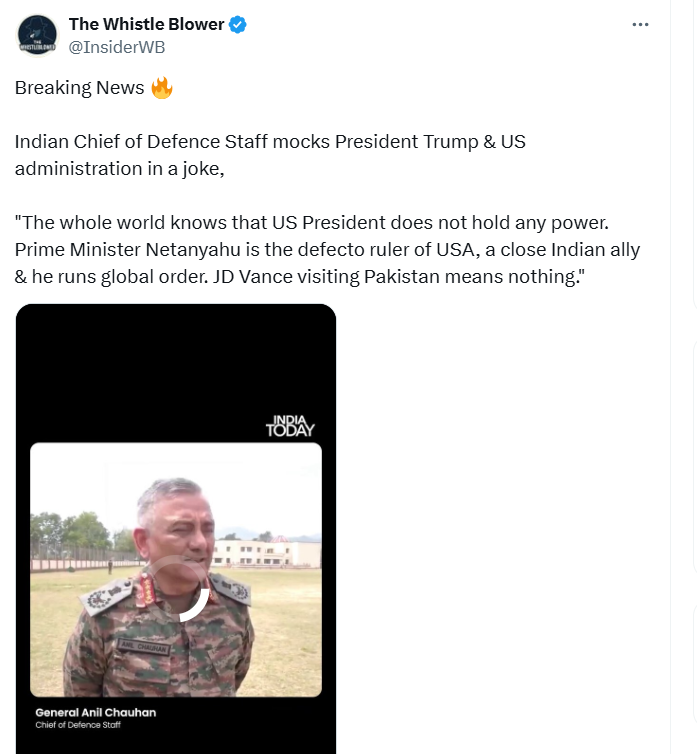
#FactCheck - Misleading Video Allegedly Depicting Trampling of Indian Tri-colour in Kerala or Tamil Nadu Circulates on Social Media
Executive Summary:
The video that allegedly showed cars running into an Indian flag while Pakistan flags flying in the air in Indian states, went viral on social media but it has been established to be misleading. The video posted is neither from Kerala nor Tamil Nadu as claimed, instead from Karachi, Pakistan. There are specific details like the shop's name, Pakistani flags, car’s number plate, geolocation analyses that locate where the video comes from. The false information underscores the importance of verifying information before sharing it.


Claims:
A video circulating on social media shows cars trampling the Indian Tricolour painted on a road, as Pakistani flags are raised in pride, with the incident allegedly taking place in Tamil Nadu or Kerala.


Fact Check:
Upon receiving the post we closely watched the video, and found several signs that indicated the video was from Pakistan but not from any place in India.
We divided the video into keyframes and found a shop name near the road.
We enhanced the image quality to see the shop name clearly.


We can see that it’s written as ‘Sanam’, also we can see Pakistan flags waving on the road. Taking a cue from this we did some keyword searches with the shop name. We found some shops with the name and one of the shop's name ‘Sanam Boutique’ located in Karachi, Pakistan, was found to be similar when analyzed using geospatial Techniques.



We also found a similar structure of the building while geolocating the place with the viral video.


Additional confirmation of the place is the car’s number plate found in the keyframes of the video.

We found a website that shows the details of the number Plate in Karachi, Pakistan.

Upon thorough investigation, it was found that the location in the viral video is from Karachi, Pakistan, but not from Kerala or Tamil Nadu as claimed by different users in Social Media. Hence, the claim made is false and misleading.
Conclusion:
The video circulating on social media, claiming to show cars trampling the Indian Tricolour on a road while Pakistani flags are waved, does not depict an incident in Kerala or Tamil Nadu as claimed. By fact-checking methodologies, it has been confirmed now that the location in the video is actually from Karachi, Pakistan. The misrepresentation shows the importance of verifying the source of any information before sharing it on social media to prevent the spread of false narratives.
- Claim: A video shows cars trampling the Indian Tricolour painted on a road, as Pakistani flags are raised in pride, taking place in Tamil Nadu or Kerala.
- Claimed on: X (Formerly known as Twitter)
- Fact Check: Fake & Misleading