#FactCheck - AI-Generated Video Falsely Shared as ‘Multi-Hooded Snake’ Sighting in Vrindavan
A video is being widely shared on social media showing devotees seated in a boat appearing stunned as a massive, multi-hooded snake—resembling the mythical Sheshnag—suddenly emerges from the middle of a water body.
The video captures visible panic and astonishment among the devotees. Social media users are sharing the clip claiming that it is from Vrindavan, with some portraying the sight as a divine or supernatural event. However, research conducted by the Cyber Peace Foundation found the viral claim to be false. Our research revealed that the video is not authentic and has been generated using artificial intelligence (AI).
Claim
On January 17, 2026, a user shared the viral video on Instagram with the caption suggesting that God had appeared again in the age of Kalyug. The post claims that a terrifying video from Vrindavan has surfaced in which devotees sitting in a boat were shocked to see a massive multi-hooded snake emerge from the water. The caption further states that devotees are hailing the creature as an incarnation of Sheshnag or Vasuki Nag, raising religious slogans and questioning whether the sight represents a divine sign. (The link to the post, its archive link, and screenshots are available.)
- https://www.instagram.com/reel/DTngN9FkoX0/?igsh=MTZvdTN1enI2NnFydA%3D%3D
- https://archive.ph/UuAqB
Fact Check:
Upon closely examining the viral video, we suspected that it might be AI-generated. To verify this, the video was scanned using the AI detection tool SIGHTENGINE, which indicated that the visual is 99 per cent AI-generated.
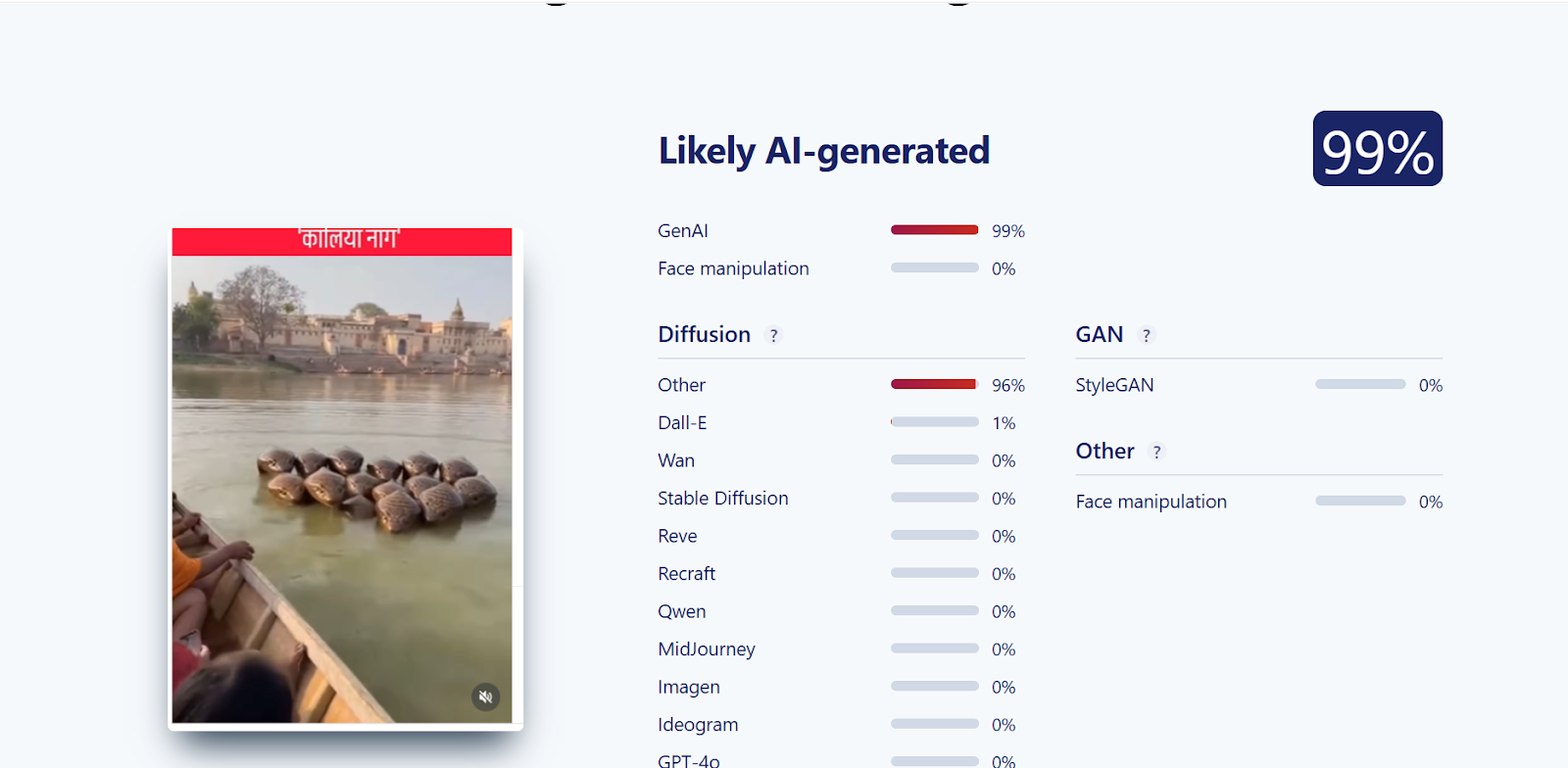
In the next step of the research , the video was analysed using another AI detection tool, HIVE Moderation. According to the results obtained, the video was found to be 62 per cent AI-generated.
Conclusion
Our research clearly establishes that the viral video claiming to show a multi-hooded snake in Vrindavan is not real. The clip has been created using artificial intelligence and is being falsely shared on social media with religious and sensational claims.
Related Blogs
.webp)
Executive Summary
Amid heightened tensions following Israel and US actions against Iran, a video is being widely shared on social media. The footage shows thick black smoke rising into the sky from a location, suggesting a major explosion or attack. However, research conducted by the CyberPeace found the viral claim to be misleading. Our research revealed that the video is not recent and has no connection to the current Israel-Iran tensions. In fact, the footage is nearly a year old and shows a fire at a casino in Mexico, now being shared out of context.
Claim
Users circulating the video claim that it shows an attack on Tel Aviv, Israel. On March 1, 2026, a user on X shared the clip with the caption, “Iran has drained the oil out of Tel Aviv,” implying a devastating retaliatory strike. (Post and archive links provided above.)

Fact Check:
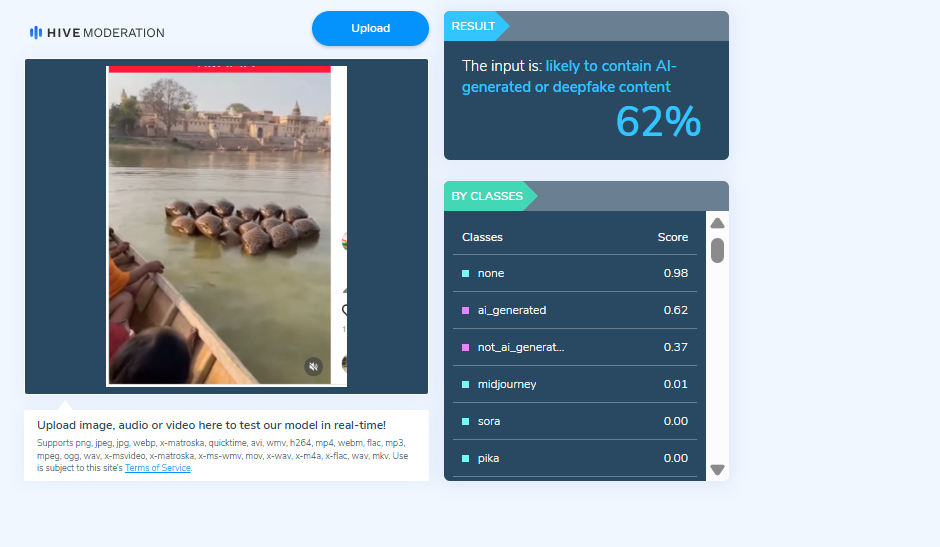
To verify the authenticity of the video, we extracted key frames and performed a reverse image search using Google Lens. During the search, we found the same visuals in a Spanish media report published on January 16, 2025. This confirmed that the video predates the ongoing geopolitical developments.
According to the report, the footage shows a fire at the Royal Park Casino located inside the Cinépolis plaza in Culiacán, Mexico. Local outlet Meganoticias Culiacán reported on X that the casino was “completely burned down.” The structure reportedly collapsed following the blaze, and emergency responders confirmed that several people were injured. Further keyword searches led us to the same footage on the official YouTube channel of Milenio, uploaded on January 17, 2025. The report clearly states that the fire occurred at the Royal Yacht Casino in Mexico and is unrelated to any recent military developments.

Conclusion
Evidence gathered during our research clearly establishes that the viral video is not related to any missile attack by Iran on Israel. The claim is false. The footage is from a fire incident at a casino in Mexico and is being misleadingly shared in the context of current international tensions, potentially creating unnecessary panic and confusion.
Introduction
In today’s digital world, data has emerged as the new currency that influences global politics, markets, and societies. Companies, governments, and tech behemoths aim to control data because it accords them influence and power. However, a fundamental challenge brought about by this increased reliance on data is how to strike a balance between privacy protection and innovation and utility.
In recognition of these dangers, more than 200 Nobel laureates, scientists, and world leaders have recently signed the Global Call for AI Red Lines. Governments are urged by this initiative to create legally binding international regulations on artificial intelligence by 2026. Its goal is to stop AI from going beyond moral and security bounds, particularly in areas like political manipulation, mass surveillance, cyberattacks, and dangers to democratic institutions.
One way to address the threat to privacy is through pseudonymization, which makes it possible to use data valuable for research and innovation by substituting personal identifiers for artificial ones. Pseudonymization thus directly advances the AI Red Lines initiative's mission of facilitating technological advancement while lowering the risks of data misuse and privacy violations.
The Red Lines of AI: Why do they matter?
The Global Call for AI Red Lines initiative represents a collective attempt to impose precaution before catastrophe, which was done with the objective of recognising the Red Lines in the use of AI tools. Thus, anything that unites the risks of using AI is due to the absence of global safeguards. Some of these Red Lines can be understood as;
- Cybersecurity breaches in the form of exposure of financial and personal data due to AI-driven hacking and surveillance.
- Occurrence of privacy invasions due to endless tracking.
- Generative AI can also help to create realistic fake content, undermining the trust of public discourses, leading to misinformation.
- Algorithmic amplification of polarising content can also threaten civic stability, leading to a demographic disruption.
Legal Frameworks and Regulatory Landscape
The regulations of Artificial Intelligence stand fragmented across jurisdictions, leaving significant loopholes aside. Some of the frameworks already provide partial guidance. The European Union’s Artificial Intelligence Act 2024 bans “unacceptable” AI practices, whereas the US-China Agreement also ensures that nuclear weapons remain under human, not machine-controlled. The UN General Assembly has adopted resolutions urging safe and ethical AI usage, with a binding and elusive global treaty.
On the front of data protection, the General Data Protection Regulations (GDPR) of EU offers a clear definition of Pseudonymisation under Article 4(5). It also describes a process where personal data is altered in a way that it cannot be attributed to an individual without additional information, which must be stored securely and separately. Importantly, pseudonymised data still qualifies as “personal data” under GDPR. However, India’s Digital Personal Data Protection Act (DPDP) 2023 adopts a similar stance. It does not explicitly define pseudonymisation in broad terms, such as “personal data” by including potentially reversible identifiers. According to Section 8(4) of the Act, companies are meant to adopt appropriate technical or organisational measures. International bodies and conventions like the OECD Principles on AI or the Council of Europe Convention 108+ emphasize accountability, transparency, and data minimisation. Collectively, these instruments point towards pseudonymization as a best practice, though interpretations of its scope differ.
Strategies for Corporate Implementation
For a company, pseudonymisation is not just about compliance, it is also a practical solution that offers measurable benefits. By pseudonymising data, businesses can get benefits, such as;
- Enhancing Privacy protection by masking identifiers like names or IDs by reducing the impact of data breaches.
- Preserving Data Utility, unlike having a full anonymisation, pseudonymisation also retains patterns that are essential for analytical innovation.
- Facilitating data sharing can allow organizations to collaborate with their partners and researchers while maintaining proper trust.
According to these benefits, competitive advantages get translated to clauses where customers find it more likely to trust organizations that prioritise data protection, while pseudonymisation further enables the firms to engage in cross-border collaboration without violating local data laws.
Balancing Privacy Rights and Data Utility
Balancing is a central dilemma; on one side lies the case of necessity over data utility, where companies, researchers and governments rely on large datasets to enhance the scale of AI innovation. On the other hand lies the question of the right to privacy, which is a non-negotiable principle protected under the international human rights law.
Pseudonymisation offers a practical compromise by enabling the use of sensitive data while reducing the privacy risks. Taking examples of different domains, such as healthcare, it allows the researchers to work with patient information without exposing identities, whereas in finance, it supports fraud detection without revealing the customer details.
Conclusion
The rapid rise of artificial intelligence has led to the outpacing of regulations, raising urgent questions related to safety, fairness and accountability. The global call for recognising the AI red lines is a bold step that looks in the direction of setting universal boundaries. Yet, alongside the remaining global treaties, practical safeguards are also needed. Pseudonymisation exemplifies such a safeguard, which is legally recognised under the GDPR and increasingly relevant in India’s DPDP Act. It balances the twin imperatives of privacy, protection, and data utility. For organizations, adopting pseudonymisation is not only about ensuring regulatory compliance, rather, it is also about building trust, ensuring resilience, and aligning with the broader ethical responsibilities in this digital age. As the future of AI is debatable, the guiding principles also need to be clear. By embedding techniques for preserving privacy, like pseudonymisation, into AI systems, we can take a significant step towards developing a sustainable, ethical and innovation-driven digital ecosystem.
References
https://www.techaheadcorp.com/blog/shadow-ai-the-risks-of-unregulated-ai-usage-in-enterprises/
https://planetmainframe.com/2024/11/the-risks-of-unregulated-ai-what-to-know/
https://cepr.org/voxeu/columns/dangers-unregulated-artificial-intelligence
https://www.forbes.com/sites/bernardmarr/2023/06/02/the-15-biggest-risks-of-artificial-intelligence/
%20(1).webp)
Disclaimer:
The information is based on claims made by threat actors and does not imply confirmation of the breach, by CyberPeace. CyberPeace includes this detail solely to provide factual transparency and does not condone any unlawful activities. This information is shared only for research purposes and to spread awareness. CyberPeace encourages individuals and organizations to adopt proactive cybersecurity measures to protect against potential threats.
🚨 Data Breach Alert ⚠️:
Recently The Research Wing of CyberPeace and Autobot Infosec have come across a claim on a threat actor’s dark web website alleging a data breach involving 637k+ records from Federal Bank. According to the threat actor’s claim, the data allegedly includes sensitive details such as-
- 🧑Customer Name
- 🆔Customer ID
- 🏠 Customer Address
- 🎂 Date of Birth
- 🔢 Age
- 🚻 Gender
- 📞Mobile Number
- 🪪 PAN Number
- 🚘 Driving License Number
- 🛂 Passport Number
- 🔑 UID Number
- 🗳️ Voter ID Information
The alleged data was initially discovered on a dark web website, where the threat actors allegedly claimed to be offering the breached information for sale. Following their announcement of the breach, a portion of the data was reportedly published on December 27, 2024. A few days later, the full dataset was allegedly released on the same forum.
About the Threat Actor Group:
Bashe, a ransomware group that emerged in 2024, is claimed to have evolved from the LockBit ransomware group, previously operating under the names APT73 and Eraleig. The group employs data encryption combined with extortion tactics, threatening to release sensitive information if ransom demands are unmet. Their operations primarily target critical industries, including technology, healthcare, and finance, demonstrating a strategic focus on high-value sectors.

Breakdown of the Alleged Post by the Threat Actor:
- Target: Allegedly involves Customer’s Data of Federal Bank.
- Data Volume: Claimed breach includes 637,894 records.
- Data Fields: Threat actor claims the data contains sensitive information, including Customer name, Customer ID, Date of Birth, PAN Number, Age, Gender, Father Name, Spouse Name, Driving Licence, Passport Number, UID Number, Voter ID, District, Zip Code, Home Address, Mailing Address, State etc.
Analysis:
The analysis of the alleged data breach highlights the states purportedly most impacted, along with insights into the affected age groups, gender distribution, and other key insights associated with the compromised data. This evaluation aims to provide a clearer understanding of the claimed breach's scope and its potential demographic and geographic impact.
Top States Impacted:
As per the alleged breached data, Tamil Nadu has the highest number of affected customers, accounting for a significant 34.49% of the total breach. Karnataka follows closely with 26.89%, indicating a substantial number of individuals affected in the state. In contrast states such as Uttar Pradesh, Haryana, Delhi, and Rajasthan report minimal impact, with each state having less than 1% of affected customers. Gujarat records 3.70% of the breach, with a sharp drop in affected numbers from other states, highlighting a significant disparity in the extent of the breach across regions.

Impacted Age Range Statistics:
The alleged data breach has predominantly impacted customers in the 31-40 years age group, which constitutes the largest segment at 35.80% of the affected individuals. Following this, the 21-30 years age group also shows significant impact, comprising 27.72% of those affected. The 41-50 years age group accounts for 20.55% of the impacted population, while individuals aged 50 and above represent 12.68%. In contrast, the 0-20 years age group is the least affected, with only 3.24% of customers falling into this category.

Gender Wise Statistics:
The alleged data breach has predominantly impacted male customers, who constitute the majority at 74.05% of the affected individuals. Female customers account for 23.18%, while a smaller segment, categorized as "Others," constitutes 2.77%.

The alleged dataset from the threat actors indicated that a significant portion of customers' personal identification data was compromised. This includes sensitive information such as driving licenses, passport numbers, UID numbers, voter IDs, and PAN numbers.
Significance of the Allegations:
Though the claims have not been independently verified at our end it underscores the rising risks of cyberattacks and data breaches, especially in the financial and banking sectors. If true, the exposure of such sensitive information could lead to financial fraud, identity theft, and severe reputational damage for individuals and organizations alike.
CyberPeace Advisory:
CyberPeace emphasizes the importance of vigilance and proactive measures to address cybersecurity risks:
- Monitor Your Accounts: Keep a close eye on financial and email accounts for any suspicious activity.
- Update Passwords: Change your passwords immediately and enable Multi Factor Authentication(MFA) wherever possible.
- Beware of Phishing Attacks: Threat actors may exploit the leaked data to craft targeted phishing scams. Do not click on unsolicited links or share sensitive details over email or phone.
- For Organizations: Strengthen data protection mechanisms, regularly audit security infrastructure, and respond swiftly to emerging threats.
- Report: For more assistance or to report cyber incidents, visit https://cybercrime.gov.in or contact our helpline team at helpline@cyberpeace.net.
We advise affected parties and the broader public to stay alert and take necessary precautions. CyberPeace remains committed to raising awareness about cybersecurity threats and advocating for better protection mechanisms. We urge all stakeholders to investigate the claims and ensure appropriate steps are taken to protect the impacted data, if the breach is confirmed. Our Research Wing is actively observing the situation and we aim to collaborate with the stakeholders and relevant agencies to mitigate the impact.
Stay Vigilant! Stay CyberPeaceful.


