#FactCheck: Viral Video Showing Pakistan Shot Down Indian Air Force' MiG-29 Fighter Jet
Executive Summary
Recent claims circulating on social media allege that an Indian Air Force MiG-29 fighter jet was shot down by Pakistani forces during "Operation Sindoor." These reports suggest the incident involved a jet crash attributed to hostile action. However, these assertions have been officially refuted. No credible evidence supports the existence of such an operation or the downing of an Indian aircraft as described. The Indian Air Force has not confirmed any such event, and the claim appears to be misinformation.

Claim
A social media rumor has been circulating, suggesting that an Indian Air Force MiG-29 fighter jet was shot down by Pakistani Air forces during "Operation Sindoor." The claim is accompanied by images purported to show the wreckage of the aircraft.

Fact Check
The social media posts have falsely claimed that a Pakistani Air Force shot down an Indian Air Force MiG-29 during "Operation Sindoor." This claim has been confirmed to be untrue. The image being circulated is not related to any recent IAF operations and has been previously used in unrelated contexts. The content being shared is misleading and does not reflect any verified incident involving the Indian Air Force.

After conducting research by extracting key frames from the video and performing reverse image searches, we successfully traced the original post, which was first published in 2024, and can be seen in a news article from The Hindu and Times of India.
A MiG-29 fighter jet of the Indian Air Force (IAF), engaged in a routine training mission, crashed near Barmer, Rajasthan, on Monday evening (September 2, 2024). Fortunately, the pilot safely ejected and escaped unscathed, hence the claim is false and an act to spread misinformation.

Conclusion
The claims regarding the downing of an Indian Air Force MiG-29 during "Operation Sindoor" are unfounded and lack any credible verification. The image being circulated is outdated and unrelated to current IAF operations. There has been no official confirmation of such an incident, and the narrative appears to be misleading. Peoples are advised to rely on verified sources for accurate information regarding defence matters.
- Claim: Pakistan Shot down an Indian Fighter Jet, MIG-29
- Claimed On: Social Media
- Fact Check: False and Misleading
Related Blogs

Introduction
CyberPeace Chronicles is a one-stop for the latest edition of news, updates, and findings in global cyberspace. As we step into the cyberage, it is pertinent that we need to incorporate cybersecurity practices in our day-to-day activities. From laptops to automated homes and cars, we are all surrounded by technology in some form or another. Thus, with the increased dependency, we need to eradicate the scope of vulnerabilities and threats around us and create robust and sustainable safety mechanisms for us and future generations.
What, When and How?
- WIN-RAR Update: CVE-2023-33831, a serious vulnerability, was identified in WinRAR versions prior to 6.23 in April 2023. When users attempted to access seemingly harmless files inside ZIP archives, this vulnerability allowed attackers to run arbitrary code. Cybercriminals transmitted malware families like DarkMe, GuLoader, and Remcos RAT by taking advantage of this vulnerability. It is essential to update WinRAR to version 6.23 or later in order to protect your computer and your data. Follow the following steps to secure your device -
- Checking Your Current WinRAR Version
- Downloading the Latest WinRAR Version
- Installing the Updated WinRAR
- Completing the Installation
- Verifying the Update
- Cleaning Up
- Indonesian Hacker Groups Target Indian Digital Infrastructure: As India geared up to host the G20 delegation as part of the Leadership Summit, various reports pointed towards different forms and intensity-based cyber attacks on Indian organisations and digital infrastructure. Tech firms in India have been successful in tracing the origination of the attacks to be from Indonesia. It is believed that hacker groups backed by anti-India elements have been trying to target the digital resources of India. Organisations and central agencies like Computer Emergency Response Team (CERT-In), National Critical Information Infrastructure Protection Centre (NCIIPC), I4C (Indian Cybercrime Coordination Centre), Delhi Police, Intelligence Bureau (IB), Research and Analysis Wing (R&AW), National Investigation Agency (NIA) and Central Bureau of Investigation (CBI) have constantly been working in keeping the Digital interests of India safe and secure, and with the ongoing G20 summit, it is very pertinent to be mindful of potential threats prevailing to prepare counter tactics for the same.
- CLOP Ransomware: The CL0P ransomware is thought to have initially surfaced in 2019 and was developed by a cybercriminal organisation that spoke Russian. The threat actor FIN11 (also known as TA505 and Snakefly), who is notorious for being financially driven, is frequently connected to the CL0P ransomware, which had its roots at the beginning of 2019. By utilising this technique, CL0P has targeted businesses utilising the "Accellion FTA" file transfer appliance's vulnerable version. Accordingly, it has been asserted that the following vulnerabilities have been used to access victim data and maybe switch to victim networks. Numerous well-publicized attacks carried out by CL0P have had an impact on organisations all across the world. Especially for Managed File Transfer (MFT) programmes, the CL0P performers are well known for their talent in developing zero-day vulnerabilities. The gang went after Accellion File Transfer Appliance (FTA) devices in both 2020 and 2021, then early in 2023, they went after Fortran/Linoma GoAnywhere MFT servers, and then later in June, they went after MOVEit transfer deployments. Up to 500 organisations are thought to have been harmed by this aggressive operation. Some of the ways to mitigate the risk are as follows:
- Regular Software Updates: Updating programmes and systems helps prevent known security flaws that fraudsters frequently exploit.
- Employee Training: Employee training can significantly lower the likelihood of successful penetration by educating staff members about phishing scams and safe internet conduct.
- Network Segmentation: By separating networks and restricting lateral movement, a ransomware attack's potential effects can be reduced.
- Regular Data backups: Data backups can lessen the effects of encryption and deter payment by regularly backing up data and storing it offsite.
- Security solutions: Putting in place effective cybersecurity measures like firewalls, intrusion detection systems, and cutting-edge endpoint protection can greatly improve an organisation's defences.
- Increased scrutiny for SIM card vendors: As phishing and smishing scams are on the rise in India, the Telecom Regulatory Authority of India (TRAI) has repeatedly issued notifications and consultation papers to address this growing concern. Earlier this year, TRAI notified that promotional calling will not be continued from 10-digit personal numbers. Instead, companies will now have to take authorised 9-digit numbers for promotional calls and SMSs. Similarly, to increase the efficiency of the same, TRAI has laid down that all the SIM card vendors will now have to be verified again, and any discrepancy found against any of the vendors will lead to blacklisting and penal actions against the vendor.
Conclusion
In conclusion, the digital landscape in 2023 is rife with both opportunities and challenges. The recent discovery of a critical vulnerability in WinRAR underscores the importance of regularly updating software to protect against malicious attacks. It is imperative for users to follow the provided steps to secure their devices and safeguard their data. Furthermore, the cyber threat landscape continues to evolve, with Indonesian hacker groups targeting Indian digital infrastructure, particularly during significant events like the G20 summit. Indian organisations and cybersecurity agencies are working diligently to defend against these threats and ensure the security of digital assets. The emergence of ransomware attacks, exemplified by the CL0P ransomware, serves as a stark reminder of the need for robust cybersecurity measures. Regular software updates, employee training, network segmentation, data backups, and advanced security solutions are crucial components of a comprehensive defence strategy against ransomware and other cyber threats. Additionally, the Telecom Regulatory Authority of India's efforts to enhance security in the telecommunications sector, such as stricter verification of SIM card vendors, demonstrate a proactive approach to addressing the rising threat of phishing and smishing scams. In this dynamic digital landscape, staying informed and implementing proactive cybersecurity measures is essential for individuals, organisations, and nations to protect their digital assets and maintain a secure online environment. Vigilance, collaboration, and ongoing adaptation are key to meeting the challenges posed by cyber threats in 2023 and beyond.

Introduction
In the digital era, where technology is growing rapidly, the role of Artificial Intelligence (AI) has been making its way to different corners of the world. Where nothing seems to be impossible, technology and innovation have been moving conjointly and once again, and such innovation is in the limelight with its groundbreaking initiative known as “Project Groot”, which has been announced by the AI chip leader “Nvidia”. The core of this project is the fusion of technology with AI and robotics, where a humanoid can be produced with the capability to understand the natural language and interact with it to further learn from the physical environment by observing human actions and skills. Project Groot aims to assist humans in diverse sectors such as Healthcare and so on.
Humanoid robots are based on NVIDIA’s thor system-on-chip (SoC). The thor powers the intelligence of these robots, and the chip has been designed to handle complex tasks and ensure a safe and natural interaction between humans and robots. However, a big question arises about the ethical considerations of privacy, autonomy and the possible replacement of human workers.
Brief Analysis
Nvidia has announced Project GR00T, or Generalist Robot 00 Technology, which aims to create AI-powered humanoid robots with human-like understanding and movement. The project is part of Nvidia's efforts to drive breakthroughs in robotics and embodied AI, which can interact with and learn from a physical environment. The robots built on this platform are designed to understand natural language and emulate movements by observing human actions, such as coordination, dexterity, and other skills.
The model has been trained on NVIDIA GPU-accelerated simulation, enabling the robots to learn from human demonstrations with imitation learning and from the robotics platform NVIDIA Isaac Lab for reinforcement learning. This multimodal AI system acts as the mind for humanoid robots, allowing them to learn new skills and interact with the real world. Leading names in robotics, such as Figure, Boston Dynamics, Apptronik, Agility Robotics, Sanctuary AI, and Unitree, are reported to have collaborated with Nvidia to leverage GR00T.
Nvidia has also updated Isaac with Isaac Manipulator and Isaac Perceptor, which add multi-camera 3D vision. The company also unveiled a new computer, Jetson Thor, to aid humanoid robots based on NVIDIA's SoC, which is designed to handle complex tasks and ensure a safe and natural interaction between humans and robots.
Despite the potential job loss associated with humanoid robots potentially handling hazardous and repetitive tasks, many argue that they can aid humans and make their lives more comfortable rather than replacing them.
Policy Recommendations
The Nvidia project highlights a significant development in AI Robotics, presenting a brimming potential and ethical challenges critical for the overall development and smooth assimilation of AI-driven tech in society. To ensure its smooth assimilation, a comprehensive policy framework must be put in place. This includes:
- Human First Policy - Emphasis should be on better augmentation rather than replacement. The authorities must focus on better research and development (R&D) of applications that aid in modifying human capabilities, enhancing working conditions, and playing a role in societal growth.
- Proper Ethical Guidelines - Guidelines stressing human safety, autonomy and privacy should be established. These norms must include consent for data collection, fair use of AI in decision making and proper protocols for data security.
- Deployment of Inclusive Technology - Access to AI Driven Robotics tech should be made available to diverse sectors of society. It is imperative to address potential algorithm bias and design flaws to avoid discrimination and promote inclusivity.
- Proper Regulatory Frameworks - It is crucial to establish regulatory frameworks to govern the smooth deployment and operation of AI-driven tech. The framework must include certification for safety and standards, frequent audits and liability protocols to address accidents.
- Training Initiatives - Educational programs should be introduced to train the workforce for integrating AI driven robotics and their proper handling. Upskilling of the workforce should be the top priority of corporations to ensure effective integration of AI Robotics.
- Collaborative Research Initiatives - AI and emerging technologies have a profound impact on the trajectory of human development. It is imperative to foster collaboration among governments, industry and academia to drive innovation in AI robotics responsibly and undertake collaborative initiatives to mitigate and address technical, societal, legal and ethical issues posed by AI Robots.
Conclusion
On the whole, Project GROOT is a significant quantum leap in the advancement of robotic technology and indeed paves the way for a future where robots can integrate seamlessly into various aspects of human lives.
References
- https://indianexpress.com/article/explained/explained-sci-tech/what-is-nvidias-project-gr00t-impact-robotics-9225089/
- https://medium.com/paper-explanation/understanding-nvidias-project-groot-762d4246b76d
- https://www.techradar.com/pro/nvidias-project-groot-brings-the-human-robot-future-a-significant-step-closer
- https://www.barrons.com/livecoverage/nvidia-gtc-ai-conference/card/nvidia-announces-ai-model-for-humanoid-robot-development-BwT9fewMyD6XbuBrEDSp

Executive Summary:
A video of India’s Defence Minister Rajnath Singh is going viral on social media. The post claims that Rajnath Singh is openly supporting Israeli-American attacks against Iran. In the video, he can allegedly be heard saying that Prime Minister Narendra Modi had visited Israel before the war began and warned Tehran that disturbing peace would have serious consequences.
Research by CyberPeace found that the viral video is a deepfake created using Artificial Intelligence (AI). Rajnath Singh has not made any such statement about Iran or the Israel-US conflict.
Claim
A Facebook user “Sheikh Sadeque Ali” shared the video on March 2, 2026. The caption of the post reads, “Indian Defence Minister Rajnath Singh is supporting Israel’s attack on Iran. This clearly shows that India supports the killing of Muslims.”
In the viral video, Rajnath Singh appears to say in English: “Prime Minister Modi’s visit to Israel before the attack on Iran reflects India’s solidarity with its strategic partner… He warned Tehran that hostile actions would have serious consequences for regional peace.”

Fact Check:
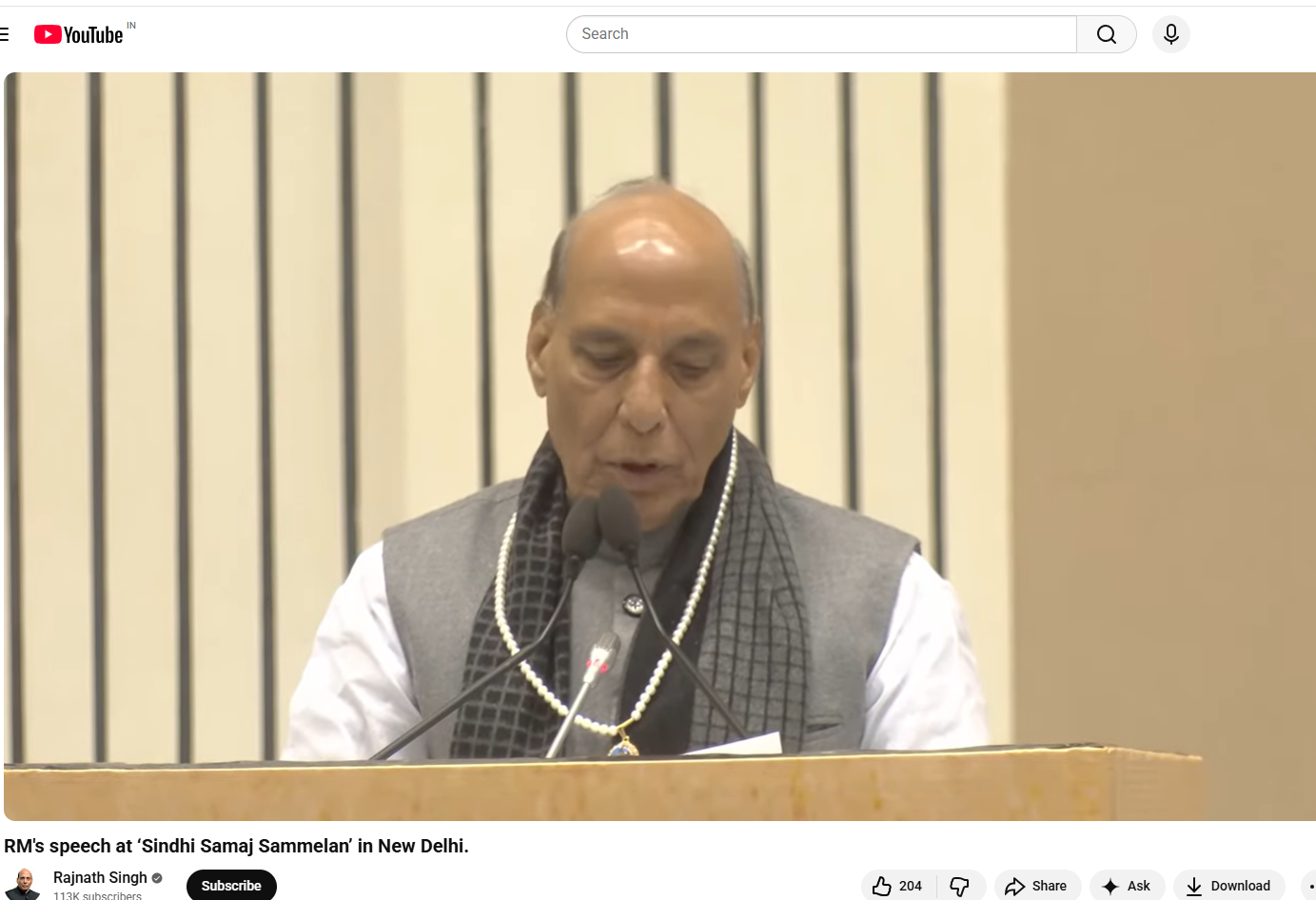
To verify the claim, we extracted keyframes from the viral video and conducted a reverse image search. During the research , we found the original video on Rajnath Singh’s official YouTube channel. The video was uploaded on November 23, 2025.In the original video, Rajnath Singh was addressing a Sindhi community conference in Delhi. During his speech, he was talking about Sindhi culture and the history of Partition. He did not mention Israel, Iran or any Middle East conflict during the entire program.
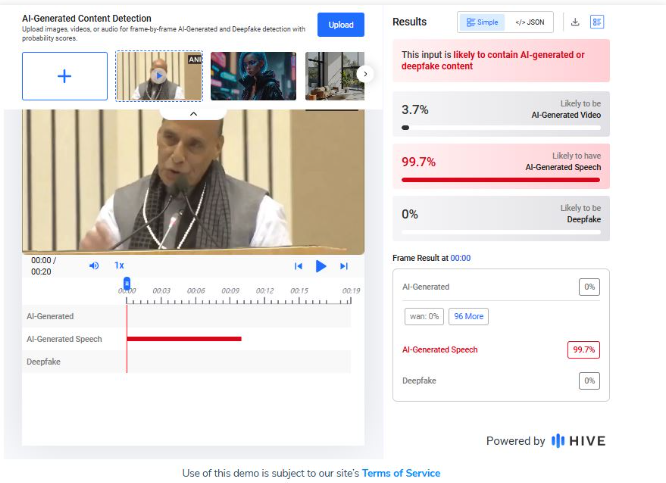
Upon closely examining the viral video, technical inconsistencies between the lip movements and the audio (lip-sync discrepancies) can be observed, which strongly indicate that the video may have been generated using AI. To verify this, we analysed the clip using several AI-detection tools. The AI detection tool Hive Moderation indicated that the video has a 99% probability of being AI-generated.
Conclusion:
Our research found that the viral video of Rajnath Singh is a deepfake. He has not made any statement supporting Israel or opposing Iran. The original video is from a Sindhi community event in Delhi, which has been digitally altered using AI to spread a misleading claim.


