#FactCheck - Viral Video Claiming Attack on Burj Khalifa is AI-Generated
Executive Summary
Amid rising tensions between the United States, Israel, and Iran, a video is circulating on social media claiming that Burj Khalifa in Dubai has been attacked. The clip is being widely shared with users alleging that a strike took place near the iconic skyscraper. However, research by CyberPeace found the claim to be misleading. Our research revealed that the viral video is not real and was generated using artificial intelligence.
Claim
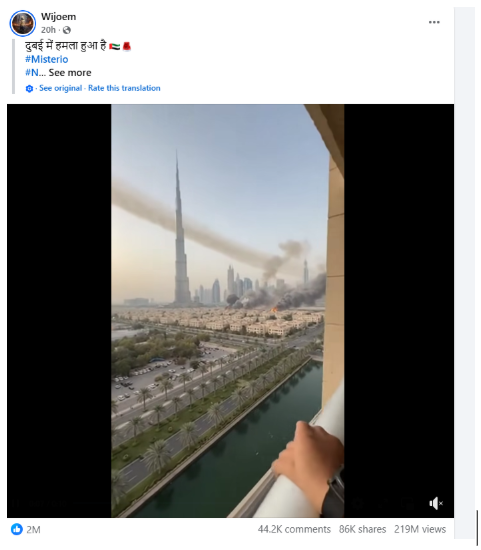
On March 1, 2026, a Facebook user shared the viral clip claiming that an attack had taken place in Dubai. The post was shared with the caption: “Dubai has been attacked.” The link to the post and its archive is provided below along with a screenshot.
Fact Check
To verify the claim, we first searched Google using relevant keywords. During this process, we found a report published on March 1, 2026, by the Indian news outlet Dainik Bhaskar.
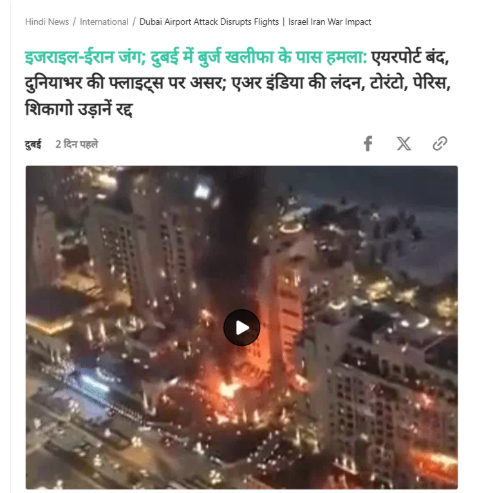
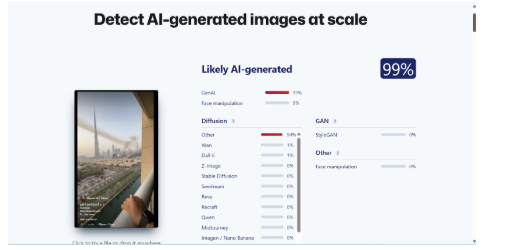
According to the report, tensions in the Middle East escalated amid the Israel–Iran conflict, impacting several countries in the region. A drone incident reportedly occurred near Burj Khalifa, prompting authorities to evacuate the building as a precautionary measure and temporarily switch off its lights. However, the visuals seen in the viral video do not match the details or imagery described in the report. Upon closely examining the viral clip, we noticed several technical inconsistencies and unusual visual elements, raising suspicions that the video might have been generated using artificial intelligence. To verify this, we analyzed the video using the AI detection tool Sightengine. The results indicated a 99% probability that the video was AI-generated.
Conclusion
Our research found that the viral video circulating on social media is not authentic. The footage was created using artificial intelligence and does not depict a real attack on Burj Khalifa.
Related Blogs

Introduction
Cybercrime in India is developing at a rapid rate in terms of depth and volume, with culprits leveraging technology, anonymity, and social engineering to exploit unsuspecting victims. In a high-profile instance of coordinated police action, the Delhi Police Crime Branch recently cracked a large-scale pan-India cybercrime syndicate with its arms stretching across Delhi, Rajasthan, and Uttar Pradesh. The syndicate used to be involved in a range of cybercrimes, from sextortion and online fraud to fake call centres and cloning of bank accounts. With over ₹5 crore of illicit financial transactions revealed, the operation highlights the critical role of proactive cyber policing, data security and public awareness in India's war against digital crime.
A Multi-State Operation: Crime Network across States
On May 24, 2025, on receiving a tip-off, the Delhi Police conducted a specific raid in New Ashok Nagar to catch a suspect consignment said to be used for cybercrime. This resulted in a multi-layered investigation that revealed a large crime syndicate. Police recovered 28 mobile phones, 30 SIM cards, 15 debit cards, 8 cheque books, and two laptops, equipment said to have been used in crimes ranging from sextortion to fake loan scams.
Three of the initial arrests revealed the use of fake kits like pre-activated SIMs and counterfeit documents to create phoney digital identities and bank accounts. They were being used to bypass KYC norms and make untraceable transactions, illustrating how cyber thieves exploit digital identity as well as financial authentication loopholes in the system.
Fake Call Centre Falsely Claiming to be a Lender
Tracing the leads, the investigation then led the police to Mundka, a semi-residential and industrial area in Delhi, where a fake call centre in the name of a loan assistance service was operating. Suspects were allegedly operating the business. With deceptive scripts, their telemarketing staff lured victims with the offer of instant personal loans. When a prospective victim replied favorably and was willing to go further, he was asked to send identification documents and was then forced to pay a "processing fee." Once the payment was made, the accused would cut off contact immediately, leaving the victims shortchanged.
During the raid, seven individuals were apprehended, six of whom were trained tele-callers with a reasonable level of technical skill. In spite of possessing educational certificates and receiving a meagre pay of between ₹8,000 and ₹9,000 a month, these individuals had been enticed into the cybercrime network, demonstrating how educated youth are now more commonly being exploited or recruited by such scam networks in return for quick money.
Uncovering the Sextortion Racket
The most shocking disclosure was that of a sextortion racket being run from New Ashok Nagar, a residential area located in West Delhi, New Delhi. Suspects tricked victims with fraudulent Facebook profiles, contacted them on Messenger, and then changed to WhatsApp video calls. Pornographic videos were played on such calls while the reactions of the victim were secretly recorded. These were later utilised for extortion by threatening to share them with the whole world. The ability of such a group to blackmail and psychologically manipulate the victims indicates the psychological nature of cybercrime and the need for online safety education.
Impact and Significance: A Wake-Up Call for Law Enforcement and Public Awareness
This crackdown is uncovering some ominous trends that reflect the changing face of cybercrime in India. The syndicate's framework highlights the organised and multi-state nature of cybercrime, mostly operating through systemic loopholes. Misuse of social media sites and fintech apps is also rampant, and these are being leveraged for scams, sextortion, and monetary fraud. One of the most concerning trends is young people becoming more engaged in cybercrime, either out of economic necessity or enticed by easy cash. Most of these scams increasingly involve psychological manipulation, particularly in sextortion, where shame and fear are employed as tools. Digital identity fraud has also been facilitated through false documents and lenient Know Your Customer (KYC) checks, with fraudsters being able to evade verification processes.
These observations underscore the necessity of strong reporting channels. There also needs to be an urgent implementation of stringent verification standards in the telecom and banking industries, along with extensive community-level digital literacy initiatives to sensitise citizens to online threats and preventive measures.
CyberPeace Vision: Building a Safe Digital India
India needs a multi-level cyber security approach, comprising people awareness, AI-driven detection systems, and coordination of inter-state policing. Precedence needs to be given to:
- Capacity building of cyber police units.
- Real-time exchange of scam intelligence among law enforcement.
- Schools, colleges, and workplaces should be aware of digital hygiene.
- Rehabilitation of cyber-offenders, especially youth.
- Countering online misinformation and disinformation through fact-checking and public education campaigns
- Ensuring inclusivity in cyber safety policies so vulnerable populations, including rural users, senior citizens, and linguistic minorities, are not left behind
The breakdown of the syndicate is a major victory, but the absence of difficulty with which these networks function highlights the need for cybercrime prevention initiatives, not after the fact.
Conclusion
The Delhi Police bust of a pan-India cybercrime gang is evidence of the increasing reach and audacity of cyber crooks from one corner of India to another. From sextortion and social engineering to financial fraud and identity theft on the web, the bust demonstrates how deep and pervasive cybercrime gangs have become. It is also a reminder that anyone can get entangled and that education, awareness, and early reporting are our best defence. With India's online presence expanding day by day, our collective cyber awareness must keep pace. The fight against cybercrime will not be won only by arrests, but through a national effort to secure our digital spaces.
References
- https://indianexpress.com/article/cities/delhi/delhi-police-cyber-crime-syndicate-10047218/
- https://www.thehindu.com/news/cities/Delhi/delhi-police-bust-pan-india-cybercrime-syndicate/article69652694.ece#:~:text=The%20Delhi%20police%20have%20dismantled,and%20an%20orchestrated%20sextortion%20racket.
- https://cybercrime.gov.in/
- https://www.ncrb.gov.in/
- https://economictimes.indiatimes.com/wealth/save/online-scams-are-on-the-rise-learn-about-the-latest-tricks-fraudsters-are-using-to-identify-frauds-and-protect-yourself/articleshow/114162295.cms?from=mdr

Introduction
In the digital realm of social media, Meta Platforms, the driving force behind Facebook and Instagram, faces intense scrutiny following The Wall Street Journal's investigative report. This exploration delves deeper into critical issues surrounding child safety on these widespread platforms, unravelling algorithmic intricacies, enforcement dilemmas, and the ethical maze surrounding monetisation features. Instances of "parent-managed minor accounts" leveraging Meta's subscription tools to monetise content featuring young individuals have raised eyebrows. While skirting the line of legality, this practice prompts concerns due to its potential appeal to adults and the associated inappropriate interactions. It's a nuanced issue demanding nuanced solutions.
Failed Algorithms
The very heartbeat of Meta's digital ecosystem, its algorithms, has come under intense scrutiny. These algorithms, designed to curate and deliver content, were found to actively promoting accounts featuring explicit content to users with known pedophilic interests. The revelation sparks a crucial conversation about the ethical responsibilities tied to the algorithms shaping our digital experiences. Striking the right balance between personalised content delivery and safeguarding users is a delicate task.
While algorithms play a pivotal role in tailoring content to users' preferences, Meta needs to reevaluate the algorithms to ensure they don't inadvertently promote inappropriate content. Stricter checks and balances within the algorithmic framework can help prevent the inadvertent amplification of content that may exploit or endanger minors.
Major Enforcement Challenges
Meta's enforcement challenges have come to light as previously banned parent-run accounts resurrect, gaining official verification and accumulating large followings. The struggle to remove associated backup profiles adds layers to concerns about the effectiveness of Meta's enforcement mechanisms. It underscores the need for a robust system capable of swift and thorough actions against policy violators.
To enhance enforcement mechanisms, Meta should invest in advanced content detection tools and employ a dedicated team for consistent monitoring. This proactive approach can mitigate the risks associated with inappropriate content and reinforce a safer online environment for all users.
The financial dynamics of Meta's ecosystem expose concerns about the exploitation of videos that are eligible for cash gifts from followers. The decision to expand the subscription feature before implementing adequate safety measures poses ethical questions. Prioritising financial gains over user safety risks tarnishing the platform's reputation and trustworthiness. A re-evaluation of this strategy is crucial for maintaining a healthy and secure online environment.
To address safety concerns tied to monetisation features, Meta should consider implementing stricter eligibility criteria for content creators. Verifying the legitimacy and appropriateness of content before allowing it to be monetised can act as a preventive measure against the exploitation of the system.
Meta's Response
In the aftermath of the revelations, Meta's spokesperson, Andy Stone, took centre stage to defend the company's actions. Stone emphasised ongoing efforts to enhance safety measures, asserting Meta's commitment to rectifying the situation. However, critics argue that Meta's response lacks the decisive actions required to align with industry standards observed on other platforms. The debate continues over the delicate balance between user safety and the pursuit of financial gain. A more transparent and accountable approach to addressing these concerns is imperative.
To rebuild trust and credibility, Meta needs to implement concrete and visible changes. This includes transparent communication about the steps taken to address the identified issues, continuous updates on progress, and a commitment to a user-centric approach that prioritises safety over financial interests.
The formation of a task force in June 2023 was a commendable step to tackle child sexualisation on the platform. However, the effectiveness of these efforts remains limited. Persistent challenges in detecting and preventing potential child safety hazards underscore the need for continuous improvement. Legislative scrutiny adds an extra layer of pressure, emphasising the urgency for Meta to enhance its strategies for user protection.
To overcome ongoing challenges, Meta should collaborate with external child safety organisations, experts, and regulators. Open dialogues and partnerships can provide valuable insights and recommendations, fostering a collaborative approach to creating a safer online environment.
Drawing a parallel with competitors such as Patreon and OnlyFans reveals stark differences in child safety practices. While Meta grapples with its challenges, these platforms maintain stringent policies against certain content involving minors. This comparison underscores the need for universal industry standards to safeguard minors effectively. Collaborative efforts within the industry to establish and adhere to such standards can contribute to a safer digital environment for all.
To align with industry standards, Meta should actively participate in cross-industry collaborations and adopt best practices from platforms with successful child safety measures. This collaborative approach ensures a unified effort to protect users across various digital platforms.
Conclusion
Navigating the intricate landscape of child safety concerns on Meta Platforms demands a nuanced and comprehensive approach. The identified algorithmic failures, enforcement challenges, and controversies surrounding monetisation features underscore the urgency for Meta to reassess and fortify its commitment to being a responsible digital space. As the platform faces this critical examination, it has an opportunity to not only rectify the existing issues but to set a precedent for ethical and secure social media engagement.
This comprehensive exploration aims not only to shed light on the existing issues but also to provide a roadmap for Meta Platforms to evolve into a safer and more responsible digital space. The responsibility lies not just in acknowledging shortcomings but in actively working towards solutions that prioritise the well-being of its users.
References
- https://timesofindia.indiatimes.com/gadgets-news/instagram-facebook-prioritised-money-over-child-safety-claims-report/articleshow/107952778.cms
- https://www.adweek.com/blognetwork/meta-staff-found-instagram-tool-enabled-child-exploitation-the-company-pressed-ahead-anyway/107604/
- https://www.tbsnews.net/tech/meta-staff-found-instagram-subscription-tool-facilitated-child-exploitation-yet-company

Introduction
We consume news from various sources such as news channels, social media platforms and the Internet etc. In the age of the Internet and social media, the concern of misinformation has become a common issue as there is widespread misinformation or fake news on the Internet and social media platforms.
Misinformation on social media platforms
The wide availability of user-provided content on online social media platforms facilitates the spread of misinformation. With the vast population on social media platforms, the information gets viral and spreads all over the internet. It has become a serious concern as such misinformation, including rumours, morphed images, unverified information, fake news, and planted stories, spread easily on the internet, leading to severe consequences such as public riots, lynching, communal tensions, misconception about facts, defamation etc.
Platform-centric measures to mitigate the spread of misinformation
- Google introduced the ‘About this result’ feature’. This allows the users to help with better understand the search results and websites at a glance.
- During the covid-19 pandemic, there were huge cases of misinformation being shared. Google, in April 2020, invested $6.5 million in funding to fact-checkers and non-profits fighting misinformation around the world, including a check on information related to coronavirus or on issues related to the treatment, prevention, and transmission of Covid-19.
- YouTube also have its Medical Misinformation Policy which prevents the spread of information or content which is in contravention of the World Health Organization (WHO) or local health authorities.
- At the time of the Covid-19 pandemic, major social media platforms such as Facebook and Instagram have started showing awareness pop-ups which connected people to information directly from the WHO and regional authorities.
- WhatsApp has a limit on the number of times a WhatsApp message can be forwarded to prevent the spread of fake news. And also shows on top of the message that it is forwarded many times. WhatsApp has also partnered with fact-checking organisations to make sure to have access to accurate information.
- On Instagram as well, when content has been rated as false or partly false, Instagram either removes it or reduces its distribution by reducing its visibility in Feeds.
Fight Against Misinformation
Misinformation is rampant all across the world, and the same needs to be addressed at the earliest. Multiple developed nations have synergised with tech bases companies to address this issue, and with the increasing penetration of social media and the internet, this remains a global issue. Big tech companies such as Meta and Google have undertaken various initiatives globally to address this issue. Google has taken up the initiative to address this issue in India and, in collaboration with Civil Society Organisations, multiple avenues for mass-scale awareness and upskilling campaigns have been piloted to make an impact on the ground.
How to prevent the spread of misinformation?
Conclusion
In the digital media space, there is a widespread of misinformative content and information. Platforms like Google and other social media platforms have taken proactive steps to prevent the spread of misinformation. Users should also act responsibly while sharing any information. Hence creating a safe digital environment for everyone.


