#FactCheck - "Viral Video Misleadingly Claims Surrender to Indian Army, Actually Shows Bangladesh Army”
Executive Summary:
A viral video has circulated on social media, wrongly showing lawbreakers surrendering to the Indian Army. However, the verification performed shows that the video is of a group surrendering to the Bangladesh Army and is not related to India. The claim that it is related to the Indian Army is false and misleading.

Claims:
A viral video falsely claims that a group of lawbreakers is surrendering to the Indian Army, linking the footage to recent events in India.



Fact Check:
Upon receiving the viral posts, we analysed the keyframes of the video through Google Lens search. The search directed us to credible news sources in Bangladesh, which confirmed that the video was filmed during a surrender event involving criminals in Bangladesh, not India.

We further verified the video by cross-referencing it with official military and news reports from India. None of the sources supported the claim that the video involved the Indian Army. Instead, the video was linked to another similar Bangladesh Media covering the news.

No evidence was found in any credible Indian news media outlets that covered the video. The viral video was clearly taken out of context and misrepresented to mislead viewers.
Conclusion:
The viral video claiming to show lawbreakers surrendering to the Indian Army is footage from Bangladesh. The CyberPeace Research Team confirms that the video is falsely attributed to India, misleading the claim.
- Claim: The video shows miscreants surrendering to the Indian Army.
- Claimed on: Facebook, X, YouTube
- Fact Check: False & Misleading
Related Blogs

Executive Summary
A video circulating on social media falsely claims that Air India has cancelled all of its international flights until July due to a fuel shortage. However, research conducted by CyberPeace Research Wing found the claim to be misleading and false. Our research revealed that Air India has made no announcement regarding the cancellation of all international flights. In reality, the airline has only made temporary reductions and adjustments on select international routes due to increasing operational pressure and the impact on profitability.
Claim
An X (formerly Twitter) user shared the viral video on May 3, 2026, claiming: “Due to a fuel shortage, Air India has cancelled all its international flights until July.”he post quickly gained attention and was widely shared on social media platforms.

Fact Check
To verify the claim, we examined the official social media accounts of Air India. During the research, we found a post on X in which the airline itself described the viral claim as fake and misleading.

Taking the research further, we searched using relevant keywords and found a report published by ETNOW Swadesh on May 13, 2026. According to the report, Air India has not cancelled all international flights. Instead, due to mounting operational costs and pressure on profitability, the airline has temporarily reduced or modified services on a few select international routes.

Conclusion
Our research found that Air India has not announced the cancellation of all international flights until July. The viral claim circulating on social media is false and misleading. The airline has only implemented temporary adjustments and reductions on certain international routes, not a complete suspension of global operations.
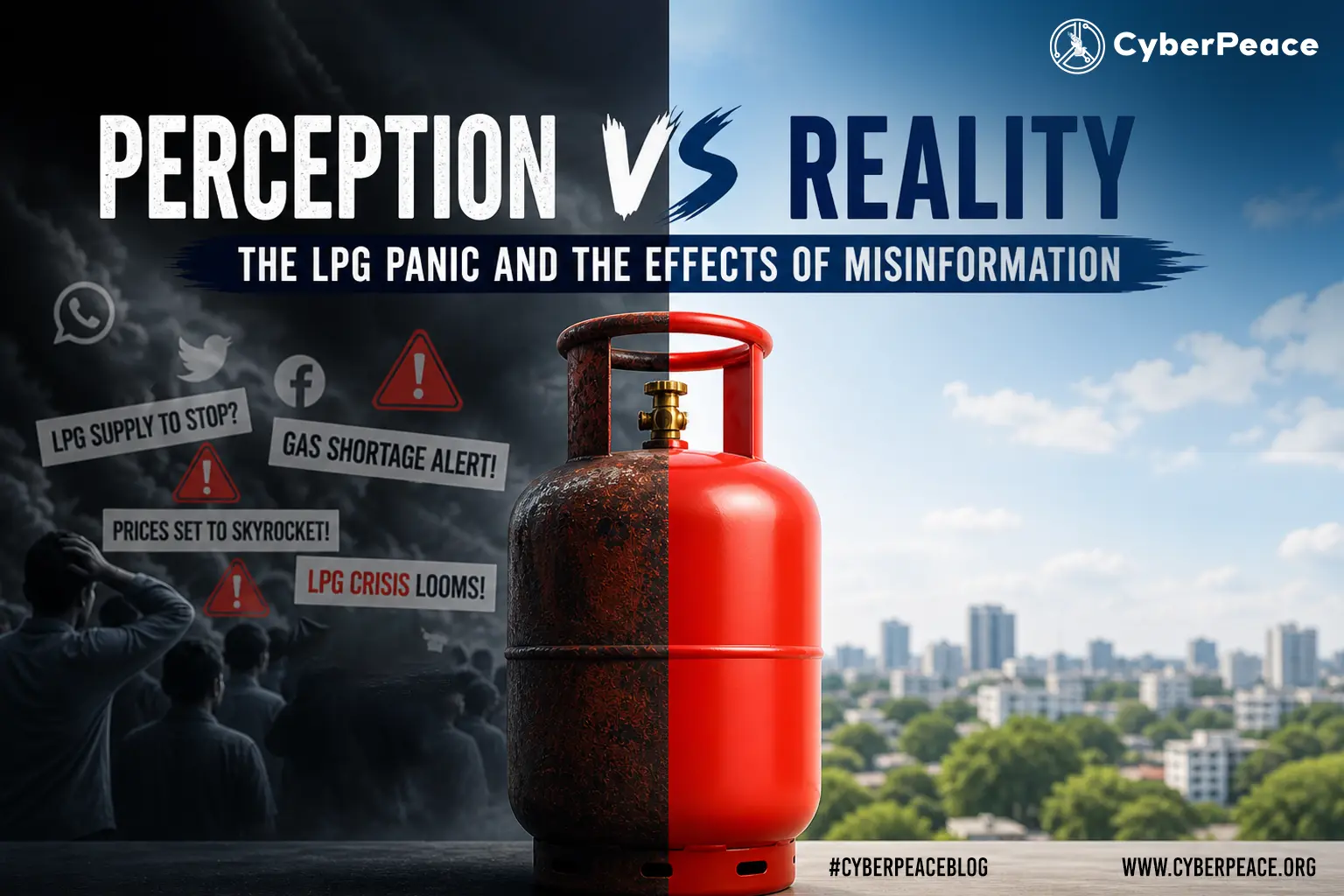
In recent months, conversations around the possible shortage of liquefied petroleum gas (LPG), a basic cooking fuel in Indian households, have quietly resurfaced across the country. From whispers in local markets to viral messages circulating on social media, concerns about LPG availability began to take hold in the public imagination. Though the immediacy of the situation has since faded, its echoes remain, reminding us how quickly uncertainty can spread. Like a ripple across still water, a single rumour can travel far, gathering force as it moves and blurring the line between perception and reality.
Against this backdrop, in April 2026, reports began circulating about a potential LPG shortage. The Union Government moved quickly to counter what it identified as misinformation, emphasising that supply remained stable and urging citizens not to engage in panic buying. A noticeable disconnect emerged between official communication and public perception. Across different regions, signs of anxiety-driven behaviour became evident. Instances of panic buying and hoarding increased, law enforcement agencies conducted raids to address such actions, and opportunistic thefts were reported, often exploiting widespread concern. These incidents highlight how misinformation, even when addressed promptly, can continue to shape public behaviour.
It is worth noting that rising prices also played a role in shaping public response, as increases in LPG rates contributed to a sense of urgency among consumers. Therefore, the surge in panic buying cannot be attributed solely to misinformation, but rather to a combination of economic pressures and perceived scarcity.
Misinformation Ecosystem - From Rumours to Behaviour
The spread of misinformation is occurring at an unprecedented pace and is, in large part, driven by the viral nature of social media. Digital platforms not only enable the rapid dissemination of information but also allow it to be amplified in ways that would not be possible through traditional media outlets. Often, the drive for virality outweighs any concern for accuracy, meaning that many individuals who spread misinformation are motivated more by the pursuit of attention than by any ideological agenda. Recent arrests of individuals involved in spreading misinformation about LPG and petrol shortages, much of which went viral, suggest that misinformation today is frequently driven by the desire for visibility rather than ideological motives. The information being circulated has largely followed a similar pattern, focusing on fears of an LPG shortage, expectations of price increases, and concerns about supply disruptions. Even though this information has not been verified, it has triggered behavioural responses among individuals. In several areas, including parts of Uttar Pradesh and Goa, the spread of misinformation through social media has led to panic buying, despite official assurances that there would be sufficient LPG supply to meet demand.
The impact of panic buying, and its associated misinformation, has already been seen in multiple sectors; these increased demands have placed pressure on the distribution network, leading to disruptions in access, as well as being out of stock of certain products. In many cases, commercial users of products (especially restaurants) have experienced significant disruption, threatening their continued operations, and industry representatives have alerted others about the inconsistent supply of commercial cylinders; likewise, consumers (households) are beginning to switch to alternative products (e.g., induction cooking) as a reflection of the anticipatory mindset to address the uncertainty created through perceptions of Product Scarcity.
State Response: Managing Misinformation or Behaviour?

The government has taken a variety of approaches, from advisories and enforcement actions to communicating with citizens indirectly. For example, State Governments have been directed to combat misinformation, monitor supply chains and take action against hoarding and black market activity. There has been a significant increase in the level of large- scale enforcement activity, with over 3,700 raids carried out to crack down on hoarding and black marketing related to LPG, in addition to confiscating cylinders and issuing penalties to those who break the law. In addition, the authorities have also focused on maintaining regular communication with the public in order to reassure them about the supply of LPG and fuel stability.
Geopolitical Context: Why Rumours Are Believable
Understanding today’s panic requires an understanding of the global environment: i.e., due to the ongoing conflict in West Asia, the energy markets are unstable, and energy supply is uncertain not only in West Asia but across a large part of the world. Even if domestic supply remains stable, public perception is affected by global instability. A clear example of this can be seen in neighbouring countries to India; Pakistan has seen significant increases in the cost of fuel, implemented measures such as reducing the number of days individuals work each week, and has created public support mechanisms; Bangladesh has imposed restrictions on the use of energy, has shortened the number of hours individuals can operate businesses each day, and has restricted the total amount of energy used; Sri Lanka has begun to ration fuel, and to increase the price of petrol; and Nepal has reduced the numbers of days individuals may work each week, and has adjusted supply.
All of these examples are not isolated instances, but are markers of a common regional environment. As we live in a global community that is connected in many ways, these developments will quickly affect public expectations everywhere. Therefore, for consumers in India, seeing evidence of rationing of fuel and shortages of fuel in neighbouring countries increases their belief that these types of problems could occur in their country.
Critical Perspective: Between Panic and Precaution
The LPG incident has brought about questions surrounding the nature of misinformation in terms of its definition & regulation. One of the main concerns is whether or not "misinformation" is being cast too widely. To be sure, false claims need to be addressed; however, not everything that is responded to publicly is based on untrue facts, as many times public responses are based on perceived risk via global and/or local incidents that occur. Perhaps the greatest challenge is the difficulty in differentiating precaution and panic. People’s memories of the COVID-19 pandemic are fresh in their minds and will serve to influence their behaviours moving onward, in that many people are stockpiling or preparing for uncertainty not out of irrational fear, but as an anticipatory response to their prior experiences.
Conclusion
The Indian LPG "crisis" is not so much a problem with actual supply chain breakdown as it is a result of how information and behaviour are connected through perception. This cohabitating environment of panic buying, law enforcement, and government assurance demonstrates an evident disconnect and gap between how governments present a narrative and how the public responds. While there is some role of misinformation within this discourse, the misinformation itself extends beyond any or all false claims about LPG supply and operates within a greater ecosystem of global uncertainty and personal experience. As such, and because of this, perception becomes an incredibly strong force in itself that produces true economic consequences.
Reference
- https://www.pib.gov.in/PressReleasePage.aspx?PRID=2248640&utm_source®=3&lang=2
- https://www.pmindia.gov.in/en/news_updates/pm-addresses-the-lok-sabha-on-the-ongoing-conflict-in-west-asia/
- https://www.ndtv.com/delhi-news/iran-war-middle-east-conflict-why-the-lpg-crisis-is-forcing-migrants-to-quietly-leave-delhi-11313629
- https://timesofindia.indiatimes.com/city/bareilly/thieves-steal-108-lpg-cylinders-from-godown-in-up/articleshow/130035518.cms
- https://indianexpress.com/article/india/arrested-rumours-lpg-petrol-shortage-police-chasing-views-10614193/
- https://www.hindustantimes.com/cities/lucknow-news/social-media-rumours-fuel-panic-buying-in-some-up-districts-situation-normal-in-lucknow-101774465353107.html
- https://timesofindia.indiatimes.com/city/goa/fear-of-shortage-price-rise-fuels-panic-buying-across-goa/articleshow/129810144.cms
- https://www.news18.com/cities/new-delhi-news/online-rumours-offline-rush-panic-buying-sweeps-petrol-pumps-across-cities-whats-the-truth-ws-ln-9995684.html
- https://m.economictimes.com/news/india/3700-raids-conducted-across-country-to-wipe-out-lpg-black-marketing-says-centre/articleshow/130025232.cms
- https://www.reuters.com/business/energy/induction-stoves-fly-off-shelves-india-gas-shortage-fears-spark-panic-buying-2026-03-12/
- https://www.ndtv.com/india-news/restaurant-body-warns-of-closures-over-commercial-lpg-supply-concerns-writes-to-minister-11194418
- https://www.freepressjournal.in/mumbai/fpj-dialogue-we-are-getting-only-1-cylinder-instead-of-10-says-ahar-president-vijay-shetty-on-mumbai-lpg-crisis
- https://www.hindustantimes.com/world-news/fuel-cuts-wfh-and-more-how-indias-neighbours-are-dealing-with-global-energy-crisis-triggered-by-us-iran-war-101775397199941.html
- https://www.abc.net.au/news/2026-03-30/four-step-fuel-supply-plan-national-cabinet-fuel-crisis/106512706
- https://tribune.net.ph/2026/04/07/philippines-scrambles-as-regional-oil-crisis-hits

Introduction
As India moves full steam ahead towards a trillion-dollar digital economy, how user data is gathered, processed and safeguarded is under the spotlight. One of the most pervasive but least known technologies used to gather user data is the cookie. Cookies are inserted into every website and application to improve functionality, measure usage and customize content. But they also present enormous privacy threats, particularly when used without explicit user approval.
In 2023, India passed the Digital Personal Data Protection Act (DPDP) to give strong legal protection to data privacy. Though the act does not refer to cookies by name, its language leaves no doubt as to the inclusion of any technology that gathers or processes personal information and thus cookies regulation is at the centre of digital compliance in India. This blog covers what cookies are, how international legislation, such as the GDPR, has addressed them and how India's DPDP will regulate their use.
What Are Cookies and Why Do They Matter?
Cookies are simply small pieces of data that a website stores in the browser. They were originally designed to help websites remember useful information about users, such as your login session or what is in your shopping cart. Netscape initially built them in 1994 to make web surfing more efficient.
Cookies exist in various types. Session cookies are volatile and are deleted when the browser is shut down, whereas persistent cookies are stored on the device to monitor users over a period of time. First-party cookies are made by the site one is visiting, while third-party cookies are from other domains, usually utilised for advertisements or analytics. Special cookies, such as secure cookies, zombie cookies and tracking cookies, differ in intent and danger. They gather information such as IP addresses, device IDs and browsing history information associated with a person, thus making it personal data per the majority of data protection regulations.
A Brief Overview of the GDPR and Cookie Policy
The GDPR regulates how personal data can be processed in general. However, if a cookie collects personal data (like IP addresses or identifiers that can track a person), then GDPR applies as well, because it sets the rules on how that personal data may be processed, what lawful bases are required, and what rights the user has.
The ePrivacy Directive (also called the “Cookie Law”) specifically regulates how cookies and similar technologies can be used. Article 5(3) of the ePrivacy Directive says that storing or accessing information (such as cookies) on a user’s device requires prior, informed consent, unless the cookie is strictly necessary for providing the service requested by the user.
In the seminal Planet49 decision, the Court of Justice of the European Union held that pre-ticked boxes do not represent valid consent. Another prominent enforcement saw Amazon fined €35 million by France's CNIL for using tracking cookies without user consent.
Cookies and India’s Digital Personal Data Protection Act (DPDP), 2023
India's Digital Personal Data Protection Act, 2023 does not refer to cookies specifically but its provisions necessarily come into play when cookies harvest personal data like user activity, IP addresses, or device data. According to DPDP, personal data is to be processed for legitimate purposes with the individual's consent. The consent has to be free, informed, clear and unambiguous. The individuals have to be informed of what data is collected, how it will be processed.. The Act also forbids behavioural monitoring and targeted advertising in the case of children.
The Ministry of Electronics and IT released the Business Requirements Document for Consent Management Systems (BRDCMS) in June 2025. Although it is not binding by law, it provides operational advice on cookie consent. It recommends that websites use cookie banners with "Accept," "Reject," and "Customize" choices. Users must be able to withdraw or change their consent at any moment. Multi-language handling and automatic expiry of cookie preferences are also suggested to suit accessibility and privacy requirements.
The DPDP Act and the BRDCMS together create a robust user-rights model, even in the absence of a special cookie law.
What Should Indian Websites Do?
For the purposes of staying compliant, Indian websites and online platforms need to act promptly to harmonise their use of cookies with DPDP principles. This begins with a transparent and simple cookie banner providing users with an opportunity to accept or decline non-essential cookies. Consent needs to be meaningful; coercive tactics such as cookie walls must not be employed. Websites need to classify cookies (e.g., necessary, analytics and ads) and describe each category's function in plain terms under the privacy policy. Users must be given the option to modify cookie settings anytime using a Consent Management Platform (CMP). Monitoring children or their behavioural information must be strictly off-limits.
These are not only about being compliant with the law, they're about adhering to ethical data stewardship and user trust building.
What Should Users Do?
Cookies need to be understood and controlled by users to maintain online personal privacy. Begin by reading cookie notices thoroughly and declining unnecessary cookies, particularly those associated with tracking or advertising. The majority of browsers today support blocking third-party cookies altogether or deleting them periodically.
It is also recommended to check and modify privacy settings on websites and mobile applications. It is possible to minimise surveillance with the use of browser add-ons such as ad blockers or privacy extensions. Users are also recommended not to blindly accept "accept all" in cookie notices and instead choose "customise" or "reject" where not necessary for their use.
Finally, keeping abreast of data rights under Indian law, such as the right to withdraw consent or to have data deleted, will enable people to reclaim control over their online presence.
Conclusion
Cookies are a fundamental component of the modern web, but they raise significant concerns about individual privacy. India's DPDP Act, 2023, though not explicitly referring to cookies, contains an effective legal framework that regulates any data collection activity involving personal data, including those facilitated by cookies.
As India continues to make progress towards comprehensive rulemaking and regulation, companies need to implement privacy-first practices today. And so must the users, in an active role in their own digital lives. Collectively, compliance, transparency and awareness can build a more secure and ethical internet ecosystem where privacy is prioritised by design.
References
- https://prsindia.org/billtrack/digital-personal-data-protection-bill-2023
- https://gdpr-info.eu/
- https://d38ibwa0xdgwxx.cloudfront.net/create-edition/7c2e2271-6ddd-4161-a46c-c53b8609c09d.pdf
- https://oag.ca.gov/privacy/ccpa
- https://www.barandbench.com/columns/cookie-management-under-the-digital-personal-data-protection-act-2023#:~:text=The%20Business%20Requirements%20Document%20for,the%20DPDP%20Act%20and%20Rules.
- https://samistilegal.in/cookies-meaning-legal-regulations-and-implications/#
- https://secureprivacy.ai/blog/india-digital-personal-data-protection-act-dpdpa-cookie-consent-requirements
- https://law.asia/cookie-use-india/
- https://www.cookielawinfo.com/major-gdpr-fines-2020-2021/#:~:text=4.,French%20websites%20could%20refuse%20cookies.


