#FactCheck - Fake Video Uses AI Voice to Falsely Attribute Remarks on Prasidh Krishna to Virat Kohli
A video circulating widely on social media claims that Indian cricketer Virat Kohli made a sarcastic remark about fast bowler Prasidh Krishna ahead of the New Zealand series. In the clip, Kohli is allegedly heard saying that he expected to be the top scorer of the series, but lost all hope after seeing Prasidh Krishna’s name in the squad.
Users sharing the video claim that Kohli publicly commented on Prasidh Krishna in this manner.
Research by the CyberPeace Foundation has found the viral claim to be false. Our probe revealed that the viral clip has been digitally manipulated. The video is originally from a 2024 advertisement featuring Virat Kohli, in which his voice has been altered using deepfake (AI-generated) technology and falsely presented with a misleading narrative.
Claim
The video was shared on Instagram on January 6, 2025, with users claiming that Kohli made the remark after the New Zealand squad was announced. The post included the altered audio suggesting Kohli’s disappointment over Prasidh Krishna’s selection. Link, archive link

Fact Check:
To verify the claim, we extracted key frames from the viral video and conducted a Google Reverse Image Search. This led us to the original video posted by Virat Kohli himself on X (formerly Twitter) on April 15, 2024. The original clip was part of a brand advertisement, and no such statement about the New Zealand series or Prasidh Krishna was made in it. Link and Screenshot

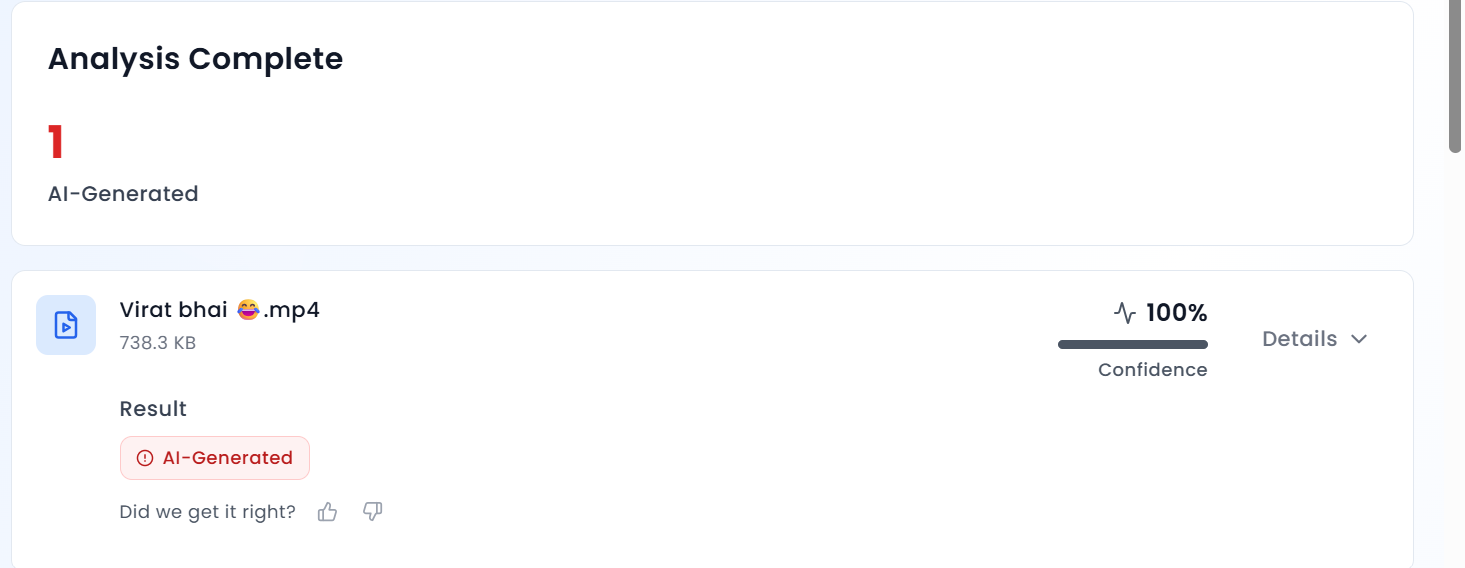
A close review of the viral clip raised suspicions due to the unnatural tone and inconsistencies in Kohli’s voice. To confirm this, we analysed the video using the AI detection tool Aurigin AI. The tool’s results showed that the audio in the viral clip is 100 percent AI-generated, confirming that Kohli’s voice was artificially manipulated.
Conclusion
The CyberPeace Foundation’s research confirms that the viral video claiming Virat Kohli mocked Prasidh Krishna is fake and misleading. The clip is taken from an old advertisement and has been doctored using deepfake technology to alter Kohli’s voice. The video is being circulated on social media with a false claim, and Virat Kohli has made no such statement regarding the New Zealand series or Prasidh Krishna.
Related Blogs
.webp)
The Digital Covenant: Aligning Communication with SDG Goals
“Rethinking Communication, Cyber Responsibility, and Sustainability in a Connected World”
Introduction
It is rightly said by Antonio Guterres, United Nations Secretary General, “Everyone should be able to express themselves freely without fear of attack. Everyone should be able to access a range of views and information sources.” In 2024, when the Global Alliance for PR and Communication Management asserted that it aligns with the era of digital transformation, where technology is moving at terminal velocity and bringing various risks and threats, it called on the global leaders and stakeholders to proclaim ‘Responsible Communication’ as the 18th Sustainable Development Goal (SDG). On May 17th, as we celebrate World Telecommunication and Information Society Day (WTISD) 2025, we must align our personal, professional, and virtual spaces with a safe and sustainable information age.
In terms of digital growth, it is indubitable that India is growing at a brisk pace consistently in alignment with its South Asian and Western counterparts and has incorporated international covenants on digital personal data and cyber crimes within its domestic regime.
UN Global Principles for Information Integrity
The United Nations has displayed its constant commitment to the achievement of the seventeen SDGs that were adopted at the United Nations Conference in 2012 in Rio de Janeiro. It recognises that you cannot isolate the digital transformation, technology, and digitisation from other areas that are included within the SDGs, such as health, education, and poverty. The UN released Policy Brief 8 in June 2023 by the UN Secretary-General that seeks to empirically derive data on the threats posed to information integrity and then come up with norms that help guide the member states, the digital platforms, and other stakeholders. The norms must be in conformity with the right to freedom of opinion and expression and the right to information access.
In line with its agenda, it has formulated Global Principles of Information Integrity, which include “Societal Trust and Resilience”, “Healthy Incentives”, “Public Empowerment”, “Independent, Free and Pluralistic Media” and “Transparency and Research”. The principles recognise the harm caused by hatred, misinformation, and disinformation propagated by the misuse of advances in Artificial Intelligence Technology (AI).
Breaking the Binary: Bridging the Gender Digital Divide
The reflection of how far we have come and how far we have to go can be deciphered with a single sentence, i.e., using digital technologies to promote gender equality. This can be seen both as a paradox and a pressing call to action. As we celebrate WTISD 2025, the day highlights the fundamental role of Information and Communication Technologies (ICTs) in accelerating progress and bringing those not included in this digital transformation to become a part of this change, especially the female population that remains isolated from mainstream growth. As per the data given by ITU, “Out of the world population, 70 per cent of men are using the internet, compared with 65 per cent of women.”
This exclusion is not merely a technical gap but a societal and economic chasm, reinforcing existing inequalities. By including such an important goal in the theme of this day, it marks a critical moment towards the formation of gender-sensitive digital policies, promoting digital literacy among women and girls, and ensuring safe, affordable, and meaningful connectivity. We can explore the future potential where technology is the true instrument for gender parity, not a mirror of old hierarchies.
India and its courts have time and again proven their commitment to cultivating digital transformation as an inherent strength to bridge this digital divide, and the recent judgement where the court declared the right to digital access an intrinsic part of the right to life and liberty is a single instance among many.
CyberPeace Resolution on World Telecommunication and Information Society Day
CyberPeace is actively bridging the gap between digital safety and sustainable development through its initiatives, aligning with the principles of the Sustainable Development Goals (SDGs). The ‘CyberPeace Corps’ empowers communities by fostering cyber hygiene awareness and building digital resilience. The ‘CyberPeace Initiative’, a project with Google.org, tackles digital misinformation, promoting informed online engagement. Additionally, Digital Shakti, now in its fifth phase, empowers women by enhancing their digital literacy and safety. These are just a few of the many impactful initiatives by CyberPeace, aimed at creating a safer and more inclusive digital future. Together, we are spreading awareness and strengthening the foundation for a safer and more inclusive digital future and promoting responsible tech use. Let us be resolute on this World Telecommunication and Information Society Day for “Clean Data. Safe Clicks. Stronger Future. Pledge to Cyber Hygiene Today!”
References

Introduction
Since users are now constantly retrieving critical data on their mobile devices, fraudsters are now focusing on these devices. App-based, network-based, and device-based vulnerabilities are the three main ways of attacking that Mobile Endpoint Security names as mobile threats. Composed of the following features: program monitoring and risk, connection privacy and safety, psychological anomaly and reconfiguration recognition, and evaluation of vulnerabilities and management, this is how Gartner describes Mobile Threat Defense (MTD).
The widespread adoption and prevalence of cell phones among consumers worldwide have significantly increased in recent years. Users of these operating system-specific devices can install a wide range of software, or "apps," from online marketplaces like Google Play and the Apple App Store. The applications described above are the lifeblood of cell phones; they improve users' daily lives and augment the devices' performance. The app marketplaces let users quickly search for and install new programs, but certain malicious apps/links/websites can also be the origin of malware hidden among legitimate apps. These days, there are many different security issues and malevolent attacks that might affect mobile devices.
Unveiling Malware Landscape
The word "malware" refers to a comprehensive category of spyware intended to infiltrate networks, steal confidential data, cause disruptions, or grant illegal access. Malware can take many forms, such as Trojan horses, worms, ransomware, infections, spyware, and adware. Because each type has distinct goals and features, security specialists face a complex problem. Malware is a serious risk to both people and businesses. Security incidents, monetary losses, harm to one's credibility, and legal repercussions are possible outcomes. Understanding malware's inner workings is essential to defend against it effectively. Malware analysis is helpful in this situation. The practice of deconstructing and analysing dangerous software to comprehend its behaviour, operation, and consequences is known as malware analysis.Major threats targeting mobile phones
Viruses: Viruses are self-renewing programs that can steal data, launch denial of service assaults, or enact ransomware strikes. They spread by altering other software applications, adding malicious code, and running it on the target's device. Computer systems all over the world are still infected with viruses, which attack different operating systems like Mac and Microsoft Windows, even though there is a wealth of antiviral programs obtainable to mitigate their impacts.
Worms: Infections are independent apps that propagate quickly and carry out payloads—such as file deletion or the creation of botnets—to harm computers. Worms, in contrast to viruses, usually harm a computer system, even if it's just through bandwidth use. By taking advantage of holes in security or other vulnerabilities on the target computer, they spread throughout computer networks.
Ransomware: It causes serious commercial and organisational harm to people and businesses by encrypting data and demanding payment to unlock it. The daily operations of the victim organisation are somewhat disrupted, and they need to pay a ransom to get them back. It is not certain, though, that the financial transaction will be successful or that they will receive a working translation key.
Adware: It can be controlled via notification restrictions or ad-blockers, tracks user activities and delivers unsolicited advertisements. Adware poses concerns to users' privacy even though it's not always malevolent since the information it collects is frequently combined with information gathered from other places and used to build user profiles without their permission or knowledge.
Spyware: It can proliferate via malicious software or authentic software downloads, taking advantage of confidential data. This kind of spyware gathers data on users' actions without their authorisation or agreement, including:Internet activityBanking login credentialsPasswordsPersonally Identifiable Information (PII)
Navigating the Mobile Security Landscape
App-Centric Development: Regarding mobile security, app-centric protections are a crucial area of focus. Application authorisations should be regularly reviewed and adjusted to guarantee that applications only access the knowledge that is essential and to lower the probability of data misuse. Users can limit hazards and have greater oversight over their confidentiality by closely monitoring these settings. Installing trustworthy mobile security apps also adds another line of protection. With capabilities like app analysis, real-time protection, and antivirus scanning, these speciality apps strengthen your gadget's protection against malware and other harmful activity.
Network Security: Setting priorities for secure communication procedures is crucial for safeguarding confidential data and thwarting conceivable dangers in mobile security. Avoiding unprotected public Wi-Fi networks is essential since they may be vulnerable to cyberattacks. To lessen the chance of unwelcome entry and data surveillance, promote the usage of reliable, password-protected networks instead. Furthermore, by encrypting data transfer, Virtual Private Networks (VPNs) provide additional protection and make it more difficult for malevolent actors to corrupt information. To further improve security, avoid using public Wi-Fi for essential transactions and hold off until a secure network is available. Users can strengthen their handheld gadgets against possible privacy breaches by implementing these practices, which can dramatically lower the risk of data eavesdropping and illegal access.
Constant development: Maintaining a robust mobile security approach requires a dedication to constant development. Adopt a proactive stance by continuously improving and modifying your security protocols. By following up on recurring outreach and awareness campaigns, you can stay updated about new hazards. Because cybersecurity is a dynamic field, maintaining one step ahead and utilising emerging technologies is essential. Stay updated with security changes, implement the newest safeguards, and incorporate new industry standard procedures into your plan. This dedication to ongoing development creates a flexible barrier, strengthening your resistance to constantly evolving mobile security threats.
Threat emergency preparedness: To start, familiarise yourself with the ever-changing terrain associated with mobile dangers to security. Keep updated on new threats including malware, phishing, and illegal access.
Sturdy Device Management: Put in place a thorough approach to device management. This includes frequent upgrades, safe locking systems, and additional safeguarding capabilities like remote surveillance and erasing.
Customer Alertness: Emphasise proper online conduct and acquaint yourself and your team with potential hazards, such as phishing efforts.
Dynamic Measures for a Robust Wireless Safety Plan
In the dynamic field of mobile assurances, taking a proactive strategy is critical. To strengthen safeguards, thoroughly research common risks like malware, phishing, and illegal access. Establish a strong device management strategy that includes frequent upgrades, safe locking mechanisms, and remote monitoring and deletion capabilities for added security.
Promoting user awareness by educating people so they can identify and block any hazards, especially regarding phishing attempts. Reduce the dangers of data eavesdropping and illegal access by emphasising safe communication practices, using Virtual Private Networks (VPNs), and avoiding public Wi-Fi for essential transactions.
Pay close attention to app-centric integrity by periodically checking and modifying entitlements. Downloading trustworthy mobile security apps skilled at thwarting malware and other unwanted activity will enhance your smartphone's defenses. Lastly, create an atmosphere of continuous development by keeping up with new threats and utilising developing technology to make your handheld security plan more resilient overall.
Conclusion
Mobile privacy threats grow as portable electronics become increasingly integrated into daily activities. Effective defense requires knowledge of the various types of malware, such as worms, ransomware, adware, and spyware. Tools for Mobile Threat Defense, which prioritise vulnerability assessment, management, anomaly detection, connection privacy, and program monitoring, are essential. App-centric development, secure networking procedures, ongoing enhancement, threat readiness, strong device control, and user comprehension are all components of a complete mobile security strategy. People, as well as organisations, can strengthen their defenses against changing mobile security threats by implementing dynamic measures and maintaining vigilance, thereby guaranteeing safe and resilient mobile surrounding.
References
https://www.titanfile.com/blog/types-of-computer-malware/
https://www.simplilearn.com/what-is-a-trojan-malware-article
https://www.linkedin.com/pulse/latest-anti-analysis-tactics-guloader-malware-revealed-ukhxc/?trk=article-ssr-frontend-pulse_more-articles_related-content-card

Executive Summary
A video is going viral on social media showing a massive building engulfed in flames and collapsing into debris. It is being widely claimed that Iran launched a powerful attack that destroyed Israel’s army headquarters. However, research by CyberPeace reveals that this claim is misleading. The viral video is AI-generated and has no connection to any real-world event.
Claim
An X (formerly Twitter) user shared the viral video with the caption: “Iran has targeted Israel’s army headquarters. It seems Israel’s dream of becoming ‘Greater Israel’ will remain unfulfilled.”
Post link:
- https://x.com/KAMESHKUMAR96/status/2039009484069368083
Archived version:
- https://archive.ph/HKXkK
- https://x.com/KAMESHKUMAR96/status/2039009484069368083
- https://archive.ph/HKXkK

Similar videos have also been shared by other users on social media:
Fact Check
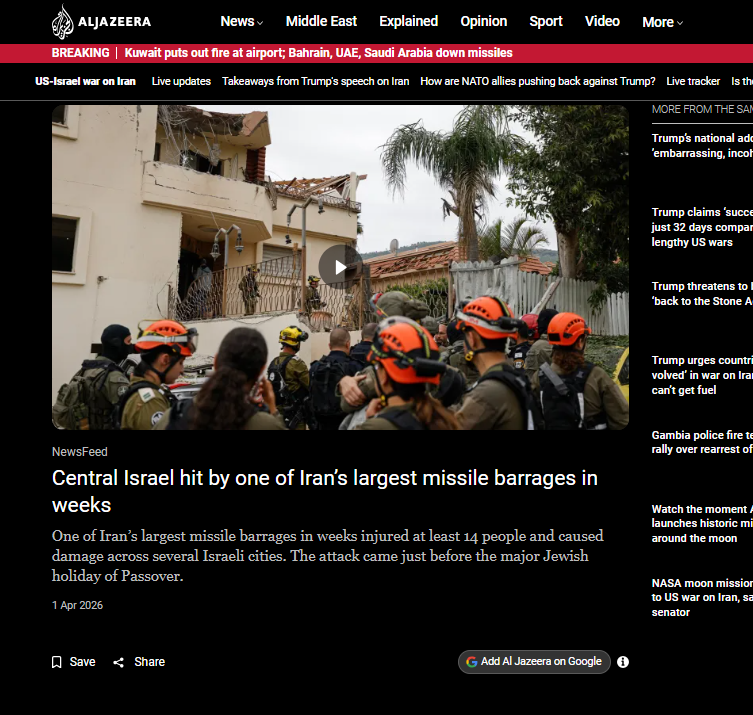
To verify the claim, we extracted keyframes from the viral video and conducted a reverse image search. During this process, we found several credible media reports confirming that Iran has carried out drone and missile attacks on Israel and the Gulf regions in recent times. However, none of these reports featured the viral video, indicating that it is not authentic footage.
- https://www.youtube.com/watch?v=fxDBX90bYng
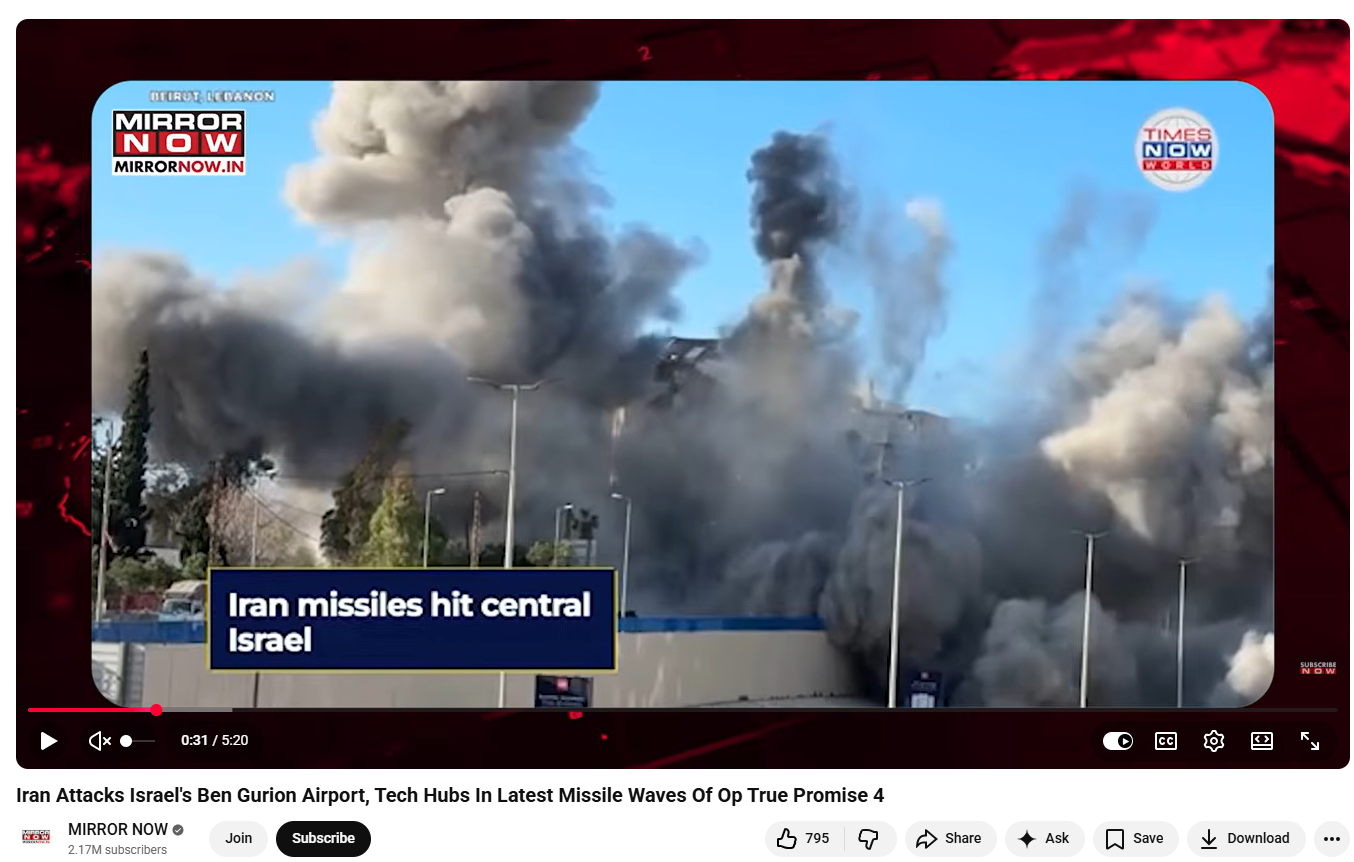
A closer examination of the video revealed multiple visual inconsistencies commonly associated with AI-generated content. For instance, a building on the left side appears to bend and collapse in a rubber-like manner—something that is physically unrealistic for structures made of concrete and steel. Additionally, the smoke and flames appear unnatural and lack realistic dynamics.
To further verify, we analyzed the video using the AI detection tool Hive Moderation, which classified it as 99.9% AI-generated.
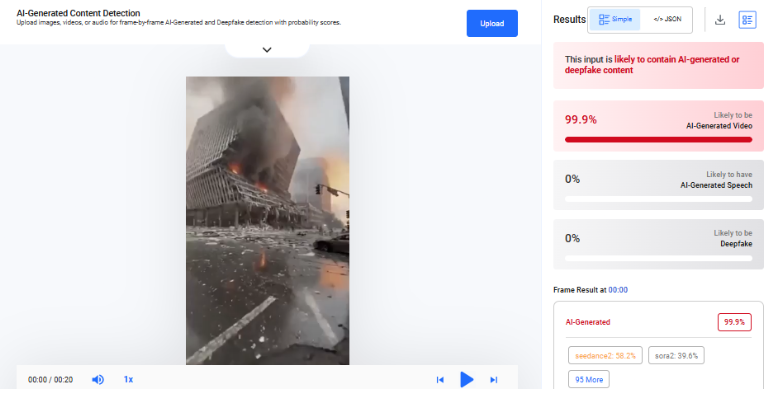
We also tested the video using the Deepfake-o-Meter platform.The AVSRDD (2025) model detected it as 99.5% AI-generated

Conclusion
Our research clearly establishes that the viral video claiming Iran destroyed Israel’s army headquarters is false and misleading. The footage does not appear in any credible news coverage of recent attacks, which strongly indicates that it is not real. Moreover, multiple AI detection tools consistently classify the video as artificially generated, with extremely high probability scores. Visual anomalies in the clip further support this finding.


