#FactCheck: Viral video of Unrest in Kenya is being falsely linked with J&K
Executive Summary:
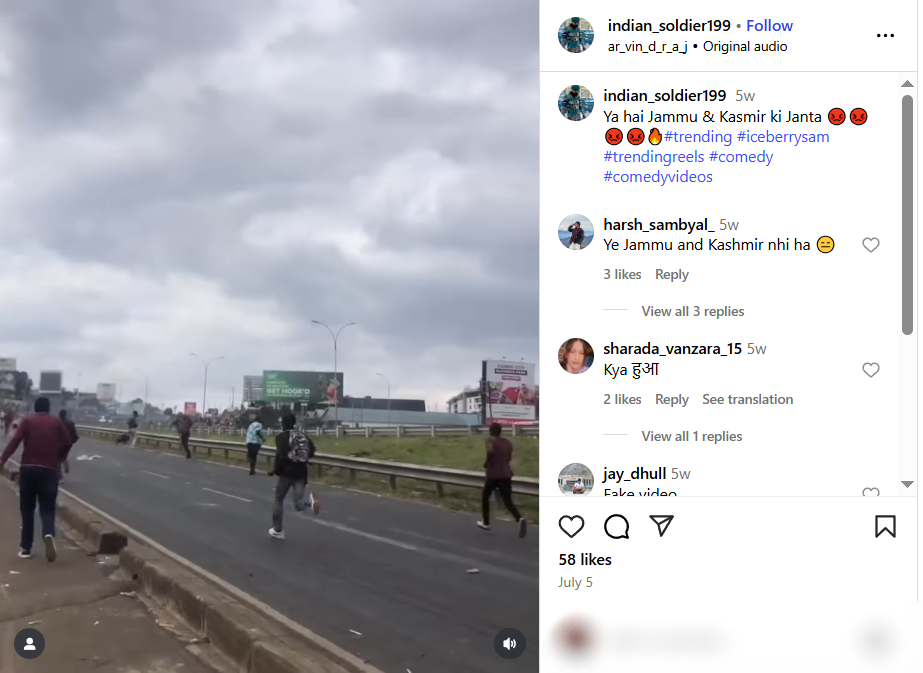
A video of people throwing rocks at vehicles is being shared widely on social media, claiming an incident of unrest in Jammu and Kashmir, India. However, our thorough research has revealed that the video is not from India, but from a protest in Kenya on 25 June 2025. Therefore, the video is misattributed and shared out of context to promote false information.

Claim:
The viral video shows people hurling stones at army or police vehicles and is claimed to be from Jammu and Kashmir, implying ongoing unrest and anti-government sentiment in the region.
Fact Check:
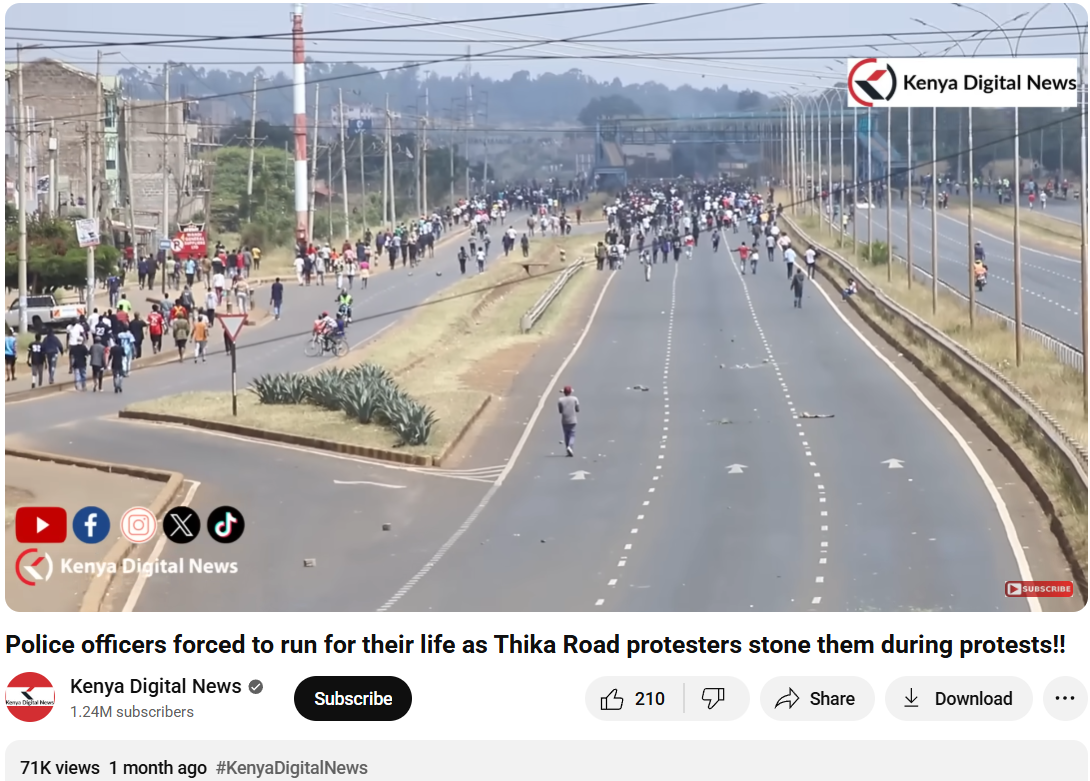
To verify the validity of the viral statement, we did a reverse image search by taking key frames from the video. The results clearly demonstrated that the video was not sourced from Jammu and Kashmir as claimed, but rather it was consistent with footage from Nairobi, Kenya, where a significant protest took place on 25 June 2025. Protesters in Kenya had congregated to express their outrage against police brutality and government action, which ultimately led to violent clashes with police.

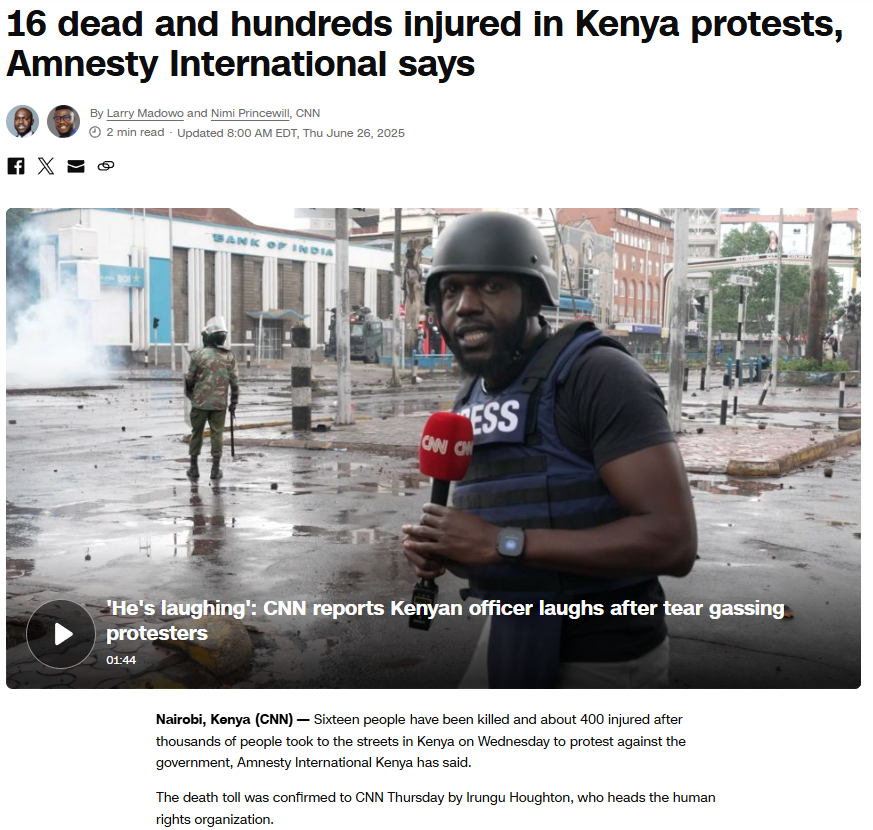
We also came across a YouTube video with similar news and frames. The protests were part of a broader anti-government movement to mark its one-year time period.
To support the context, we did a keyword search of any mob violence or recent unrest in J&K on a reputable Indian news source, But our search did not turn up any mention of protests or similar events in J&K around the relevant time. Based on this evidence, it is clear that the video has been intentionally misrepresented and is being circulated with false context to mislead viewers.
Conclusion:
The assertion that the viral video shows a protest in Jammu and Kashmir is incorrect. The video appears to be taken from a protest in Nairobi, Kenya, in June 2025. Labeling the video incorrectly only serves to spread misinformation and stir up uncalled for political emotions. Always be sure to verify where content is sourced from before you believe it or share it.
- Claim: Army faces heavy resistance from Kashmiri youth — the valley is in chaos.
- Claimed On: Social Media
- Fact Check: False and Misleading
Related Blogs

Executive Summary:
The picture of a boy making sand art of Indian Cricketer Virat Kohli spreading in social media, claims to be false. The picture which was portrayed, revealed not to be a real sand art. The analyses using AI technology like 'Hive' and ‘Content at scale AI detection’ confirms that the images are entirely generated by artificial intelligence. The netizens are sharing these pictures in social media without knowing that it is computer generated by deep fake techniques.

Claims:
The collage of beautiful pictures displays a young boy creating sand art of Indian Cricketer Virat Kohli.




Fact Check:
When we checked on the posts, we found some anomalies in each photo. Those anomalies are common in AI-generated images.

The anomalies such as the abnormal shape of the child’s feet, blended logo with sand color in the second image, and the wrong spelling ‘spoot’ instead of ‘sport’n were seen in the picture. The cricket bat is straight which in the case of sand made portrait it’s odd. In the left hand of the child, there’s a tattoo imprinted while in other photos the child's left hand has no tattoo. Additionally, the face of the boy in the second image does not match the face in other images. These made us more suspicious of the images being a synthetic media.
We then checked on an AI-generated image detection tool named, ‘Hive’. Hive was found to be 99.99% AI-generated. We then checked from another detection tool named, “Content at scale”


Hence, we conclude that the viral collage of images is AI-generated but not sand art of any child. The Claim made is false and misleading.
Conclusion:
In conclusion, the claim that the pictures showing a sand art image of Indian cricket star Virat Kohli made by a child is false. Using an AI technology detection tool and analyzing the photos, it appears that they were probably created by an AI image-generated tool rather than by a real sand artist. Therefore, the images do not accurately represent the alleged claim and creator.
Claim: A young boy has created sand art of Indian Cricketer Virat Kohli
Claimed on: X, Facebook, Instagram
Fact Check: Fake & Misleading
.webp)
Introduction
Misinformation is a major issue in the AI age, exacerbated by the broad adoption of AI technologies. The misuse of deepfakes, bots, and content-generating algorithms have made it simpler for bad actors to propagate misinformation on a large scale. These technologies are capable of creating manipulative audio/video content, propagate political propaganda, defame individuals, or incite societal unrest. AI-powered bots may flood internet platforms with false information, swaying public opinion in subtle ways. The spread of misinformation endangers democracy, public health, and social order. It has the potential to affect voter sentiments, erode faith in the election process, and even spark violence. Addressing misinformation includes expanding digital literacy, strengthening platform detection capabilities, incorporating regulatory checks, and removing incorrect information.
AI's Role in Misinformation Creation
AI's growth in its capabilities to generate content have grown exponentially in recent years. Legitimate uses or purposes of AI many-a-times take a backseat and result in the exploitation of content that already exists on the internet. One of the main examples of misinformation flooding the internet is when AI-powered bots flood social media platforms with fake news at a scale and speed that makes it impossible for humans to track and figure out whether the same is true or false.
The netizens in India are greatly influenced by viral content on social media. AI-generated misinformation can have particularly negative consequences. Being literate in the traditional sense of the word does not automatically guarantee one the ability to parse through the nuances of social media content authenticity and impact. Literacy, be it social media literacy or internet literacy, is under attack and one of the main contributors to this is the rampant rise of AI-generated misinformation. Some of the most common examples of misinformation that can be found are related to elections, public health, and communal issues. These issues have one common factor that connects them, which is that they evoke strong emotions in people and as such can go viral very quickly and influence social behaviour, to the extent that they may lead to social unrest, political instability and even violence. Such developments lead to public mistrust in the authorities and institutions, which is dangerous in any economy, but even more so in a country like India which is home to a very large population comprising a diverse range of identity groups.
Misinformation and Gen AI
Generative AI (GAI) is a powerful tool that allows individuals to create massive amounts of realistic-seeming content, including imitating real people's voices and creating photos and videos that are indistinguishable from reality. Advanced deepfake technology blurs the line between authentic and fake. However, when used smartly, GAI is also capable of providing a greater number of content consumers with trustworthy information, counteracting misinformation.
Generative AI (GAI) is a technology that has entered the realm of autonomous content production and language creation, which is linked to the issue of misinformation. It is often difficult to determine if content originates from humans or machines and if we can trust what we read, see, or hear. This has led to media users becoming more confused about their relationship with media platforms and content and highlighted the need for a change in traditional journalistic principles.
We have seen a number of different examples of GAI in action in recent times, from fully AI-generated fake news websites to fake Joe Biden robocalls telling the Democrats in the U.S. not to vote. The consequences of such content and the impact it could have on life as we know it are almost too vast to even comprehend at present. If our ability to identify reality is quickly fading, how will we make critical decisions or navigate the digital landscape safely? As such, the safe and ethical use and applications of this technology needs to be a top global priority.
Challenges for Policymakers
AI's ability to generate anonymous content makes it difficult to hold perpetrators accountable due to the massive amount of data generated. The decentralised nature of the internet further complicates regulation efforts, as misinformation can spread across multiple platforms and jurisdictions. Balancing the need to protect the freedom of speech and expression with the need to combat misinformation is a challenge. Over-regulation could stifle legitimate discourse, while under-regulation could allow misinformation to propagate unchecked. India's multilingual population adds more layers to already-complex issue, as AI-generated misinformation is tailored to different languages and cultural contexts, making it harder to detect and counter. Therefore, developing strategies catering to the multilingual population is necessary.
Potential Solutions
To effectively combat AI-generated misinformation in India, an approach that is multi-faceted and multi-dimensional is essential. Some potential solutions are as follows:
- Developing a framework that is specific in its application to address AI-generated content. It should include stricter penalties for the originator and spreader and dissemination of fake content in proportionality to its consequences. The framework should establish clear and concise guidelines for social media platforms to ensure that proactive measures are taken to detect and remove AI-generated misinformation.
- Investing in tools that are driven by AI for customised detection and flagging of misinformation in real time. This can help in identifying deepfakes, manipulated images, and other forms of AI-generated content.
- The primary aim should be to encourage different collaborations between tech companies, cyber security orgnisations, academic institutions and government agencies to develop solutions for combating misinformation.
- Digital literacy programs will empower individuals by training them to evaluate online content. Educational programs in schools and communities teach critical thinking and media literacy skills, enabling individuals to better discern between real and fake content.
Conclusion
AI-generated misinformation presents a significant threat to India, and it is safe to say that the risks posed are at scale with the rapid rate at which the nation is developing technologically. As the country moves towards greater digital literacy and unprecedented mobile technology adoption, one must be cognizant of the fact that even a single piece of misinformation can quickly and deeply reach and influence a large portion of the population. Indian policymakers need to rise to the challenge of AI-generated misinformation and counteract it by developing comprehensive strategies that not only focus on regulation and technological innovation but also encourage public education. AI technologies are misused by bad actors to create hyper-realistic fake content including deepfakes and fabricated news stories, which can be extremely hard to distinguish from the truth. The battle against misinformation is complex and ongoing, but by developing and deploying the right policies, tools, digital defense frameworks and other mechanisms, we can navigate these challenges and safeguard the online information landscape.
References:
- https://economictimes.indiatimes.com/news/how-to/how-ai-powered-tools-deepfakes-pose-a-misinformation-challenge-for-internet-users/articleshow/98770592.cms?from=mdr
- https://www.dw.com/en/india-ai-driven-political-messaging-raises-ethical-dilemma/a-69172400
- https://pure.rug.nl/ws/portalfiles/portal/975865684/proceedings.pdf#page=62

Introduction
In the past few decades, technology has rapidly advanced, significantly impacting various aspects of life. Today, we live in a world shaped by technology, which continues to influence human progress and culture. While technology offers many benefits, it also presents certain challenges. It has increased dependence on machines, reduced physical activity, and encouraged more sedentary lifestyles. The excessive use of gadgets has contributed to social isolation. Different age groups experience the negative aspects of the digital world in distinct ways. For example, older adults often face difficulties with digital literacy and accessing information. This makes them more vulnerable to cyber fraud. A major concern is that many older individuals may not be familiar with identifying authentic versus fraudulent online transactions. The consequences of such cybercrimes go beyond financial loss. Victims may also experience emotional distress, reputational harm, and a loss of trust in digital platforms.
Why Senior Citizens Are A Vulnerable Target
Digital exploitation involves a variety of influencing tactics, such as coercion, undue influence, manipulation, and frequently some sort of deception, which makes senior citizens easy targets for scammers. Senior citizens have been largely neglected in research on this burgeoning type of digital crime. Many of our parents and grandparents grew up in an era when politeness and trust were very common, making it difficult for them to say “no” or recognise when someone was attempting to scam them. Seniors who struggle with financial stability may be more likely to fall for scams promising financial relief or security. They might encounter obstacles in learning to use new technologies, mainly due to unfamiliarity. It is important to note that these factors do not make seniors weak or incapable. Rather, it is the responsibility of the community to recognise and address the unique vulnerabilities of our senior population and work to prevent them from falling victim to scams.
Senior citizens are the most susceptible to social engineering attacks. Scammers may impersonate people, such as family members in distress, government officials, and deceive seniors into sending money or sharing personal information. Some of them are:
- The grandparent scam
- Tech support scam
- Government impersonation scams
- Romance scams
- Digital arrest
Protecting Senior Citizens from Digital Scams
As a society, we must focus on educating seniors about common cyber fraud techniques such as impersonation of family members or government officials, the use of fake emergencies, or offers that seem too good to be true. It is important to guide them on how to verify suspicious calls and emails, caution them against sharing personal information online, and use real-life examples to enhance their understanding.
Larger organisations and NGOs can play a key role in protecting senior citizens from digital scams by conducting fraud awareness training, engaging in one-on-one conversations, inviting seniors to share their experiences through podcasts, and organising seminars and workshops specifically for individuals aged 60 and above.
Safety Tips
In today's digital age, safeguarding oneself from cyber threats is crucial for people of all ages. Here are some essential steps everyone should take at a personal level to remain cyber secure:
- Ensuring that software and operating systems are regularly updated allows users to benefit from the latest security fixes, reducing their vulnerability to cyber threats.
- Avoiding the sharing of personal information online is also essential. Monitoring bank statements is equally important, as it helps in quickly identifying signs of potential cybercrime. Reviewing financial transactions and reporting any unusual activity to the bank can assist in detecting and preventing fraud.
- If suspicious activity is suspected, it is advisable to contact the company directly using a different phone line. This is because cybercriminals can sometimes keep the original line open, leading individuals to believe they are speaking with a legitimate representative. In such cases, attackers may impersonate trusted organisations to deceive users and gain sensitive information.
- If an individual becomes a victim of cybercrime, they should take immediate action to protect their personal information and seek professional guidance.
- Stay calm and respond swiftly and wisely. Begin by collecting and preserving all evidence—this includes screenshots, suspicious messages, emails, or any unusual activity. Report the incident immediately to the police or through an official platform like www.cybercrime.gov.in and the helpline number 1930.
- If financial information is compromised, the affected individual must alert their bank or financial institution without delay to secure their accounts. They should also update passwords and implement two-factor authentication as additional safeguards.
Conclusion: Collective Action for Cyber Dignity and Inclusion
Elder abuse in the digital age is an invisible crisis. It’s time we bring it into the spotlight and confront it with education, empathy, and collective action. Safeguarding senior citizens from cybercrime necessitates a comprehensive approach that combines education, vigilance, and technological safeguards. By fostering awareness and providing the necessary tools and support, we can empower senior citizens to navigate the digital world safely and confidently. Let us stand together to support these initiatives, to be the guardians our elders deserve, and to ensure that the digital world remains a place of opportunity, not exploitation.
REFERENCES -
- https://portal.ct.gov/ag/consumer-issues/hot-scams/the-grandparents-scam
- https://www.fbi.gov/how-we-can-help-you/scams-and-safety/common-frauds-and-scams/tech-support-scams
- https://consumer.ftc.gov/articles/how-avoid-government-impersonation-scam
- https://www.jpmorgan.com/insights/fraud/fraud-mitigation/helping-your-elderly-and-vulnerable-loved-ones-avoid-the-scammers
- https://www.fbi.gov/how-we-can-help-you/scams-and-safety/common-frauds-and-scams/romance-scams
- https://www.jpmorgan.com/insights/fraud/fraud-mitigation/helping-your-elderly-and-vulnerable-loved-ones-avoid-the-scammers


