Introduction:
Technology has become a vital part of everyone’s life nowadays, it occupies essential activities of a person’s life whether we are working or playing and studying. I would say from education to corporate, technology makes everything easier and simpler to achieve the goals for a particular thing. Corporate companies are using technology for their day-to-day work and there are many law-based foundations that are publishing blogs and papers for legal awareness, many lawyers use internet technology for promoting themselves which amounts to growth in their work. Some legal work can now be done by machines, which was previously unthinkable. Large disputes frequently have many documents to review. Armies of young lawyers and paralegals are typically assigned to review these documents. This work can be done by a properly trained machine. Machine drafting of documents is also gaining popularity. We’ve also seen systems that can forecast the outcome of a dispute. We are starting to see machines take on many tasks that we once thought was solely the domain of lawyers.
How to expand law firms and the corporate world with the help of technology?
If we talk about how lawyers’ lives will be impacted by technology then I would explain about law students first. Students are the one who is utilizing the technology at its best for their work, tech could be helpful in students’ lives. as law students use SCC online and manupatra, which are used for case laws. And during their law internships, they use it to help their seniors to find appropriate cases for them. and use it as well for their college research work. SCC and manupatra are very big platforms by which we can say if students use technology for their careers, it will impact their law career in the best ways.
A lawyer running a law firm is not a small task, and there are plenty of obstacles to that, such as a lack of tech solutions, failure to fulfil demands, and inability to innovate, these obstacles prevent the growth of some firms. The right legal tech can grow an organization or a law firm and there will be fewer obstacles.
Technology can be proven as a good mechanism to grow the law firm, as everything depends on tech, from court work to corporate. If we talk about covid during 2020, everything shifted towards the virtual world, court hearings switched to online mode due to covid which proved as a bone to the legal system as the case hearings were speedy and there was no physical contact due to that.
Legal automation is also helping law firms to grow in a competitive world. And it has other benefits also like shifting tedious tasks from humans to machines, allowing the lawyer to work on more valuable work. I would say that small firms should also need to embrace automation for competition in the corporate sector. Today, artificial intelligence offers a solution to solve or at least make the access-to-justice issue better and completely transform our traditional legal system.
There was a world-cited author, Richard Susskind, OBE, who talked about the future of law and lawyers and he wrote a book, Online Courts and the Future of Justice. Richard argues that technology is going to bring about a fascinating decade of change in the legal sector and transform our court system. Although automating our old ways of working plays a part in this, even more, critical is that artificial intelligence and technology will help give more individuals access to justice.
The rise of big data has also resulted in rapid identification systems, which allow police officers to quickly see an individual’s criminal history through a simple search.The FBI’s Next Generation Identification (NGI) system matches individuals with their criminal history information using biometrics such as fingerprints, palm prints, iris recognition, and facial recognition. The NGI’s current technologies are constantly being updated, and new ones are being added, to make the NGI the most comprehensive way to gather up-to-date information on the person being examined
During covid, there were e-courts services in courts, and lawyers and judges were taking cases online. After the covid, the use of technology increased in the law field also from litigation to corporate. As technology can also safeguard confidential information between parties and lawyers. There was ODR, (online dispute resolution) happening meetings that were taking place online mode.
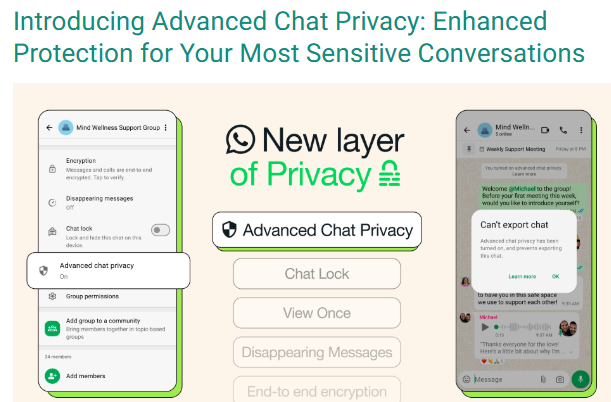
File sharing is inevitable in the practice of law. Yet sometimes the most common ways of sharing (think email) are not always the most secure. With the remote office, the boom has come an increased need for alternate file-sharing solutions. There is data encryption to protect data as it is a reliable method to protect confidential data and information.
Conclusion-
Technology has been playing a vital role in the legal industry and has increased the efficiency of legal offices and the productivity of clerical workers. With the advent of legal tech, there is greater transparency between legal firms and clients. Clients know how many fees they must pay and can keep track of the day-to-day progress of the lawyer on their case. Also, there is no doubt that technology, if used correctly, is fast and efficient – more than any human individual. This can prove to be of great assistance to any law firm. Lawyers of the future will be the ones who create the systems that will solve their client’s problems. These legal professionals will include legal knowledge engineers, legal risk managers, system developers, design thinking experts, and others. These people will use technology to create new ways of solving legal problems. In many ways, the legal sector is experiencing the same digitization that other industries have, and because it is so document-intensive, it is actually an industry that stands to benefit greatly from what technology has to offer.