#FactCheck: AI-Generated Footage Fuels False Claim of Strike on Al Udeid Air Base
Executive Summary
The ongoing conflict between the US-Israel and Iran has entered its third week. During this period, Iran reportedly targeted the US military base at Al Udeid in Qatar. Amid this, a video is going viral on social media showing people, vehicles, and chaos following an alleged attack. Some users are sharing it as footage of an Iranian missile strike on the Al Udeid Air Base. However, an research by the CyberPeacefound that the viral video is not real but AI-generated.
Claim:
An Instagram user “thenewscartel” shared the video on March 17, 2026, with the caption: “Al Udeid Air Base, Qatar (March 16, 2026): Iran launched ballistic missiles and drones at the US military’s largest Middle East base near Doha as retaliation for US-Israel strikes in Tehran. Qatar’s Defense Ministry confirmed multiple launches. Most were intercepted by Qatari air defense. One missile landed near the base or in an uninhabited area. No casualties or major damage reported. Explosions were heard in Doha, and smoke was seen in the sky.”

Fact Check:
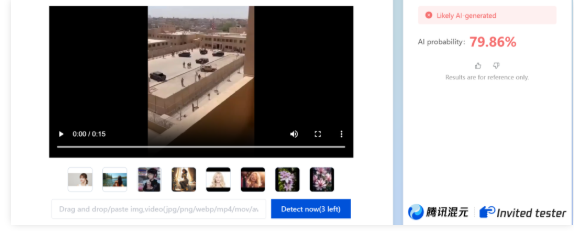
To verify the claim, we closely examined the viral video. We observed multiple visual inconsistencies—one person appears to be walking in reverse, another disappears and reappears, and the body shapes of people distort as they begin to run. These anomalies strongly indicate AI manipulation. We then analyzed the video using the AI detection tool Zhuque AI, which indicated an approximately 80 percent likelihood that the video is AI-generated.
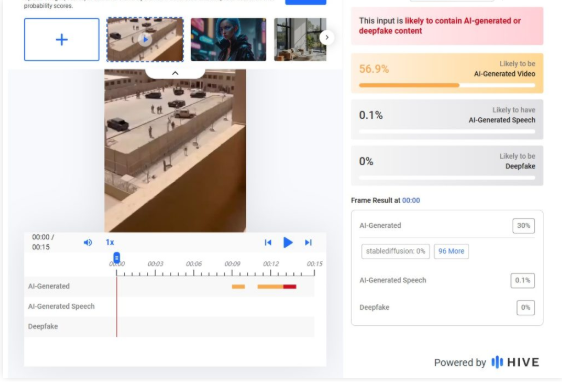
Further analysis using Hive Moderation showed around a 57 percent probability of the video being AI-generated.
Conclusion:
Our research found that the viral video being shared as footage of an Iranian attack on the US military base at Al Udeid in Qatar is AI-generated and not related to any real incident.
Related Blogs

Overview:
‘Kia Connect’ is the application that is used to connect ‘Kia’ cars which allows the user control various parameters of the vehicle through the application on his/her smartphone. The vulnerabilities found in most Kias built after 2013 with but little exception. Most of the risks are derived from a flawed API that deals with dealer relations and vehicle coordination.
Technical Breakdown of Exploitation:
- API Exploitation: The attack uses the vulnerabilities in Kia’s dealership network. The researchers also noticed that, for example, the logs generated while impersonating a dealer and registering on the Kia dealer portal would be sufficient for deriving access tokens needed for next steps.
- Accessing Vehicle Information: The license plate number allowed the attackers to get the Vehicle Identification Number (VIN) number of their preferred car. This VIN can then be used to look up more information about the car and is an essential number to determine for the shared car.
- Information Retrieval: Having the VIN number in hand, attackers can launch a number of requests to backends to pull more sensitive information about the car owner, including:
- Name
- Email address
- Phone number
- Geographical address
- Modifying Account Access: With this information, attackers could change the accounts settings to make them a second user on the car, thus being hidden from the actual owner of the account.
- Executing Remote Commands: Once again, it was discovered that attackers could remotely execute different commands on the vehicle, which includes:some text
- Unlocking doors
- Starting the engine
- Monitoring the location of the vehicle in terms of position.
- Honking the horn
Technical Execution:
The researchers demonstrated that an attacker could execute a series of four requests to gain control over a Kia vehicle:
- Generate Dealer Token: The attacker sends an HTTP request in order to create a dealer token.
- Retrieve Owner Information: As indicated using the generated token, they make another request to another endpoint that returns the owner’s email address and phone number.
- Modify Access Permissions: The attacker takes advantage of the leaked information (email address and VIN) of the owner to change between users accounts and make himself the second user.
- Execute Commands: As the last one, they can send commands to perform actions on the operated vehicle.
Security Response and Precautionary Measures for Vehicle Owners
- Regular Software Updates: Car owners must make sure their cars receive updates on the recent software updates provided by auto producers.
- Use Strong Passwords: The owners of Kia Connect accounts should develop specific and complex passwords for their accounts and then update them periodically. They should avoid using numbers like the birth dates, vehicle numbers and simple passwords.
- Enable Multi-Factor Authentication: For security, vehicle owners should turn on the use of the secondary authentication when it is available to protect against unauthorized access to an account.
- Limit Personal Information Sharing: Owners of vehicles should be careful with the details that are connected with the account on their car, like the e-mail or telephone number, sharing them on social networks, for example.
- Monitor Account Activity: It is also important to monitor the account activity because of change or access attempts that are unauthorized. In case of any abnormality or anything suspicious felt while using the car, report it to Kia customer support.
- Educate Yourself on Vehicle Security: Being aware of cyber threats that are connected to vehicles and learning about how to safeguard a vehicle from such threats.
- Consider Disabling Remote Features When Not Needed: If remote features are not needed, then it is better to turn them off, and then turn them on again when needed. This can prove to help diminish the attack vector for would-be hackers.
Industry Implications:
The findings from this research underscore broader issues within automotive cybersecurity:
- Web Security Gaps: Most car manufacturers pay more attention to equipment running in automobiles instead of the safety of the websites that the car uses to operate thereby exposing automobiles that are connected very much to risks.
- Continued Risks: Vehicles become increasingly connected to internet technologies. Auto makers will have to carry cyber security measures in their cars in the future.
Conclusion:
The weaknesses found in Kia’s connected car system are a key concern for Automotive security. Since cars need web connections for core services, suppliers also face the problem of risks and need to create effective safeguards. Kia took immediate actions to tighten the safety after disclosure; however, new threats will emerge as this is a dynamic domain involving connected technology. With growing awareness of these risks, it is now important for car makers not only to put in proper security measures but also to maintain customer communication on how it safeguards their information and cars against cyber dangers. That being an incredibly rapid approach to advancements in automotive technology, the key to its safety is in our capacity to shield it from ever-present cyber threats.
Reference:
- https://timesofindia.indiatimes.com/auto/cars/hackers-could-unlock-your-kia-car-with-just-a-license-plate-is-yours-safe/articleshow/113837543.cms
- https://www.thedrive.com/news/hackers-found-millions-of-kias-could-be-tracked-controlled-with-just-a-plate-number
- https://www.securityweek.com/millions-of-kia-cars-were-vulnerable-to-remote-hacking-researchers/
- https://news24online.com/auto/kia-vehicles-hack-connected-car-cybersecurity-threat/346248/
- https://www.malwarebytes.com/blog/news/2024/09/millions-of-kia-vehicles-were-vulnerable-to-remote-attacks-with-just-a-license-plate-number
- https://informationsecuritybuzz.com/kia-vulnerability-enables-remote-acces/
- https://samcurry.net/hacking-kia

A war in the twenty-first century does not start when the first bullet or missile is fired. It begins much earlier, covertly, and without any official announcement. Cyberspace is this new battlefield. States now use a variety of ransomware, malicious codes, and disinformation campaigns to undermine their enemies' capabilities before launching an offensive. These pre-conflict cyber operations are now the primary frontline of contemporary hybrid warfare, which is changing how conflicts are fought and conducted.
The Birth of a Digital Battlefield
Hybrid Warfare is a blend of conventional military force with nonmilitary tactics like economic coercion, disinformation, and cyberattacks that have evolved rapidly in recent decades. Hybrid methods of warfare are nothing new, as the scale and sophistication of cyber operations in modern conflicts are unprecedented. Russia’s actions in Ukraine demonstrated the capability of digital tools to paralyse the critical systems before its heavy munitions could be deployed for combat operations. Within days of the 2022 invasions, Ukraine faced massive Distributed Denial of Service (DDoS) attacks targeting banks, government websites, and energy infrastructures. The digital frontlines have softened the physical defences long before the conventional warfare began.
According to the FP Analytics’ “Digital Front Lines” Project, cyber operations are no longer an auxiliary tactic but a core component of hybrid warfare, blurring the boundary between peace and war. They enable states to exert pressure, gather intelligence, and disrupt adversaries, often without being attributed or held accountable.
Cyber Operations: The modern Prelude to War
The use of digital technologies for surveillance, information network disruption, or critical infrastructure destruction is known as cyber operations. They are especially useful instruments for pre-conflict manipulation because of their ambiguity and stealth. Cyberattacks, in contrast to conventional military strikes, can accomplish strategic goals while providing plausible deniability.
Coordinated cyberattacks that spread misinformation and damaged public confidence disrupted government communication systems prior to Russia's invasion of Ukraine. These sorts of incidents highlight the integrated nature of cyber and kinetic operations, where digital assaults often serve as the initial phases of modern wars.
The Expanding Spectrum of Actors or Threat
Cyberspace has democratized warfare, which once required an army, can now be initiated by a handful of skilled programmers with access to the right tools. The cyber landscape of the present times features a wide spectrum of threat actors, which can be understood as;
- State actors like intelligence or military agencies conduct cyber operations as part of official foreign policy.
- Cybercriminals pursue financial gains, often overlapping with political motives.
- Terrorist groups use cyberspace to spread propaganda for coordinated attacks.
- Cyber mercenaries being hired by both the state and nonstate clients can blur the ethical and legal boundaries.
This diversity can complicate the attribution by determining that anyone who is actively working behind conducting cyberattacks can be notoriously difficult, allowing the states to hide behind “plausible deniability.” This ‘Gray Zone’ of conflict below the threshold of a declared war, above mere diplomacy, has become the preferred arena for modern power struggles.
Civilian Involvement and Ethical Dilemmas
Unlike traditional warfare, where the cyber domain entangles civilians as both participants and targets. Much of the nation’s critical infrastructure, which includes energy grids, hospitals, transportation, and communication systems, is owned and operated by private entities. As a result, the civilian industries and experts are becoming central to both cyber defence and offence.
During the Russia–Ukraine War, the volunteer hackers from around the world were many of whom are being coordinated through the app Telegram, which is termed as ‘IT Army of Ukraine’, are known for conducting digital strikes on Russian networks. Conversely, the Russia-affiliated hacker groups like Conti had vowed to retaliate against any nations that supported Ukraine.
This civilian participation raises profound legal and moral questions, over a private company’s role in defending their networks of becoming a combatant, or the impact of retaliatory cyberattacks on civilian infrastructure war crimes. International law has yet to provide a clear answer, which can leave dangerous gaps in the governance to counter cybercrimes.
Susceptibility of Contemporary Society to Cyber Warfare
Cyberwarfare can impact an entire global digital ecosystem due to its interconnectedness. Power grids, hospitals, air traffic systems, and even automation devices can be compromised. While the NotPetya ransomware, which was cloaked as ransomware, caused billions of losses and caused worldwide economic damage from shipping companies to pharmaceutical companies, the WannaCry ransomware attacks in 2017 paralysed hospitals throughout the UK's National Health Service.
When taken as a whole, these incidents have also shown that cyberattacks are no longer limited to espionage situations and can have real-world consequences comparable to those of conventional warfare. The consequences of cyberattacks could increase dramatically as our dependence on technology increases. Because these effects are profoundly psychological in nature and seek to sow fear, mistrust, and social disintegration, they are not merely technical or economic in nature.
The Future: Permanent Cyber Frontlines
Technological developments have made cyberspace a permanent theatre of conflict, joining the land, sea, air, and space. Countries are currently making significant investments in cyber capabilities for deterrence as well as defence. According to security experts like Eriksson and Giacomello, societies are now inherently fragile due to our increasing reliance on information technologies.
Cyber operations in this context are about strategic dominance in a globalised world, not just digital espionage. Who controls the networks and algorithms that run contemporary civilisation will determine the future of war, not just who controls the skies or the seas. As per the new reality, before the drop of the first bomb, a silent war in cyberspace will already be underway.
References
- https://digitalfrontlines.io/2023/05/25/the-evolution-of-cyber-operations-in-armed-conflict/
- https://theses.ubn.ru.nl/server/api/core/bitstreams/9d74149e-fb9a-402f-aa65-a90445ad7603/content
- https://cybersecurityguide.org/resources/cyberwarfare/
- https://re.public.polimi.it/retrieve/e0c31c0b-ce6c-4599-e053-1705fe0aef77/21%20Century%20Cyber%20Warfare.pdf
.webp)
Incident Overview
Earlier this week, the Chinese media reported that several ‘Macau’ government websites were hacked, indicating a significant targeted cyberattack. The hacked website includes those of the office of the Secretary for Security, the public security police, the fire services department and the Security Forces Services Bureau. It was reported that the police have launched a criminal investigation to trace the source of the crime. Furthermore, officials believe the source of the intrusion was likely from overseas, and authorities have carried out an emergency response in conjunction with telecommunication operators to restore affected services on a priority basis. The densely populated Macau is a special administrative region on the south coast of China and the cyber attacks on the essential government website of China raise a serious concern.
Response and Mitigation
Macau's authorities carried out an emergency response in collaboration with telecommunication operators to restore regular services as a distributed denial-of-service attack (DDoS) was reported to be carried out on certain government websites which resulted in the inactivity of those several websites. The country's security forces instructed Macau Telecom to investigate the incident and submit a report and improvement plan to prevent similar attacks in the future.
Context and Implications
The hack on the government websites of Macau is not a single incident; rather, it is a part of an increasing pattern of cyberattacks on the region's vital infrastructure. According to a recent report, the frequency of cybercrimes has tripled since 2020, targeting Macau's critical infrastructure, which is worrying. This pattern draws attention to the growing threats that public sector organisations and governments throughout the world confront.
Final Words
In light of such sophisticated attacks targeting vital infrastructure or critical government operations, it is imperative that the country ensure powerful cybersecurity strategies and measures. Implementing robust cybersecurity measures, developing incident response planning, regular security checks, employee training on cyber hygiene, public awareness and capacity building and international collaboration to jointly develop and plan counteract strategies is a crucial step to build safeguards against such cyber threats.
The incident of a cyberattack on the government websites of Macau serves stark reminder of the evolving threats and cybersecurity challenges, it is a serious concern when critical government websites are compromised by malicious actors. It highlights the necessity for continuous vigilance and cybersecurity measures in place to counter such cyber attacks. A comprehensive approach to cybersecurity, the government can enhance their overall cybersecurity posture, establish resilience against such threats in future, and save the functionality of essential government websites.
References:
- https://macaudailytimes.com.mo/websites-of-office-of-the-secretary-for-security-targeted-in-a-cyber-attack.html
- https://www.reuters.com/world/china/several-macau-government-websites-hacked-says-chinese-state-media-2024-07-11/
- https://4imag.com/several-macau-government-websites-hacked-says-chinese-state-media/
- https://www.aol.com/news/several-macau-government-websites-hacked-001435511.htmlhttps://therecord.media/macau-government-websites-hit-with-cyberattack
- https://macaonews.org/news/city/macau-cyberattacks-cyber-security-attacks-macao/


