in the video Sharing this clip, some users are claiming that it is from Uttam Nagar in Delhi, where members of the Hindu community celebrated Holi on the occasion of Eid on March 21. Research by the CyberPeace found the viral claim to be misleading. Our probe revealed that the video is not related to Holi celebrations on Eid in Uttam Nagar, Delhi. In fact, the video has been available on the internet since 2024 and is said to be from Raichur district in Karnataka. Several users have shared it claiming that it was recorded during Ganesh Chaturthi celebrations.
Claim:
A social media user shared the viral video on March 21, 2026, with a misleading claim. The link and archive link of the post are given below.

Fact Check:
To verify the viral claim, we first conducted a keyword search on Google. However, we did not find any credible media report supporting the claim. In the next step, we extracted keyframes from the video and performed a reverse search using Google Lens. During this process, we found the same video on an Instagram account, which was posted on September 23, 2024.
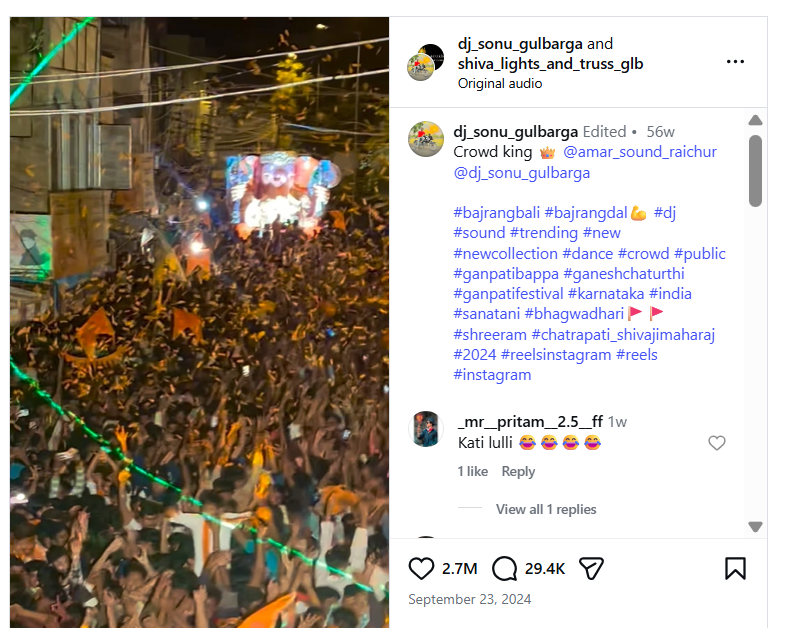
The user had captioned the video as “Ganesh Chaturthi 2024,” suggesting that the clip is related to the festival. Further, upon closely analyzing the video, we noticed that the mosque visible in the background had “Usmania Masjid” written on it. We then searched for this location on Google Maps and found that the mosque is located on Teen Khandil Road in Raichur, Karnataka, which matches the visuals seen in the viral clip.

Conclusion:
Our research found that the video is not from Uttam Nagar, Delhi, nor is it related to Holi celebrations on Eid. The clip has been available online since 2024 and is from Raichur, Karnataka. It has been shared with a misleading claim and is actually linked to Ganesh Chaturthi celebrations.
Related Blogs

Introduction
The digital landscape of the nation has reached a critical point in its evolution. The rapid adoption of technologies such as cloud computing, mobile payment systems, artificial intelligence, and smart infrastructure has led to a high degree of integration between digital systems and governance, commercial activity, and everyday life. As dependence on these systems continues to grow, a wide range of cyber threats has emerged that are complex, multi-layered, and closely interconnected. By 2026, cyber security threats directed at India are expected to include an increasing number of targeted, well-organised, and strategic cyber attacks. These attacks are likely to focus on exploiting the trust placed in technology, institutions, automation, and the fast pace of technological change.
1. Social Engineering 2.0: Hyper-Personalised AI Phishing & Mobile Banking Malware
Cybercriminals have moved from generalised methods to hyper-targeted attacks through AI-based psychological manipulation. In addition to social media profiles, data breaches, and digital/tracking footprints, the latest types of cybercrimes expected in 2026 will involve AI-based analysis of this information to create and increase the use of hyper-targeted phishing emails.
Phishing emails are capable of impersonating banks, employers, and even family members, with all the same regionally or culturally relevant tone, language, and context as would be done if these persons were sending the emails in person.
With malicious applications disguised as legitimate service apps, cybercriminals have the ability to intercept and capture One-Time Passwords (OTPs), hijack user sessions, and steal money from user accounts in a matter of minutes.
These types of attempts or attacks are successful not only because of their technical sophistication, but because they take advantage of human trust at scale, giving them an almost limitless reach into the financial systems of people around the world through their computers and mobile devices.
2. Cloud and Supply Chain Vulnerabilities
As Indian organisations increasingly migrate to cloud infrastructure, cloud misconfigurations are emerging as a major cybersecurity risk. Weak identity controls, exposed storage, and improper access management can allow attackers to bypass traditional network defences. Alongside this, supply chain attacks are expected to intensify in 2026.
In supply chain attacks, cybercriminals compromise a trusted software vendor or service provider to infiltrate multiple downstream organisations. Even entities with strong internal security can be affected through third-party dependencies. For India’s startup ecosystem, government digital platforms, and IT service providers, this presents a systemic risk. Strengthening vendor risk management and visibility across digital supply chains will be essential.
3. Threats to IoT and Critical Infrastructure
By implementing smart cities, digital utilities, and connected public services, IoT has opened itself up to increased levels of operational technology (OT) through India’s initiative. However, there is currently a lack of adequate security in the form of strong authentication, encryption, and update methods available on many IoT devices. By the year 2026, attackers are going to be able to exploit these vulnerabilities much more than they already are.
Cyberattacks on critical infrastructure such as energy, transportation, healthcare, and telecom systems have far-reaching consequences that extend well beyond data loss; they directly affect the provision of essential services, can damage public safety, and raise concerns over national security. Effectively securing critical infrastructure needs to involve dedicated security solutions to deal with the specific needs of critical infrastructure, in contrast to conventional IT security.
4. Hidden File Vectors and Stealth Payload Delivery
SVG File Abuse in Stealth Attacks
Cybercriminals are continually searching for ways to bypass security filters, and hidden file vectors are emerging as a preferred tactic. One such method involves the abuse of SVG (Scalable Vector Graphics) files. Although commonly perceived as harmless image files, SVGs can contain embedded scripts capable of executing malicious actions.
By 2026, SVG-based attacks are expected to be used in phishing emails, cloud file sharing, and messaging platforms. Because these files often bypass traditional antivirus and email security systems, they provide an effective stealth delivery mechanism. Indian organisations will need to rethink assumptions about “safe” file formats and strengthen deep content inspection capabilities.
5. Quantum-Era Cyber Risks and “Harvest Now, Decrypt Later” Attacks
Although practical quantum computers are still emerging, quantum-era cyber risks are already a present-day concern. Adversaries are believed to be intercepting and storing encrypted data now with the intention of decrypting it in the future once quantum capabilities mature—a strategy known as “harvest now, decrypt later.” This poses serious long-term confidentiality risks.
Recognising this threat, the United States took early action during the Biden administration through National Security Memorandum 10, which directed federal agencies to prepare for the transition to quantum-resistant cryptography. For India, similar foresight is essential, as sensitive government communications, financial data, health records, and intellectual property could otherwise be exposed retrospectively. Preparing for quantum-safe cryptography will therefore become a strategic priority in the coming years.
6. AI Trust Manipulation and Model Exploitation
Poisoning the Well – Direct Attacks on AI Models
As artificial intelligence systems are increasingly used for decision-making—ranging from fraud detection and credit scoring to surveillance and cybersecurity—attackers are shifting focus from systems to models themselves. “Poisoning the well” refers to attacks that manipulate training data, feedback mechanisms, or input environments to distort AI outputs.
In the context of India's rapidly growing digital ecosystem, compromised AI models can result in biased decisions, false security alerts or denying legitimate services. The big problem with these types of attacks is they may occur without triggering conventional security measures. Transparency, integrity and continuous monitoring of AI systems will be key to creating and maintaining stakeholder confidence in the decision-making process of the automated systems.
Recommendations
Despite the increasing sophistication of malicious cyber actors, India is entering this phase with a growing level of preparedness and institutional capacity. The country has strengthened its cyber security posture through dedicated mechanisms and relevant agencies such as the Indian Cyber Crime Coordination Centre, which play a central role in coordination, threat response, and capacity building. At the same time, sustained collaboration among government bodies, non-governmental organisations, technology companies, and academic institutions has expanded cyber security awareness, skill development, and research. These collective efforts have improved detection capabilities, response readiness, and public resilience, placing India in a stronger position to manage emerging cyber threats and adapt to the evolving digital environment.
Conclusion
By 2026, complexity, intelligence, and strategic intent will increasingly define cyber threats to the digital ecosystem. Cyber criminals are expected to use advanced methods of attack, including artificial intelligence assisted social engineering and the exploitation of cloud supply chain risks. As these threats evolve, adversaries may also experiment with quantum computing techniques and the manipulation of AI models to create new ways of influencing and disrupting digital systems. In response, the focus of cybersecurity is shifting from merely preventing breaches to actively protecting and restoring digital trust. While technical controls remain essential, they must be complemented by strong cybersecurity governance, adherence to regulatory standards, and sustained user education. As India continues its digital transformation, this period presents a valuable opportunity to invest proactively in cybersecurity resilience, enabling the country to safeguard citizens, institutions, and national interests with confidence in an increasingly complex and dynamic digital future.
References
- https://www.seqrite.com/india-cyber-threat-report-2026/
- https://www.uscsinstitute.org/cybersecurity-insights/blog/ai-powered-phishing-detection-and-prevention-strategies-for-2026
- https://www.expresscomputer.in/guest-blogs/cloud-security-risks-that-should-guide-leadership-in-2026/130849/
- https://www.hakunamatatatech.com/our-resources/blog/top-iot-challenges
- https://csrc.nist.gov/csrc/media/Presentations/2024/u-s-government-s-transition-to-pqc/images-media/presman-govt-transition-pqc2024.pdf
- https://www.cyber.nj.gov/Home/Components/News/News/1721/214

Introduction
The ramifications of cybercrime can be far-reaching. Depending on the size of the attack, even entire countries can be affected if their critical infrastructure is connected to the internet. The vast majority of security breaches start within the perimeter and most internet attacks are socially engineered. Unwittingly trusting any email or web request from an unknown sender creates a potential danger for those organisations that depend on the Internet for their business functions. In this ever-evolving digital downtown yet another group has emerged from its darkest corners of targeting the UK’s very bastion of British and global heritage; a treasure trove of around 14 million volumes, ancient manuscripts, in the precious British Library. A group self-identified as Rhysida. Their bold maneuver, executed with the stealth of seasoned cyber brigands, has cast a shadow as long and dark as those found in the Gothic novels that rest on the library's shelves. The late October cyber-attack has thrust the British Library into an unnerving state of chaos, a situation more commonly aligned with works of dystopian fiction than the everyday reality of a revered institution.
The Modus Operandi
The gang uses all-new Rhysida ransomware to jeopardize Virtual Private Networks, which is typically used by library staff to gain access to their employee’s systems remotely. The Ransomware presents itself as a regular decoy file in a familiar fashion as regular phishing attacks in an email, tricking its victim and downloading itself into the host system. Once the malware enters the system it stays dormant and lurks around the system for a period of time. The new malware has significantly reduced the dwell time from 4 days to less than 24 hours which enables it to evade periodic system checks to avoid detection.
Implications of Cyber Attack
Implications of the cyber-attack have been sobering and multifaceted. The library's systems, which serve as the lifeline for countless scholars, students, and the reading public, were left in disarray, unsettlingly reminiscent of a grand mansion invaded by incorporeal thieves. The violation has reverberated through the digital corridors of this once-impenetrable fortress, and the virtual aftershocks are ongoing. Patrons, who traverse a diverse spectrum of society, but share a common reverence for knowledge, received unsettling news: the possibility that their private data has been compromised—a sanctity breached, revealing yet again how even the most hallowed of spaces are not impervious to modern threats.
It is with no small sense of irony that we consider the nature of the stolen goods—names, email addresses, and the like. It is not the physical tomes of inestimable value that have been ransacked, but rather the digital footprints of those who sought the wisdom within the library's walls. This virtual Pandora's Box, now unleashed onto the dark web, has been tagged with a monetary value. Rhysida has set the ominous asking price of a staggering $740,000 worth of cryptocurrency for the compromised data, flaunting their theft with a hubris that chills the spine.
Yet, in this convoluted narrative unfolds a subplot that offers some measure of consolation. Payment information purports the library has not been included in this digital heist, offering a glint of reassurance amidst the prevailing uncertainty. This digital storm has had seismic repercussions: the library's website and interconnected systems have been besieged and access to the vast resources significantly hampered. The distressing notice of a 'major technology outage' transformed the digital facade from a portal for endless learning to a bulletin of sorrow, projecting the sombre message across virtual space.
The Impact
The impact of this violation will resonate far beyond the mere disruption of services; it signals the dawn of an era where venerable institutions of culture and learning must navigate the depths of cybersecurity. As the library grapples with the breach, a new front has opened in the age-old battle for the preservation of knowledge. The continuity of such an institution in a digitised world will be tested, and the outcome will define the future of digital heritage management. As the institution rallies, led by Roly Keating, its Chief Executive, one observes not a defeatist retreat, but a stoic, strategic regrouping. Gratitude is extended to patrons and partners whose patience has become as vital a resource as the knowledge the library preserves. The reassurances given, while acknowledging the laborious task ahead, signal not just an intention to repair but to fortify, to adapt, to evolve amidst adversity.
This wretched turn of events serves as a portentous reminder that threats to our most sacred spaces have transformed. The digital revolution has indeed democratised knowledge but has also exposed it to neoteric threats. The British Library, a repository of the past, must now confront a distinctly modern adversary. It requires us to posit whether our contemporary guardians of history are equipped to combat those who wield malicious code as their weapons of choice.
Best Practices for Cyber Resilience
It is crucial to keep abreast with recent developments in cyberspace and emerging trends. Libraries in the digital age must ensure the protection of their patron’s data by applying comprehensive security protocols to safeguard the integrity, availability and confidentiality of sensitive information of their patrons. A few measures that can be applied by libraries include.
- Secured Wi-Fi networks: Libraries offering public Wi-Fi facilities must secure them with strong encryption protocols such as WPA 3. Libraries should establish separate networks for internal operations allowing separation of staff and public networks to protect sensitive information.
- Staff Training Programs: To avoid human error it is imperative that comprehensive training programs are conducted on a regular basis to generate greater awareness of cyber threats among staff and educate them about best practices of cyber hygiene and data security.
- Data Backups and Recovery Protocols: Patrons' sensitive data should be updated and backed up regularly. Proper verification of the user’s data integrity is crucial and should be stored securely in a dedicated repository to ensure full recovery of the user’s data in the event of a breach.
- Strong Authentication: Strong authentication to enhance library defenses is crucial to combat cyber threats. Staff and Patrons should be educated on strong password usage and the implementation of Multi-Factor Authentication to add an extra layer of security.
Conclusion
Finally, whatever the future holds, what remains unassailable is the cultural edifice that is the British Library. Its trials and tribulations, like those of the volumes it safeguards, become a part of a larger narrative of endurance and defiance. In the canon of history—filled with conflicts and resolutions—the library, like the lighter anecdotes and tragic tales it harbours, will decidedly hold its place. And perhaps, with some assurance, we might glean from the sentiment voiced by Milton—an assurance that the path from turmoil to enlightenment, though fraught with strenuous challenges, is paved with lessons learned and resilience rediscovered. Cyberspace is constantly evolving hence it is in our best interest to keep abreast of all developments in this digital sphere. Maximum threats can be avoided if we are vigilant.
References:
.webp)
Executive Summary
This report analyses a recently launched social engineering attack that took advantage of Microsoft Teams and AnyDesk to deliver DarkGate malware, a MaaS tool. This way, through Microsoft Teams and by tricking users into installing AnyDesk, attackers received unauthorized remote access to deploy DarkGate that offers such features as credential theft, keylogging, and fileless persistence. The attack was executed using obfuscated AutoIt scripts for the delivery of malware which shows how threat actors are changing their modus operandi. The case brings into focus the need to put into practice preventive security measures for instance endpoint protection, staff awareness, limited utilization of off-ice-connection tools, and compartmentalization to safely work with the new and increased risks that contemporary cyber threats present.
Introduction
Hackers find new technologies and application that are reputable for spreading campaigns. The latest use of Microsoft Teams and AnyDesk platforms for launching the DarkGate malware is a perfect example of how hackers continue to use social engineering and technical vulnerabilities to penetrate the defenses of organizations. This paper focuses on the details of the technical aspect of the attack, the consequences of the attack together with preventive measures to counter the threat.
Technical Findings
1. Attack Initiation: Exploiting Microsoft Teams
The attackers leveraged Microsoft Teams as a trusted communication platform to deceive victims, exploiting its legitimacy and widespread adoption. Key technical details include:
- Spoofed Caller Identity: The attackers used impersonation techniques to masquerade as representatives of trusted external suppliers.
- Session Hijacking Risks: Exploiting Microsoft Teams session vulnerabilities, attackers aimed to escalate their privileges and deploy malicious payloads.
- Bypassing Email Filters: The initial email bombardment was designed to overwhelm spam filters and ensure that malicious communication reached the victim’s inbox.
2. Remote Access Exploitation: AnyDesk
After convincing victims to install AnyDesk, the attackers exploited the software’s functionality to achieve unauthorized remote access. Technical observations include:
- Command and Control (C2) Integration: Once installed, AnyDesk was configured to establish persistent communication with the attacker’s C2 servers, enabling remote control.
- Privilege Escalation: Attackers exploited misconfigurations in AnyDesk to gain administrative privileges, allowing them to disable antivirus software and deploy payloads.
- Data Exfiltration Potential: With full remote access, attackers could silently exfiltrate data or install additional malware without detection.
3. Malware Deployment: DarkGate Delivery via AutoIt Script
The deployment of DarkGate malware utilized AutoIt scripting, a programming language commonly used for automating Windows-based tasks. Technical details include:
- Payload Obfuscation: The AutoIt script was heavily obfuscated to evade signature-based antivirus detection.
- Process Injection: The script employed process injection techniques to embed DarkGate into legitimate processes, such as explorer.exe or svchost.exe, to avoid detection.
- Dynamic Command Loading: The malware dynamically fetched additional commands from its C2 server, allowing real-time adaptation to the victim’s environment.
4. DarkGate Malware Capabilities
DarkGate, now available as a Malware-as-a-Service (MaaS) offering, provides attackers with advanced features. Technical insights include:
- Credential Dumping: DarkGate used the Mimikatz module to extract credentials from memory and secure storage locations.
- Keylogging Mechanism: Keystrokes were logged and transmitted in real-time to the attacker’s server, enabling credential theft and activity monitoring.
- Fileless Persistence: Utilizing Windows Management Instrumentation (WMI) and registry modifications, the malware ensured persistence without leaving traditional file traces.
- Network Surveillance: The malware monitored network activity to identify high-value targets for lateral movement within the compromised environment.
5. Attack Indicators
Trend Micro researchers identified several indicators of compromise (IoCs) associated with the DarkGate campaign:
- Suspicious Domains: example-remotesupport[.]com and similar domains used for C2 communication.
- Malicious File Hashes:some text
- AutoIt Script: 5a3f8d0bd6c91234a9cd8321a1b4892d
- DarkGate Payload: 6f72cde4b7f3e9c1ac81e56c3f9f1d7a
- Behavioral Anomalies:some text
- Unusual outbound traffic to non-standard ports.
- Unauthorized registry modifications under HKCU\Software\Microsoft\Windows\CurrentVersion\Run.
Broader Cyber Threat Landscape
In parallel with this campaign, other phishing and malware delivery tactics have been observed, including:
- Cloud Exploitation: Abuse of platforms like Cloudflare Pages to host phishing sites mimicking Microsoft 365 login pages.
- Quishing Campaigns: Phishing emails with QR codes that redirect users to fake login pages.
- File Attachment Exploits: Malicious HTML attachments embedding JavaScript to steal credentials.
- Mobile Malware: Distribution of malicious Android apps capable of financial data theft.
Implications of the DarkGate Campaign
This attack highlights the sophistication of threat actors in leveraging legitimate tools for malicious purposes. Key risks include:
- Advanced Threat Evasion: The use of obfuscation and process injection complicates detection by traditional antivirus solutions.
- Cross-Platform Risk: DarkGate’s modular design enables its functionality across diverse environments, posing risks to Windows, macOS, and Linux systems.
- Organizational Exposure: The compromise of a single endpoint can serve as a gateway for further network exploitation, endangering sensitive organizational data.
Recommendations for Mitigation
- Enable Advanced Threat Detection: Deploy endpoint detection and response (EDR) solutions to identify anomalous behavior like process injection and dynamic command loading.
- Restrict Remote Access Tools: Limit the use of tools like AnyDesk to approved use cases and enforce strict monitoring.
- Use Email Filtering and Monitoring: Implement AI-driven email filtering systems to detect and block email bombardment campaigns.
- Enhance Endpoint Security: Regularly update and patch operating systems and applications to mitigate vulnerabilities.
- Educate Employees: Conduct training sessions to help employees recognize and avoid phishing and social engineering tactics.
- Implement Network Segmentation: Limit the spread of malware within an organization by segmenting high-value assets.
Conclusion
Using Microsoft Teams and AnyDesk to spread DarkGate malware shows the continuous growth of the hackers’ level. The campaign highlights how organizations have to start implementing adequate levels of security preparedness to threats, including, Threat Identification, Training employees, and Rights to Access.
The DarkGate malware is a perfect example of how these attacks have developed into MaaS offerings, meaning that the barrier to launch highly complex attacks is only decreasing, which proves once again why a layered defense approach is crucial. Both awareness and flexibility are still the key issues in addressing the constantly evolving threat in cyberspace.


