#FactCheck - Viral Video of ‘Hatha Yogi’ Meditating on Snowy Mountain Is AI-Generated
A video claiming to show a Hatha yogi performing extreme penance on a snow-covered mountain amid strong icy winds is going viral on social media. In the clip, the ascetic is seen balancing on one hand in a yoga posture, while users portray the visuals as a rare example of extraordinary spiritual endurance in harsh climatic conditions.
However, an investigation by the CyberPeace Foundation has found the claim to be false. Our analysis confirms that the viral video is AI-generated and does not depict a real person or an actual event.
Claim:
A Instagram user shared the video with the caption:
“Hatha yogi, what kind of soil are these people made of?” The post suggests that the visuals show a real yogi performing intense meditation on a frozen mountain.
- https://www.instagram.com/reels/DTK32TvDGIJ/
- (Archive link as provided) https://perma.cc/H84M-MGXZ

Fact Check:
To verify the claim, the CyberPeace Foundation conducted a detailed examination of the viral video.No credible or verifiable news reports were found to support the claim that such an incident ever occurred.
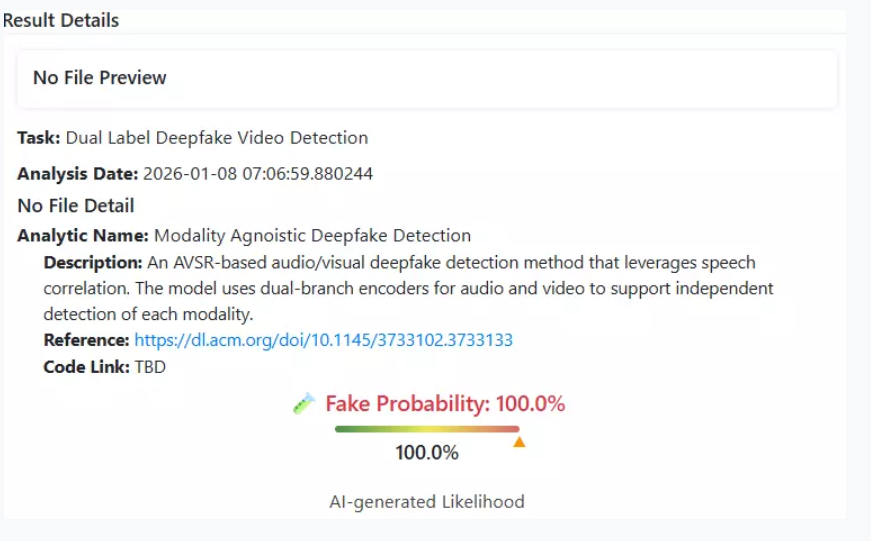
The viral video was analysed using the AI detection tool Deepfake-O-Meter.Its AVSRDD (2025) module flagged the video as AI-generated, confirming that the visuals were digitally created and not recorded in real life.
Multiple indicators within the footage,such as unnatural body balance, environmental inconsistencies, and visual artifacts are consistent with AI-generated content.
Conclusion
The viral video purportedly showing a yogi meditating on a frozen mountain is not real. It has been created using artificial intelligence and is being circulated on social media with a misleading narrative. Users are advised to exercise caution and verify content before sharing such sensational claims.
Related Blogs

Introduction:
With improved capabilities and evasion strategies, the Vultur banking Trojan has reappeared and is a serious danger to Android users. The virus now employs numerous encrypted payloads, encrypted communication, and poses as legitimate apps. It is transmitted by trojanized dropper programs on the Google Play Store. Vultur targets victims via phone calls and SMS messages. With the help of this updated version of Vultur, attackers may take total control of compromised devices. They can perform a variety of remote control operations like install, remove, upload, and download files, halt the execution of programs, and circumvent the lock screen. The virus is now far more hazardous than it was previously because of its improved capacity to remotely access and manipulate machines.
Overview:
The Android banking malware Vultur is well-known for its ability to record screens. It was first identified by ThreatFabric in March 2021 and targets banking apps for remote control and keylogging.
The malicious apps were hosted on the Google Play Store by the Brunhilda dropper-framework, which was used for its distribution. Initial versions of the program used reputable remote access tools such as ngrok and AlphaVNC.
Hybrid attacks have been used in recent operations to disseminate the Brunhilda dropper via phone calls and SMS. The dropper uses a number of payloads to distribute an upgraded version of Vultur.
41 new Firebase Cloud Messaging (FCM) commands and seven new Command-and-Control (C2) methods are included in the most recent version of Vultur.
With the help of Android's Accessibility Services, these enhancements concentrate on remote access functionality that improves the malware's capacity to communicate with the victim's screen.
Modus operandi of Attack:
Hybrid Attack Method:
- Utilizes a phone call, two SMS messages, and trick users into installing malware.
- First SMS tricks victims into calling a certain number by claiming to have made significant, unlawful transactions, which gives the impression of urgency.
- Although there was no transaction in reality, the urgency motivates victims to act quickly.
Trozonized MacAfee App:
- The victims are told to install a trojanized version of the McAfee Security program from a given link during the phone call.
- This app looks harmless and has features similar to the original McAfee Security app, but it's actually the Brunhilda dropper.
- The victims are misled into assuming that the security software they are installing is authentic.
Execution of Vultur Payloads:
- Three payloads connected to Vultur are decrypted and executed via the Brunhilda dropper.
- Threat actors can carry out a variety of malicious operations, including keylogging and screen recording, on the victim's mobile device thanks to these payloads, which grant them total access over it.
- The infected device of the victim allows the threat actors to launch additional assaults or obtain private data.
Indication of the attack:
The symptoms of a Vultur banking Trojan infection include:
- Remote Access: This malware gives the hacker the ability to remotely use the infected device via clicking, scrolling, and swiping through Android's accessibility services.
- File Management: Through this, the malware is able to copy, share, remove, create, and locate files from devices it has infected.
- App Blocking: For instance; the malicious software can be programmed to stop the victims from opening a certain bunch of apps.
- Custom Notifications: Attackers can embed the malware with the functionality of displaying the customized notifications in the taskbar.
- Keyguard Disabling: The malware may be designed to turn off Screen Lock Guard feature so the lock screen security measure can be easily bypassed.
- Encrypted C2 Communication: The malware chooses AES data encryption, with Base64 text encoding to provide hidden traces for C2 communication.
- Payload Decryption: The malware uses native code, mostly written in C as well as C++, to decode the goods, thus, making a process of reversing more complicated.
- Spying on Financial Apps: The malware uses screen-streaming and keylogging as ways of acquiring facts about the victim’s mobile banking applications.
Indicator of Compromise:
File hash (SHA-256)
- edef007f1ca60fdf75a7d5c5ffe09f1fc3fb560153633ec18c5ddb46cc75ea21
- 89625cf2caed9028b41121c4589d9e35fa7981a2381aa293d4979b36cf5c8ff2
- 1fc81b03703d64339d1417a079720bf0480fece3d017c303d88d18c70c7aabc3
- 4fed4a42aadea8b3e937856318f9fbd056e2f46c19a6316df0660921dd5ba6c5
- 001fd4af41df8883957c515703e9b6b08e36fde3fd1d127b283ee75a32d575fc
- fc8c69bddd40a24d6d28fbf0c0d43a1a57067b19e6c3cc07e2664ef4879c221b
- 7337a79d832a57531b20b09c2fc17b4257a6d4e93fcaeb961eb7c6a95b071a06
- 7f1a344d8141e75c69a3c5cf61197f1d4b5038053fd777a68589ecdb29168e0c
- 26f9e19c2a82d2ed4d940c2ec535ff2aba8583ae3867502899a7790fe3628400
- 2a97ed20f1ae2ea5ef2b162d61279b2f9b68eba7cf27920e2a82a115fd68e31f
- c0f3cb3d837d39aa3abccada0b4ecdb840621a8539519c104b27e2a646d7d50d
- 92af567452ecd02e48a2ebc762a318ce526ab28e192e89407cac9df3c317e78d
- fa6111216966a98561a2af9e4ac97db036bcd551635be5b230995faad40b7607
- dc4f24f07d99e4e34d1f50de0535f88ea52cc62bfb520452bdd730b94d6d8c0e
- 627529bb010b98511cfa1ad1aaa08760b158f4733e2bbccfd54050838c7b7fa3
- f5ce27a49eaf59292f11af07851383e7d721a4d60019f3aceb8ca914259056af
- 5d86c9afd1d33e4affa9ba61225aded26ecaeb01755eeb861bb4db9bbb39191c
- 5724589c46f3e469dc9f048e1e2601b8d7d1bafcc54e3d9460bc0adeeada022d
- 7f1a344d8141e75c69a3c5cf61197f1d4b5038053fd777a68589ecdb29168e0c
- fd3b36455e58ba3531e8cce0326cce782723cc5d1cc0998b775e07e6c2622160
- 819044d01e8726a47fc5970efc80ceddea0ac9bf7c1c5d08b293f0ae571369a9
- 0f2f8adce0f1e1971cba5851e383846b68e5504679d916d7dad10133cc965851
- fb1e68ee3509993d0fe767b0372752d2fec8f5b0bf03d5c10a30b042a830ae1a
- d3dc4e22611ed20d700b6dd292ffddbc595c42453f18879f2ae4693a4d4d925a
- f4d7e9ec4eda034c29b8d73d479084658858f56e67909c2ffedf9223d7ca9bd2
- 7ca6989ccfb0ad0571aef7b263125410a5037976f41e17ee7c022097f827bd74
- c646c8e6a632e23a9c2e60590f012c7b5cb40340194cb0a597161676961b4de0
Command and Control Servers
- safetyfactor[.]online
- cloudmiracle[.]store
- flandria171[.]appspot[.]com (FCM)
- newyan-1e09d[.]appspot[.]com (FCM)
Droppers distribution URL’s
- mcafee[.]960232[.]com
- mcafee[.]353934[.]com
- mcafee[.]908713[.]com
- mcafee[.]784503[.]com
- mcafee[.]053105[.]com
- mcafee[.]092877[.]com
- mcafee[.]582630[.]com
- mcafee[.]581574[.]com
- mcafee[.]582342[.]com
- mcafee[.]593942[.]com
- mcafee[.]930204[.]com
Steps to be taken when your device is compromised?.
- Change the password: Vultur revealed multiple cases where threat actors can gain access to your financial and private information. To safeguard your account, reset passwords on other devices and create secure, unique passwords during the time. Instead of simply storing your password, a reputed password manager is the most secure way of storing information.
- Keep an eye on your transactions and accounts: It is advised that you regularly monitor your online accounts for any unusual or illegal activity. Keep a watch out for any irregularities, and report anything suspicious to the provider or authorities straight immediately.. Also check your credit reports and scores attentively to make sure that your identity or cards are not compromised.
- Make sure you are using identity theft protection: Many pieces of information about your identity are stored in an Android device. Cyber criminals can easily get hold of this data and make major damage to you, including stealing your money and identity. For your own protection, some of the identity theft protection services that monitor all your personal information and notify you on any unusual activity and, as well, helps you to freeze your accounts would be beneficial.
- Immediately get in touch with your banks and credit card companies: Your personal information such as credit card or bank details is of high risk to be exposed to hackers who could use them to make transactions without you knowing. You should inform your credit card and the lending bank about the situation as soon as possible. They would help you if your cards were used for fraudulent charges and your card be either frozen or canceled. Besides, they can get new cards issued.
- Make your contacts alert regarding the fraud you faced: Threat actors may access your social media or email accounts to send phishing messages or spam to people in your contact list, if they gain access to them. Moreover, they may masquerade as you and try to extort cash from you or disclose your personal information. Distributing a message to your contacts stating that they shouldn’t open or reply to any messages that look like they are not from you and look very strange or suspicious, will be a great idea.
- Make a backup and wipe all your device content in factory settings: You can always factory reset your device to ensure it is free of viruses and spyware. In other words, it will refresh Android and leave behind all your data and settings. Back up all the critical data prior to processing it and assure that everything is restored from a trustworthy source only.
Preventive measures to be taken:
- Avoid calling back to the hacker: If a hacker texts you claiming to have approved a sizable bank transaction, refrain from picking up the phone. You can always check by making a call to your own financial intuition. However, never pick up on an unknown number that someone else sends you.
- Avoid sideloading apps and shortened URLs: Try to avoid sideloading apps. That's the moment when you install apps from unofficial sources. Users may be tricked into downloading malware using short URLs.
- Be careful granting permissions: Be cautious when allowing permissions for apps. Think about whether an app really needs access to specific data or device functions.
- Limit the apps you have on your phone: On your phone, having plenty of apps might sometimes make it easier to become infected with malware. Over time, these apps may allow harmful code to enter your system, and the more programs you have to update and monitor, the greater the risk to your Android device. This is how to remove pointless apps from your Android device.
- Download apps from reputable sources: Additionally, make sure the programs you download are from reputable and authorized developers. Do your homework and read reviews before you install.
- Keep your Android device updated: With the help of software and security upgrades, your phone can automatically maintain security. Remember to install them.
- Have good antivirus software on all your devices: The best defense against malware on all of your devices is to install antivirus software. By blocking you from clicking on potentially dangerous links, antivirus software can keep malware off your devices and keep hackers from accessing your personal data.
Conclusion:
Vultur is a terrifying banking Trojan with a great deal of sophistication. It's unsettling that hackers can take complete control of your Android device, which emphasizes how crucial it is that you take precautions. It all starts with a text message in these attacks. You must take the time to independently contact your banking institution to check whether there are any issues. You may prevent having your entire device compromised and your personal information exposed by simply investing an additional few minutes.
Reference:
- https://research.nccgroup.com/2024/03/28/android-malware-vultur-expands-its-wingspan/
- https://www.threatfabric.com/blogs/vultur-v-for-vnc\
- https://www.tomsguide.com/computing/malware-adware/this-nasty-android-banking-trojan-lets-hackers-completely-hijack-your-phone-how-to-stay-safe
- https://thehackernews.com/2024/04/vultur-android-banking-trojan-returns.html?m=1
- https://www.smallbiztechnology.com/archive/2024/04/vultur-trojan-heightens-android-app-security-risks.html/
- https://securityaffairs.com/161320/malware/vultur-banking-trojan-android.html
- https://www.malwarebytes.com/blog/detections/android-trojan-spy-vultur
- https://www.scmagazine.com/brief/updated-vultur-android-banking-trojan-emerges
- https://innovatecybersecurity.com/security-threat-advisory/windows-server-updates-blamed-for-domain-controller-crashes-kb5035855-and-kb5035857/

Executive Summary
Iran’s official news agencies have denied claims that senior officials, including Foreign Minister Abbas Araghchi and Parliament Speaker Mohammad Bagher Ghalibaf, have arrived in Pakistan for talks. A senior official told Iran’s Tasnim News Agency that Tehran is considering Pakistan’s proposal for peace talks, but any dialogue would depend on the United States fulfilling its commitment to halt military actions on all fronts.
Notably, the United States and Iran had agreed to a two-week ceasefire on April 8, 2026, with discussions reportedly scheduled for April 11 in Islamabad. Amid this backdrop, a video showing fighter jets escorting a large aircraft is being widely circulated on social media. Users claim that Pakistan deployed these jets to escort an Iranian delegation into the country.
However, an research by the CyberPeace found the claim to be false. The viral video is not recent and dates back to 2019.
Claim
An X (formerly Twitter) user shared the video claiming that Pakistan Air Force jets were escorting an Iranian delegation into Pakistan.

Fact Check
Reverse image search of keyframes from the viral video led us to a February 18, 2019 report by Radio Free Europe/Radio Liberty. The report stated that the fighter jets were deployed by Pakistan to escort the aircraft of Saudi Crown Prince Mohammed bin Salman during his visit to Pakistan on February 17, 2019.
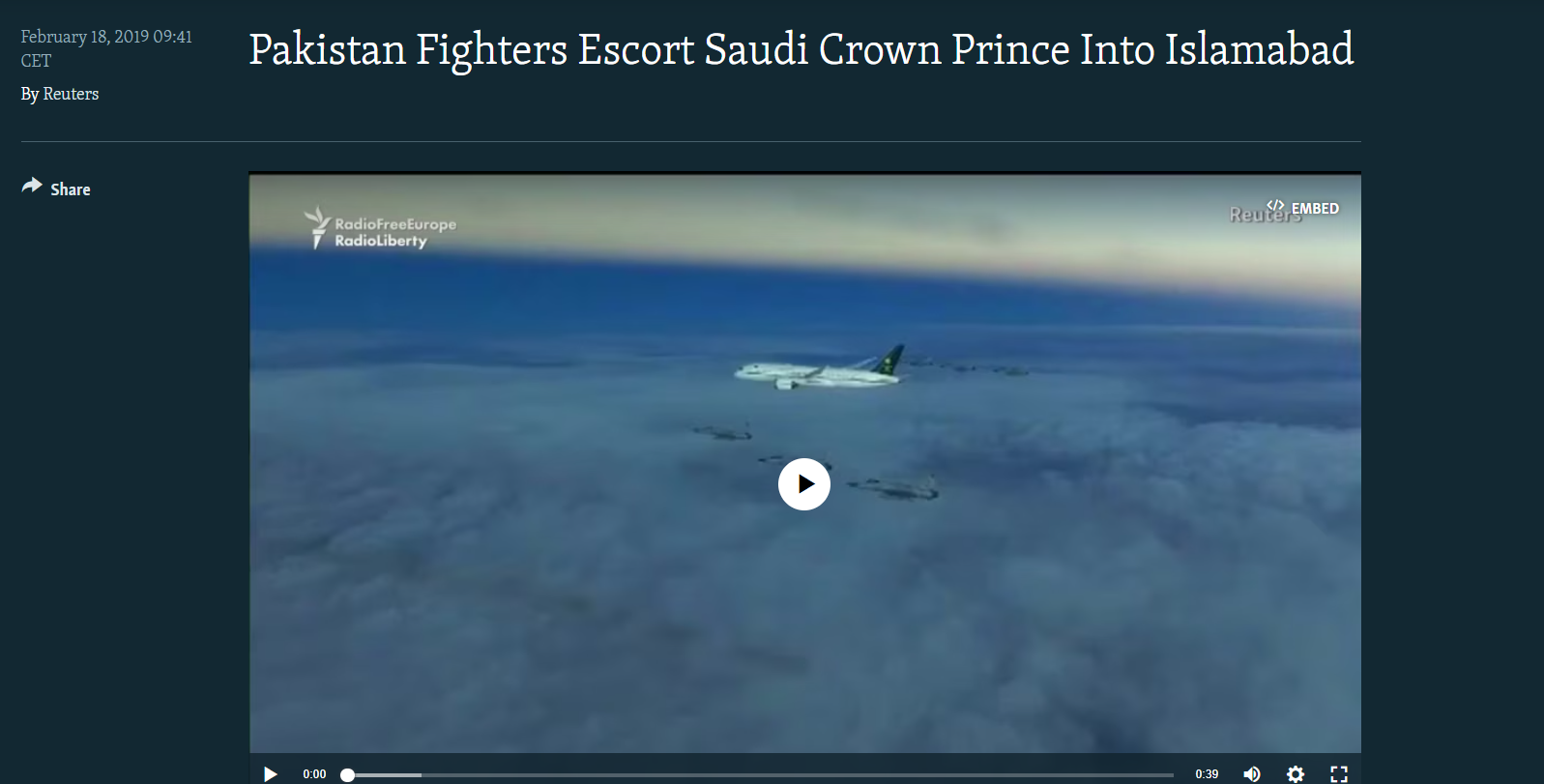
Further verification led us to the same footage uploaded on YouTube by the channel “SCMP Archive” on July 6, 2020. At the time, Pakistan’s Air Force had described the escort as part of a ceremonial welcome tradition for visiting dignitaries.

Conclusion
The viral claim is misleading. The video does not show Pakistani fighter jets escorting an Iranian delegation amid ongoing ceasefire talks. Instead, it is an old clip from 2019, when Pakistan deployed JF-17 fighter jets to welcome Saudi Crown Prince Mohammed bin Salman during his official visit. There is no evidence linking the video to current geopolitical developments involving Iran and Pakistan. The footage has been taken out of context and reshared with a false narrative to mislead viewers.
Executive Summary
A video of Delhi government cabinet minister Kapil Mishra is being shared on social media. In the clip, he can be heard saying that from the next day, only 50 percent attendance will be allowed in offices, while the remaining 50 percent employees will work from home. He also states that all institutions must comply with this. Users are sharing the video as a recent development. However, a study by the CyberPeace found the viral claim to be misleading. Our research revealed that the video is not recent but dates back to December 2025.
Claim:
An Instagram user shared the viral video on March 24, 2026. The link to the post is given below.

Fact Check:
To verify the claim, we conducted a keyword search on Google. During this process, we found a report published on December 17, 2025, on NDTV Hindi. According to the report, the Delhi government had made 50 percent work-from-home mandatory in government offices due to severe air pollution. Additional restrictions were also imposed under GRAP Stage IV.

Further, we found the original video on the official social media handle of BJP Delhi. In this video, Kapil Mishra can be heard stating that 50 percent work-from-home has been made mandatory in all government and private offices in Delhi, while health and other essential services have been exempted from this arrangement.

Conclusion:
Our research found that the viral video is not recent. It is from December 2025 and is being shared with a misleading claim.


