#FactCheck: AI Video made by Pakistan which says they launched a cross-border airstrike on India's Udhampur Airbase
Executive Summary:
A social media video claims that India's Udhampur Air Force Station was destroyed by Pakistan's JF-17 fighter jets. According to official sources, the Udhampur base is still fully operational, and our research proves that the video was produced by artificial intelligence. The growing problem of AI-driven disinformation in the digital age is highlighted by this incident.

Claim:
A viral video alleges that Pakistan's JF-17 fighter jets successfully destroyed the Udhampur Air Force Base in India. The footage shows aircraft engulfed in flames, accompanied by narration claiming the base's destruction during recent cross-border hostilities.

Fact Check :
The Udhampur Air Force Station was destroyed by Pakistani JF-17 fighter jets, according to a recent viral video that has been shown to be completely untrue. The audio and visuals in the video have been conclusively identified as AI-generated based on a thorough analysis using AI detection tools such as Hive Moderation. The footage was found to contain synthetic elements by Hive Moderation, confirming that the images were altered to deceive viewers. Further undermining the untrue claims in the video is the Press Information Bureau (PIB) of India, which has clearly declared that the Udhampur Airbase is still fully operational and has not been the scene of any such attack.

Our analysis of recent disinformation campaigns highlights the growing concern that AI-generated content is being weaponized to spread misinformation and incite panic, which is highlighted by the purposeful misattribution of the video to a military attack.
Conclusion:
It is untrue that the Udhampur Air Force Station was destroyed by Pakistan's JF-17 fighter jets. This claim is supported by an AI-generated video that presents irrelevant footage incorrectly. The Udhampur base is still intact and fully functional, according to official sources. This incident emphasizes how crucial it is to confirm information from reliable sources, particularly during periods of elevated geopolitical tension.
- Claim: Recent video footage shows destruction caused by Pakistani jets at the Udhampur Airbase.
- Claimed On: Social Media
- Fact Check: False and Misleading
Related Blogs

Introduction
Meta is the leader in social media platforms and has been successful in having a widespread network of users and services across global cyberspace. The corporate house has been responsible for revolutionizing messaging and connectivity since 2004. The platform has brought people closer together in terms of connectivity, however, being one of the most popular platforms is an issue as well. Popular platforms are mostly used by cyber criminals to gain unauthorised data or create chatrooms to maintain anonymity and prevent tracking. These bad actors often operate under fake names or accounts so that they are not caught. The platforms like Facebook and Instagram have been often in the headlines as portals where cybercriminals were operating and committing crimes.
To keep the data of the netizen safe and secure Paytm under first of its kind service is offering customers protection against cyber fraud through an insurance policy available for fraudulent mobile transactions up to Rs 10,000 for a premium of Rs 30. The cover ‘Paytm Payment Protect’ is provided through a group insurance policy issued by HDFC Ergo. The company said that the plan is being offered to increase the trust in digital payments, which will push up adoption.
Meta’s Cybersecurity
Meta has one of the best cyber security in the world but that diest mean that it cannot be breached. The social media giant is the most vulnerable platform in cases of data breaches as various third parties are also involved. As seen the in the case of Cambridge Analytica, a huge chunk of user data was available to influence the users in terms of elections. Meta needs to be ahead of the curve to have a safe and secure platform, for this Meta has deployed various AI and ML driven crawlers and software which work o keeping the platform safe for its users and simultaneously figure out which accounts may be used by bad actors and further removes the criminal accounts. The same is also supported by the keen participation of the user in terms of the reporting mechanism. Meta-Cyber provides visibility of all OT activities, observes continuously the PLC and SCADA for changes and configuration, and checks the authorization and its levels. Meta is also running various penetration and bug bounty programs to reduce vulnerabilities in their systems and applications, these testers are paid heavily depending upon the scope of the vulnerability they found.
CyberRoot Risk Investigation
Social media giant Meta has taken down over 40 accounts operated by an Indian firm CyberRoot Risk Analysis, allegedly involved in hack-for-hire services along with this Meta has taken down 900 fraudulently run accounts, these accounts are said to be operated from China by an unknown entity. CyberRoot Risk Analysis was responsible for sharing malware over the platform and used it to impersonate themselves just as their targets, i.e lawyers, doctors, entrepreneurs, and industries like – cosmetic surgery, real estate, investment firms, pharmaceutical, private equity firms, and environmental and anti-corruption activists. They would get in touch with such personalities and then share malware hidden in files which would often lead to data breaches subsequently leading to different types of cybercrimes.
Meta and its team is working tirelessly to eradicate the influence of such bad actors from their platforms, use of AI and Ml based tools have increased exponentially.
Paytm CyberFraud Cover
Paytm is offering customers protection against cyber fraud through an insurance policy available for fraudulent mobile transactions up to Rs 10,000 for a premium of Rs 30. The cover ‘Paytm Payment Protect’ is provided through a group insurance policy issued by HDFC Ergo. The company said that the plan is being offered to increase the trust in digital payments, which will push up adoption. The insurance cover protects transactions made through UPI across all apps and wallets. The insurance coverage has been obtained by One97 Communications, which operates under the Paytm brand.
The exponential increase in the use of digital payments during the pandemic has made more people susceptible to cyber fraud. While UPI has all the digital safeguards in place, most UPI-related frauds are undertaken by confidence tricksters who get their victims to authorise a transaction by passing collect requests as payments. There are also many fraudsters collecting payments by pretending to be merchants. These types of frauds have resulted in a loss of more than Rs 63 crores in the previous financial year. The issue of data insurance is new to India but is indeed the need of the hour, majority of netizens are unaware of the value of their data and hence remain ignorant towards data protection, such steps will result in safer data management and protection mechanisms, thus safeguarding the Indian cyberspace.
Conclusion
cyberspace is at a critical juncture in terms of data protection and privacy, with new legislation coming out on the same we can expect new and stronger policies to prevent cybercrimes and cyber-attacks. The efforts by tech giants like Meta need to gain more speed in terms of the efficiency of cyber safety of the platform and the user to make sure that the future of the platforms remains secured strongly. The concept of data insurance needs to be shared with netizens to increase awareness about the subject. The initiative by Paytm will be a monumental initiative as this will encourage more platforms and banks to commit towards coverage for cyber crimes. With the increasing cases of cybercrimes, such financial coverage has come as a light of hope and security for the netizens.
.webp)
Executive Summary
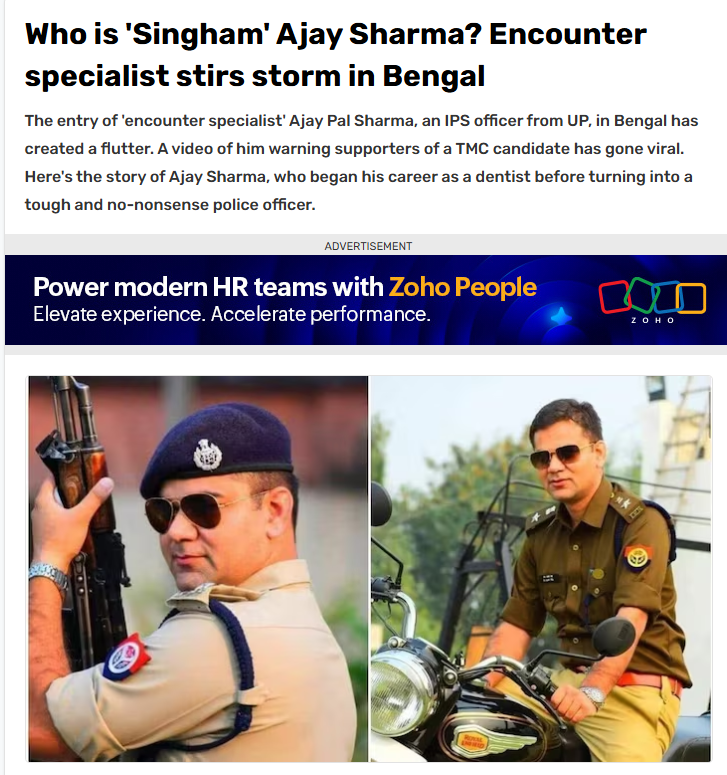
Ahead of the final phase of the West Bengal Assembly elections, a claim regarding Uttar Pradesh cadre IPS officer Ajay Pal Sharma began circulating widely on social media. Users claimed that Sharma was being sent to West Bengal on deputation for a period of five years. However, research conducted by CyberPeace Research Wing found the claim to be false. Sources close to the IPS officer confirmed that no such deputation order has been issued so far and that Ajay Pal Sharma is currently posted as Additional Commissioner in Prayagraj, Uttar Pradesh. Ajay Pal Sharma had earlier been deployed as a police observer during the West Bengal elections. During that period, a video of him warning Trinamool Congress candidate Jahangir Khan from the Falta constituency had gone viral on social media.
Claim
Several users on Facebook and X claimed that Ajay Pal Sharma had been transferred to West Bengal for five years under an administrative arrangement involving experienced officers from different states. One Facebook user wrote:“This decision has been taken under an administrative arrangement through which experienced officers are deployed in different states.”
- https://www.facebook.com/photo.php?fbid=818902764628152&set=a.296761956842238&type=3
- https://perma.cc/FD8Q-CF7L?type=standard

Fact Check
Our research found that the deputation claim is false. Ajay Pal Sharma is currently serving as Additional Commissioner in Prayagraj, a position he has held since 2025. Further scrutiny revealed that the claim appears to have originated from a parody account on X. On May 4, around 6 PM, the account @abdullah_0mar posted the claim regarding Sharma’s alleged five-year deputation to Bengal. However, in the comments section, the user later clarified that the post was intended as satire.

We also reviewed several news reports regarding Ajay Pal Sharma’s role during the West Bengal elections. Reports confirmed that the Election Commission had deployed him as a police observer in South 24 Parganas district during the polls. However, none of the reports mentioned any five-year transfer or deputation to West Bengal.
Conclusion
The viral claim is false. No official order has been issued regarding IPS officer Ajay Pal Sharma’s deputation to West Bengal for five years. Sources close to the officer confirmed that he continues to serve as Additional Commissioner in Prayagraj, Uttar Pradesh. Sharma had only been deputed as a police observer during the West Bengal Assembly elections, during which a video of him warning TMC candidate Jahangir Khan went viral online.

Introduction
Ransomware is one of the serious cyber threats as it causes consequences such as financial losses, data loss, and reputation damage. Recently in 2023, a new ransomware called Akira ransomware emerged or surfaced. It has targeted and affected various enterprises or industries, such as BSFI, Construction, Education, Healthcare, Manufacturing, real estate and consulting, primarily based in the United States. Akira ransomware has targeted industries by exploiting the double-extortion technique by exfiltrating and encrypting sensitive data and imposing the threat on victims to leak or sell the data on the dark web if the ransom is not paid. The Akira ransomware gang has extorted a ransom ranging from $200,000 to millions of dollars.
Uncovering the Akira Ransomware operations and their targets
Akira ransomware gang has gained unauthorised access to computer systems by using sophisticated encryption algorithms to encrypt the Data. When such an encryption process is completed, the affected device or network will not be able to access its files or use its data.
The affected files by Akira ransomware showed the extension named “.akira”, and the file’s icon shows blank white pages. The Akira ransomware has developed a data leak site so as to extort victims. And it has also used the ransom note named “akira_readme.txt”.
Akira ransomware steeled the corporate data of various organisations, which the Akira ransomware gang used as leverage while threatening the affected organisation with high ransom demands. Akira Ransomware gang threaten the victims to leak their sensitive data or corporate data in the public domain if the demanded ransom amount is not paid. Akira ransomware gang has leaked the data of four organisations and the size ranges from 5.9GB to 259 GB of data leakage.
Akira Ransomware gang communicating with Victims
The Akira ransomware has provided a unique negotiation password to each victim to initiate communication. Where the ransomware gang deployed a chat system for the purpose of negotiation and demanding ransom from the affected organisations. They have deployed a ransom note as akira_readme.txt so as to provide information as to how they have affected the victim’s files or data along with links to the Akira data leak site and negotiation site.
How Akira Ransomware is different from Pegasus Spyware
Pegasus, developed in the year 2011, belongs to one of the most powerful family of spyware. Once it has infected, it can spear your phone and your text messages or emails. It has the ability to turn your phone into a surveillance device, from copying your messages to harvesting your photos and recording calls. In fact, it has the ability to record you through your phone camera or record your conversation by using your microphone, it also has the ability to track your pinpoint location. In contrast, newly Akira ransomware affects encrypting your files and preventing access to your Data and then asking for ransom n the pretext of leaking your data or for decryption.
How to recover from malware attacks
If affected by such type of malware attack, you can use anti-malware tools such as SpyHunter 5 or Malwarebytes to scan your system. These are the security software which can scan your system and remove suspicious malware files and entries. If you are unable to perform the scan or antivirus in normal mode due to malware in your system, you can use it in Safe Mode. And try to find a relevant decryptor which can help you to recover your files. Do not fall into a ransomware gang’s trap because there is no guarantee that they will help you to recover or will not leak your data after paying the ransom amount.
Best practices to be safe from such ransomware attacks
Conclusion
The Akira ransomware operation poses serious threats to various organisations worldwide. There is a high need to employ robust cybersecurity measures to safeguard networks and sensitive data. Organisations must ensure to keep their software system updated and backed up to a secure network on a regular basis. Paying the ransom is illegal mean instead you should report the incident to law enforcement agencies and can consult with cybersecurity professionals for the recovery method.


